
- Calculators
- Swot Analysis
- Pestle Analysis
- Five Forces Analysis
- Organizational Structure
- Copywriting
- Research Topics
- Student Resources

Services We Provide

Resources We Provide

Login / Register

- 15 Latest Networking Research Topics for Students
Comparative analysis between snort and suricata IDS software(s)
Description of the topic
The main focus of this research is to conduct a comparative analysis between Snort and Suricata software to determine which IDS software can provide better performance. There are various IDS software(s) available that can be used by organizations but it is difficult to identify which one is best (Aldarwbi et al., 2022). Different organizational structures are often facing problems while setting up an IDS system which results in false positives and intrusions. Through this research, it can be identified which IDS software is better and what secure configuration is required to detect intrusions (Waleed et al., 2022).
Research objectives
- To evaluate Snort and Suricata IDS software(s) to determine the most optimal one.
- To identify the false positive rate of Snort and Suricata on the networked environment.
Research questions
RQ1: Which IDS software can perform better on the production network in terms of performance, security, scalability and reliability?
RQ2: What different ways can be followed to deal with false positive problems in IDS technology?
Research methodology
The given research objectives and research questions can be addressed using quantitative research methodology where an experimental approach can be followed. For the given topic, both Snort and Suricata IDS systems should be configured and tested against different attacks. Depending on the findings, it can be analyzed which IDS software can perform better in terms of performance and security (Shuai & Li, 2021).
- Aldarwbi, M.Y., Lashkari, A.H. and Ghorbani, A.A. (2022) “The sound of intrusion: A novel network intrusion detection system,” Computers and Electrical Engineering , 104, p. 108455.
- Shuai, L. and Li, S. (2021) “Performance optimization of Snort based on DPDK and Hyperscan,” Procedia Computer Science , 183, pp. 837-843.
- Waleed, A., Jamali, A.F. and Masood, A. (2022) “Which open-source ids? Snort, Suricata or Zeek,” Computer Networks , 213, p. 109116.
Role of honeypots and honey nets in network security
Network Security has become essential nowadays and there is a need for setting up robust mechanisms to maintain confidentiality and integrity (Feng et al., 2023). Due to the number of security mechanisms available, organizations found it hard to finalize and implement them on their network. For example, honey pots and honeynet approaches look almost the same and have the same purpose but work differently. Under this research topic, the configuration of honeynets and honeypots can be done to check which one can perform better security in terms of trapping cyber attackers. The entire implementation can be carried out in the cloud-based instance for improved security and it can be identified which type of honey pot technology must be preferred (Maesschalck et al., 2022).
- To set up a honey pot system using Open Canary on the virtual instance to protect against cyber attackers.
- To set up a honeynet system on the virtual instance to assure protection is provided against malicious attackers.
- To test honeypots and honeynets by executing DDoS attacks to check which can provide better security.
RQ1: Why is there a need for using honeypots over honey pots in a production networked environment?
RQ2: What are the differences between cloud-based and local honey pot systems for endpoint protection?
This research can be carried out using the quantitative method of research. At the initial stage, the implementation of honeypots and honeypots can be done on the virtual instance following different security rules. Once the rules are applied, the testing can be performed using a Kali Linux machine to check whether honey pots were effective or honeynets (Gill et al., 2020).
- Feng, H. et al. (2023) “Game theory in network security for Digital Twins in industry,” Digital Communications and Networks [Preprint].
- Gill, K.S., Saxena, S. and Sharma, A. (2020) “GTM-CSEC: A game theoretic model for cloud security based on ids and Honeypot,” Computers & Security , 92, p. 101732
- Maesschalck, S. et al. (2022) “Don’t get stung, cover your ICS in honey: How do honeypots fit within industrial control system security,” Computers & Security , 114, p. 102598.
How do malware variants are progressively improving?
This research can be based on evaluating how malware variants are progressively improving and what should be its state in the coming future. Malware is able to compromise confidential user’s information assets which is why this research can be based on identifying current and future consequences owing to its improvements (Deng et al., 2023). In this field, there is no research work that has been carried out to identify how malware variants are improving their working and what is expected to see in future. Once the evaluation is done, a clear analysis can also be done on some intelligent preventive measures to deal with dangerous malware variants and prevent any kind of technological exploitation (Tang et al., 2023).
- To investigate types of malware variants available to learn more about malware's hidden features.
- To focus on future implications of malware executable programs and how they can be avoided.
- To discuss intelligent solutions to deal with all malware variants.
RQ1: How do improvements in malware variants impact enterprises?
RQ2: What additional solutions are required to deal with malware variants?
In this research, qualitative analysis can be conducted on malware variants and the main reason behind their increasing severity. The entire research can be completed based on qualitative research methodology to answer defined research questions and objectives. Some real-life case studies should also be integrated into the research which can be supported by the selected topic (Saidia Fasci et al., 2023).
- Deng, H. et al. (2023) “MCTVD: A malware classification method based on three-channel visualization and deep learning,” Computers & Security , 126, p. 103084.
- Saidia Fasci, L. et al. (2023) “Disarming visualization-based approaches in malware detection systems,” Computers & Security , 126, p. 103062.
- Tang, Y. et al. (2023) “BHMDC: A byte and hex n-gram based malware detection and classification method,” Computers & Security , p. 103118.
Implementation of IoT - enabled smart office/home using cisco packet tracer
The Internet of Things has gained much more attention over the past few years which is why each enterprise and individual aims at setting up an IoT network to automate their processes (Barriga et al., 2023). This research can be based on designing and implementing an IoT-enabled smart home/office network using Cisco Packet Tracer software. Logical workspace, all network devices, including IoT devices can be used for preparing a logical network star topology (Elias & Ali, 2014). To achieve automation, the use of different IoT rules can be done to allow devices to work based on defined rules.
- To set up an IoT network on a logical workspace using Cisco Packet Tracer simulation software.
- To set up IoT-enabled rules on an IoT registration server to achieve automation (Hou et al., 2023).
RQ: Why is the Cisco packet tracer preferred for network simulation over other network simulators?
At the beginning of this research, a quantitative research methodology can be followed where proper experimental set-up can be done. As a packet tracer is to be used, the star topology can be used to interconnect IoT devices, sensors and other network devices at the home/office. Once a placement is done, the configuration should be done using optimal settings and all IoT devices can be connected to the registration server. This server will have IoT rules which can help in achieving automation by automatically turning off lights and fans when no motion is detected (Baggan et al., 2022).
- Baggan, V. et al. (2022) “A comprehensive analysis and experimental evaluation of Routing Information Protocol: An Elucidation,” Materials Today: Proceedings , 49, pp. 3040–3045.
- Barriga, J.A. et al. (2023) “Design, code generation and simulation of IOT environments with mobility devices by using model-driven development: Simulateiot-Mobile,” Pervasive and Mobile Computing , 89, p. 101751.
- Elias, M.S. and Ali, A.Z. (2014) “Survey on the challenges faced by the lecturers in using packet tracer simulation in computer networking course,” Procedia - Social and Behavioral Sciences , 131, pp. 11–15.
- Hou, L. et al. (2023) “Block-HRG: Block-based differentially private IOT networks release,” Ad Hoc Networks , 140, p. 103059.
Comparative analysis between AODV, DSDV and DSR routing protocols in WSN networks
For wireless sensor networks (WSN), there is a major need for using WSN routing rather than performing normal routines. As WSN networks are self-configured, there is a need for an optimal routing protocol that can improve network performance in terms of latency, jitter, and packet loss (Luo et al., 2023). There are often various problems faced when WSN networks are set up due to a lack of proper routing protocol selection. As a result of this, severe downtime is faced and all links are not able to communicate with each other easily (Hemanand et al., 2023). In this research topic, the three most widely used WSN routing protocols AODV, DSDV and DSR can be compared based on network performance. To perform analysis, three different scenarios can be created in network simulator 2 (Ns2).
- To create three different scenarios on ns2 software to simulate a network for 1 to 100 seconds.
- To analyze which WSN routing is optimal in terms of network performance metrics, including latency, jitter and packet loss.
- To use CBR and NULL agents for all wireless scenarios to start with simulation purposes.
RQ: How do AODV, DSR and DSDV routing protocols differ from each other in terms of network performance?
This research can be carried out using a quantitative research method. The implementation for the provided research topic can be based on Ns2 simulation software where three different scenarios can be created (AODV, DSDV and DSR). For each scenario, NULL, CSR and UDP agents can be done to start with simulation for almost 1 to 100 seconds. For all transmissions made during the given time, network performance can be checked to determine which routing is best (Mohapatra & Kanungo, 2012).
- Human and, D. et al. (2023) “Analysis of power optimization and enhanced routing protocols for Wireless Sensor Networks,” Measurement: Sensors , 25, p. 100610. Available at: https://doi.org/10.1016/j.measen.2022.100610.
- Luo, S., Lai, Y. and Liu, J. (2023) “Selective forwarding attack detection and network recovery mechanism based on cloud-edge cooperation in software-defined wireless sensor network,” Computers & Security , 126, p. 103083. Available at: https://doi.org/10.1016/j.cose.2022.103083.
- Mohapatra, S. and Kanungo, P. (2012) “Performance analysis of AODV, DSR, OLSR and DSDV routing protocols using NS2 Simulator,” Procedia Engineering , 30, pp. 69–76. Available at: https://doi.org/10.1016/j.proeng.2012.01.835.
Securing wireless network using AAA authentication and WLAN controller
Wireless networks often face intrusion attempts due to insecure protocols and sometimes open SSIDs. As a result of this, man-in-the-middle and eavesdropping attacks become easier which results in the loss of confidential information assets (Sivasankari & Kamalakkannan, 2022). When it comes to managing networks in a large area, there are higher chances for attacks that enable cyber attackers in intercepting ongoing communication sessions. However, there is currently no research conducted where the use of AAA authentication has been done with WLAN controllers to make sure a higher level of protection is provided (Nashwan, 2021). The proposed research topic can be based on securing wireless networks with the help of AAA authentication and WLAN controllers. The use of AAA authentication can be done to set up a login portal for users whilst the WLAN controller can be used for managing all wireless access points connected to the network (Nashwan, 2021).
- To set up AAA authentication service on the wireless network simulated on Cisco Packet Tracer for proper access control.
- To set up a WLAN controller on the network to manage all wireless access points effortlessly.
- To use WPA2-PSK protocol on the network to assure guest users are only able to access wireless networks over a secure protocol.
RQ1: What additional benefits are offered by AAA authentication on the WLAN networks?
RQ2: Why are wireless networks more likely to face network intrusions than wired networks?
This research topic is based on the secure implementation of a wireless LAN network using a Cisco packet tracer. Hence, this research can be carried out using a quantitative research method. The implementation can be carried out using AAA authentication which can assure that access control is applied for wireless logins. On the other hand, a WLAN controller can also be configured which can ensure that all WAPs are managed (ZHANG et al., 2012).
- Nashwan, S. (2021) “AAA-WSN: Anonymous Access Authentication Scheme for wireless sensor networks in Big Data Environment,” Egyptian Informatics Journal , 22(1), pp. 15–26.
- Sivasankari, N. and Kamalakkannan, S. (2022) “Detection and prevention of man-in-the-middle attack in IOT network using regression modeling,” Advances in Engineering Software , 169, p. 103126.
- ZHANG, J. et al. (2012) “AAA authentication for Network mobility,” The Journal of China Universities of Posts and Telecommunications , 19(2), pp. 81-86.
OWASP's approach to secure web applications from web application exploits
The research can revolve around the development of web applications by considering OWASP's top 10 rules. Usually, web applications are deployed by organizations depending on their requirements and these applications are vulnerable to various exploits, including injection, broken authentication and other forgery attacks (Poston, 2020). Identifying every single vulnerability is difficult when reference is not taken and often organizations end up hosting a vulnerable server that leads to privacy issues and compromises confidential information easily. In this research, OWASP's top 10 approaches can be followed to develop a secure web application that can be able to protect against top web application exploits. This approach is based on emphasizing severe and minor vulnerabilities which must be patched for protecting against web application attacks (Deepa & Thilagam, 2016).
- The first objective can be setting up an insecure web application on the cloud environment which can be exploited with different techniques.
- The second objective can be to consider all techniques and procedures provided by OWASP's top 10 methodologies.
- The last objective can be applying all fixes to insecure web applications to make them resistant to OWASP top 10 attacks (Sonmez, 2019).
RQ1: What are the benefits of using OWASP's top 10 approaches to harden web applications in comparison to other security approaches?
The research methodology considered for this research project can be quantitative using an experimental approach. The practical work can be done for the selected topic using AWS or the Azure cloud platform. Simply, a virtual web server can be configured and set up with a secure and insecure web application. Following OWASP's top 10 techniques and procedures, the web application can be secured from possible attacks. In addition, insecure applications can also be exploited and results can be evaluated (Applebaum et al., 2021).
- Applebaum, S., Gaber, T. and Ahmed, A. (2021) “Signature-based and machine-learning-based web application firewalls: A short survey,” Procedia Computer Science , 189, pp. 359–367. Available at: https://doi.org/10.1016/j.procs.2021.05.105.
- Deepa, G. and Thilagam, P.S. (2016) “Securing web applications from injection and logic vulnerabilities: Approaches and challenges,” Information and Software Technology , 74, pp. 160–180. Available at: https://doi.org/10.1016/j.infsof.2016.02.005.
- Poston, H. (2020) “Mapping the owasp top Ten to the blockchain,” Procedia Computer Science , 177, pp. 613-617. Available at: https://doi.org/10.1016/j.procs.2020.10.087.
- Sonmez, F.Ö. (2019) “Security qualitative metrics for Open Web Application Security Project Compliance,” Procedia Computer Science , 151, pp. 998-1003. Available at: https://doi.org/10.1016/j.procs.2019.04.140.
Importance of configuring RADIUS (AAA) server on the network
User authentication has become significant nowadays as it guarantees that a legitimate user is accessing the network. But a problem is faced when a particular security control is to be identified for authentication and authorization. These controls can be categorized based on mandatory access controls, role-based access control, setting up captive portals and many more. Despite several other security controls, one of the most efficient ones is the RADIUS server (SONG et al., 2008). This server can authenticate users on the network to make sure network resources are accessible to only legal users. This research topic can be based on understanding the importance of RADIUS servers on the network which can also be demonstrated with the help of the Cisco Packet Tracer. A network can be designed and equipped with a RADIUS server to ensure only legal users can access network resources (WANG et al., 2009).
- To configure RADIUS (AAA) server on the network which can be able to authenticate users who try to access network resources.
- To simulate a network on a packet tracer simulation software and verify network connectivity.
RQ1: What are other alternatives to RADIUS (AAA) authentication servers for network security?
RQ2: What are the common and similarities between RADIUS and TACACS+ servers?
As a logical network is to be designed and configured, a quantitative research methodology can be followed. In this research coursework, a secure network design can be done using a packet tracer network simulator, including a RADIUS server along with the DMZ area. The configuration for the RADIUS server can be done to allow users to only access network resources by authenticating and authorizing (Nugroho et al., 2022).
- Nugroho, Y.S. et al. (2022) “Dataset of network simulator related-question posts in stack overflow,” Data in Brief , 41, p. 107942.
- SONG, M., WANG, L. and SONG, J.-de (2008) “A secure fast handover scheme based on AAA protocol in Mobile IPv6 Networks,” The Journal of China Universities of Posts and Telecommunications , 15, pp. 14-18.
- WANG, L. et al. (2009) “A novel congestion control model for interworking AAA in heterogeneous networks,” The Journal of China Universities of Posts and Telecommunications , 16, pp. 97-101.
Comparing mod security and pF sense firewall to block illegitimate traffic
Firewalls are primarily used for endpoint security due to their advanced features ranging from blocking to IDS capabilities and many more. It is sometimes challenging to identify which type of firewall is best and due to this reason, agencies end up setting up misconfigured firewalls (Tiwari et al., 2022). This further results in a cyber breach, destroying all business operations. The research can be emphasizing conducting a comparison between the two most widely used firewalls i.e. Mod Security and pF sense. Using a virtualized environment, both firewalls can be configured and tested concerning possible cyber-attacks (Lu & Yang, 2020).
- To use the local environment to set up Mod security and pF sense firewall with appropriate access control rules.
- To test both firewalls by executing distributed denial of service attacks from a remote location.
- To compare which type of firewall can provide improved performance and robust security.
RQ: How do Mod security and pF sense differ from each other in terms of features and performance?
The practical experimentation for both firewalls can be done using a virtualized environment where two different machines can be created. Hence, this research can be carried out using a quantitative research method . The first machine can have Mod security and the second machine can have pF sense configured. A new subnet can be created which can have these two machines. The third machine can be an attacking machine which can be used for testing firewalls. The results obtained can be then evaluated to identify which firewall is best for providing security (Uçtu et al., 2021).
- Lu, N. and Yang, Y. (2020) “Application of evolutionary algorithm in performance optimization of Embedded Network Firewall,” Microprocessors and Microsystems , 76, p. 103087.
- Tiwari, A., Papini, S. and Hemamalini, V. (2022) “An enhanced optimization of parallel firewalls filtering rules for scalable high-speed networks,” Materials Today: Proceedings , 62, pp. 4800-4805.
- Uçtu, G. et al. (2021) “A suggested testbed to evaluate multicast network and threat prevention performance of Next Generation Firewalls,” Future Generation Computer Systems , 124, pp. 56-67.
Conducting a comprehensive investigation on the PETYA malware
The main purpose of this research is to conduct a comprehensive investigation of the PETYA malware variant (McIntosh et al., 2021). PETYA often falls under the category of ransomware attacks which not only corrupt and encrypt files but can compromise confidential information easily. Along with PETYA, there are other variants also which lead to a security outage and organizations are not able to detect these variants due to a lack of proper detection capabilities (Singh & Singh, 2021). In this research, a comprehensive analysis has been done on PETYA malware to identify its working and severity level. Depending upon possible causes of infection of PETYA malware, some proactive techniques can also be discussed (Singh & Singh, 2021). A separation discussion can also be made on other malware variants, their features, and many more.
- The main objective of this research is to scrutinize the working of PETYA malware because a ransomware attack can impact the micro and macro environment of the organizations severely.
- The working of PETYA malware along with its source code can be reviewed to identify its structure and encryption type.
- To list all possible CVE IDs which are exploited by the PETYA malware.
RQ1: How dangerous is PETYA malware in comparison to other ransomware malware?
This research can be based on qualitative research methodology to evaluate the working of PETYA malware from various aspects, the methodology followed and what are its implications. The research can be initiated by evaluating the working of PETYA malware, how it is triggered, what encryption is applied and other factors. A sample source code can also be analyzed to learn more about how cryptography is used with ransomware (Abijah Roseline & Geetha, 2021).
- Abijah Roseline, S. and Geetha, S. (2021) “A comprehensive survey of tools and techniques mitigating computer and mobile malware attacks,” Computers & Electrical Engineering , 92, p. 107143.
- McIntosh, T. et al. (2021) “Enforcing situation-aware access control to build malware-resilient file systems,” Future Generation Computer Systems , 115, pp. 568-582.
- Singh, J. and Singh, J. (2021) “A survey on machine learning-based malware detection in executable files,” Journal of Systems Architecture , 112, p. 101861.
Setting up a Live streaming server on the cloud platform
Nowadays, various organizations require a live streaming server to stream content depending upon their business. However, due to a lack of proper hardware, organizations are likely to face high network congestion, slowness and other problems (Ji et al., 2023). Referring to the recent cases, it has been observed that setting up a streaming server on the local environment is not expected to perform better than a cloud-based streaming server configuration (Martins et al., 2019). This particular research topic can be based on setting up a live streaming server on the AWS or Azure cloud platform to make sure high network bandwidth is provided with decreased latency. The research gap analysis would be conducted to analyze the performance of live streaming servers on local and cloud environments in terms of network performance metrics (Bilal et al., 2018).
- To set up a live streaming server on the AWS or Azure cloud platform to provide live streaming services.
- To use load balancers alongside streaming servers to ensure the load is balanced and scalability is achieved.
- To use Wireshark software to test network performance during live streaming.
RQ1: Why are in-house streaming servers not able to provide improved performance in comparison to cloud-based servers?
RQ2: What additional services are provided by cloud service providers which help in maintaining network performance?
The implementation is expected to carry out on the AWS cloud platform with other AWS services i.e. load balancer, private subnet and many more (Efthymiopoulou et al., 2017). Hence, this research can be carried out using a quantitative research method. The configuration of ec2 instances can be done which can act as a streaming server for streaming media and games. For testing this project, the use of OBS studio can be done which can help in checking whether streaming is enabled or not. For network performance, Wireshark can be used for testing network performance (George et al., 2020).
- Bilal, KErbad, A. and Hefeeda, M. (2018) “QoE-aware distributed cloud-based live streaming of multi-sourced Multiview Videos,” Journal of Network and Computer Applications , 120, pp. 130-144.
- Efthymiopoulou, M. et al. (2017) “Robust control in cloud-assisted peer-to-peer live streaming systems,” Pervasive and Mobile Computing , 42, pp. 426-443.
- George, L.C. et al. (2020) “Usage visualization for the AWS services,” Procedia Computer Science , 176, pp. 3710–3717.
- Ji, X. et al. (2023) “Adaptive QoS-aware multipath congestion control for live streaming,” Computer Networks , 220, p. 109470.
- Martins, R. et al. (2019) “Iris: Secure reliable live-streaming with Opportunistic Mobile Edge Cloud offloading,” Future Generation Computer Systems , 101, pp. 272-292.
Significance of using OSINT framework for Network reconnaissance
Network reconnaissance is becoming important day by day when it comes to penetration testing. Almost all white hat hackers are dependent on the OSINT framework to start with network reconnaissance and footprinting when it comes to evaluating organizational infrastructure. On the other hand, cyber attackers are also using this technique to start fetching information about their target. Currently, there is no investigation carried out to identify how effective the OSINT framework is over traditional reconnaissance activities (Liu et al., 2022). This research is focused on using OSINT techniques to analyze victims using different sets of tools like Maltego, email analysis and many other techniques. The analysis can be based on fetching sensitive information about the target which can be used for conducting illegal activities (Abdullah, 2019).
- To use Maltego software to conduct network reconnaissance on the target by fetching sensitive information.
- To compare the OSINT framework with other techniques to analyze why it performs well.
RQ1: What is the significance of using the OSINT framework in conducting network reconnaissance?
RQ2: How can the OSINT framework be used by cyber hackers for conducting illegitimate activities?
The OSINT framework is easily accessible on its official website where different search options are given. Hence, this research can be carried out using a quantitative research method. Depending upon the selected target, each option can be selected and tools can be shortlisted for final implementation. Once the tools are shortlisted, they can be used to conduct network reconnaissance (González-Granadillo et al., 2021). For example, Maltego can be used as it is a powerful software to fetch information about the target.
- Abdullah, S.A. (2019) “Seui-64, bits an IPv6 addressing strategy to mitigate reconnaissance attacks,” Engineering Science and Technology , an International Journal, 22(2), pp. 667–672.
- Gonzalez-Granadillo, G. et al. (2021) “ETIP: An enriched threat intelligence platform for improving OSINT correlation, analysis, visualization and sharing capabilities,” Journal of Information Security and Applications , 58, p. 102715.
- Liu, W. et al. (2022) “A hybrid optimization framework for UAV Reconnaissance Mission Planning,” Computers & Industrial Engineering , 173, p. 108653.
Wired and wireless network hardening in cisco packet tracer
At present, network security has become essential and if enterprises are not paying attention to the security infrastructure, there are several chances for cyber breaches. To overcome all these issues, there is a need for setting up secure wired and wireless networks following different techniques such as filtered ports, firewalls, VLANs and other security mechanisms. For the practical part, the use of packet tracer software can be done to design and implement a highly secure network (Sun, 2022).
- To use packet tracer simulation software to set up secure wired and wireless networks.
- Use different hardening techniques, including access control rules, port filtering, enabling passwords and many more to assure only authorized users can access the network (Zhang et al., 2012).
RQ: Why is there a need for emphasizing wired and wireless network security?
Following the quantitative approach, the proposed research topic implementation can be performed in Cisco Packet Tracer simulation software. Several devices such as routers, switches, firewalls, wireless access points, hosts and workstations can be configured and interconnected using Cat 6 e cabling. For security, every device can be checked and secure design principles can be followed like access control rules, disabled open ports, passwords, encryption and many more (Smith & Hasan, 2020).
- Smith, J.D. and Hasan, M. (2020) “Quantitative approaches for the evaluation of Implementation Research Studies,” Psychiatry Research , 283, p. 112521.
- Sun, J. (2022) “Computer Network Security Technology and prevention strategy analysis,” Procedia Computer Science , 208, pp. 570–576.
- Zhang, YLiang, R. and Ma, H. (2012) “Teaching innovation in computer network course for undergraduate students with a packet tracer,” IERI Procedia , 2, pp. 504–510.
Different Preemptive ways to resist spear phishing attacks
When it comes to social engineering, phishing attacks are rising and are becoming one of the most common ethical issues as it is one of the easiest ways to trick victims into stealing information. This research topic is based on following different proactive techniques which would help in resisting spear phishing attacks (Xu et al., 2023). This can be achieved by using the Go-Phish filter on the machine which can automatically detect and alert users as soon as the phished URL is detected. It can be performed on the cloud platform where the apache2 server can be configured along with an anti-phishing filter to protect against phishing attacks (Yoo & Cho, 2022).
- To set up a virtual instance on the cloud platform with an apache2 server and anti-phishing software to detect possible phishing attacks.
- To research spear phishing and other types of phishing attacks that can be faced by victims (Al-Hamar et al., 2021).
RQ1: Are phishing attacks growing just like other cyber-attacks?
RQ2: How effective are anti-phishing filters in comparison to cyber awareness sessions?
The entire research can be conducted by adhering to quantitative research methodology which helps in justifying all research objectives and questions. The implementation of the anti-phishing filter can be done by creating a virtual instance on the cloud platform which can be configured with an anti-phishing filter. Along with this, some phishing attempts can also be performed to check whether the filter works or not (Siddiqui et al., 2022).
- Al-Hamar, Y. et al. (2021) “Enterprise credential spear-phishing attack detection,” Computers & Electrical Engineering , 94, p. 107363.
- Siddiqui, N. et al. (2022) “A comparative analysis of US and Indian laws against phishing attacks,” Materials Today: Proceedings , 49, pp. 3646–3649.
- Xu, T., Singh, K. and Rajivan, P. (2023) “Personalized persuasion: Quantifying susceptibility to information exploitation in spear-phishing attacks,” Applied Ergonomics , 108, p. 103908.
- Yoo, J. and Cho, Y. (2022) “ICSA: Intelligent chatbot security assistant using text-CNN and multi-phase real-time defense against SNS phishing attacks,” Expert Systems with Applications , 207, p. 117893.
Evaluating the effectiveness of distributed denial of service attacks
The given research topic is based on evaluating the effectiveness of distributed denial of service attacks on cloud and local environments. Hence, this research can be carried out using a quantitative research method. Cyber attackers find DDoS as one of the most dangerous technological exploitation when it comes to impacting network availability (Krishna Kishore et al., 2023). This research can revolve around scrutinizing the impact of DDoS attacks on the local environment and cloud environment. This can be done by executing DDoS attacks on a simulated environment using hoping or other software(s) to check where it has a higher magnitude (de Neira et al., 2023).
- To set up a server on the local and cloud environment to target using DDoS attacks for checking which had experienced slowness.
- To determine types of DDoS attack types, their magnitude and possible mitigation techniques.
RQ: Why do DDoS attacks have dynamic nature and how is it likely to sternly impact victims?
The experimentation for this research can be executed by creating a server on the local and cloud environment. Hence, this research can be carried out using a quantitative research method. These servers can be set up as web servers using apache 2 service. On the other hand, a Kali Linux machine can be configured with DDoS execution software. Each server can be targeted with DDoS attacks to check its effectiveness (Benlloch-Caballero et al., 2023).
- Benlloch-Caballero, P., Wang, Q. and Alcaraz Calero, J.M. (2023) “Distributed dual-layer autonomous closed loops for self-protection of 5G/6G IOT networks from distributed denial of service attacks,” Computer Networks , 222, p. 109526.
- de Neira, A.B., Kantarci, B. and Nogueira, M. (2023) “Distributed denial of service attack prediction: Challenges, open issues and opportunities,” Computer Networks , 222, p. 109553.
- Krishna Kishore, P., Ramamoorthy, S. and Rajavarman, V.N. (2023) “ARTP: Anomaly-based real time prevention of distributed denial of service attacks on the web using machine learning approach,” International Journal of Intelligent Networks , 4, pp. 38–45.
Recommended Readings
Latest Web Development Research Topics
Top Management Research Topics
Newest AI Research Topics
Research in every field is becoming more and more essential because of constant developments around the world. Similar is the case in the field of networking. This is the reason; students who are preparing to master the field of networking need to keep their knowledge of the current state of the art in the field up to date.
However, choosing the right research topic often becomes a tough task for students to carry out their research effectively. That being the case, this list contains 15 latest research topics in the field of networking. Whether you are a seasoned researcher or just starting, this list can provide you with ample inspiration and guidance to drive your research forward in the dynamic and evolving field of Networking.
Copyright © 2023 CrowJack. All Rights Reserved
- How it works

Useful Links
How much will your dissertation cost?
Have an expert academic write your dissertation paper!
Dissertation Services
Get unlimited topic ideas and a dissertation plan for just £45.00
Order topics and plan
Get 1 free topic in your area of study with aim and justification
Yes I want the free topic
Computer Networking Dissertation Topics
Published by Carmen Troy at January 5th, 2023 , Revised On May 9, 2024
A dissertation is an essential aspect of completing your degree program. Whether you are pursuing your master’s or are enrolled in a PhD program, you will not be awarded a degree without successfully submitting a thesis. To ensure that your thesis is submitted successfully without any hindrances, you should first get your topic and dissertation outline approved by your professor. When approving, supervisors focus on a lot of aspects.
However, relevance, recency, and conciseness play a huge role in accepting or rejecting your topic.
As a computer networking student, you have a variety of networking topics to choose from. With the field evolving with each passing day, you must ensure that your thesis covers recent computer networking topics and explores a relevant problem or issue. To help you choose the right topic for your dissertation, here is a list of recent and relevant computer networking dissertation topics.
List Of Trending Ideas For Your Computer Networking Dissertation
- Machine learning for proactive network anomaly detection
- The role of software-defined-networking (SDN) for network performance and security
- Applications and challenges of 6G technologies
- How to ensure fairness and efficiency in Multi-Access Edge Computing (MEC)
- Denial-of-Service (DoS) Attacks in the Age of Distributed Denial-of-Service (DDoS) Attacks
- Applications and rise of Low-Power Wide Area Networks (LPWANs)
- Efficient Resource Allocation and Quality-of-Service (QoS) Management
- Ethical Implications of Artificial Intelligence (AI) in Network Management
- The best ways to use Blockchain for Tamper-Proof Evidence Collection and Storage
- Role of Network Operators in Cloud Gaming
Computer Networking Dissertation Topics For Your Research
Topic 1: an evaluation of the network security during machine to machine communication in iot.
Research Aim: The research aims to evaluate the network security issues associated with M2M communication in IoT.
Objectives:
- To evaluate the factors affecting the network security of IoT devices.
- To determine the methods for increasing data integrity in M2M communication against physical tampering and unauthorised monitoring.
- To evaluate the network security issues associated with M2M communication in IoT and offer suitable recommendations for improvement.
Topic 2: An analysis of the cybersecurity challenges in public clouds and appropriate intrusion detection mechanisms.
Research Aim: The aim of the research is to analyse the cybersecurity challenges in public clouds and the appropriate intrusion detection mechanisms.
Objectives:
- To analyse the types of cybersecurity threats impacting public clouds.
- To determine some of the competent intrusion detection techniques that can be used in cloud computing.
- To investigate the cybersecurity challenges in public clouds and offer mitigating with appropriate intrusion detection techniques.
Topic 3: Investigating the impact of SaaS cloud ERP on the scalability and cost-effectiveness of business.
Research Aim: The research aims to investigate the impact of SaaS cloud ERP on the scalability and cost-effectiveness of business.
- To analyse the benefits of SaaS ERP over traditional ERP.
- To evaluate the characteristics of SaaS architecture in cloud computing and determine its varieties.
- To investigate how SaaS cloud ERP impacts business scalability and cost-effectiveness.
Topic 4: An evaluation of the requirements of cloud repatriation and the challenges associated with it.
Research Aim: The research aims to evaluate the requirements of cloud repatriation in organisations and the associated challenges
- To analyse the key factors of cloud repatriation.
- To determine the challenges associated with cloud repatriation from public clouds.
- To evaluate the need for cloud repatriation in organisations and the associated complexities
Topic 5: An examination of the security mechanisms in decentralised networks and the ways of enhancing system robustness
Research Aim: The research aims to investigate the security mechanisms in decentralised networks and the ways of enhancing system robustness.
- To analyse the concept of decentralised networks and understand their difference from centralised networks.
- To analyse the security mechanisms in decentralised networks to determine how it offers visibility and traceability.
- To investigate the security mechanisms in decentralised networks and how system robustness can be increased for better privacy and security.
Latest Computer Networking Dissertation Topics
Exploring the importance of computer networking in today’s era.
Research Aim: Even though computer networking has been practised for a few years now, its importance has increased immensely over the past two years. A few main reasons include the use of technology by almost every business and the aim to offer customers an easy and convenient shopping experience. The main aim of this research will be to explain the concepts of computer networking, its benefits, and its importance in the current era. The research will also discuss how computer networking has helped businesses and individuals perform their work and benefit from it. The research will then specifically state examples where computer networking has brought positive changes and helped people achieve what they want.
Wireless Networks in Business Settings – An Analysis
Research Aim: Wireless networks are crucial in computer networking. They help build networks seamlessly, and once the networks are set up on a wireless network, it becomes extremely easy for the business to perform its daily activities. This research will investigate all about wireless networks in a business setting. It will first introduce the various wireless networks that can be utilised by a business and will then talk about how these networks help companies build their workflow around them. The study will analyse different wireless networks used by businesses and will conclude how beneficial they are and how they are helping the business.
Understanding Virtual Private Networks – A Deep Analysis of Their Challenges
Research Aim: Private virtual networks (VPN) are extremely common today. These are used by businesses and individuals alike. This research aims to understand how these networks operate and how they help businesses build strong and successful systems and address the challenges of VPNs. A lot of businesses do not adopt virtual private networks due to the challenges that they bring. This research will address these challenges in a way that will help businesses implement VPNs successfully.
A Survey of the Application of Wireless Sensor Networks
Research Aim: Wireless sensor networks are self-configured, infrastructure-less wireless networks to pass data. These networks are now extremely popular amongst businesses because they can solve problems in various application domains and possess the capacity to change the way work is done. This research will investigate where wireless sensor networks are implemented, how they are being used, and how they are performing. The research will also investigate how businesses implement these systems and consider factors when utilising these wireless sensor networks.
Computer Network Security Attacks – Systems and Methods to Respond
Research Aim: With the advent of technology today, computer networks are extremely prone to security attacks. A lot of networks have security systems in place. However, people with nefarious intent find one way to intrude and steal data/information. This research will address major security attacks that have impacted businesses and will aim to address this challenge. Various methods and systems will be highlighted to protect the computer networks. In addition to this, the research will also discuss various methods to respond to attacks and to keep the business network protected.
Preventing a Cyberattack – How Can You Build a Powerful Computer Network?
Research Aim: Cyberattacks are extremely common these days. No matter how powerful your network is, you might be a victim of phishing or hacking. The main aim of this research will be to outline how a powerful computer network can be built. Various methods to build a safe computer network that can keep data and information will be outlined, and the study will also highlight ways to prevent a cyberattack. In addition to this, the research will talk about the steps that should be taken to keep the computer network safe. The research will conclude with the best way and system to build a powerful and safe computer network.
Types of Computer Networks: A Comparison and Analysis
Research Aim: There are different types of computer networks, including LAN, WAN, PAN, MAN, CAN, SAN, etc. This research will discuss all the various types of computer networks to help readers understand how all these networks work. The study will then compare the different types of networks and analyse how each of them is implemented in different settings. The dissertation will also discuss the type of computer networks that businesses should use and how they can use them for their success. The study will then conclude which computer network is the best and how it can benefit when implemented.
Detecting Computer Network Attacks by Signatures and Fast Content Analysis
Research Aim: With technological advancement, today, many computer network attacks can be detected beforehand. While many techniques are utilised for detecting these attacks, the use of signatures and fast content analysis are the most popular ones. This research will explore these techniques in detail and help understand how they can detect a computer network attack and prevent it. The research will present different ways these techniques are utilised to detect an attack and help build powerful and safe computer networks. The research will then conclude how helpful these two techniques are and whether businesses should implement them.
Overview of Wireless Network Technologies and their Role in Healthcare
Research Aim: Wireless network technologies are utilised by several industries. Their uses and benefits have helped businesses resolve many business problems and assisted them in conducting their daily activities without any hindrance. This networking topic will help explore how wireless network technologies work and will talk about their benefits. This research aims to find out how wireless technologies help businesses carry out their daily routine tasks effortlessly. For this research, the focus will be on the healthcare industry. The study will investigate how wireless network technology has helped the healthcare sector and how it has benefited them to perform their daily tasks without much effort.
Setting up a Business Communication System over a Computer Network
Research Aim: Communication is an essential aspect of every business. Employees need to communicate effectively to keep the business going. In the absence of effective communication, businesses suffer a lot as the departments are not synchronised, and the operations are haphazard. This research will explore the different ways through which network technologies help conduct smooth and effective communication within organisations. This research will conclude how wireless networks have helped businesses build effective communication systems within their organisation and how they have benefited from it. It will then conclude how businesses have improved and solved major business problems with the help of these systems.
Free Dissertation Topic
Phone Number
Academic Level Select Academic Level Undergraduate Graduate PHD
Academic Subject
Area of Research
Frequently Asked Questions
How to find computer networking dissertation topics.
To find computer networking dissertation topics:
- Follow industry news and emerging technologies.
- Investigate unresolved networking challenges.
- Review recent research papers.
- Explore IoT, cybersecurity , and cloud computing.
- Consider real-world applications.
- Select a topic aligned with your expertise and career aspirations.
You May Also Like
Urban law is a branch of the legal profession that encompasses all aspects of laws and regulations affecting cities and their inhabitants.
Can’t find a topic for your radiology dissertation? Pick from our top radiology research topics to prepare your dissertation or radiology publication.
Need interesting and manageable Facial Recognition dissertation topics? Here are the trending Facial Recognition dissertation titles so you can choose the most suitable one.
USEFUL LINKS
LEARNING RESOURCES

COMPANY DETAILS
- How It Works
Communications and Networking Research Group
Search form.
- Publications
PUBLICATIONS
Journal articles | other papers | conference papers | book chapters | technical reports, journal articles.
134. Vishrant Tripathi, Nick Jones, Eytan Modiano, Fresh-CSMA: A Distributed Protocol for Minimizing Age of Information, IEEE Journal on Communications and Networks, 2024.
133. Bai Liu, Quang Nguyen, Qingkai Liang, Eytan Modiano, Tracking Drift-Plus-Penalty: Utility Maximization for Partially Observable and Controllable Networks, IEEE/ACM Transactions on Networking, 2024.
132. Xinzhe Fu, Eytan Modiano, Optimal Routing to Parallel Servers with Unknown Utilities – Multi-armed Bandit With Queues, IEEE/ACM Transactions on Networking, January 2022.
131. Bai Liu, Qingkai Liang, Eytan Modiano, Tracking MaxWeight: Optimal Control for Partially Observable and Controllable Networks, IEEE/ACM Transactions on Networking, August 2023.
130. Xinzhe Fu, Eytan Modiano, Joint Learning and Control in Stochastic Queueing Networks with unknown Utilities, Proceedings of the ACM on Measurement and Analysis of Computing Systems, 2023.
129. Vishrant Tripathi, Rajat Talak, Eytan Modiano, Information Freshness in Multi-Hop Wireless Networks, IEEE/ACM Transactions on Networking,” April 2023.
128. Xinzhe Fu, Eytan Modiano, “ Learning-NUM: Network Utility Maximization with Unknown Utility Functions and Queueing Delay ,” IEEE/ACM Transactions on Networking,” 2022.
127. Bai Liu, Qiaomin Xie, Eytan Modiano, " RL-QN: A Reinforcement Learning Framework for Optimal Control of Queueing Systems ," ACM Transactions on Modeling and Performance Evaluation of Computing Systems (TOMPECS), 2022.
126. Xinzhe Fu and E. Modiano, “ Elastic Job Scheduling with Unknown Utility Functions ,” Performance Evaluation, 2021.
125. Bai Liu and E. Modiano, “ Optimal Control for Networks with Unobservable Malicious Nodes ,” Performance Evaluation, 2021.
124. Vishrant Tripathi, Rajat Talak, Eytan Modiano, " Age Optimal Information Gathering and Dissemination on Graphs ,” Transactions on Mobile Computing, April 2021.
123. Xinyu Wu, Dan Wu, Eytan Modiano, “ Predicting Failure Cascades in Large Scale Power Systems via the Influence Model Framework, ” IEEE Transactions on Power Systems, 2021.
122. Roy D. Yates, Yin Sun, D. Richard Brown III, Sanjit K. Kaul, Eytan Modiano and Sennur Ulukus, “ Age of Information: An Introduction and Survey, ” Journal on Selected Areas in Communications, February 2021.
121. Jianan Zhang, Abhishek Sinha, Jaime Llorca, Anonia Tulino, Eytan Modiano, “ Optimal Control of Distributed Computing Networks with Mixed-Cast Traffic Flows ,” IEEE/ACM Transactions on Networking, 2021.
120. Thomas Stahlbuhk, Brooke Shrader, Eytan Modiano, " Learning Algorithms for Minimizing Queue Length Regret ,” IEEE Transactions on Information Theory, 2021.
119. Thomas Stahlbuhk, Brooke Shrader, Eytan Modiano, “ Throughput Maximization in Uncooperative Spectrum Sharing Networks ,” IEEE/ACM IEEE/ACM Transactions on Networking, Vol. 28, No. 6, December 2020.
118. Thomas Stahlbuhk, Brooke Shrader, Eytan Modiano, “ Learning algorithms for scheduling in wireless networks with unknown channel statistics ,” Ad Hoc Networks, Vol. 85, pp. 131-144, 2019.
117. Rajat Talak, Eytan Modiano, “ Age-Delay Tradeoffs in Queueing Systems ,” IEEE Transactions on Information Theory, 2021.
116. Rajat Talak, Sertac Karaman, Eytan Modiano, " Improving Age of Information in Wireless Networks with Perfect Channel State Information ,” IEEE/ACM Transactions on Networking, Vol. 28, No. 4, August 2020.
115. Igor Kadota and Eytan Modiano, “ Minimizing the Age of Information in Wireless Networks with Stochastic Arrivals ,” IEEE Transactions on Mobile Computing, 2020.
114. Rajat Talak, Sertac Karaman, Eytan Modiano, “ Optimizing Information Freshness in Wireless Networks under General Interference Constraints ,” IEEE/ACM transactions on Networking, Vol. 28, No. 1, February 2020.
113. X. Fu and E. Modiano, " Fundamental Limits of Volume-based Network DoS Attacks ," Proceedings of the ACM on Measurement and Analysis of Computing Systems, Vol. 3, No. 3, December 2019.
112. Rajat Talak, Sertac Karaman, Eytan Modiano, “ Capacity and Delay Scaling for Broadcast Transmission in Highly Mobile Wireless Networks ,” IEEE Transactions on Mobile Computing, 2019.
111. Abhishek Sinha and Eytan Modiano, “ Throughput-Optimal Broadcast in Wireless Networks with Point-to-Multipoint Transmissions , IEEE Transactions on Mobile Computing, Vol. 19, No. 9, September 2020.
110. Yu-Pin Hsu, Eytan Modiano, Lingjie Duan, “ Scheduling Algorithms for Minimizing Age of Information in Wireless Broadcast Networks with Random Arrivals ,” IEEE Transactions on Mobile Computing, Vol. 19, No. 12, December 2020.
109. Xiaolin Jiang, Hossein S. Ghadikolaei, Gabor Fodor, Eytan Modiano, Zhibo Pang, Michele Zorzi, Carlo Fischione, " Low-latency Networking: Where Latency Lurks and How to Tame It ,” Proceedings of the IEEE, 2019.
108. Jianan Zhang, Edmund Yeh, Eytan Modiano, “ Robustness of Interdependent Random Geometric Networks ,” IEEE Transactions on Network Science and Engineering, Vol. 6, No. 3, July-September 2019.
107. Qingkai Liang, Hyang-Won Lee, Eytan Modiano, “ Robust Design of Spectrum-Sharing Networks ,” IEEE Transactions on Mobile Computing, Vol. 18, No. 8, August 2019.
106. A. Sinha, L. Tassiulas, E. Modiano, “ Throughput-Optimal Broadcast in Wireless Networks with Dynamic Topology ,” IEEE Transactions on Mobile Computing, Vol. 18, No. 5, May 2019.
105. Igor Kadota, Abhishek Sinha, Eytan Modiano, “ Scheduling Algorithms for Optimizing Age of Information in Wireless Networks With Throughput Constraints ,” IEEE/ACM Transactions on Networking, August 2019.
104. Igor Kadota, Abhishek Sinha, Rahul Singh, Elif Uysal-Biyikoglu, Eytan Modjano, “ Scheduling Policies for Minimizing Age of Information in Broadcast Wireless Networks ,” IEEE/ACM Transactions on Networking, Vol. 26, No. 5, October 2018.
103. Jianan Zhang and Eytan Modiano, “ Connectivity in Interdependent Networks ,” IEEE/ACM Transactions on Networking, 2018.
102. Qingkai Liang, Eytan Modiano, “ Minimizing Queue Length Regret Under Adversarial Network Models ,” Proceedings of the ACM on Measurement and Analysis of Computing Systems, Volume 2, Issue 1, April 2018, Article No.: 11, pp 1-32. (same as Sigmetrics 2018).
101. A. Sinha and E. Modiano, “ Optimal Control for Generalized Network Flow Problems ,” IEEE/ACM Transactions on Networking, 2018.
100. Hossein Shokri-Ghadikolaei, Carlo Fischione, Eytan Modiano “ Interference Model Similarity Index and Its Applications to mmWave Networks ,” IEEE Transactions on Wireless Communications, 2018.
99. Matt Johnston, Eytan Modiano, “ Wireless Scheduling with Delayed CSI: When Distributed Outperforms Centralized, ’ IEEE Transactions on Mobile Computing, 2018.
98. A. Sinha, G. Paschos, E. Modiano, “ Throughput-Optimal Multi-hop Broadcast Algorithms ," IEEE/ACM Transactions on Networking, 2017.
97. Nathan Jones, Georgios Paschos, Brooke Shrader, Eytan Modiano, " An Overlay Architecture for Throughput Optimal Multipath Routing ,” IEEE/ACM Transactions on Networking, 2017.
96. Greg Kuperman, Eytan Modiano, “ Providing Guaranteed Protection in Multi-Hop Wireless Networks with Interference Constraints ,” IEEE Transactions on Mobile Computing, 2017.
95. Matt Johnston, Eytan Modiano, Isaac Kesslassy, “ Channel Probing in Opportunistic Communications Systems ,” IEEE Transactions on Information Theory, November, 2017.
94. Anurag Rai, Georgios Paschos, Chih-Ping Lee, Eytan Modiano, " Loop-Free Backpressure Routing Using Link-Reversal Algorithms ", IEEE/ACM Transactions on Networking, October, 2017.
93. Matt Johnston and Eytan Modiano, “" Controller Placement in Wireless Networks with Delayed CSI ,” IEEE/ACM Transactions on Networking, 2017.
92. Jianan Zheng, E. Modiano, D. Hay, " Enhancing Network Robustness via Shielding ,” IEEE Transactions on Networking, 2017.
91. M. Markakis, E. Modiano, J.N. Tsitsiklis, “ Delay Analysis of the Max-Weight Policy under Heavy-Tailed Traffic via Fluid Approximations ,” Mathematics of Operations Research, October, 2017.
90. Qingkai Liang and E. Modiano, “ Survivability in Time-Varying Graphs ,” IEEE Transactions on Mobile Computing, 2017.
89. A. Sinha, G. Paschos, C. P. Li, and E. Modiano, “ Throughput-Optimal Multihop Broadcast on Directed Acyclic Wireless Networks ," IEEE/ACM Transactions on Networking, Vol. 25, No. 1, Feb. 2017.
88. G. Celik, S. Borst, , P. Whiting , E. Modiano, “ Dynamic Scheduling with Reconfiguration Delays ,” Queueing Systems, 2016.
87. G. Paschos, C. P. Li, E. Modiano, K. Choumas, T. Korakis, “ In-network Congestion Control for Multirate Multicast ,” IEEE/ACM Transactions on Networking, 2016.
86. H. Seferoglu and E. Modiano, “ TCP-Aware Backpressure Routing and Scheduling ,” IEEE Transactions on Mobile Computing, 2016.
85. H. Seferoglu and E. Modiano, “ Separation of Routing and Scheduling in Backpressure-Based Wireless Networks ," IEEE/ACM Transactions on Networking, Vol. 24, No. 3, 2016.
84. M. Markakis, E. Modiano, J.N. Tsitsiklis, “ Delay Stability of Back-Pressure Policies in the presence of Heavy-Tailed Traffic ,” IEEE/ACM Transactions on Networking, 2015.
83. S. Neumayer, E. Modiano, “ Network Reliability Under Geographically Correlated Line and Disk Failure Models ,” Computer Networks, to appear, 2016.
82. S. Neumayer, E. Modiano, A. Efrat, “ Geographic Max-Flow and Min-Cut Under a Circular Disk Failure Model ,” Computer Networks, 2015.
81. Marzieh Parandehgheibi, Hyang-Won Lee, Eytan Modiano, Survivable Path Sets: A new approach to survivability in multi-layer networks ,” IEEE Journal on Lightwave Technology, 2015.
80. G. Kuperman, E. Modiano, A. Narula-Tam, “ Network Protection with Multiple Availability Guarantees ,” Computer Networks, 2015.
79. G. Kuperman, E. Modiano, A. Narula-Tam, “ Analysis and Algorithms for Partial Protection in Mesh Networks ,” IEEE/OSA Journal of Optical Communications and Networks, 2014.
78. Krishna Jagannathan, Mihalis Markakis, Eytan Modiano, John Tsitsiklis, " Throughput Optimal Scheduling over Time-Varying Channels in the presence of Heavy-Tailed Traffic ,” IEEE Transactions on Information Theory, 2014.
77. Chih-Ping Li and Eytan Modiano, “ Receiver-Based Flow Control for Networks in Overload ," IEEE/ACM Transactions on Networking, Vol. 23, No. 2, 2015.
76. Matthew Johnston, Hyang-Won Lee, Eytan Modiano, “ A Robust Optimization Approach to Backup Network Design with Random Failures ,” IEEE/ACM Transactions on Networking, Vol. 23, No. 4, 2015.
75. Guner Celik and Eytan Modiano, “ Scheduling in Networks with Time-Varying Channels and Reconfiguration Delay ," IEEE/ACM Transactions on Networking, Vol. 23, No. 1, 2015.
74. Matt Johnston, H.W. Lee, E. Modiano, “ Robust Network Design for Stochastic Traffic Demands ," IEEE Journal of Lightwave Technology, 2013.
73. Mihalis Markakis, Eytan Modiano, John Tsitsiklis, “ Max-Weight Scheduling in Queueing Networks With Heavy-Tailed Traffic, ” IEEE/ACM Transactions on Networking, 2014.
72. Kayi Lee, Hyang-Won Lee, Eytan Modiano, " Maximizing Reliability in WDM Networks through Lightpath Routing ,” IEEE ACM Transactions on Networking, 2014.
71. Krishna Jaggannathan and Eytan Modiano, “ The Impact of Queue Length Information on Buffer Overflow in Parallel Queues ,” IEEE transactions on Information Theory, 2013.
70. Krishna Jagannathan, Ishai Menashe, Gil Zussman, Eytan Modiano, “ Non-cooperative Spectrum Access - The Dedicated vs. Free Spectrum Choice ,” IEEE JSAC, special issue on Economics of Communication Networks & Systems, to appear, 2012.
69. Guner Celik and Eytan Modiano, “ Dynamic Server Allocation over Time Varying Channels with Switchover Delay ," IEEE Transactions on Information Theory, to appear, 2012.
68. Anand Srinivas and Eytan Modiano, " Joint Node Placement and Assignment for Throughput Optimization in Mobile Backbone Networks ,” IEEE JSAC, special issue on Communications Challenges and Dynamics for Unmanned Autonomous Vehicles, June, 2012.
67. Guner Celik and Eytan Modiano, “ Controlled Mobility in Stochastic and Dynamic Wireless Networks ," Queueing Systems, 2012.
66. Krishna Jagannathan, Shie Mannor, Ishai Menache, Eytan Modiano, “ A State Action Frequency Approach to Throughput Maximization over Uncertain Wireless Channels ,” Internet Mathematics, Vol. 9, Nos. 2–3: 136–160.
65. Long Le, E. Modiano, N. Shroff, “Optimal Control of Wireless Networks with Finite Buffers ,” IEEE/ACM Transactions on Networking, to appear, 2012.
64. K. Jagannathan, M. Markakis, E. Modiano, J. Tsitsiklis, “Queue Length Asymptotics for Generalized Max-Weight Scheduling in the presence of Heavy-Tailed Traffic,” IEEE/ACM Transactions on Networking, Vol. 20, No. 4, August 2012.
63. Kayi Lee, Hyang-Won Lee, Eytan Modiano, “ Reliability in Layered Networks with Random Link Failures, ” IEEE/ACM Transactions on Networking, December 2011.
62. Krishna Jagannathan, Eytan Modiano, Lizhong Zheng, “ On the Role of Queue Length Information in Network Control ,” IEEE Transactions on Information Theory, September 2011.
61. Hyang-Won Lee, Long Le, Eytan Modiano, “ Distributed Throughput Maximization in Wireless Networks via Random Power Allocation, ” IEEE Transactions on Mobile Computing, 2011.
60. Sebastian Neumayer, Gil Zussman, Rueven Cohen, Eytan Modiano, " Assessing the Vulnerability of the Fiber Infrastructure to Disasters, " IEEE/ACM Transactions on Networking, December 2011.
59. Kayi Lee, Eytan Modiano, Hyang-Won Lee, “ Cross Layer Survivability in WDM-based Networks ,” IEEE/ACM Transactions on Networking, August 2011.
58. Emily Craparo, Jon How, and Eytan Modiano, “Throughput Optimization in Mobile Backbone Networks,” IEEE Transactions on Mobile Computing, April, 2011.
57. Hyang-Won Lee, Kayi Lee, and Eytan Modiano, “Diverse Routing in Networks with Probabilistic Failures,” IEEE/ACM Transactions on Networking, December, 2010.
56. Guner Celik, Gil Zussman, Wajahat Khan and Eytan Modiano, “MAC Protocols For Wireless Networks With Multi-packet Reception Cabaility ,” IEEE Transactions on Mobile Computing, February, 2010.
55. Atilla Eryilmaz, Asuman Ozdaglar, Devavrat Shah, and Eytan Modiano, “Distributed Cross-Layer Algorithms for the Optimal Control of Multi-hop Wireless Networks,” IEEE/ACM Transactions on Networking, April 2010.
54. Murtaza Zafer and Eytan Modiano, “Minimum Energy Transmission over a Wireless Channel With Deadline and Power Constraints ,” IEEE Transactions on Automatic Control, pp. 2841-2852, December, 2009.
53. Murtaza Zafer and Eytan Modiano, “A Calculus Approach to Energy-Efficient Data Transmission with Quality of Service Constraints,” IEEE/ACM Transactions on Networking, 2009.
52. Anand Srinivas, Gil Zussman, and Eytan Modiano, “Construction and Maintenance of Wireless Mobile Backbone Networks,” IEEE/ACM Transactions on Networking, 2009.
51. Andrew Brzezinski, Gil Zussman, and Eytan Modiano, “Distributed Throughput Maximization in Wireless Mesh Networks Via Pre-Partitioning,” IEEE/ACM Transactions on Networking, December, 2008.
50. Amir Khandani, Eytan Modiano, Jinane Abounadi, Lizhong Zheng, “Reliability and Route Diversity in Wireless Networks,” IEEE Transactions on Wireless Communications, December, 2008.
49. Alessandro Tarello, Jun Sun, Murtaza Zafer and Eytan Modiano, “Minimum Energy Transmission Scheduling Subject to Deadline Constraints,” ACM Wireless Networks, October, 2008.
48. Murtaza Zafer, Eytan Modiano, “Optimal Rate Control for Delay-Constrained Data Transmission over a Wireless Channel,” IEEE Transactions on Information Theory, September, 2008.
47. Andrew Brzezinski and Eytan Modiano, “Achieving 100% Throughput In Reconfigurable IP/WDM Networks,” IEEE/ACM Transactions on Networking, August, 2008.
46. Michael Neely, Eytan Modiano and C. Li, “Fairness and Optimal Stochastic Control for Heterogeneous Networks,” IEEE/ACM Transactions on Networking, September, 2008.
45. Amir Khandani, Jinane Abounadi, Eytan Modiano, Lizhong Zheng, “Cooperative Routing in Static Wireless Networks,” IEEE Transactions on Communications, November 2007.
44. Murtaza Zafer, Eytan Modiano, “Joint Scheduling of Rate-guaranteed and Best-effort Users over a Wireless Fading Channel,” IEEE Transactions on Wireless Communications, October, 2007.
43. Krishna Jagannathan, Sem Borst, Phil Whiting and Eytan Modiano, “Scheduling of Multi-Antenna Broadcast Systems with Heterogeneous Users,” IEEE Journal of Selected Areas in Communications, September, 2007.Amir Khandani, Jinane
42. Anand Ganti, Eytan Modiano, and John Tsitsiklis, “Optimal Transmission Scheduling in Symmetric Communication Models with Intermittent Connectivity, ” IEEE Transactions on Information Theory, March, 2007.
41. Michael Neely and Eytan Modiano, “Logarithmic Delay for NxN Packet Switches Under Crossbar Constraints,” IEEE/ACM Transactions on Networking, November, 2007.
40. Jun Sun, Jay Gao, Shervin Shambayati and Eytan Modiano, “Ka-Band Link Optimization with Rate Adaptation for Mars and Lunar Communications,” International Journal of Satellite Communications and Networks, March, 2007.
39. Jun Sun and Eytan Modiano, "Fair Allocation of A Wireless Fading Channel: An Auction Approach" Institute for Mathematics and its Applications, Volume 143: Wireless Communications, 2006.
38. Jun Sun, Eytan Modiano and Lizhong Zhang, “Wireless Channel Allocation Using An Auction Algorithm,” IEEE Journal on Selected Areas in Communications, May, 2006.
37. Murtaza Zafer and Eytan Modiano, "Blocking Probability and Channel Assignment for Connection Oriented Traffic in Wireless Networks," IEEE Transactions on Wireless Communications, April, 2006.
36. Alvin Fu, Eytan Modiano, and John Tsitsiklis, "Optimal Transmission Scheduling over a fading channel with Energy and Deadline Constraints" IEEE Transactions on Wireless Communications, March,2006.
35. Poompat Saengudomlert, Eytan Modiano and Rober Gallager, “On-line Routing and Wavelength Assignment for Dynamic Traffic in WDM Ring and Torus Networks,” IEEE Transactions on Networking, April, 2006.
34. Li-Wei Chen, Eytan Modiano and Poompat Saengudomlert, "Uniform vs. Non-Uniform band Switching in WDM Networks," Computer Networks (special issue on optical networks), January, 2006.
33. Andrew Brzezinski and Eytan Modiano, "Dynamic Reconfiguration and Routing Algorithms for IP-over-WDM networks with Stochastic Traffic," IEEE Journal of Lightwave Technology, November, 2005
32. Randall Berry and Eytan Modiano, "Optimal Transceiver Scheduling in WDM/TDM Networks," IEEE Journal on Selected Areas in Communications, August, 2005.
31. Poompat Saengudomlert, Eytan Modiano, and Robert G. Gallager, “Dynamic Wavelength Assignment for WDM All-Optical Tree Networks,” IEEE Transactions on Networking, August, 2005.
30. Ashwinder Ahluwalia and Eytan Modiano, "On the Complexity and Distributed Construction of Energy Efficient Broadcast Trees in Wireless Ad Hoc Networks," IEEE Transactions on Wireless Communications, October, 2005.
29. Michael Neely, Charlie Rohrs and Eytan Modiano, "Equivalent Models for Analysis of Deterministic Service Time Tree Networks," IEEE Transactions on Information Theory, October, 2005.
28. Michael Neely and Eytan Modiano, "Capacity and Delay Tradeoffs for Ad Hoc Mobile Networks," IEEE Transactions on Information Theory, May, 2005.
27. Li-Wei Chen and Eytan Modiano, "Efficient Routing and Wavelength Assignment for Reconfigurable WDM Networks with Wavelength Converters," IEEE/ACM Transactions on Networking, February, 2005. Selected as one of the best papers from Infocom 2003 for fast-track publication in IEEE/ACM Transactions on Networking.
26. Michael Neely and Eytan Modiano, "Convexity in Queues with General Inputs," IEEE Transactions on Information Theory, May, 2005.
25. Anand Srinivas and Eytan Modiano, "Finding Minimum Energy Disjoint Paths in Wireless Ad Hoc Networks," ACM Wireless Networks, November, 2005. Selected to appear in a special issue dedicated to best papers from Mobicom 2003.
24. Michael Neely, Eytan Modiano and Charlie Rohrs, "Dynamic Power Allocation and Routing for Time-Varying Wireless Networks," IEEE Journal of Selected Areas in Communication, January, 2005.
23. Chunmei Liu and Eytan Modiano, "On the performance of additive increase multiplicative decrease (AIMD) protocols in hybrid space-terrestrial networks," Computer Networks, September, 2004.
22. Li-Wei Chen and Eytan Modiano, "Dynamic Routing and Wavelength Assignment with Optical Bypass using Ring Embeddings," Optical Switching and Networking (Elsevier), December, 2004.
21. Aradhana Narula-Tam, Eytan Modiano and Andrew Brzezinski, "Physical Topology Design for Survivable Routing of Logical Rings in WDM-Based Networks," IEEE Journal of Selected Areas in Communication, October, 2004.
20. Randall Berry and Eytan Modiano, "'The Role of Switching in Reducing the Number of Electronic Ports in WDM Networks," IEEE Journal of Selected Areas in Communication, October, 2004.
19. Jun Sun and Eytan Modiano, "Routing Strategies for Maximizing Throughput in LEO Satellite Networks,," IEEE JSAC, February, 2004.
18. Jun Sun and Eytan Modiano, "Capacity Provisioning and Failure Recovery for Low Earth Orbit Satellite Networks," International Journal on Satellite Communications, June, 2003.
17. Alvin Fu, Eytan Modiano, and John Tsitsiklis, "Optimal Energy Allocation and Admission Control for Communications Satellites," IEEE Transactions on Networking, June, 2003.
16. Michael Neely, Eytan Modiano and Charles Rohrs, "Power Allocation and Routing in Multi-Beam Satellites with Time Varying Channels," IEEE Transactions on Networking, February, 2003.
15. Eytan Modiano and Aradhana Narula-Tam, "Survivable lightpath routing: a new approach to the design of WDM-based networks," IEEE Journal of Selected Areas in Communication, May 2002.
14. Aradhana Narula-Tam, Phil Lin and Eytan Modiano, "Efficient Routing and Wavelength Assignment for Reconfigurable WDM Networks," IEEE Journal of Selected Areas in Communication, January, 2002.
13. Brett Schein and Eytan Modiano, "Quantifying the benefits of configurability in circuit-switched WDM ring networks with limited ports per node," IEEE Journal on Lightwave Technology, June, 2001.
12. Aradhana Narula-Tam and Eytan Modiano, "Dynamic Load Balancing in WDM Packet Networks with and without Wavelength Constraints," IEEE Journal of Selected Areas in Communications, October 2000.
11. Randy Berry and Eytan Modiano, "Reducing Electronic Multiplexing Costs in SONET/WDM Rings with Dynamically Changing Traffic," IEEE Journal of Selected Areas in Communications, October 2000.
10. Eytan Modiano and Richard Barry, "A Novel Medium Access Control Protocol for WDM-Based LANs and Access Networks Using a Master-Slave Scheduler," IEEE Journal on Lightwave Technology, April 2000.
9. Eytan Modiano and Anthony Ephremides, "Communication Protocols for Secure Distributed Computation of Binary Functions," Information and Computation, April 2000.
8. Angela Chiu and Eytan Modiano, "Traffic Grooming Algorithms for Reducing Electronic Multiplexing Costs in WDM Ring Networks," IEEE Journal on Lightwave Technology, January 2000.
7. Eytan Modiano, "An Adaptive Algorithm for Optimizing the Packet Size Used in Wireless ARQ Protocols," Wireless Networks, August 1999.
6. Eytan Modiano, "Random Algorithms for Scheduling Multicast Traffic in WDM Broadcast-and-Select Networks," IEEE Transactions on Networking, July, 1999.
5. Eytan Modiano and Richard Barry, "Architectural Considerations in the Design of WDM-based Optical Access Networks," Computer Networks, February 1999.
4. V.W.S. Chan, K. Hall, E. Modiano and K. Rauschenbach, "Architectures and Technologies for High-Speed Optical Data Networks," IEEE Journal of Lightwave Technology, December 1998.
3. Eytan Modiano and Anthony Ephremides, "Efficient Algorithms for Performing Packet Broadcasts in a Mesh Network," IEEE Transactions on Networking, May 1996.
2. Eytan Modiano, Jeffrey Wieselthier and Anthony Ephremides, "A Simple Analysis of Queueing Delay in a Tree Network of Discrete-Time Queues with Constant Service Times," IEEE Transactions on Information Theory, February 1996.
1. Eytan Modiano and Anthony Ephremides, "Communication Complexity of Secure Distributed Computation in the Presence of Noise," IEEE Transactions on Information Theory, July 1992.
Other Papers
5. Eytan Modiano, "Satellite Data Networks," AIAA Journal on Aerospace Computing, Information and Communication, September, 2004.
4. Eytan Modiano and Phil Lin, "Traffic Grooming in WDM networks," IEEE Communications Magazine, July, 2001.
3. Eytan Modiano and Aradhana Narula, "Mechanisms for Providing Optical Bypass in WDM-based Networks," SPIE Optical Networks, January 2000.
2. K. Kuznetsov, N. M. Froberg, Eytan Modiano, et. al., "A Next Generation Optical Regional Access Networks," IEEE Communications Magazine, January, 2000.
1. Eytan Modiano, "WDM-based Packet Networks," (Invited Paper) IEEE Communications Magazine, March 1999.
Conference Papers
246. Xinyu Wu, Dan Wu, Eytan Modiano, “ Overload Balancing in Single-Hop Networks With Bounded Buffers ,” IFIP Networking, 2022.
245. Xinzhe Fu, Eytan Modiano, “ Optimal Routing for Stream Learning Systems ,” IEEE Infocom, April 2022.
244. Vishrant Tripathi, Luca Ballotta, Luca Carlone, E. Modiano, “ Computation and Communication Co-Design for Real-Time Monitoring and Control in Multi-Agent Systems ,” IEEE Wiopt, 2021.
243. Eray Atay, Igor Kadota, E. Modiano, “ Aging Wireless Bandits: Regret Analysis and Order-Optimal Learning Algorithm ,” IEEE Wiopt 2021.
242. Xinzhe Fu and E. Modiano, “ Elastic Job Scheduling with Unknown Utility Functions ,” IFIP Performance, Milan, 2021.
241. Bai Liu and E. Modiano, “ Optimal Control for Networks with Unobservable Malicious Nodes ,” IFIP Performance, Milan, 2021.
240. Bai Liu, Qiaomin Xie, Eytan Modiano, “ RL-QN: A Reinforcement Learning Framework for Optimal Control of Queueing Systems ,” ACM Sigmetrics Workshop on Reinforcement Learning in Networks and Queues (RLNQ), 2021.
239. Xinzhe Fu and E. Modiano, “ Learning-NUM: Network Utility Maximization with Unknown Utility Functions and Queueing Delay , ACM MobiHoc 2021.
238. Vishrant Tripathi and Eytan Modiano, “ An Online Learning Approach to Optimizing Time-Varying Costs of AoI ,” ACM MobiHoc 2021.
237. Igor Kadota, Muhammad Shahir Rahman, and Eytan Modiano, " WiFresh: Age-of-Information from Theory to Implementation ,” International Conference on Computer Communications and Networks (ICCCN), 2021.
236. Vishrant Tripathi and Eytan Modiano, “ Age Debt: A General Framework For Minimizing Age of Information ,” IEEE Infocom Workshop on Age-of-Information, 2021.
235. Igor Kadota, Eytan Modiano, “ Age of Information in Random Access Networks with Stochastic Arrivals ,” IEEE Infocom, 2020.
234. Igor Kadota, M. Shahir Rahman, Eytan Modiano, Poster: Age of Information in Wireless Networks: from Theory to Implementation , ACM Mobicom, 2020.
233. Xinyu Wu, Dan Wu, Eytan Modiano, “ An Influence Model Approach to Failure Cascade Prediction in Large Scale Power Systems ,” IEEE American Control Conference, July, 2020.
232. X. Fu and E. Modiano, " Fundamental Limits of Volume-based Network DoS Attacks ," Proc. ACM Sigmetrics, Boston, MA, June 2020.
231. Vishrant Tripathi, Eytan Modiano, “ A Whittle Index Approach to Minimizing Functions of Age of Information ,” Allerton Conference on Communication, Control, and Computing, September 2019.
230. Bai Liu, Xiaomin Xie, Eytan Modiano, “ Reinforcement Learning for Optimal Control of Queueing Systems ,” Allerton Conference on Communication, Control, and Computing, September 2019.
229. Rajat Talak, Sertac Karaman, Eytan Modiano, “ A Theory of Uncertainty Variables for State Estimation and Inference ,” Allerton Conference on Communication, Control, and Computing, September 2019.
228. Rajat Talak, Eytan Modiano, “ Age-Delay Tradeoffs in Single Server Systems ,” IEEE International Symposium on Information Theory, Paris, France, July, 2019.
227. Rajat Talak, Sertac Karaman, Eytan Modiano, “ When a Heavy Tailed Service Minimizes Age of Information ,” IEEE International Symposium on Information Theory, Paris, France, July, 2019.
226. Qingkai Liang, Eytan Modiano, “ Optimal Network Control with Adversarial Uncontrollable Nodes ,” ACM MobiHoc, Catania, Italy, June 2019.
225. Igor Kadota, Eytan Modiano, “ Minimizing the Age of Information in Wireless Networks with Stochastic Arrivals ,” ACM MobiHoc, June 2019.
224. Maotong Xu, Jelena Diakonikolas, Suresh Subramaniam, Eytan Modiano, “ A Hierarchical WDM-based Scalable Data Center Network Architecture ,” IEEE International Conference on Communications (ICC), Shanghai, China, June 2019.
223. Maotong Xu, Min Tian, Eytan Modiano, Suresh Subramaniam, " RHODA Topology Configuration Using Bayesian Optimization
222. Anurag Rai, Rahul Singh and Eytan Modiano, " A Distributed Algorithm for Throughput Optimal Routing in Overlay Networks ,” IFIP Networking 2019, Warsaw, Poland, May 2019.
221. Qingkai Liang and Eytan Modiano, " Optimal Network Control in Partially-Controllable Networks ,” IEEE Infocom, Paris, April 2019.
220. Xinzhe Fu and Eytan Modiano, " Network Interdiction Using Adversarial Traffic Flows ,” IEEE Infocom, Paris, April 2019.
219. Vishrant Tripathi, Rajat Talak, Eytan Modiano, " Age Optimal Information Gathering and Dissemination on Graphs ,” IEEE Infocom, Paris, April 2019.
218. Jianan Zhang, Hyang-Won Lee, Eytan Modiano, " On the Robustness of Distributed Computing Networks ,” DRCN 2019, Coimbra, Portugal, March, 2019.
217. Hyang-Won Lee, Jianan Zhang and Eytan Modiano, " Data-driven Localization and Estimation of Disturbance in the Interconnected Power System ,” IEEE Smartgridcomm, October, 2018.
216. Jianan Zhang and Eytan Modiano, " Joint Frequency Regulation and Economic Dispatch Using Limited Communication ,” IEEE Smartgridcomm, October, 2018.
215. Rajat Talak, Sertac Karaman, Eytan Modiano, " Scheduling Policies for Age Minimization in Wireless Networks with Unknown Channel State ,” IEEE International Symposium on Information Theory, July 2018.
214. Thomas Stahlbuhk, Brooke Shrader, Eytan Modiano, " Online Learning Algorithms for Minimizing Queue Length Regret ,” IEEE International Symposium on Information Theory, July 2018.
213. Rajat Talak, Sertac Karaman, Eytan Modiano, " Distributed Scheduling Algorithms for Optimizing Information Freshness in Wireless Networks ,” IEEE SPAWC, Kalamata, Greece, June, 2018.
212. Rajat Talak, Sertac Karaman, Eytan Modiano, " Optimizing Information Freshness in Wireless Networks under General Interference Constraints ,” ACM MobiHoc 2018, Los Angeles, CA, June 2018.
211. Thomas Stahlbuhk, Brooke Shrader, Eytan Modiano, " Learning Algorithms for Scheduling in Wireless Networks with Unknown Channel Statistics ,” ACM MobiHoc, June 2018.
210. Khashayar Kamran, Jianan Zhang, Edmund Yeh, Eytan Modiano, " Robustness of Interdependent Geometric Networks Under Inhomogeneous Failures ,” Workshop on Spatial Stochastic Models for Wireless Networks (SpaSWiN), Shanghai, China, May 2018.
209. Rajat Talak, Sertac Karaman, Eytan Modiano, " Optimizing Age of Information in Wireless Networks with Perfect Channel State Information ,” Wiopt 2018, Shanghai, China, May 2018.
208. Abhishek Sinha, Eytan Modiano, " Network Utility Maximization with Heterogeneous Traffic Flows ,” Wiopt 2018, Shanghai, China, May 2018.
207. Qingkai Liang, Eytan Modiano, " Minimizing Queue Length Regret Under Adversarial Network Models ,” ACM Sigmetrics, 2018.
206. Jianan Zhang, Abhishek Sinha, Jaime Llorca, Anonia Tulino, Eytan Modiano, " Optimal Control of Distributed Computing Networks with Mixed-Cast Traffic Flows ,” IEEE Infocom, Honolulu, HI, April 2018.
205. Qingkai Liang, Eytan Modiano, " Network Utility Maximization in Adversarial Environments ,” IEEE Infocom, Honolulu, HI, April 2018.
204. Igor Kadota, Abhishek Sinha, Eytan Modiano, " Optimizing Age of Information in Wireless Networks with Throughput Constraints ,” IEEE Infocom, Honolulu, HI, April 2018.
203. QIngkai Liang, Verina (Fanyu) Que, Eytan Modiano, " Accelerated Primal-Dual Policy Optimization for Safe Reinforcement Learning ,” NIPS workshop on “Transparent and interpretable machine learning in safety critical environments,"December 2017.
202. Rahul Singh, Xueying Guo,Eytan Modiano, " Risk-Sensitive Optimal Control of Queues ,” IEEE Conference on Decision and Control (CDC), December 2017.
201. Rajat Talak, Sertac Karaman, Eytan Modiano, " Minimizing Age of Information in Multi-Hop Wireless Networks ,” Allerton Conference on Communication, Control, and Computing, September 2017.
200. Abhishek Sinha, Eytan Modiano, " Throughput-Optimal Broadcast in Wireless Networks with Point-to-Multipoint Transmissions ,” ACM MobiHoc, Madras, India, July 2017.
199. Rajat Talak, Sertac Karaman, Eytan Modiano, " Capacity and delay scaling for broadcast transmission in highly mobile wireless networks ,” ACM MobiHoc, Madras, India, July 2017.
198.5 . Y.-P. Hsu, E. Modiano, and L. Duan, " Age of Information: Design and Analysis of Optimal Scheduling Algorithms ,” IEEE International Symposium on Information Theory (ISIT), 2017.
198. Qingkai Liang and Eytan Modiano, " Coflow Scheduling in Input-Queued Switches: Optimal Delay Scaling and Algorithms ,” IEEE Infocom, Atlanta, GA, May 2017.
197. Jianan Zhang and Eytan Modiano, " Robust Routing in Interdependent Networks ,” IEEE Infocom, Atlanta, GA, May 2017.
196. Abhishek Sinha, Eytan Modiano, " Optimal Control for Generalized Network Flow Problems ,” IEEE Infocom, Atlanta, GA, May 2017.
195. Rajat Talak*, Sertac Karaman, Eytan Modiano, " Speed Limits in Autonomous Vehicular Networks due to Communication Constraints ,” IEEE Conference on Decision and Control (CDC), Las Vegas, NV, December 2016.
194. Marzieh Parandehgheibi*, Konstantin Turitsyn, Eytan Modiano, " Distributed Frequency Control in Power Grids Under Limited Communication ,” IEEE Conference on Decision and Control (CDC), Las Vegas, NV, December 2016.
193. Igor Kadota, Elif Uysal-Biyikoglu, Rahul Singh, Eytan Modiano, " Minimizing Age of Information in Broadcast Wireless Networks ,” Allerton Allerton Conference on Communication, Control, and Computing, September 2016.
192. Jianan Zhang, Edmund Yeh, Eytan Modiano, " Robustness of Interdependent Random Geometric Networks ,” Allerton Conference on Communication, Control, and Computing, September 2016.
191. Abhishek Sinha, Leandros Tassiulas, Eytan Modiano, " Throughput-Optimal Broadcast in Wireless Networks with Dynamic Topology ,” ACM MobiHoc'16, Paderborn, Germany, July, 2016. (winner of best paper award)
190. Abishek Sinha, Georgios Paschos, Eytan Modiano, " Throughput-Optimal Multi-hop Broadcast Algorithms ,” ACM MobiHoc'16, Paderborn, Germany, July, 2016.
189. Thomas Stahlbuhk, Brooke Shrader, Eytan Modiano, " Throughput Maximization in Uncooperative Spectrum Sharing Networks ,” IEEE International Symposium on Information Theory, Barcelona, Spain, July 2016.
188. Thomas Stahlbuhk, Brooke Shrader, Eytan Modiano, " Topology Control for Wireless Networks with Highly-Directional Antennas ,” IEEE Wiopt, Tempe, Arizona, May, 2016.
187. Qingkai Liang, H.W. Lee, Eytan Modiano, " Robust Design of Spectrum-Sharing Networks ,” IEEE Wiopt, Tempe, Arizona, May, 2016.
186. Hossein Shokri-Ghadikolae, Carlo Fischione and Eytan Modiano, " On the Accuracy of Interference Models in Wireless Communications ,” IEEE International Conference on Communications (ICC), 2016.
185. Qingkai Liang and Eytan Modiano, " Survivability in Time-varying Networks ,” IEEE Infocom, San Francisco, CA, April 2016.
184. Kyu S. Kim, Chih-Ping Li, Igor Kadota, Eytan Modiano, " Optimal Scheduling of Real-Time Traffic in Wireless Networks with Delayed Feedback ,” Allerton conference on Communication, Control, and Computing, September 2015.
183. Marzieh Parandehgheibi, Eytan Modiano, " Modeling the Impact of Communication Loss on the Power Grid Under Emergency Control ,” IEEE SmartGridComm, Miami, FL, Nov. 2015.
182. Anurag Rai, Chih-ping Li, Georgios Paschos, Eytan Modiano, " Loop-Free Backpressure Routing Using Link-Reversal Algorithms ,” Proceedings of the ACM MobiHoc, July 2015.
181. Longbo Huang, Eytan Modiano, " Optimizing Age of Information in a Multiclass Queueing System ,” Proceedings of IEEE ISIT 2015, Hong Kong, Jun 2015.
180. M. Johnston, E. Modiano, " A New Look at Wireless Scheduling with Delayed Information ,” Proceedings of IEEE ISIT 2015, Hong Kong, June 2015.
179. M. Johnston, E. Modiano, " Scheduling over Time Varying Channels with Hidden State Information ,” Proceedings of IEEE ISIT 2015, Hong Kong, June 2015.
178. M. Johnston and E. Modiano, " Controller Placement for Maximum Throughput Under Delayed CSI ,” IEEE Wiopt, Mombai, India, May 2015.
177. A. Sinha, G. Paschos, C. P. Li, and E. Modiano, " Throughput Optimal Broadcast on Directed Acyclic Graphs ,” IEEE Infocom, Hong Kong, April 2015.
176. J. Zheng and E. Modiano, " Enhancing Network Robustness via Shielding ,” IEEE Design of Reliable Communication Networks, Kansas City, March 2015.
175. H. W. Lee and E. Modiano, " Robust Design of Cognitive Radio Networks ,” Information and Communication Technology Convergence (ICTC), 2014.
174. Greg Kuperman and Eytan Modiano, " Disjoint Path Protection in Multi-Hop Wireless Networks with Interference Constraints ,” IEEE Globecom, Austin, TX, December 2014.
173. Marzieh Parandehgheibi, Eytan Modiano, David Hay, " Mitigating Cascading Failures in Interdependent Power Grids and Communication Networks ,” IEEE Smartgridcomm, Venice, Italy, November 2014.
172. Georgios Paschos and Eytan Modiano, " Throughput optimal routing in overlay networks ,” Allerton conference on Communication, Control, and Computing, September 2014.
171. Nathan Jones, George Paschos, Brooke Shrader, Eytan Modiano, " An overlay architecture for Throughput Optimal Multipath Routing ,” ACM MobiHoc, August 2014.
170. Matt Johnston, Eytan Modiano, Yuri Polyanskiy, " Opportunistic Scheduling with Limited Channel State Information: A Rate Distortion Approach ,” IEEE International Symposium on Information Theory, Honolulu, HI, July 2014.
169. Chih-Ping Li, Georgios Paschos, Eytan Modiano, Leandros Tassiulas, " Dynamic Overload Balancing in Server Farms ,” Networking 2014, Trondheim, Norway, June, 2014.
168. Hulya Seferonglu and Eytan Modiano, " TCP-Aware Backpressure Routing and Scheduling ,” Information Theory and Applications, San Diego, CA, February 2014.
167. Mihalis Markakis, Eytan Modiano, John Tsitsiklis, " Delay Stability of Back-Pressure Policies in the presence of Heavy-Tailed Traffic ,” Information Theory and Applications, San Diego, CA, February 2014.
166. Kyu Soeb Kim, Chih-ping Li, Eytan Modiano, " Scheduling Multicast Traffic with Deadlines in Wireless Networks ,” IEEE Infocom, Toronto, CA, April 2014.
165. Georgios Paschos, Chih-ping Li, Eytan Modiano, Kostas Choumas, Thanasis Korakis, " A Demonstration of Multirate Multicast Over an 802.11 Mesh Network ,” IEEE Infocom, Toronto, CA, April 2014.
164. Sebastian Neumayer, Eytan Modiano, " Assessing the Effect of Geographically Correlated Failures on Interconnected Power-Communication Networks ,” IEEE SmartGridComm, 2013.
163. Marzieh Parandehgheibi, Eytan Modiano, " Robustness of Interdependent Networks: The case of communication networks and the power grid ,” IEEE Globecom, December 2013.
162. Matt Johnston, Eytan Modiano, " Optimal Channel Probing in Communication Systems: The Two-Channel Case ,” IEEE Globecom, December 2013.
161. Mihalis Markakis, Eytan Modiano, John N. Tsitsiklis, " Delay Analysis of the Max-Weight Policy under Heavy-Tailed Traffic via Fluid Approximations ,” Allerton Conference, October 2013.
160. Matthew Johnston, Isaac Keslassy, Eytan Modiano, " Channel Probing in Communication Systems: Myopic Policies Are Not Always Optimal ,” IEEE International Symposium on Information Theory, July 2013.
159. Krishna P Jagannathan, Libin Jiang, Palthya Lakshma Naik, Eytan Modiano, " Scheduling Strategies to Mitigate the Impact of Bursty Traffic in Wireless Networks ,” 11th International Symposium on Modeling and Optimization in Mobile, Ad Hoc and Wireless Networks Wiopt 2013, Japan, May 2013. (Winner – Best Paper Award).
158. Hulya Seferoglu and Eytan Modiano, " Diff-Max: Separation of Routing and Scheduling in Backpressure-Based Wireless Networks ,” IEEE Infocom, Turin, Italy, April 2013.
157. Chih-Ping Li, Eytan Modiano, " Receiver-Based Flow Control for Networks in Overload ,” IEEE Infocom, Turin, Italy, April 2013.
156. Nathan Jones, Brooke Shrader, Eytan Modiano, " Distributed CSMA with Pairwise Coding ,” IEEE Infocom, Turin, Italy, April 2013.
155. Greg Kuperman and Eytan Modiano, " Network Protection with Guaranteed Recovery Times using Recovery Domains ,” IEEE Infocom, Turin, Italy, April 2013.
154. Greg Kuperman and Eytan Modiano, " Providing Protection in Multi-Hop Wireless Networks ,” IEEE Infocom, Turin, Italy, April 2013.
153. Greg Kuperman, Eytan Modiano, Aradhana Narula-Tam, " Network Protection with Multiple Availability Guarantees ,” IEEE ICC workshop on New Trends in Optical Networks Survivability, June 2012.
152. Nathaniel Jones, Brooke Shrader, Eytan Modiano, " Optimal Routing and Scheduling for a Simple Network Coding Scheme ,” IEEE Infocom, Orlando, Fl, March, 2012.
151. Mihalis Markakis, Eytan Modiano, John Tsitsiklis, " Max-Weight Scheduling in Networks with Heavy-Tailed Traffic ,” IEEE Infocom, Orlando, Fl, March, 2012.
150. Guner Celik and Eytan Modiano, " Scheduling in Networks with Time-Varying Channels and Reconfiguration Delay ,” IEEE Infocom, Orlando, Fl, March, 2012.
149. Sebastian Neumayer, Alon Efrat, Eytan Modiano, " Geographic Max-Flow and Min-cut Under a Circular Disk Failure Model ,” IEEE Infocom (MC), Orlando, Fl, March, 2012.
148. Marzieh Parandehgheibi, Hyang-Won Lee, and Eytan Modiano, " Survivable Paths in Multi-Layer Networks ,” Conference on Information Science and Systems, March, 2012.
147. Greg Kuperman, Eytan Modiano, and Aradhana Narula-Tam, " Partial Protection in Networks with Backup Capacity Sharing ,” Optical Fiber Communications Conference (OFC), Anaheim, CA, March, 2012.
146. Krishna Jagannathan, Libin Jiang, Eytan Modiano, " On Scheduling Algorithms Robust to Heavy-Tailed Traffic ,” Information Theory and Applications (ITA), San Diego, CA, February 2012.
145. M. Johnston, H.W. Lee, E. Modiano, " Robust Network Design for Stochastic Traffic Demands ,” IEEE Globecom, Next Generation Networking Symposium, Houston, TX, December 2011.
144. S. Neumayer, E. Modiano, " Network Reliability Under Random Circular Cuts ,” IEEE Globecom, Optical Networks and Systems Symposium, Houston, TX, December 2011.
143. H.W. Lee, K. Lee, E. Modiano, " Maximizing Reliability in WDM Networks through Lightpath Routing ,” IEEE Globecom, Optical Networks and Systems Symposium, Houston, TX, December 2011.
142. Guner Celik, Sem Borst, Eytan Modiano, Phil Whiting, " Variable Frame Based Max-Weight Algorithms for Networks with Switchover Delay ,” IEEE International Symposium on Information Theory, St. Petersburgh, Russia, August 2011.
141. Krishna Jaganathan, Ishai Menache, Eytan Modiano, and Gil Zussman, " Non-cooperative Spectrum Access - The Dedicated vs. Free Spectrum Choice ,” ACM MOBIHOC'11, May 2011.
140. Krishna Jagannathan, Shie Mannor, Ishai Menache, Eytan Modiano, " A State Action Frequency Approach to Throughput Maximization over Uncertain Wireless Channels ,” IEEE Infocom (Mini-conference), Shanghai, China, April 2011.
139. Guner Celik, Long B. Le, Eytan Modiano, " Scheduling in Parallel Queues with Randomly Varying Connectivity and Switchover Delay ,” IEEE Infocom (Mini-conference), Shanghai, China, April 2011.
138. Gregory Kuperman, Eytan Modiano, Aradhana Narula-Tam, " Analysis and Algorithms for Partial Protection in Mesh Networks ,” IEEE Infocom (Mini-conference), Shanghai, China, April 2011.
137. Matthew Johnston, Hyang-Won Lee, Eytan Modiano, " A Robust Optimization Approach to Backup Network Design with Random Failures ,” IEEE Infocom, Shanghai, China, April 2011.
136. Krishna Jagannathan, Mihalis Markakis, Eytan Modiano, John Tsitsiklis, " Queue Length Asymptotics for Generalized Max-Weight Scheduling in the presence of Heavy-Tailed Traffic ,” IEEE Infocom, Shanghai, China, April 2011.
135. Guner Celik and Eytan Modiano, " Dynamic Vehicle Routing for Data Gathering in Wireless Networks ,” In Proc. IEEE CDC'10, Dec. 2010..***
134. Long B. Le, Eytan Modiano, Changhee Joo, and Ness B. Shroff, " Longest-queue-first scheduling under the SINR interference model ,” ACM MobiHoc, September 2010..***
133. Krishna Jagannathan, Mihalis Markakis, Eytan Modiano, John Tsitsiklis, " Throughput Optimal Scheduling in the Presence of Heavy-Tailed Traffic ,” Allerton Conference on Communication, Control, and Computing, September 2010..**
132. Delia Ciullo, Guner Celik, Eytan Modiano, " Minimizing Transmission Energy in Sensor Networks via Trajectory Control ,” IEEE Wiopt 2010, Avignon, France, June 2010, (10 pages; CD proceedings – page numbers not available).
131. Sebastian Neumayer and Eytan Modiano, " Network Reliability with Geographically Correlated Failures ,” IEEE Infocom 2010, San Diego, CA, March 2010, (9 pages; CD proceedings – page numbers not available).**
130. Long Le, Eytan Modiano, Ness Shroff, " Optimal Control of Wireless Networks with Finite Buffers ,” IEEE Infocom 2010, San Diego, CA, March 2010, (9 pages; CD proceedings – page numbers not available).
129. Kayi Lee, Hyang-Won Lee, Eytan Modiano, " Reliability in Layered Network with Random Link Failures ,” IEEE Infocom 2010, San Diego, CA, March 2010, (9 pages; CD proceedings – page numbers not available).**
128. Krishna Jagannathan, Eytan Modiano, " The Impact of Queue length Information on Buffer Overflow in Parallel Queues ,” Allerton Conference on Communication, Control, and Computing, September 2009, pgs. 1103 -1110 **
127. Mihalis Markakis, Eytan Modiano, John Tsitsiklis, " Scheduling Policies for Single-Hop with Heavy-Tailed Traffic ,” Allerton Conference on Communication, Control, and Computing, September 2009, pgs. 112 – 120..**
126. Dan Kan, Aradhana Narula-Tam, Eytan Modiano, " Lightpath Routing and Capacity Assignment for Survivable IP-over-WDM Networks ,” DRCN 2009, Alexandria, VA October 2009, pgs. 37 -44..**
125. Mehdi Ansari, Alireza Bayesteh, Eytan Modiano, " Opportunistic Scheduling in Large Scale Wireless Networks ,” IEEE International Symposium on Information Theory, Seoul, Korea, June 2009, pgs. 1624 – 1628.
124. Hyang-Won Lee, Eytan Modiano and Long Bao Le, " Distributed Throughput Maximization in Wireless Networks via Random Power Allocation ,” IEEE Wiopt, Seoul, Korea, June 2009. (9 pages; CD proceedings – page numbers not available).
123. Wajahat Khan, Eytan Modiano, Long Le, " Autonomous Routing Algorithms for Networks with Wide-Spread Failures ,” IEEE MILCOM, Boston, MA, October 2009. (6 pages; CD proceedings – page numbers not available).**
122. Guner Celik and Eytan Modiano, " Random Access Wireless Networks with Controlled Mobility ,” IEEE Med-Hoc-Nets, Haifa, Israel, June 2009, pgs. 8 – 14.**
121. Hyang-Won Lee and Eytan Modiano, " Diverse Routing in Networks with Probabilistic Failures ,” IEEE Infocom, April 2009, pgs. 1035 – 1043.
120. Kayi Lee and Eytan Modiano, " Cross-layer Survivability in WDM-based Networks ,” IEEE Infocom, April 2009, pgs. 1017 -1025..**
119. Krishna Jagannathan, Eytan Modiano, Lizhong Zheng, " On the Trade-off between Control Rate and Congestion in Single Server Systems ,” IEEE Infocom, April 2009, pgs. 271 – 279.**
118. Sebastian Neumayer, Gil Zussman, Rueven Cohen, Eytan Modiano, " Assessing the Vulnerability of the Fiber Infrastructure to Disasters ,” IEEE Infocom, April 2009, pgs. 1566 – 1574.**
117. Long Le, Krishna Jagannathan and Eytan Modiano, " Delay analysis of max-weight scheduling in wireless ad hoc networks ,” Conference on Information Science and Systems, Baltimore, MD, March, 2009, pgs. 389 – 394.**
116. Krishna Jagannathan, Eytan Modiano, Lizhong Zheng, " Effective Resource Allocation in a Queue: How Much Control is Necessary? ,” Allerton Conference on Communication, Control, and Computing, September 2008, pgs. 508 – 515.**
115. Sebastian Neumayer, Gil Zussman, Rueven Cohen, Eytan Modiano, " Assessing the Impact of Geographically Correlated Network Failures ,” IEEE MILCOM, November 2008. (6 pages; CD proceedings – page numbers not available).**
114. Emily Craparo, Jonathan P. How, and Eytan Modiano, " Simultaneous Placement and Assignment for Exploration in Mobile Backbone Networks ,” IEEE conference on Decision and Control (CDC), November 2008, pgs. 1696 – 1701 **
113. Anand Srinivas and Eytan Modiano, " Joint node placement and assignment for throughput optimization in mobile backbone networks ,” IEEE INFOCOM'08, pp. 1130 – 1138, Phoenix, AZ, Apr. 2008, pgs. 1130 – 1138.**
112. Guner Celik, Gil Zussman, Wajahat Khan and Eytan Modiano, " MAC for Networks with Multipacket Reception Capability and Spatially Distributed Nodes ,” IEEE INFOCOM'08, Phoenix, AZ, Apr. 2008, pgs. 1436 – 1444.**
111. Gil Zussman, Andrew Brzezinski, and Eytan Modiano, " Multihop Local Pooling for Distributed Throughput Maximization in Wireless Networks ,” IEEE INFOCOM'08, Phoenix, AZ, Apr. 2008, pgs 1139 – 1147.**
110. Emily Craparo, Jonathan How and Eytan Modiano, " Optimization of Mobile Backbone Networks: Improved Algorithms and Approximation ,” IEEE American Control Conference, Seattle, WA, June 2008, pgs. 2016 – 2021.**
109. Atilla Eryilmaz, Asuman Ozdaglar, Devavrat Shah, Eytan Modiano, " Imperfect Randomized Algorithms for the Optimal Control of Wireless Networks ,” Conference on Information Science and Systems, Princeton, NJ, March, 2008, pgs. 932 – 937.
108. Anand Srinivas and Eytan Modiano, " Optimal Path Planning for Mobile Backbone Networks ,” Conference on Information Science and Systems, Princeton, NJ, March, 2008, pgs. 913 – 918.
107. Kayi Lee and Eytan Modiano, " Cross-layer Survivability in WDM Networks with Multiple Failures ,” IEEE Optical Fiber Communications Conference, San Diego, CA February, 2008 (3 pages; CD proceedings – page numbers not available).
106. Andrew Brzezinski, Gil Zussman and Eytan Modiano, " Local Pooling Conditions for Joint Routing and Scheduling ,” Workshop on Information Theory and Applications, pp. 499 – 506, La Jolla, CA, January, 2008, pgs. 499 – 506.
105. Murtaza Zafer and Eytan Modiano, " Minimum Energy Transmission over a Wireless Fading Channel with Packet Deadlines ,” Proceedings of IEEE Conference on Decision and Control (CDC), New Orleans, LA, December, 2007, pgs. 1148 – 1155.**
104. Atilla Eryilmaz, Asuman Ozdaglar, Eytan Modiano, " Polynomial Complexity Algorithms for Full Utilization of Multi-hop Wireless Networks ,” IEEE Infocom, Anchorage, AK, April, 2007, pgs. 499 – 507.
103. Murtaza Zafer and Eytan Modiano, " Delay Constrained Energy Efficient Data Transmission over a Wireless Fading Channel ,” Workshop on Information Theory and Application, University of California, San Diego, CA, February, 2007, pgs. 289 – 298.**
102. Atilla Eryilmaz, Eytan Modiano, Asuman Ozdaglar, " Randomized Algorithms for Throughput-Optimality and Fairness in Wireless Networks ,” Proceedings of IEEE Conference on Decision and Control (CDC), San Diego, CA, December, 2006, pgs. 1936 – 1941.
101. Anand Srinivas, Gil Zussman, and Eytan Modiano, " Distributed Mobile Disk Cover - A Building Block for Mobile Backbone Networks ,” Proc. Allerton Conf. on Communication, Control, and Computing, Allerton, IL, September 2006, (9 pages; CD proceedings – page numbers not available).**
100. Krishna Jagannathan, Sem Borst, Phil Whiting, Eytan Modiano, " Scheduling of Multi-Antenna Broadcast Systems with Heterogeneous Users ,” Allerton Conference on Communication, Control and Computing, Allerton, IL, September 2006, (10 pages; CD proceedings – page numbers not available).**
99. Andrew Brzezinski, Gil Zussman, and Eytan Modiano, " Enabling Distributed Throughput Maximization in Wireless Mesh Networks - A Partitioning Approach ,” Proceedings of ACM MOBICOM'06, Los Angeles, CA, Sep. 2006, (12 pages; CD proceedings – page numbers not available).**
98. Eytan Modiano, Devavrat Shah, and Gil Zussman, " Maximizing Throughput in Wireless Networks via Gossiping ,” Proc. ACM SIGMETRICS / IFIP Performance'06, Saint-Malo, France, June 2006, (12 pages; CD proceedings – page numbers not available). (best paper award)
97. Anand Srinivas, Gil Zussman, and Eytan Modiano, " Mobile Backbone Networks – Construction and Maintenance ,” Proc. ACM MOBIHOC'06, Florence, Italy, May 2006, (12 pages; CD proceedings – page numbers not available).**
96. Andrew Brzezinski and Eytan Modiano, " Achieving 100% throughput in reconfigurable optical networks ,” IEEE INFOCOM 2006 High-Speed Networking Workshop, Barcelona, Spain, April 2006, (5 pages; CD proceedings – page numbers not available).**
95. Krishna P. Jagannathan, Sem Borst, Phil Whiting, Eytan Modiano, " Efficient scheduling of multi-user multi-antenna systems ,” Proceedings of WiOpt 2006, Boston, MA, April 2006, (8 pages; CD proceedings – page numbers not available).**
94. Andrew Brzezinski and Eytan Modiano, " Greedy weighted matching for scheduling the input-queued switch ,” Conference on Information Sciences and Systems (CISS), Princeton, NJ, March 2006, pgs. 1738 – 1743.**
93. Murtaza Zafer and Eytan Modiano, " Optimal Adaptive Data Transmission over a Fading Channel with Deadline and Power Constraints ,” Conference on Information Sciences and Systems (CISS), Princeton, New Jersey, March 2006, pgs. 931 – 937.**
92. Li-Wei Chen and E. Modiano, " A Geometric Approach to Capacity Provisioning in WDM Networks with Dynamic Traffic ,” Conference on Information Science and Systems (CISS), Princeton, NJ, March, 2006, pgs. 1676 – 1683, **
91. Jun Sun and Eytan Modiano, " Channel Allocation Using Pricing in Satellite Networks ,” Conference on Information Science and Systems (CISS), Princeton, NJ, March, 2006, pgs. 182 – 187.**
90. Jun Sun, Jay Gao, Shervin Shambayatti and Eytan Modiano, " Ka-Band Link Optimization with Rate Adaptation ,” IEEE Aerospace Conference, Big Sky, MN, March, 2006. (7 pages; CD proceedings – page numbers not available).
89. Alessandro Tarello, Eytan Modiano and Jay Gao, " Energy efficient transmission scheduling over Mars proximity links ,” IEEE Aerospace Conference, Big Sky, MN, March, 2006. (10 pages; CD proceedings – page numbers not available).
88. A. Brzezinski and E. Modiano, " RWA decompositions for optimal throughput in reconfigurable optical networks ,” INFORMS Telecommunications Conference, Dallas, TX, March 2006 (3 pages; CD proceedings – page numbers not available).**
87. Li Wei Chen and E. Modiano, " Geometric Capacity Provisioning for Wavelength Switched WDM Networks ,” Workshop on Information Theory and Application, University of California, San Diego, CA, February, 2006. (8 pages; CD proceedings – page numbers not available).**
86. Murtaza Zafer and Eytan Modiano, " Joint Scheduling of Rate-guaranteed and Best-effort Services over a Wireless Channel ,” IEEE Conference on Decision and Control, Seville, Spain, December, 2005, pgs. 6022–6027.**
85. Jun Sun and Eytan Modiano, " Opportunistic Power Allocation for Fading Channels with Non-cooperative Users and Random Access ,” IEEE BroadNets – Wireless Networking Symposium, Boston, MA, October, 2005, pgs. 397–405.**
84. Li Wei Chen and Eytan Modiano, " Uniform vs. Non-uniform Band Switching in WDM Networks ,” IEEE BroadNets-Optical Networking Symposium, Boston, MA, October, 2005, pgs. 219– 228.**
83. Sonia Jain and Eytan Modiano, " Buffer Management Schemes for Enhanced TCP Performance over Satellite Links ,” IEEE MILCOM, Atlantic City, NJ, October 2005 (8 pages; CD proceedings – page numbers not available).**
82. Murtaza Zafer and Eytan Modiano, " Continuous-time Optimal Rate Control for Delay Constrained Data Transmission ,” Allerton Conference on Communications, Control and Computing, Allerton, IL, September, 2005 (10 pages; CD proceedings – page numbers not available).**
81. Alessandro Tarello, Eytan Modiano, Jun Sun, Murtaza Zafer, " Minimum Energy Transmission Scheduling subject to Deadline Constraints ,” IEEE Wiopt, Trentino, Italy, April, 2005, pgs. 67–76. (Winner of best student paper award).**
80. Amir Khandani, Eytan Modiano, Jinane Abounadi, Lizhong Zheng, " Reliability and Route Diversity in Wireless Networks ,” Conference on Information Science and System, Baltimore, MD, March, 2005, (8 pages; CD proceedings – page numbers not available).**
79. Andrew Brzezinski, Iraj Saniee, Indra Widjaja, Eytan Modiano, " Flow Control and Congestion Management for Distributed Scheduling of Burst Transmissions in Time-Domain Wavelength Interleaved Networks ,” IEEE/OSA Optical Fiber Conference (OFC), Anaheim, CA, March, 2005, pgs. WC4-1–WC4-3.
78. Andrew Brzezinski and Eytan Modiano, " Dynamic Reconfiguration and Routing Algorithms for IP-over-WDM Networks with Stochastic Traffic ,” IEEE Infocom 2005, Miami, FL, March, 2005, pgs. 6–11.**
77. Murtaza Zafer and Eytan Modiano, " A Calculus Approach to Minimum Energy Transmission Policies with Quality of Service Guarantees ,” IEEE Infocom 2005, Miami, FL, March, 2005, pgs. 548–559.**
76. Michael Neely and Eytan Modiano, " Fairness and optimal stochastic control for heterogeneous networks ,” IEEE Infocom 2005, Miami, FL, March, 2005, pgs. 1723 – 1734.**
75. Aradhana Narula-Tam, Thomas G. Macdonald, Eytan Modiano, and Leslie Servi, " A Dynamic Resource Allocation Strategy for Satellite Communications ,” IEEE MILCOM, Monterey, CA, October, 2004, pgs. 1415 – 1421.
74. Li-Wei Chen, Poompat Saengudomlert and Eytan Modiano, " Optimal Waveband Switching in WDM Networks ,” IEEE International Conference on Communication (ICC), Paris, France, June, 2004, pgs. 1604 – 1608.**
73. Michael Neely and Eytan Modiano, " Logarithmic Delay for NxN Packet Switches ,” IEEE Workshop on High performance Switching and Routing (HPSR 2004), Phoenix, AZ, April, 2004, pgs. 3–9.**
72. Li-Wei Chen and Eytan Modiano, " Dynamic Routing and Wavelength Assignment with Optical Bypass using Ring Embeddings ,” IEEE Workshop on High performance Switching and Routing (HPSR 2004), Phoenix, Az, April, 2004, pgs. 119–125.**
71. Randall Berry and Eytan Modiano, " On the Benefits of Tunability in Reducing Electronic Port Counts in WDM/TDM Networks ,” IEEE Infocom, Hong Kong, March 2004, pgs. 1340–1351.
70. Andrew Brzezinski and Eytan Modiano, " A new look at dynamic traffic scheduling in WDM networks with transceiver tuning latency ,” Informs Telecommunications Conference, Boca Raton, FL, March 2004, pgs. 25–26.**
69. Chunmei Liu and Eytan Modiano, " Packet Scheduling with Window Service Constraints ,” Conference on Information Science and System, Princeton, NJ, March, 2004, pgs. 178–184.**
68. Jun Sun, Eytan Modiano, and Lizhong Zheng, " A Novel Auction Algorithm for Fair Allocation of a Wireless Fading Channel ,” Conference on Information Science and System, Princeton, NJ, March, 2004, pgs. 1377–1383.**
67. Murtaza Zafer and Eytan Modiano, " Impact of Interference and Channel Assignment on Blocking Probability in Wireless Networks ,” Conference on Information Science and System, Princeton, NJ, March, 2004, pgs. 430–436.**
66. Chunmei Liu and Eytan Modiano, " An Analysis of TCP over Random Access Satellite Links ,” IEEE Wireless Communications and Networking Conference (WCNC), Atlanta, GA, February, 2004, pgs. 2033–2040..**
65. Randall Berry and Eytan Modiano, " Using tunable optical transceivers for reducing the number of ports in WDM/TDM Networks ,” IEEE/OSA Optical Fiber Conference (OFC), Los Angeles, CA, February, 2004, pgs. 23–27.
64. Aradhana Narula-Tam, Eytan Modiano and Andrew Brzezinski, " Physical Topology Design for Survivable Routiing of Logical Rings in WDM-based Networks ,” IEEE Globecom, San francisco, CA, December, 2003, pgs. 2552–2557.
63. Jun Sun, Lizhong Zheng and Eytan Modiano, " Wireless Channel Allocation Using an Auction Algorithm ,” Allerton Conference on Communications, Control and Computing, October, 2003, pgs. 1114–1123..**
62. Amir Khandani, Jinane Abounadi, Eytan Modiano, Lizhong Zhang, " Cooperative Routing in Wireless Networks ,” Allerton Conference on Communications, Control and Computing, October, 2003, pgs. 1270–1279.**
61. Poompat Saengudomlert, Eytan Modiano and Robert Gallager, " Dynamic Wavelength Assignment for WDM all optical Tree Networks ,” Allerton Conference on Communications, Control and Computing, October, 2003, 915–924.**
60. Aradhana Narula-Tam and Eytan Modiano, " Designing Physical Topologies that Enable Survivable Routing of Logical Rings ,” IEEE Workshop on Design of Reliable Communication Networks (DRCN), October, 2003, pgs. 379–386.
59. Anand Srinivas and Eytan Modiano, " Minimum Energy Disjoint Path Routing in Wireless Ad Hoc Networks ,” ACM Mobicom, San Diego, Ca, September, 2003, pgs. 122–133.**
58. Michael Neely and Eytan Modiano, " Improving Delay in Ad-Hoc Mobile Networks Via Redundant Packet Transfers ,” Conference on Information Science and System, Baltimore, MD, March, 2003 (6 pages; CD proceedings – page numbers not available).**
57. Michael Neely, Eytan Modiano and Charles Rohrs, " Dynamic Power Allocation and Routing for Time Varying Wireless Networks ,” IEEE Infocom 2003, San Francisco, CA, April, 2003, pgs. 745–755.**
56. Alvin Fu, Eytan Modiano, and John Tsitsiklis, " Optimal Energy Allocation for Delay-Constrained Data Transmission over a Time-Varying Channel ,” IEEE Infocom 2003, San Francisco, CA, April, 2003, pgs. 1095–1105.**
55. Poompat Saengudomlert, Eytan Modiano and Rober Gallager, " On-line Routing and Wavelength Assignment for Dynamic Traffic in WDM Ring and Torus Networks ,” IEEE Infocom 2003, San Francisco, CA, April, 2003, pgs. 1805–1815.**
54. Li-Wei Chen and Eytan Modiano, " Efficient Routing and Wavelength Assignment for Reconfigurable WDM Networks with Wavelength Converters ,” IEEE Infocom 2003, San Francisco, CA, April, 2003, pgs. 1785–1794. Selected as one of the best papers of Infocom 2003 for fast track publication in IEEE/ACM Transactions on Networking.**
53. Mike Neely, Jun Sun and Eytan Modiano, " Delay and Complexity Tradeoffs for Dynamic Routing and Power Allocation in a Wireless Network ,” Allerton Conference on Communication, Control, and Computing, Allerton, Illinois, October, 2002, pgs. 157 –159.**
52. Anand Ganti, Eytan Modiano and John Tsitsiklis, " Transmission Scheduling for Multi-Channel Satellite and Wireless Networks ,” Allerton Conference on Communication, Control, and Computing, Allerton, Illinois, October, 2002, pgs. 1318–1327.**
51. Poompat Saengudomlert, Eytan Modiano, and Robert G. Gallager, " Optimal Wavelength Assignment for Uniform All-to-All Traffic in WDM Tree Networks ,” Allerton Conference on Communication, Control, and Computing, Allerton, Illinois, October, 2002, pgs. 528–537.**
50. Hungjen Wang, Eytan Modiano and Muriel Medard, " Partial Path Protection for WDM Networks: End-to-End Recovery Using Local Failure Information ,” IEEE International Symposium on Computer Communications (ISCC), Taormina, Italy, July 2002, pgs. 719–725.**
49. Jun Sun and Eytan Modiano, " Capacity Provisioning and Failure Recovery in Mesh-Torus Networks with Application to Satellite Constellations ,” IEEE International Symposium on Computer Communications (ISCC), Taormina, Italy, July 2002, pgs. 77–84.**
48. Alvin Fu, Eytan Modiano, and John Tsitsiklis, " Optimal Energy Allocation and Admission Control for Communications Satellites ,” IEEE INFOCOM 2002, New York, June, 2002, pgs. 648–656.**
47. Michael Neely, Eytan Modiano and Charles Rohrs, " Power and Server Allocation in a Multi-Beam Satellite with Time Varying Channels ,” IEEE INFOCOM 2002, New York, June, 2002, pgs. 1451–1460..**
46. Mike Neely, Eytan Modiano and Charles Rohrs, " Tradeoffs in Delay Guarantees and Computation Complexity for N x N Packet Switches ,” Conference on Information Science and Systems, Princeton, NJ, March, 2002, pgs. 136–148.**
45. Alvin Fu, Eytan Modiano and John Tsitsiklis, " Transmission Scheduling Over a Fading Channel with Energy and Deadline Constraints ,” Conference on Information Science and System, Princeton, NJ, March, 2002, pgs. 1018–1023.**
44. Chunmei Liu and Eytan Modiano, " On the Interaction of Layered Protocols: The Case of Window Flow Control and ARQ ,” Conference on Information Science and System, Princeton, NJ, March, 2002, pgs. 118–124.**
43. Mike Neely, Eytan Modiano and Charles Rohrs, " Packet Routing over Parallel Time-varying Queues with Application to Satellite and Wireless Networks ,” Conference on Information Science and System, Princeton, NJ, March, 2002, pgs. 360–366.**
42. Ahluwalia Ashwinder, Eytan Modiano and Li Shu, " On the Complexity and Distributed Construction of Energy Efficient Broadcast Trees in Static Ad Hoc Wireless Networks ,” Conference on Information Science and System, Princeton, NJ, March, 2002, pgs. 807–813.**
41. Jun Sun and Eytan Modiano, " Capacity Provisioning and Failure Recovery for Satellite Constellations ,” Conference on Information Science and System, Princeton, NJ, March, 2002, pgs. 1039–1045.**
40. Eytan Modiano, Hungjen Wang, and Muriel Medard, " Partial Path Protection for WDM networks ,” Informs Telecommunications Conference, Boca Raton, FL, March 2002, pgs. 78–79.**
39. Poompat Saengudomlert, Eytan H. Modiano, and Robert G. Gallager, " An On-Line Routing and Wavelength Assignment Algorithm for Dynamic Traffic in a WDM Bidirectional Ring ,” Joint Conference on Information Sciences (JCIS), Durham, North Carolina, March, 2002, pgs. 1331–1334.**
38. Randy Berry and Eytan Modiano, " Switching and Traffic Grooming in WDM Networks ,” Joint Conference on Information Sciences (JCIS), Durham, North Carolina, March, 2002, pgs. 1340–1343.
37. Eytan Modiano, Hungjen Wang, and Muriel Medard, " Using Local Information for WDM Network Protection ,” Joint Conference on Information Sciences (JCIS), Durham, North Carolina, March, 2002, pgs. 1398–1401.**
36. Aradhana Narula-Tam and Eytan Modiano, " Network architectures for supporting survivable WDM rings ,” IEEE/OSA Optical Fiber Conference (OFC) 2002, Anaheim, CA, March, 2002, pgs. 105–107.
35. Michael Neely, Eytan Modiano, Charles Rohrs, " Packet Routing over Parallel Time-Varying Queues with Application to Satellite and Wireless Networks ,” Allerton Conference on Communication, Control, and Computing, Allerton, Illinois, September, 2001, pgs. 1110-1111.**
34. Eytan Modiano and Randy Berry, " The Role of Switching in Reducing Network Port Counts ,” Allerton Conference on Communication, Control, and Computing, Allerton, Illinois, September, 2001, pgs. 376-385.
33. Eytan Modiano, " Resource allocation and congestion control in next generation satellite networks ,” IEEE Gigabit Networking Workshop (GBN 2001), Anchorage, AK, April 2001, (2 page summary-online proceedings).
32. Eytan Modiano and Aradhana Narula-Tam, " Survivable Routing of Logical Topologies in WDM Networks ,” IEEE Infocom 2001, Anchorage, AK, April 2001, pgs. 348–357.
31. Michael Neely and Eytan Modiano, " Convexity and Optimal Load Distribution in Work Conserving */*/1 Queues ,” IEEE Infocom 2001, Anchorage, AK, April 2001, pgs. 1055–1064.
30. Eytan Modiano and Randy Berry, " Using Grooming Cross- Connects to Reduce ADM Costs in Sonet/WDM Ring Networks ,” IEEE/OSA Optical Fiber Conference (OFC) 2001, Anaheim, CA March 2001, pgs. WL1- WL3.
29. Eytan Modiano and Aradhana Narula-Tam, " Designing Survivable Networks Using Effective Rounting and Wavelenght Assignment (RWA) ,” IEEE/OSA Optical Fiber Conference (OFC) 2001, Anaheim, CA March 2001, pgs. TUG5-1 – TUG5– 3.
28. Roop Ganguly and Eytan Modiano, " Distributed Algorithms and Architectures for Optical Flow Switching in WDM networks ,” IEEE International Symposium on Computer Communications (ISCC 2000), Antibes, France, July 2000, pgs. 134–139.
27. Aradhana Narula-Tam, Philip J. Lin and Eytan Modiano, " Wavelength Requirements for Virtual topology Reconfiguration in WDM Ring Networks ,” IEEE International Conference on Communications (ICC 2000), New Orleans, LA, June 2000, pgs. 1650–1654.
26. Eytan Modiano, "Optical Flow Switching for the Next Generation Internet,” IEEE Gigabit Networking Workshop (GBN 2000), Tel-aviv, March 2000 (2 page summary-online proceedings).
25. Aradhana Narula and Eytan Modiano, " Dynamic Reconfiguration in WDM Packet Networks with Wavelength Limitations ,” IEEE/OSA Optical Fiber Conference (OFC) 2000, Baltimore, MD, March, 2000, pgs. 1210–1212.
24. Brett Schein and Eytan Modiano, " Quantifying the benefits of configurability in circuit-switched WDM ring networks ,” IEEE Infocom 2000, Tel Aviv, Israel, April, 2000, pgs.1752–1760..***
23. Aradhana Narula-Tam and Eytan Modiano, " Load Balancing Algorithms for WDM-based IP networks ,” IEEE Infocom 2000, Tel Aviv, Israel, April, 2000, pgs. 1010–1019.
22. Nan Froberg, M. Kuznetsov, E. Modiano, et. al., " The NGI ONRAMP test bed: Regional Access WDM technology for the Next Generation Internet ,” IEEE LEOS ’99, October, 1999, pgs. 230–231.
21. Randy Berry and Eytan Modiano, " Minimizing Electronic Multiplexing Costs for Dynamic Traffic in Unidirectional SONET Ring Networks ,” IEEE International Conference on Communications (ICC ’99), Vancouver, CA, June 1999, pgs. 1724–1730..***
20. Brett Schein and Eytan Modiano, "Increasing Traffic Capacity in WDM Ring Networks via Topology Reconfiguration,” Conference on Information Science and Systems, Baltimore, MD, March 1999, pgs. 201 – 206.
19. Eytan Modiano and Richard Barry, " Design and Analysis of an Asynchronous WDM Local Area Network Using a Master/Slave Scheduler ,” IEEE Infocom ’99, New York, NY, March 1999, pgs. 900–907.
18. Randy Berry and Eytan Modiano, " Grooming Dynamic Traffic in Unidirectional SONET Ring Networks ,” IEEE/OSA Optical Fiber Conference (OFC) ’99, San Diego, CA, February 1999, pgs. 71–73.
17. Angela Chiu and Eytan Modiano, " Reducing Electronic Multiplexing Costs in Unidirectional SONET/WDM Ring Networks Via Efficient Traffic Grooming ,” IEEE Globecom '98, Sydney, Australia, November 1998, pgs. 322–327.
16. Eytan Modiano, " Throughput Analysis of Unscheduled Multicast Transmissions in WDM Broadcast-and-Select Networks ,” IEEE International Symposium on Information Theory, Boston, MA, September 1998, pg. 167.
15. Eytan Modiano and Angela Chiu, "Traffic Grooming Algorithms for Minimizing Electronic Multiplexing Costs in Unidirectional SONET/WDM Ring Networks,” Conference on Information Science and Systems, Princeton, NJ, March 1998, 653–658.
14. Eytan Modiano and Eric Swanson, " An Architecture for Broadband Internet Services over a WDM-based Optical Access Network ,” IEEE Gigabit Networking Workshop (GBN '98), San Francisco, CA, March 1998 (2 page summary-online proceedings).
13. Eytan Modiano, " Unscheduled Multicasts in WDM Broadcast-and-Select Networks ,” IEEE Infocom '98, San Francisco, CA, March 1998, pgs. 86–93.
12. Eytan Modiano, Richard Barry and Eric Swanson, " A Novel Architecture and Medium Access Control (MAC) protocol for WDM Networks ,” IEEE/OSA Optical Fiber Conference (OFC) '98, San Jose, CA, February 1998, pgs. 90–91.
11. Eytan Modiano, " Scheduling Algorithms for Message Transmission Over a Satellite Broadcast System ,” IEEE MILCOM 97, Monterey, CA, November 1997, pgs. 628–634.
10. Eytan Modiano, " Scheduling Packet Transmissions in A Multi-hop Packet Switched Network Based on Message Length ,” IEEE International Conference on Computer Communications and Networks (IC3N) Las Vegas, Nevada, September 1997, pgs. 350–357.
9. Eytan Modiano, "A Simple Algorithm for Optimizing the Packet Size Used in ARQ Protocols Based on Retransmission History,” Conference on Information Science and Systems, Baltimore, MD, March 1997, pgs. 672–677.
8. Eytan Modiano, " A Multi-Channel Random Access Protocol for the CDMA Channel ,” IEEE PIMRC '95, Toronto, Canada, September 1995, pgs. 799–803.
7. Eytan Modiano Jeffrey Wieselthier and Anthony Ephremides, " A Simple Derivation of Queueing Delay in a Tree Network of Discrete-Time Queues with Deterministic Service Times ,” IEEE International Symposium on Information Theory, Trondheim, Norway, June 1994, pg. 372.
6. Eytan Modiano, Jeffrey Wieselthier and Anthony Ephremides, "An Approach for the Analysis of Packet Delay in an Integrated Mobile Radio Network,” Conference on Information Sciences and Systems, Baltimore, MD, March 1993, pgs. 138-139.
5. Eytan Modiano and Anthony Ephremides, " A Method for Delay Analysis of Interacting Queues in Multiple Access Systems ,” IEEE INFOCOM 1993, San Francisco, CA, March 1993, pgs. 447 – 454.
4. Eytan Modiano and Anthony Ephremides, " A Model for the Approximation of Interacting Queues that Arise in Multiple Access Schemes ,” IEEE International Symposium on Information Theory, San Antonio, TX, January 1993, pg. 324.
3. Eytan Modiano and Anthony Ephremides, " Efficient Routing Schemes for Multiple Broadcasts in a Mesh ,” Conference on Information Sciences and Systems, Princeton, NJ, March 1992, pgs. 929 – 934.
2. Eytan Modiano and Anthony Ephremides, " On the Secrecy Complexity of Computing a Binary Function of Non-uniformly Distributed Random Variables ,” IEEE International Symposium on Information Theory, Budapest, Hungary, June 1991, pg. 213.
1. Eytan Modiano and Anthony Ephremides, "Communication Complexity of Secure Distributed Computation in the Presence of Noise,” IEEE International Symposium on Information Theory, San Diego, CA, January 1990, pg. 142.
Book Chapters
- Hyang-Won Lee, Kayi Lee, Eytan Modiano, " Cross-Layer Survivability " in Cross-Layer Design in Optical Networks, Springer, 2013.
- Li-Wei Chen and Eytan Modiano, " Geometric Capacity Provisioning for Wavelength-Switched WDM Networks ," Chapter in Computer Communications and Networks Series: Algorithms for Next Generation Networks, Springer, 2010.
- Amir Khandani, Eytan Modiano, Lizhong Zhang, Jinane Aboundi, " Cooperative Routing in Wireless Networks ," Chapter in Advances in Pervasive Computing and Networking, Kluwer Academic Publishers, 2005.
- Jian-Qiang Hu and Eytan Modiano, " Traffic Grooming in WDM Networks ," Chapter in Emerging Optical Network Technologies, Kluwer Academic Publishers, to appear, 2004.
- Eytan Modiano, " WDM Optical Networks ," Wiley Encyclopedia of Telecommunications (John Proakis, Editor), 2003.
- Eytan Modiano, " Optical Access Networks for the Next Generation Internet ," in Optical WDM Networks: Principles and Practice, Kluwer Academic Prublishers, 2002.
- Eytan Modiano, Richard Barry and Eric Swanson, " A Novel Architecture and Medium Access Control protocol for WDM Networks ," Trends in Optics and Photonics Series (TOPS) volume on Optical Networks and Their Applications, 1998.
- Eytan Modiano and Kai-Yeung Siu, "Network Flow and Congestion Control," Wiley Encyclopedia of Electrical and Electronics Engineering, 1999.
Technical Reports
- Amir Khandani, Eytan Modiano, Jinane Abounadi, Lizhong Zheng, "Reliability and Route Diversity in Wireless Networks, " MIT LIDS Technical Report number 2634, November, 2004.
- Anand Srinivas and Eytan Modiano, "Minimum Energy Disjoint Path Routing in Wireless Ad Hoc Networks, " MIT LIDS Technical Report, P-2559, March, 2003.
- Eytan Modiano and Aradhana Narula-Tam, "Survivable lightpath routing: a new approach to the design of WDM-based networks, " LIDS report 2552, October, 2002.
- Michael Neely, Eytan Modiano and Charles Rohrs, "Packet Routing over Parallel Time-Varying Queues with Application to Satellite and Wireless Networks," LIDS report 2520, September, 2001.
- Jun Sun and Eytan Modiano, "Capacity Provisioning and Failure Recovery in Mesh-Torus Networks with Application to Satellite Constellations," LIDS report 2518, September, 2001.
- Hungjen Wang, Eytan Modiano and Muriel Medard, "Partial Path Protection for WDM Networks: End-to-End Recovery Using Local Failure Information, " LIDS report 2517, Sept. 2001.
- Alvin Fu, Eytan Modiano, and John Tsitsiklis, "Optimal Energy Allocation and Admission Control for Communications Satellites, " LIDS report 2516, September, 2001.
- Michael Neely, Eytan Modiano and Charles Rohrs, "Power and Server Allocation in a Multi-Beam Satellite with Time Varying Channels, " LIDS report 2515, September, 2001.
- Eytan Modiano, "Scheduling Algorithms for Message Transmission Over the GBS Satellite Broadcast System, " Lincoln Laboratory Technical Report Number TR-1035, June 1997.
- Eytan Modiano, "Scheduling Packet Transmissions in A Multi-hop Packet Switched Network Based on Message Length, " Lincoln Laboratory Technical Report number TR-1036, June, 1997.
Software-Defined Networking (SDN): A Review
Ieee account.
- Change Username/Password
- Update Address
Purchase Details
- Payment Options
- Order History
- View Purchased Documents
Profile Information
- Communications Preferences
- Profession and Education
- Technical Interests
- US & Canada: +1 800 678 4333
- Worldwide: +1 732 981 0060
- Contact & Support
- About IEEE Xplore
- Accessibility
- Terms of Use
- Nondiscrimination Policy
- Privacy & Opting Out of Cookies
A not-for-profit organization, IEEE is the world's largest technical professional organization dedicated to advancing technology for the benefit of humanity. © Copyright 2024 IEEE - All rights reserved. Use of this web site signifies your agreement to the terms and conditions.
Topics in Networking Research
- Conference paper
- Cite this conference paper

- Debasis Mitra 1
Part of the book series: Lecture Notes in Computer Science ((LNCCN,volume 4516))
Included in the following conference series:
- International Teletraffic Congress
1404 Accesses
What are the big movements in networking that researchers should heed? A standout is the global spread of communities of interest (the networking analogue of the flat world) and their need for “dynamic virtual networks” that support rich applications requiring resources from several domains. The imperative for inter-networking, i.e., the enablement of coordinated sharing of resources across multiple domains, is certain. This challenge has many facets, ranging from the organizational, e.g., different, possibly competing, owners to the technical, e.g., different technologies. Yet another key characteristic of the emerging networking environment is that the service provider is required to handle ever-increasing uncertainty in demand, both in volume and time. On the other hand there are new instruments available to handle the challenge. Thus, inter-networking and uncertainty management are important challenges of emerging networking that deserve attention from the research community.
We describe research that touch on both topics. First, we consider a model of data-optical inter-networking, where routes connecting end-points in data domains are concatenation of segments in the data and optical domains. The optical domain in effect acts as a carrier’s carrier for multiple data domains. The challenge to inter-networking stems from the limited view that the data and optical domains have of each other. Coordination has to be enabled through parsimonious and qualitatively restrictive information exchange across domains. Yet the overall optimization objective, which is to maximize end-to-end carried traffic with minimum lightpath provisioning cost, enmeshes data and optical domains. This example of inter-networking also involves two technologies. A mathematical reflection of the latter fact is the integrality of some of the decision variables due to wavelengths being the bandwidth unit in optical transmission. Through an application of Generalized Bender’s Decomposition the problem of optimizing provisioning and routing is decomposed into sub-problems, which are solved by the different domains and the results exchanged in iterations that provably converge to the global optimum.
In turning to uncertainty management we begin by presenting a framework for stochastic traffic management. Traffic demands are uncertain and given by probability distributions. While there are alternative perspectives (and metrics) to resource usage, such as social welfare and network revenue, we adopt the latter, which is aligned with the service provider’s interests. Uncertainty introduces the risk of misallocation of resources. What is the right measure of risk in networking? We examine various definitions of risk, some taken from modern portfolio theory, and suggest a balanced solution. Next we consider the optimization of an objective which is a risk-adjusted measure of network revenue. We obtain conditions under which the optimization problem is an instance of convex programming. Studies of the properties of the solution show that it asymptotically meets the stochastic efficiency criterion. Service providers’ risk mitigation policies are suggested. For instance, by selecting the appropriate mix of long-term contracts and opportunistic servicing of random demand, the service provider can optimize its risk-adjusted revenue. The “efficient frontier”, which is the set of Pareto optimal pairs of mean revenue and revenue risk, is useful to the service provider in selecting its operating point.
Joint work with Qiong Wang and Anwar Walid, Bell Labs, Murray Hill.
This is a preview of subscription content, log in via an institution to check access.
Access this chapter
- Available as PDF
- Read on any device
- Instant download
- Own it forever
- Compact, lightweight edition
- Dispatched in 3 to 5 business days
- Free shipping worldwide - see info
Tax calculation will be finalised at checkout
Purchases are for personal use only
Institutional subscriptions
Author information
Authors and affiliations.
Bell Labs, Alcatel-Lucent, Murray Hill, NJ 07974, USA
Debasis Mitra
You can also search for this author in PubMed Google Scholar
Editor information
Rights and permissions.
Reprints and permissions
Copyright information
© 2007 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper.
Mitra, D. (2007). Topics in Networking Research. In: Mason, L., Drwiega, T., Yan, J. (eds) Managing Traffic Performance in Converged Networks. ITC 2007. Lecture Notes in Computer Science, vol 4516. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-540-72990-7_3
Download citation
DOI : https://doi.org/10.1007/978-3-540-72990-7_3
Publisher Name : Springer, Berlin, Heidelberg
Print ISBN : 978-3-540-72989-1
Online ISBN : 978-3-540-72990-7
eBook Packages : Computer Science Computer Science (R0)
Share this paper
Anyone you share the following link with will be able to read this content:
Sorry, a shareable link is not currently available for this article.
Provided by the Springer Nature SharedIt content-sharing initiative
- Publish with us
Policies and ethics
- Find a journal
- Track your research
Networking is central to modern computing, from WANs connecting cell phones to massive data stores, to the data-center interconnects that deliver seamless storage and fine-grained distributed computing. Because our distributed computing infrastructure is a key differentiator for the company, Google has long focused on building network infrastructure to support our scale, availability, and performance needs, and to apply our expertise and infrastructure to solve similar problems for Cloud customers. Our research combines building and deploying novel networking systems at unprecedented scale, with recent work focusing on fundamental questions around data center architecture, cloud virtual networking, and wide-area network interconnects. We helped pioneer the use of Software Defined Networking, the application of ML to networking, and the development of large-scale management infrastructure including telemetry systems. We are also addressing congestion control and bandwidth management, capacity planning, and designing networks to meet traffic demands. We build cross-layer systems to ensure high network availability and reliability. By publishing our findings at premier research venues, we continue to engage both academic and industrial partners to further the state of the art in networked systems.
Recent Publications
Some of our teams.
Cloud networking
Global networking
Network infrastructure
We're always looking for more talented, passionate people.

- Artificial Intelligence
- Generative AI
- Cloud Computing
- CPUs and Processors
- Data Center
- Edge Computing
- Enterprise Storage
- Virtualization
- Internet of Things
- Network Management Software
- Network Security
- Enterprise Buyer’s Guides
- United States
- Newsletters
- Foundry Careers
- Terms of Service
- Privacy Policy
- Cookie Policy
- Copyright Notice
- Member Preferences
- About AdChoices
- E-commerce Links
- Your California Privacy Rights
Our Network
- Computerworld

25 of today’s coolest network and computing research projects
Latest concoctions from university labs include language learning website, a newfangled internet for mobile devices and even ip over xylophones.
University labs, fueled with millions of dollars in funding and some of the biggest brains around, are bursting with new research into computer and networking technologies.
ALPHADOGGS: Follow our and Facebook page
networks, computer and a general focus on shrinking things and making them faster are among the hottest areas, with some advances already making their way into the market. Here’s a roundup of 25 such projects that caught our eyes:
This free website, Duolingo, from a pair of Carnegie Mellon University computer scientists serves double duty: It helps people learn new languages while also translating the text on Web pages into different languages.
CMU’s Luis von Ahn and Severin Hacker have attracted more than 100,000 people in a beta test of the system, which initially offered free language lessons in English, Spanish, French and German, with the computer offering advice and guidance on unknown words. Using the system could go a long way toward translating the Web, many of whose pages are unreadable by those whose language skills are narrow.
Von Ahn is a veteran of such crowdsourcing technologies, having created online reCAPTCHA puzzles to cut down on spam while simultaneously digitizing old books and periodicals. Von Ahn’s spinoff company, reCAPTCHA, was acquired by Google in 2009. Duolingo, spun off in November to offer commercial and free translation services, received $3.3 million in funding from Union Square Ventures, actor Ashton Kutcher and others.
Princeton University Computer Science researchers envision an Internet that is more flexible for operators and more useful to mobile users. Princeton’s Serval system is what Assistant Professor of Computer Science Michael Freedman calls a Service Access Layer that sits between the IP Network Layer (Layer 3) and Transport Layer (Layer 4), where it can work with unmodified network devices. Serval’s purpose is to make Web services such as Gmail and Facebook more easily accessible, regardless of where an end user is, via a services naming scheme that augments what the researchers call an IP address set-up “designed for communication between fixed hosts with topology-dependent addresses.” Data center operators could benefit by running Web servers in virtual machines across the cloud and rely less on traditional load balancers.
Serval, which Freedman describes as a “replacement” technology, will likely have its first production in service-provider networks. “Its largest benefits come from more dynamic settings, so its features most clearly benefit the cloud and mobile spaces,” he says.
If any of this sounds similar to software-defined networking (SDN), there are in fact connections. Freedman worked on an SDN/OpenFlow project at Stanford University called Ethane that was spun out into a startup called Nicira for which VMware recently plunked down $1.26 billion.
WiFi routers to the rescue
Researchers at Germany’sTechnical University in Darmstadt have described a way for home Wi-Fi routers to form a backup mesh network to be used by the police, firefighters and other emergency personnel in the case of a disaster or other incident that wipes out standard cell and phone systems.
The proliferation of Wi-Fi routers makes the researchers confident that a dense enough ad hoc network could be created, but they noted that a lack of unsecured routers would require municipalities to work with citizens to allow for the devices to be easily switched into emergency mode. The big question is whether enough citizens would really allow such access, even if security was assured.
Hyperspeed signaling
University of Tulsa engineers want to slow everything down, for just a few milliseconds, to help network administrations avoid cyberattacks.
By slowing traffic, the researchers figure more malware can be detected and then headed off via an algorithm that signals at hyperspeed to set up defenses. Though researcher Sujeet Shenoi told the publication New Scientist that it might not be cheap to set up such a defense system, between the caching system and reserved data pipes needed to support the signals.
Control-Alt-Hack
University of Washington researchers have created a card game called Control-Alt-Hack that’s designed to introduce computer science students to security topics.
The game, funded in part by Intel Labs and the National Science Foundation, made its debut at the Black Hat security conference in Las Vegas over the summer. The tabletop game involves three to six players working for an outfit dubbed Hackers, Inc., that conducts security audits and consulting, and players are issued challenges, such as hacking a hotel mini bar payment system or wireless medical implant, or converting a robotic vacuum cleaner into a toy. The game features cards (including descriptions of well-rounded hackers who rock climb, ride motorcycles and do more than sit at their computers), dice, mission cards, “hacker cred tokens” and other pieces, and is designed for players ages 14 and up. It takes about an hour to play a game. No computer security degree needed.
“We went out of our way to incorporate humor,” said co-creator Tamara Denning, a UW doctoral student in computer science and engineering, referring to the hacker descriptions and challenges on the cards. “We wanted it to be based in reality, but more importantly we want it to be fun for the players.”
Ghost-USB-Honeypot project
This effort, focused on nixing malware like Flame that spreads from computer to computer via USB storage drives, got its start based on research from Sebastian Poeplau at Bonn University’s Institute of Computer Science. Now it’s being overseen by the broader Honeynet Project.
The breakthrough by Poeplau and colleagues was to create a virtual drive that runs inside a USB drive to snag malware . According to the project website: “Basically, the honeypot emulates a USB storage device. If your machine is infected by malware that uses such devices for propagation, the honeypot will trick it into infecting the emulated device.”
One catch: the security technology only works on XP 32 bit, for starters.
IP over Xylophone Players (IPoXP)
Practical applications for running IP over xylophones might be a stretch, but doing so can teach you a few things about the truly ubiquitous protocol.
A University of California Berkeley researcher named R. Stuart Geiger led this project, which he discussed earlier this year at the Association for Computing Machinery’s Conference on Human Factors in Computing Systems . Geiger’s Internet Protocol over Xylophone Players (IPoXP) provides a fully compliant IP connection between two computers. His setup uses a pair of Arduino microcontrollers, some sensors, a pair of xylophones and two people to play the xylophones.
The exercise provided some insights into the field of Human-Computer Interaction (HCI). It emulates a technique HCI specialists use to design interfaces called umwelt, which is a practice of imagining what the world must look like to the potential users of the interface. This experiment allowed participants to get the feel for what it would be like to be a circuit.
“I don’t think I realized how robust and modular the OSI model is,” Geiger said. “The Internet was designed for much more primitive technologies, but we haven’t been able to improve on it, because it is such a brilliant model.”
Making software projects work
San Francisco State University and other researchers are puzzling over why so many software projects wind up getting ditched, fail or get completed, but late and over budget. The key, they’ve discovered, is rethinking how software engineers are trained and managed to ensure they can work as teams.
The researchers, also from Florida Atlantic University and Fulda University in Germany, are conducting a National Science Foundation-funded study with their students that they hope will result in a software model that can predict whether a team is likely to fail. Their study will entail collecting information on how often software engineering students – teamed with students at the same university and at others — meet, email each other, etc.
“We want to give advice to teachers and industry leaders on how to manage their teams,” says Dragutin Petkovic, professor and chair of SF State’s Computer Science Department. “Research overwhelmingly shows that it is ‘soft skills,’ how people work together, that are the most critical to success.”
Ultra low-power wireless
Forget about 3G, 4G and the rest: University of Arkansas engineering researchers are focused on developing very low-power wireless systems that can grab data from remote sensors regardless of distortion along the network path.
These distortion-tolerant systems would enable sensors, powered by batteries or energy-harvesting, to remain in the field for long periods of time and withstand rough conditions to monitor diverse things such as tunnel stability and animal health. By tolerating distortion, the devices would expend less energy on trying to clean up communications channels.
“If we accept the fact that distortion is inevitable in practical communication systems, why not directly design a system that is naturally tolerant to distortion?” says Jingxian Wu, assistant professor of electrical engineering.
The National Science Foundation is backing this research with $280,000 in funding.
2-way wireless
University of Waterloo engineering researchers have developed a way for wireless voice and data signals to be sent and received simultaneously on a single radio channel frequency, a breakthrough they say could make for better performing, more easily connected and more secure networks.
“This means wireless companies can increase the bandwidth of voice and data services by at least a factor of two by sending and receiving at the same time, and potentially by a much higher factor through better adaptive transmission and user management in existing networks,” said Amir Khandani, a Waterloo electrical and computer engineering professor, in a statement. He says the cost for hardware and antennas to support such a system wouldn’t cost any more than for current one-way systems.
Next up is getting industry involved in bringing such technology into the standards process.
Next steps require industry involvement by including two-way in forthcoming standards to enable wide spread implementation.
The Waterloo research was funded in part by the Canada Foundation for Innovation and the Ontario Ministry of Research and Innovation.
Spray-on batteries
Researchers at Rice University in Houston have developed a prototype spray-on battery that could allow engineers to rethink the way portable electronics are designed.
The rechargeable battery boasts similar electrical characteristics to the lithium ion batteries that power almost every mobile gadget, but it can be applied in layers to almost any surface with a conventional airbrush, said Neelam Singh, a Rice University graduate student who led a team working on the technology for more than a year.
Current lithium ion batteries are almost all variations on the same basic form: an inflexible block with electrodes at one end. Because they cannot easily be shaped, they sometimes restrict designers, particularly when it comes to small gadgets with curved surfaces, but the Rice prototypes could change that. “Today, we only have a few form factors of batteries, but this battery can be fabricated to fill the space available,” said Singh.
The battery is sprayed on in five layers: two current collectors sandwich a cathode, a polymer separator and an anode. The result is a battery that can be sprayed on to plastics, metal and ceramics.
The researchers are hoping to attract interest from electronics companies, which Singh estimates could put it into production relatively easily. “Airburshing technology is well-established. At an industrial level it could be done very fast,” she said.
Mobile Mosh pit
Two MIT researchers formally unveiled over the summer a protocol called State Synchronization Protocol (SSP) and a remote log-in program using it dubbed Mosh (for mobile shell) that’s intended as an alternative to Secure Shell (SSH) for ensuring good connectivity for mobile clients even when dealing with low bandwidth connections. SSP and Mosh have been made available for free, on GNU/, FreeBSD and OS X, via an MIT website.
SSH, often used by network and system admins for remotely logging into servers, traditionally connects computers via TCP, but it’s that use of TCP that creates headaches for mobile users, since TCP assumes that the two endpoints are fixed, says Keith Winstein, a graduate student with MIT’s Computer Science and Artificial Intelligence Lab (CSAIL), and Mosh’s lead developer. “This is not a great way to do real-time communications,” Winstein says. SSP uses UDP, a connectionless, stateless transport mechanism that could be useful for stabilizing mobile usage of apps from Gmail to Skype.
Network Coding
Researchers from MIT, California Institute of Technology and University of Technology in Munich are putting network coding and error-correction coding to use in an effort to measure capacity of wired, and more challengingly, even small wireless networks (read their paper here for the gory details).
The researchers have figured out a way to gauge the upper and lower bounds of capacity in a wireless network. Such understanding could enable enterprises and service providers to design more efficient networks regardless of how much noise is on them (and wireless networks can get pretty darn noisy).
More details from MIT press office.
100 terahertz level
A University of Pittsburgh research team is claiming a communications breakthrough that they say could be used to speed up electronic devices such as and laptops in a big way. Their advance is a demonstrated access to more than 100 terahertz of bandwidth (electromagnetic spectrum between infrared and microwave light), whereas electronic devices traditionally have been limited to bandwidth in the gigahertz realm.
Researchers Hrvoje Petek of the University of Pittsburgh and visiting professor Muneaki Hase of the University of Tsukuba in Japan, have published their NSF-funded research findings in a paper in Nature Photonics. The researchers “detail their success in generating a frequency comb-dividing a single color of light into a series of evenly spaced spectral lines for a variety of uses-that spans a more than 100 terahertz bandwidth by exciting a coherent collective of atomic motions in a semiconductor silicon crystal.”
Petek says the advance could result in devices that carry a thousand-fold more information.
Separately, IBM researchers have developed a prototype optical chip that can transfer data at 1Tbps, the equivalent of downloading 500 high-definition movies, using light pulses rather than by sending electrons over wires.
The Holey Optochip is described as a parallel optical transceiver consisting of a transmitter and a receiver, and designed to handle gobs of data on corporate and consumer networks.
Cooling off with graphene
Graphene is starting to sound like a potential wonder material for the electronics business. Researchers from the University of California at Riverside, the University of Texas at Dallas and Austin, and Xiamen University in China have come up with a way to engineer graphene so that it has much better thermal properties. Such an isotopically-engineered version of graphene could be used to build cooler-running laptops, wireless gear and other equipment. The need for such a material has grown as electronic devices have gotten more powerful but shrunk in size.
“The important finding is the possibility of a strong enhancement of thermal conduction properties of isotopically pure graphene without substantial alteration of electrical, optical and other physical properties,” says UC Riverside Professor of Electrical Engineering Alexander Balandin, in a statement. “Isotopically pure graphene can become an excellent choice for many practical applications provided that the cost of the material is kept under control.”
Such a specially engineered type of graphene would likely first find its way into some chip packaging materials as well into photovoltaic solar cells and flexible displays, according to UC Riverside. Beyond that, it could be used with silicon in computer chips, for interconnect wiring to to spread heat.
Industry researchers have been making great strides on the graphene front in recent years. IBM, for example, last year said it had created the first graphene-based integrated circuit. Separately, two Nobel Prize winning scientists out of the U.K. have come up with a new way to use graphene – the thinnest material in the world – that could make Internet pipes feel a lot fatter.
Keeping GPS honest
Cornell University researchers are going on the offense against those who would try to hack GPS systems like those used in everything from cars to military drones to cellphone systems and power grids. Over the summer, Cornell researchers tested their system for outsmarting GPS spoofers during a Department of Homeland Security-sponsored demo involving a mini helicopter in the New Mexico desert at the White Sands Missile Range.
Cornell researchers have come up with GPS receiver modifications that allow the systems to distinguish between real and bogus signals that spoofers would use to trick cars, airplanes and other devices into handing over control. They emphasized that the threat of GPS spoofing is very real, with Iran last year claiming to have downed a GPS-guided American drone using such techniques.
Getting smartphones their ZZZZs
Purdue University researchers have come up with a way to detect smartphone bugs that can drain batteries while they’re not in use.
“These energy bugs are a silent battery killer,” says Y. Charlie Hu, a Purdue University professor of electrical and computer engineering. “A fully charged phone battery can be drained in as little as five hours.”
The problem is that app developers aren’t perfect when it comes to building programs that need to perform functions when phones are asleep and that use APIs provided by smartphone makers. The researchers, whose work is funded in part by the National Science Foundation, investigated the problem on Android phones, and found that about a quarter of some 187 apps contained errors that could drain batteries. The tools they’re developing to detect such bugs could be made available to developers to help them cut down on battery-draining mistakes.
Quantum leap in search
University of Southern California and University of Waterloo researchers are exploring how quantum computing technology can be used to speed up the math calculations needed to make Internet search speedy even as the gobs of data on the Web expands.
The challenge is that Google’s page ranking algorithm is considered by some to be the largest numerical calculation carried out worldwide, and no quantum computer exists to handle that. However, the researchers have created models of the web to simulate how quantum computing could be used to slice and dice the Web’s huge collection of data. Early findings have been encouraging, with quantum computers shown through the models to be faster at ranking the most important pages and improving as more pages needed to be ranked.
The research was funded by the NSF, NASA Ames Research Center, Lockheed Martin’s University Research Initiative and a Google faculty research award.
Sharing malware in a good way
Georgia Tech Research Institute security specialists have built a system called Titan designed to help corporate and government officials anonymously share information on malware attacks they are fighting, in hopes of fighting back against industrial espionage.
The threat analysis system plows through a repository of some 100,000 pieces of malicious code per day, and will give contributors quick feedback on malware samples that can be reverse-engineered by the Titan crew. Titan will also alert members of new threats, such as targeted spear-phishing attacks, and will keep tabs on not just Windows threats, but also those to MacIntosh and iOS, and Google Android systems.
“As a university, Georgia Tech is uniquely positioned to take this white hat role in between industry and government,” said Andrew Howard, a GTRI research scientist who is part of the Titan project . “We want to bring communities together to break down the walls between industry and government to provide a trusted, sharing platform.”
Touch-feely computing
Researchers from the University of Notre Dame, MIT and the University of Memphis are working on educational software that can respond to students’ cognitive and emotional states, and deliver the appropriate content based on how knowledgeable a student is about a subject, or even how bored he or she is with it.
AutoTutor and Affective AutoTutor get a feel for students’ mood and capabilities based on their responses to questions, including their facial expressions, speech patterns and hand movements.
“Most of the 20th-century systems required humans to communicate with computers through windows, icons, menus and pointing devices,” says Notre Dame Assistant Professor of Psychology Sidney D’Mello, an expert in human-computer interaction and AI in education . “But humans have always communicated with each other through speech and a host of nonverbal cues such as facial expressions, eye contact, posture and gesture. In addition to enhancing the content of the message, the new technology provides information regarding the cognitive states, motivation levels and social dynamics of the students.”
Mobile nets on the move
For emergency responders and others who need to take their mobile networks with them, even in fast-moving vehicles, data transmission quality can be problematic. North Carolina State University researchers say they’ve come up with a way to improve the quality of these Mobile ad hoc networks (MANET).
“Our goal was to get the highest data rate possible, without compromising the fidelity of the signal,” says Alexandra Duel-Hallen, a professor of electrical and computer engineering at NC State whose work is outlined in the paper “ Enabling Adaptive Rate and Relay Selection for 802.11 Mobile Ad Hoc Networks .”
The challenge is that fast moving wireless nodes make it difficult for relay paths to be identified by the network, as channel power tends to fluctuate much more in fast-moving vehicles. The researchers have come up with an algorithm for nodes to choose the best data relay and transmission paths, based on their experience with recent transmissions.
Tweet the Street
Researchers from the University of California, Riverside and Yahoo Research Barcelona have devised a model that uses data about volumes to predict how financial markets will behave. Their model bested other baseline strategies by 1.4% to 11% and outperformed the Dow Jones Industrial Average during a four-month simulation.
“These findings have the potential to have a big impact on market investors,” said Vagelis Hristidis, an associate professor at the Bourns College of Engineering. “With so much data available from social media, many investors are looking to sort it out and profit from it.”
The research, focused on what Twitter volumes, retweets and who is doing the tweeting might say about individual stocks, differs from that of earlier work focused on making sense of the broader market based on positive and negative sentiments in tweets.
As with so many stock-picking techniques, the researchers here tossed out plenty of caveats about their system, which they said might work quite differently, for example, during a period of overall market growth rather than the down market that their research focused on.
Franken-software
University of Texas, Dallas scientists have developed software dubbed Frankenstein that’s designed to be even more monstrous than the worst malware in the wild so that such threats can be understood better and defended against. Frankenstein can disguise itself as it swipes and messes with data, and could be used as a cover for a virus or other malware by stitching together pieces of such data to avoid antivirus detection methods.
“[Mary] Shelley’s story [about Dr. Frankenstein and his monster] is an example of a horror that can result from science, and similarly, we intend our creation as a warning that we need better detections for these types of intrusions,” said Kevin Hamlen, associate professor of computer science at UT Dallas who created the software, along with doctoral student Vishwath Mohan. “Criminals may already know how to create this kind of software, so we examined the science behind the danger this represents, in hopes of creating countermeasures.”
Such countermeasures might include infiltrating terrorist computer networks, the researchers say. To date, they’ve used the NSF and Air Force Office of Scientific Research-funded technology on benign algorithms, not any production systems.
Safer e-wallets
While e-wallets haven’t quite taken off yet, University of Pittsburgh researchers are doing their part to make potential e-wallet users more comfortable with the near-field communications (NRC) and/or RFID-powered technology.
Security has been a chief concern among potential users, who are afraid thieves could snatch their credit card numbers through the air. But these researchers have come up with a way for e-wallet credit cards to turn on and off, rather than being always on whenever in an electromagnetic field.
“Our new design integrates an antenna and other electrical circuitry that can be interrupted by a simple switch, like turning off the lights in the home or office,” says Marlin Mickle, the Nickolas A. DeCecco Professor of Engineering and executive director of the RFID Center for Excellence in the Swanson School. “The RFID or NFC credit card is disabled if left in a pocket or lying on a surface and unreadable by thieves using portable scanners.”
Mickle claims the advance is both simple and inexpensive, and once the researchers have received what they hope will be patent approval, they expect the technology to be adopted commercially.
Digging into Big Data
The University of California, Berkeley has been handed $10 million by the National Science Foundation as part of a broader $200 million federal government effort to encourage the exploration and better exploitation of massive amounts of information dubbed Big Data collected by far-flung wireless sensors, social media systems and more.
UC Berkeley has five years to use its funds for a project called the Algorithms, Machines and People (AMP) Expedition, which will focus on developing tools to extract important information from Big Data, such as trends that could predict everything from earthquakes to cyberattacks to epidemics.
“Buried within this flood of information are the keys to solving huge societal problems and answering the big questions of science,” said Michael Franklin, director of the AMP Expedition team and a UC Berkeley professor of electrical engineering and computer sciences, in a statement . “Our goal is to develop a new generation of data analysis tools that provide a quantum leap in our ability to make sense of the world around us.”
AMP Expedition researchers are building an open-source software stack called the Berkeley Data Analysis System (BDAS) that boasts large-scale machine-learning and data analysis methods, infrastructure that lets programmers take advantage of cloud and cluster computing, and crowdsourcing (in other words, human intelligence). It builds on the AMPLab formed early last year, with backing from Google, SAP and others.
Bob Brown tracks network research in his and Facebook page, as well on Twitter and Google + .
IDG News Service and other IDG publications contributed to this report
Related content
Cisco adds ai features to appdynamics on-premises, chips act to fund $285 million for semiconductor digital twins, microsoft’s ai ambitions fuel $3.3 billion bet on wisconsin data center, red hat unveils image mode for its linux distro, newsletter promo module test.

Bob Brown is the former news editor for Network World.
More from this author
Small cell forum seeks advice from large enterprises, how to make fully homomorphic encryption “practical and usable”, iphone 8 rumor rollup: cranking up the processors; 3d cameras; $1k-plus price, snl one step ahead of amazon with echo silver, most popular authors.

- Elizabeth Montalbano
Show me more
Insecure protocols leave networks vulnerable: report.

What is a digital twin and why is it important to IoT?

2024 global network outage report and internet health check

Has the hype around ‘Internet of Things’ paid off? | Ep. 145

Episode 1: Understanding Cisco’s Converged SDN Transport

Episode 2: Pluggable Optics and the Internet for the Future

Has the hype around ‘Internet of Things’ paid off?

Are unused IPv4 addresses a secret gold mine?

Preparing for a 6G wireless world: Exciting changes coming to the wireless industry


- SUGGESTED TOPICS
- The Magazine
- Newsletters
- Managing Yourself
- Managing Teams
- Work-life Balance
- The Big Idea
- Data & Visuals
- Reading Lists
- Case Selections
- HBR Learning
- Topic Feeds
- Account Settings
- Email Preferences
A Better Approach to Networking
- Christie Hunter Arscott

Move from “small talk” to “deep talk.”
Meeting strangers — especially in the context of work — is uncomfortable for most people. Just the thought of networking can provoke discomfort and anxiety. As humans, we have an innate need to be liked. Research shows we even have a tendency to connect our self-worth to the number of people who like us.
- Because of this, many struggle with performance anxiety when it comes to networking. You’re afraid you might say the wrong thing, forget what you were going to say, or stumble over your words. The result would be the other person not liking you. But there’s a better way to network.
- Focus on what you’re going to ask, not what going to say. Instead of preparing what you’d say when meeting someone new or how you’d respond to questions from a stranger, focus on what you’d ask in those same scenarios.
- Then, practice moving from small talk to deep talk. We tend to underestimate how much other people, and especially first-time contacts, might enjoy and find satisfaction in meaningful conversation. Instead of asking “Where are you from?” ask, “What places have you lived in and traveled to during your educational and career journey that have shaped who you are?”
Do you shy away from talking to new people at networking events? Have you ever walked into the room and felt a tightness in your chest as you stood there, sweating, wondering what to say? Most of us can relate to some version of this experience. Meeting strangers — especially in the context of work — is uncomfortable. Just the thought of networking can provoke discomfort and anxiety.
- Christie Hunter Arscott is an award-winning advisor, speaker, and author of the book Begin Boldly: How Women Can Reimagine Risk, Embrace Uncertainty, and Launch A Brilliant Career . A Rhodes Scholar, Christie has been named by Thinkers50 as one of the top management thinkers likely to shape the future of business.
Partner Center
- Our Promise
- Our Achievements
- Our Mission
- Proposal Writing
- System Development
- Paper Writing
- Paper Publish
- Synopsis Writing
- Thesis Writing
- Assignments
- Survey Paper
- Conference Paper
- Journal Paper
- Empirical Paper
- Journal Support
- Top 5 Interesting Computer Network Research Topics
A computer network is a network of diverse computing hardware linked through different communication technologies to share various resources . The communication links of the network can be either wired (cables) or wireless (radio waves / IR signals).
This page shows you useful information on Computer Network Research Topics, Projects with Source Code, Research Areas, Project Topics, and Tools!!!
Moreover, the network can be differentiated in the characteristics of constrained resources, network structure, requests history/demand, communication technologies , and more. However, it is flexible to share resources, and it has some technical challenges in real-time development. Here, we have given you the common services that we offer for overcoming network issues.
Our Approaches and Services to Solving Computer Network Issues
- Communication technologies selection
- Communication protocols in the network
- Performing both conceptual and practical research
- Study in qualitative and quantitative aspects
- Simulation Models
- Proofs / Theorems / Prototypes Testing / Use Cases
- Experiments for Various Simulation Scenarios
- Graphical / Tabular Representation of Results
- Developing New Techniques
- Thinking Novel Ideas
- Multiple Evaluations
- IEEE Standards Refinement
The layering approach in networking is used to divide the message into various chunks . Basically, there are seven layers in the networking process where each layer has unique responsibilities. All these layers co-operatively work together to transfer the message from one end to another (i.e., source to destination ). Now, we can see the available layers and their function in sequential order.
What are the layers of computer networks?
- Physical Layer – Used for offering mechanical / electrical needs, distribute the bits through transmission medium
- Data Link Layer – Used for offering hop-to-hop distribution, arrange the bits into frames
- Network Layer – Used for offering internetworking, pass over the packets between source and destination
- Transport Layer – Used for offering error correction and process-to-process distribution
- Session Layer – Used for launching and manage temporary sessions
- Presentation Layer – Used for data translation, compression, and encryption
- Application Layer – User for users to access the network resources / services
With an aim to support wireless communications, numerous different technologies have been launched. Before selecting this technology, one should undergo deep study on which is more suitable for their computer network projects . Our research team will help you in both business/individual if you need the best guidance over that selection of innovative computer network research topics . Usually, we recommend the technology based on the requirement of your selected networking projects for final year students . For your information, here we have given you a few lists of communication technologies,
Communication Technologies in Computer Networks
- Wi-Fi and Wi-Max
- Radio Frequency Identification (RFID)
- Ultra-Wideband, Bluetooth and Zigbee
- Global Positioning System (GPS)
- Mobile Communication (4G, 5G, 5G Beyond and 6G)
- Radar and Satellite Communication
- 3GPP – LTE-M, EC-GSM and Narrowband-IoT
- Non-3GPP – Sigfox, Wieghtless and LoRa
In recent days, you can witness the gradual growth of computer networks in networking industries through many new developments. It includes so many technologies to portrait the actual networking industry’s performance. Here, we have given you some new networking technologies that are expected to master the next networking industries. .
Current Technologies in Computer Networks
- Artificial Intelligence (AI) and Cloud Repatriation
- Software Defined Networks
- Fog-Edge Computing
- UAV-Wireless Data Links
- Responsive Internet Architecture
- Multiple Cloud Services Technology
- Internet of Things and Inter-Networking
- Quantum and Serverless Computing
- 5G enabled Nano Technology
- Digital Twin and Machine Learning (ML)
- Digital Communications
- Network Communications Protocols
For illustrative purpose, Digital Communication work in accordance with enabling communication technologies, modulation, signal processing projects, channel modeling, and error control . Similarly, Network Communications Protocols take an in-charge of routing, resource allocation, data distribution, and medium access control.
Both technologies/areas have high capabilities in a different dimension of the networking process. And they are network designing, model construction, networking testing on testbeds, experimental analysis, and performance assessments. Our researchers have given you the currently ongoing of innovative computer network research topics mentioned below for your reference.
Latest Computer Network Research Topics
- Enhancing System Robustness in Decentralized Network
- Improving Network Quality of Services and Resource Usage
- SLA–Aware Resource Scheduling and Provisioning
- Network Architectures Design and Processes Management
How to develop computer networks projects with source code?
Basically, networking is a widespread process where network construction and deployment in the real world is a challenging job. So, the entire process is fragmented into different tasks where they are performed by a set of skilled networking engineers as follows,
- Software Developer – Design and build software applications
- Networking Experts – modeling the network structure
- Database Admin – Store and manage the network information
- Support Specialist – Analyze the connected entities of the system
- Programmer – Develop the suitable code works for achieving required performance
For research purposes, we can simulate the original network behavior and performance inappropriate simulation tools. Most importantly, it reduces the cost of real-time implementation and deployment.
Our developers have long-term experience in handling networking concepts . So, if you need the best Computer Networks Projects with Source Code support , you can approach our team. Below, we have also mentioned our qualified services in your project.
- We do both conceptual and practical study on recent research topics
- We design unique network simulation models, proof-of-concept prototypes and investigational testbeds
- We employ result guaranteed new technologies to upgrade and assess the existing standard of networking systems
- We develop own algorithm, protocols and hybrid techniques based on project requirements
- We precisely access the network performance using suitable network parameters for comparative study of different systems
Performance Analysis of Computer Networks
Now, we can see the performance measurement of the networking model. Through the sophisticated simulation tool / experimental testbeds , we can develop any kind of network scenario. Once the model is processed, then the efficiency of the model is verified by several metrics. Here, we have given you the metrics along with different modelling techniques .
- Medium Access Control – Retransmissions Delay, Collisions and Packet loss
- Network Protocols – Latency, Throughput and Packet loss
- RF Channel Models – Noise, Shadowing and Fading
- Spectrum (Sense and Observation) – Latency and Detection Trustworthiness
- Links and Transceivers – Block error ratio and Signal-to-Noise Ratio (SNR)
What is computer network simulation?
Simulate the network model based on the code of the software application . Through code, we can instruct the model to perform our project requirements. At the end of the simulation, it yields the overall performance and behaviour of the network in different dimensions and metrics. Further, it also measures the communication between the network entities.
Purposes of source code
The source code of software has the main responsibility to create strong basements for designing and simulating the network model . Through the code only, the developers can make the smart work to tackle the problem in a simplified way. Effective code work is also a part of the contribution in research.
Since your code can help for learning or reusability (other application development), for your clarity, our developers will explain the implementation of research methodologies while delivering Computer Networks Projects with Source Code . Below, we have given you the different simulations of real-time network models,
How does computer network simulation works?
- Plan and design the model
- Develop the suitable hypothesis model
- Forecast the hypothetical aspects
- Perform comparative study to improve the hypothesis
- Simulate the developed model
- Based on experimental results, relate and enhance the hypothesis / model
- Do the experiments and get the results
So far, we have discussed computer networks, network layers, communication technologies, current research areas, computer network research topics, project simulation, and performance estimation . Now, our development team has a list of widely used network simulator tools.
Network simulators let the users modify the simulator operations for their project needs. Then the users can analyze the system performance and entity behavior under different circumstances. Further, it supports communication standards/protocols like TCP, WLAN, CR, Wi-Max, WSN , and many more. Here, we have given you the list of a few best result yielding simulators which is more apt for computer network simulations,
- Component-based network simulator with graphical user interface support
- Allow to design traffic models, decentralized system, protocols, computer networks, multi-processors, and many more
- Further, it enables animated and responsive simulation in modular environs
- Empower to design and deploy network application, device and infrastructure
- Develop predictive model, protocol and communication networks to interpret the network functionalities
- Support both real-time wired and wireless models
- Allow to create Finite State Automata for figuring out the network behavior
- Easy to design and develop traffic models
- Utilize QualNet analyzer to understand the obtained simulated outcome
- Enabled OS: Linux and Windows
For instance, NS3 (network Simulator 3) is detailed here.
NS3 is one of the best simulation tools to design and simulate networking projects . With the help of this tool, we can virtually design different nodes through Helper classes. By the by, it enables the installation of internet stacks, applications, devices, and many more. Further, we can insert parameters in the channel for performance evaluation in implementing computer network research topics . And let them produce traffic at runtime and pass the packets from source to destination through the selected route path. The other special features are given as follows,
- Create pcap file to get the core information of the transmitting packets. For instance: Source IP, Sequence no, Destination IP, etc. Employ Wireshark tool to view the pcap.
- Trace the network route for assess number of packets send/receive. For this purpose, the trace files will be produced automatically to monitor whole network.
- Easy to plot the graph from obtained simulation outcome in with assurance of preciseness.
- Network Animator is released to depict the realistic view of the network through animation. It shows you the real structure and how the data are transferred between nodes.
To sum up, we have sufficient technical professionals to support you in all the latest research areas of computer networks . In addition, our developments also give you the best assistance in project development from tool selection to result in an assessment. So, if you need our reliable service computer network research topics, projects with source code then communicate our team.
MILESTONE 1: Research Proposal
Finalize journal (indexing).
Before sit down to research proposal writing, we need to decide exact journals. For e.g. SCI, SCI-E, ISI, SCOPUS.
Research Subject Selection
As a doctoral student, subject selection is a big problem. Phdservices.org has the team of world class experts who experience in assisting all subjects. When you decide to work in networking, we assign our experts in your specific area for assistance.
Research Topic Selection
We helping you with right and perfect topic selection, which sound interesting to the other fellows of your committee. For e.g. if your interest in networking, the research topic is VANET / MANET / any other
Literature Survey Writing
To ensure the novelty of research, we find research gaps in 50+ latest benchmark papers (IEEE, Springer, Elsevier, MDPI, Hindawi, etc.)
Case Study Writing
After literature survey, we get the main issue/problem that your research topic will aim to resolve and elegant writing support to identify relevance of the issue.
Problem Statement
Based on the research gaps finding and importance of your research, we conclude the appropriate and specific problem statement.
Writing Research Proposal
Writing a good research proposal has need of lot of time. We only span a few to cover all major aspects (reference papers collection, deficiency finding, drawing system architecture, highlights novelty)
MILESTONE 2: System Development
Fix implementation plan.
We prepare a clear project implementation plan that narrates your proposal in step-by step and it contains Software and OS specification. We recommend you very suitable tools/software that fit for your concept.
Tools/Plan Approval
We get the approval for implementation tool, software, programing language and finally implementation plan to start development process.
Pseudocode Description
Our source code is original since we write the code after pseudocodes, algorithm writing and mathematical equation derivations.
Develop Proposal Idea
We implement our novel idea in step-by-step process that given in implementation plan. We can help scholars in implementation.
Comparison/Experiments
We perform the comparison between proposed and existing schemes in both quantitative and qualitative manner since it is most crucial part of any journal paper.
Graphs, Results, Analysis Table
We evaluate and analyze the project results by plotting graphs, numerical results computation, and broader discussion of quantitative results in table.
Project Deliverables
For every project order, we deliver the following: reference papers, source codes screenshots, project video, installation and running procedures.
MILESTONE 3: Paper Writing
Choosing right format.
We intend to write a paper in customized layout. If you are interesting in any specific journal, we ready to support you. Otherwise we prepare in IEEE transaction level.
Collecting Reliable Resources
Before paper writing, we collect reliable resources such as 50+ journal papers, magazines, news, encyclopedia (books), benchmark datasets, and online resources.

Writing Rough Draft
We create an outline of a paper at first and then writing under each heading and sub-headings. It consists of novel idea and resources
Proofreading & Formatting
We must proofread and formatting a paper to fix typesetting errors, and avoiding misspelled words, misplaced punctuation marks, and so on
Native English Writing
We check the communication of a paper by rewriting with native English writers who accomplish their English literature in University of Oxford.
Scrutinizing Paper Quality
We examine the paper quality by top-experts who can easily fix the issues in journal paper writing and also confirm the level of journal paper (SCI, Scopus or Normal).
Plagiarism Checking
We at phdservices.org is 100% guarantee for original journal paper writing. We never use previously published works.
MILESTONE 4: Paper Publication
Finding apt journal.
We play crucial role in this step since this is very important for scholar’s future. Our experts will help you in choosing high Impact Factor (SJR) journals for publishing.
Lay Paper to Submit
We organize your paper for journal submission, which covers the preparation of Authors Biography, Cover Letter, Highlights of Novelty, and Suggested Reviewers.
Paper Submission
We upload paper with submit all prerequisites that are required in journal. We completely remove frustration in paper publishing.
Paper Status Tracking
We track your paper status and answering the questions raise before review process and also we giving you frequent updates for your paper received from journal.
Revising Paper Precisely
When we receive decision for revising paper, we get ready to prepare the point-point response to address all reviewers query and resubmit it to catch final acceptance.
Get Accept & e-Proofing
We receive final mail for acceptance confirmation letter and editors send e-proofing and licensing to ensure the originality.
Publishing Paper
Paper published in online and we inform you with paper title, authors information, journal name volume, issue number, page number, and DOI link
MILESTONE 5: Thesis Writing
Identifying university format.
We pay special attention for your thesis writing and our 100+ thesis writers are proficient and clear in writing thesis for all university formats.
Gathering Adequate Resources
We collect primary and adequate resources for writing well-structured thesis using published research articles, 150+ reputed reference papers, writing plan, and so on.
Writing Thesis (Preliminary)
We write thesis in chapter-by-chapter without any empirical mistakes and we completely provide plagiarism-free thesis.
Skimming & Reading
Skimming involve reading the thesis and looking abstract, conclusions, sections, & sub-sections, paragraphs, sentences & words and writing thesis chorological order of papers.
Fixing Crosscutting Issues
This step is tricky when write thesis by amateurs. Proofreading and formatting is made by our world class thesis writers who avoid verbose, and brainstorming for significant writing.
Organize Thesis Chapters
We organize thesis chapters by completing the following: elaborate chapter, structuring chapters, flow of writing, citations correction, etc.
Writing Thesis (Final Version)
We attention to details of importance of thesis contribution, well-illustrated literature review, sharp and broad results and discussion and relevant applications study.
How PhDservices.org deal with significant issues ?
1. novel ideas.
Novelty is essential for a PhD degree. Our experts are bringing quality of being novel ideas in the particular research area. It can be only determined by after thorough literature search (state-of-the-art works published in IEEE, Springer, Elsevier, ACM, ScienceDirect, Inderscience, and so on). SCI and SCOPUS journals reviewers and editors will always demand “Novelty” for each publishing work. Our experts have in-depth knowledge in all major and sub-research fields to introduce New Methods and Ideas. MAKING NOVEL IDEAS IS THE ONLY WAY OF WINNING PHD.
2. Plagiarism-Free
To improve the quality and originality of works, we are strictly avoiding plagiarism since plagiarism is not allowed and acceptable for any type journals (SCI, SCI-E, or Scopus) in editorial and reviewer point of view. We have software named as “Anti-Plagiarism Software” that examines the similarity score for documents with good accuracy. We consist of various plagiarism tools like Viper, Turnitin, Students and scholars can get your work in Zero Tolerance to Plagiarism. DONT WORRY ABOUT PHD, WE WILL TAKE CARE OF EVERYTHING.
3. Confidential Info
We intended to keep your personal and technical information in secret and it is a basic worry for all scholars.
- Technical Info: We never share your technical details to any other scholar since we know the importance of time and resources that are giving us by scholars.
- Personal Info: We restricted to access scholars personal details by our experts. Our organization leading team will have your basic and necessary info for scholars.
CONFIDENTIALITY AND PRIVACY OF INFORMATION HELD IS OF VITAL IMPORTANCE AT PHDSERVICES.ORG. WE HONEST FOR ALL CUSTOMERS.
4. Publication
Most of the PhD consultancy services will end their services in Paper Writing, but our PhDservices.org is different from others by giving guarantee for both paper writing and publication in reputed journals. With our 18+ year of experience in delivering PhD services, we meet all requirements of journals (reviewers, editors, and editor-in-chief) for rapid publications. From the beginning of paper writing, we lay our smart works. PUBLICATION IS A ROOT FOR PHD DEGREE. WE LIKE A FRUIT FOR GIVING SWEET FEELING FOR ALL SCHOLARS.
5. No Duplication
After completion of your work, it does not available in our library i.e. we erased after completion of your PhD work so we avoid of giving duplicate contents for scholars. This step makes our experts to bringing new ideas, applications, methodologies and algorithms. Our work is more standard, quality and universal. Everything we make it as a new for all scholars. INNOVATION IS THE ABILITY TO SEE THE ORIGINALITY. EXPLORATION IS OUR ENGINE THAT DRIVES INNOVATION SO LET’S ALL GO EXPLORING.
Client Reviews
I ordered a research proposal in the research area of Wireless Communications and it was as very good as I can catch it.
I had wishes to complete implementation using latest software/tools and I had no idea of where to order it. My friend suggested this place and it delivers what I expect.
It really good platform to get all PhD services and I have used it many times because of reasonable price, best customer services, and high quality.
My colleague recommended this service to me and I’m delighted their services. They guide me a lot and given worthy contents for my research paper.
I’m never disappointed at any kind of service. Till I’m work with professional writers and getting lot of opportunities.
- Christopher
Once I am entered this organization I was just felt relax because lots of my colleagues and family relations were suggested to use this service and I received best thesis writing.
I recommend phdservices.org. They have professional writers for all type of writing (proposal, paper, thesis, assignment) support at affordable price.
You guys did a great job saved more money and time. I will keep working with you and I recommend to others also.
These experts are fast, knowledgeable, and dedicated to work under a short deadline. I had get good conference paper in short span.
Guys! You are the great and real experts for paper writing since it exactly matches with my demand. I will approach again.
I am fully satisfied with thesis writing. Thank you for your faultless service and soon I come back again.
Trusted customer service that you offer for me. I don’t have any cons to say.
I was at the edge of my doctorate graduation since my thesis is totally unconnected chapters. You people did a magic and I get my complete thesis!!!
- Abdul Mohammed
Good family environment with collaboration, and lot of hardworking team who actually share their knowledge by offering PhD Services.
I enjoyed huge when working with PhD services. I was asked several questions about my system development and I had wondered of smooth, dedication and caring.
I had not provided any specific requirements for my proposal work, but you guys are very awesome because I’m received proper proposal. Thank you!
- Bhanuprasad
I was read my entire research proposal and I liked concept suits for my research issues. Thank you so much for your efforts.
- Ghulam Nabi
I am extremely happy with your project development support and source codes are easily understanding and executed.
Hi!!! You guys supported me a lot. Thank you and I am 100% satisfied with publication service.
- Abhimanyu
I had found this as a wonderful platform for scholars so I highly recommend this service to all. I ordered thesis proposal and they covered everything. Thank you so much!!!
Related Pages
- Privacy Policy

Home » 300+ Social Media Research Topics
300+ Social Media Research Topics

Social media has become an integral part of our lives, and it has transformed the way we communicate, share information, and interact with each other. As social media platforms continue to evolve and gain popularity, they have also become a rich source of data for researchers. Social media research is a rapidly growing field that encompasses a wide range of topics , from understanding the psychological and social effects of social media to analyzing patterns of user behavior and identifying trends in online conversations. In this era of data-driven decision-making, social media research is more important than ever, as it provides insights into how we use and are influenced by social media. In this post, we will explore some of the most fascinating and relevant social media research topics that are shaping our understanding of this powerful medium.
Social Media Research Topics
Social Media Research Topics are as follows:
- The effects of social media on mental health
- The role of social media in political polarization
- The impact of social media on relationships
- The use of social media by businesses for marketing
- The effects of social media on body image and self-esteem
- The influence of social media on consumer behavior
- The use of social media for education
- The effects of social media on language use and grammar
- The impact of social media on news consumption
- The role of social media in activism and social change
- The use of social media for job seeking and career development
- The effects of social media on sleep patterns
- The influence of social media on adolescent behavior
- The impact of social media on the spread of misinformation
- The use of social media for personal branding
- The effects of social media on political participation
- The influence of social media on fashion trends
- The impact of social media on sports fandom
- The use of social media for mental health support
- The effects of social media on creativity
- The role of social media in cultural exchange
- The impact of social media on language learning
- The use of social media for crisis communication
- The effects of social media on privacy and security
- The influence of social media on diet and exercise behavior
- The impact of social media on travel behavior
- The use of social media for citizen journalism
- The effects of social media on political accountability
- The role of social media in peer pressure
- The impact of social media on romantic relationships
- The use of social media for community building
- The effects of social media on gender identity
- The influence of social media on music consumption
- The impact of social media on academic performance
- The use of social media for social support
- The effects of social media on social skills
- The role of social media in disaster response
- The impact of social media on nostalgia and memory
- The use of social media for charity and philanthropy
- The effects of social media on political polarization in developing countries
- The influence of social media on literary consumption
- The impact of social media on family relationships
- The use of social media for citizen science
- The effects of social media on cultural identity
- The role of social media in promoting healthy behaviors
- The impact of social media on language diversity
- The use of social media for environmental activism
- The effects of social media on attention span
- The influence of social media on art consumption
- The impact of social media on cultural values and norms.
- The impact of social media on mental health
- The impact of social media on mental health.
- The impact of social media on body image and self-esteem.
- The use of social media for political activism and social justice movements.
- The role of social media in promoting cultural diversity and inclusivity.
- The impact of social media on romantic relationships and dating.
- The use of social media for customer service and support.
- The impact of social media on mental health and well-being among young adults.
- The impact of social media on political polarization and partisanship.
- The use of social media for health communication and behavior change.
- The role of social media in shaping public opinion and attitudes towards vaccination.
- The impact of social media on political participation and civic engagement.
- The impact of social media on political polarization and echo chambers.
- The use of social media for political campaigning and the manipulation of public opinion.
- The role of social media in shaping public attitudes towards vaccination and public health.
- The impact of social media on news consumption and trust in journalism.
- The use of social media for promoting sustainable fashion practices and ethical consumption.
- The role of social media in influencing beauty standards and body image.
- The impact of social media on the music industry and the role of social media influencers.
- The use of social media for promoting mental health and well-being among healthcare professionals.
- The role of social media in shaping public attitudes towards gun violence and gun control policies.
- The impact of social media on social activism and advocacy.
- The use of social media for promoting cross-cultural communication and intercultural understanding.
- The role of social media in shaping public attitudes towards climate change and environmental policies.
- The impact of social media on public health during the COVID-19 pandemic.
- The use of social media for promoting financial literacy and access to financial services for low-income individuals.
- The role of social media in shaping public attitudes towards immigration policies and refugee crises.
- The impact of social media on political activism and social movements.
- The use of social media for promoting digital literacy and technology education in developing countries.
- The role of social media in shaping public attitudes towards gender and sexual orientation.
- The impact of social media on consumer behavior in the food and beverage industry.
- The use of social media for promoting mental health and well-being among first responders.
- The role of social media in shaping public attitudes towards racial justice and police brutality.
- The impact of social media on privacy concerns and data security.
- The use of social media for promoting interfaith dialogue and religious tolerance.
- The role of social media in shaping public attitudes towards income inequality and economic justice.
- The impact of social media on the film and television industry and consumer behavior.
- The use of social media for promoting mental health and well-being among military personnel.
- The role of social media in shaping public attitudes towards privacy and data security.
- The impact of social media on the hospitality industry and consumer behavior.
- The use of social media for promoting intergenerational communication and understanding.
- The role of social media in shaping public attitudes towards animal welfare and animal rights.
- The impact of social media on the gaming industry and gamer behavior.
- The use of social media for promoting digital literacy and technology skills among seniors.
- The role of social media in shaping public attitudes towards renewable energy and sustainability.
- The impact of social media on the advertising industry and consumer behavior.
- The use of social media for promoting mental health and well-being among children and adolescents.
- The role of social media in shaping public attitudes towards online privacy and security.
- The impact of social media on the beauty industry and consumer behavior.
- The use of social media for promoting cultural preservation and heritage tourism.
- The role of social media in shaping public attitudes towards criminal justice reform.
- The impact of social media on the automotive industry and consumer behavior.
- The use of social media for promoting mental health and well-being among marginalized communities.
- The role of social media in shaping public attitudes towards sustainable development goals.
- The impact of social media on the fashion industry and consumer behavior.
- The use of social media for promoting intercultural communication in the workplace.
- The role of social media in shaping public attitudes towards mental health policies.
- The impact of social media on the travel industry and sustainable tourism practices.
- The use of social media for health information seeking and patient empowerment.
- The role of social media in promoting environmental activism and sustainable practices.
- The impact of social media on consumer behavior and brand loyalty.
- The use of social media for promoting education and lifelong learning.
- The role of social media in shaping public opinion and attitudes towards mental health issues.
- The impact of social media on the fashion industry and fast fashion practices.
- The use of social media for promoting social entrepreneurship and social innovation.
- The role of social media in shaping public opinion and attitudes towards gun control.
- The impact of social media on the mental health and well-being of adolescents.
- The use of social media for promoting intercultural exchange and understanding.
- The role of social media in shaping public opinion and attitudes towards climate change.
- The impact of social media on political advertising and campaign strategies.
- The use of social media for promoting healthy relationships and communication skills.
- The role of social media in shaping public opinion and attitudes towards police brutality and racial justice.
- The use of social media for promoting financial literacy and personal finance management.
- The role of social media in shaping public opinion and attitudes towards LGBTQ+ rights.
- The impact of social media on the music industry and fan engagement.
- The use of social media for promoting mental health and well-being among marginalized populations.
- The role of social media in shaping public opinion and attitudes towards immigration and border policies.
- The impact of social media on the professional development and networking of journalists.
- The use of social media for promoting community building and social cohesion.
- The role of social media in shaping public opinion and attitudes towards healthcare policies.
- The impact of social media on the food industry and consumer behavior.
- The role of social media in shaping public opinion and attitudes towards gender equality.
- The impact of social media on the sports industry and athlete-fan interactions.
- The use of social media for promoting financial inclusion and access to banking services.
- The role of social media in shaping public opinion and attitudes towards animal welfare.
- The use of social media for promoting mental health and well-being among college students.
- The role of social media in shaping public opinion and attitudes towards privacy and data security.
- The role of social media in shaping public opinion and attitudes towards income inequality and poverty.
- The use of social media for promoting digital literacy and technology skills.
- The role of social media in shaping public opinion and attitudes towards renewable energy.
- The use of social media for promoting mental health and well-being among elderly populations.
- The role of social media in shaping public opinion and attitudes towards online privacy and security.
- The role of social media in shaping public opinion and attitudes towards criminal justice reform.
- The impact of social media on online activism and social movements.
- The use of social media for business-to-business communication and networking.
- The role of social media in promoting civic education and engagement.
- The impact of social media on the fashion industry and sustainable fashion practices.
- The use of social media for promoting cultural diversity and inclusion.
- The role of social media in shaping public opinion and attitudes towards police reform.
- The impact of social media on the mental health and well-being of frontline healthcare workers.
- The use of social media for promoting financial literacy and investment education.
- The role of social media in promoting environmental sustainability and conservation.
- The impact of social media on body image and self-esteem among adolescent girls.
- The use of social media for promoting intercultural dialogue and understanding.
- The role of social media in shaping public opinion and attitudes towards immigration policies and refugees.
- The impact of social media on the professional development and networking of healthcare professionals.
- The use of social media for promoting community resilience and disaster preparedness.
- The role of social media in shaping public opinion and attitudes towards the Black Lives Matter movement.
- The impact of social media on the music industry and artist-fan interactions.
- The use of social media for promoting healthy eating habits and nutrition education.
- The role of social media in promoting mental health and well-being among college students.
- The impact of social media on the entertainment industry and consumer behavior.
- The use of social media for promoting workplace diversity and inclusion.
- The role of social media in shaping public opinion and attitudes towards climate change policies.
- The impact of social media on the travel industry and consumer behavior.
- The use of social media for promoting mental health and well-being among military veterans.
- The role of social media in promoting intergenerational dialogue and understanding.
- The impact of social media on the professional development and networking of educators.
- The use of social media for promoting animal welfare and advocacy.
- The role of social media in shaping public opinion and attitudes towards reproductive rights.
- The impact of social media on the sports industry and fan behavior.
- The use of social media for promoting financial inclusion and literacy among underprivileged populations.
- The role of social media in promoting mental health and well-being among LGBTQ+ populations.
- The impact of social media on the food and beverage industry and consumer behavior.
- The use of social media for promoting interfaith dialogue and understanding.
- The role of social media in shaping public opinion and attitudes towards gun ownership.
- The use of social media for promoting mental health and well-being among caregivers.
- The role of social media in promoting sustainable tourism practices.
- The impact of social media on the gaming industry and gamer culture.
- The use of social media for promoting cultural heritage tourism and preservation.
- The role of social media in shaping public opinion and attitudes towards public transportation policies.
- The use of social media for promoting mental health and well-being among homeless populations.
- The role of social media in promoting mental health and well-being among immigrants and refugees.
- The use of social media for promoting financial literacy and entrepreneurship among youth.
- The use of social media for political mobilization and participation in authoritarian regimes.
- The role of social media in shaping public opinion and attitudes towards immigration policies.
- The impact of social media on the professional development of teachers and educators.
- The use of social media for emergency communication during public health crises.
- The role of social media in promoting LGBTQ+ rights and advocacy.
- The impact of social media on body positivity and self-acceptance among women.
- The use of social media for public diplomacy and international relations.
- The impact of social media on the mental health and well-being of marginalized communities.
- The use of social media for crisis management and disaster response in the corporate sector.
- The role of social media in promoting environmental activism and conservation.
- The impact of social media on the professional development and networking of entrepreneurs.
- The use of social media for medical education and healthcare communication.
- The role of social media in promoting cultural exchange and understanding.
- The impact of social media on social capital and civic engagement among young adults.
- The use of social media for disaster preparedness and community resilience.
- The role of social media in promoting religious pluralism and tolerance.
- The use of social media for promoting healthy lifestyles and wellness.
- The use of social media for fundraising and philanthropy in the non-profit sector.
- The role of social media in promoting interfaith dialogue and understanding.
- The impact of social media on the travel and tourism industry and consumer behavior.
- The use of social media for customer engagement and brand loyalty in the retail sector.
- The impact of social media on the political attitudes and behaviors of young adults.
- The use of social media for promoting gender equality and women’s empowerment.
- The use of social media for promoting animal welfare and adoption.
- The role of social media in promoting mental health and well-being among the elderly.
- The impact of social media on the art industry and artist-fan interactions.
- The use of social media for promoting healthy food choices and nutrition.
- The role of social media in shaping public opinion and attitudes towards income inequality.
- The use of social media for promoting political satire and humor.
- The role of social media in promoting disability rights and advocacy.
- The use of social media for promoting voter registration and participation.
- The role of social media in promoting entrepreneurship and small business development.
- The use of social media for promoting mental health and well-being among incarcerated populations.
- The role of social media in shaping public opinion and attitudes towards gun violence prevention.
- The use of social media for promoting cultural heritage and preservation.
- The impact of social media on mental health and well-being.
- The relationship between social media use and academic performance.
- The use of social media for emergency communication during natural disasters.
- The impact of social media on traditional news media and journalism.
- The role of social media in shaping public opinion and discourse.
- The use of social media for online learning and education.
- The impact of social media on the fashion and beauty industry.
- The use of social media for brand awareness and marketing.
- The impact of social media on privacy and security.
- The use of social media for job searching and recruitment.
- The impact of social media on political polarization and extremism.
- The use of social media for online harassment and cyberbullying.
- The role of social media in promoting environmental awareness and sustainability.
- The impact of social media on youth culture and identity formation.
- The use of social media for travel and tourism marketing.
- The impact of social media on consumer behavior and decision-making.
- The role of social media in shaping beauty standards and body positivity.
- The use of social media for crisis communication and disaster response.
- The impact of social media on the music industry.
- The use of social media for fundraising and philanthropy.
- The role of social media in promoting healthy lifestyles and wellness.
- The impact of social media on sports fandom and fan behavior.
- The use of social media for political lobbying and advocacy.
- The impact of social media on the entertainment industry.
- The use of social media for healthcare communication and patient engagement.
- The role of social media in promoting gender equality and feminism.
- The impact of social media on the restaurant and food industry.
- The use of social media for volunteerism and community service.
- The role of social media in promoting religious tolerance and interfaith dialogue.
- The impact of social media on the art industry.
- The use of social media for political satire and humor.
- The role of social media in promoting disability awareness and advocacy.
- The impact of social media on the real estate industry.
- The use of social media for legal advocacy and justice reform.
- The role of social media in promoting intercultural communication and understanding.
- The impact of social media on the automotive industry.
- The use of social media for pet adoption and animal welfare advocacy.
- The role of social media in promoting mental health and wellness for marginalized communities.
- The impact of social media on the retail industry.
- The use of social media for promoting civic engagement and voter participation.
- The impact of social media on the film and television industry.
- The use of social media for fashion and style inspiration.
- The role of social media in promoting activism for human rights and social issues.
- The effectiveness of social media for political campaigns.
- The role of social media in promoting fake news and misinformation.
- The impact of social media on self-esteem and body image.
- The impact of social media on romantic relationships.
- The use of social media for online activism and social justice movements.
- The impact of social media on traditional news media.
- The impact of social media on interpersonal communication skills.
- The impact of social media on the fashion industry.
- The use of social media for social support and mental health awareness.
- The use of social media for political lobbying and activism.
- The impact of social media on travel and tourism behavior.
- The use of social media for customer feedback and market research.
- The impact of social media on the restaurant industry.
- The role of social media in political activism
- The effect of social media on interpersonal communication
- The relationship between social media use and body image concerns
- The impact of social media on self-esteem
- The role of social media in shaping cultural norms and values
- The use of social media by celebrities and its impact on their image
- The role of social media in building and maintaining personal relationships
- The use of social media for job searching and recruitment
- The impact of social media on children and adolescents
- The use of social media by political candidates during election campaigns
- The role of social media in education
- The impact of social media on political polarization
- The use of social media for news consumption
- The effect of social media on sleep habits
- The use of social media by non-profit organizations for fundraising
- The role of social media in shaping public opinion
- The influence of social media on language and communication patterns
- The use of social media in crisis communication and emergency management
- The role of social media in promoting environmental awareness
- The influence of social media on music preferences
- The impact of social media on body positivity movements
- The role of social media in shaping beauty standards
- The influence of social media on sports fandom
- The use of social media for health promotion and education
- The impact of social media on political participation
- The role of social media in shaping parenting practices
- The influence of social media on food preferences and eating habits
- The use of social media for peer support and mental health advocacy
- The role of social media in shaping religious beliefs and practices
- The influence of social media on humor and comedy
- The use of social media for online activism and social justice advocacy
- The impact of social media on public health awareness campaigns
- The role of social media in promoting cultural diversity and inclusion
- The influence of social media on travel behavior and decision-making
- The use of social media for international diplomacy and relations
- The impact of social media on job satisfaction and employee engagement
- The role of social media in shaping romantic preferences and dating behavior
- The influence of social media on language learning and language use
- The use of social media for political satire and humor
- The impact of social media on social capital and community building
- The role of social media in shaping gender identity and expression
- The influence of social media on fashion and beauty advertising.
About the author
Muhammad Hassan
Researcher, Academic Writer, Web developer
You may also like

200+ Funny Research Topics

500+ Sports Research Topics

300+ American History Research Paper Topics

500+ Cyber Security Research Topics

500+ Environmental Research Topics

500+ Economics Research Topics

Latest Research Topics in Networking
Latest Research Topics in Networking offer newfangled project topics for our students from bachelors and master degree (B.E/M.E/M.Phil/M.Tech/MCA) in the field of networking. Networking is the biggest and fastest emerging area, making it hinder students with new research into networking technologies. However, students spend more money on their networking projects. To help our students, we also offer the latest networking projects at optimum cost as far as we also provided 5000+ projects from 120+ countries students from all over the world.
We develop projects both in software and hardware, and in software, we use both open source and proprietary software. We also suggest our students always choose the latest topics because the latest ideas only give something innovative and colorful.
Think well…Always be a part of us… we pose your pioneering projects…..
Topics in Networking
Latest Research Topics in Networking covers possible list of topics intended also for under graduate and also post graduate students and scholars. In networking, security is one of the major issues in all types of wired and wireless networks, e.g., cloud networking. There is also a lot of research in the networking field because it is also a vast area that prefers among more users.
Generally, networking is defined as the computing devices that exchange information and share ideas among individuals or groups of devices or users using either wired or wireless connection.
Let us see the latest topics in networking,
- Secure and control sensitive data also in cloud environment (any)
- The future of IoT and also bio metrics
- Software defined networking
- Network security and also cryptography
- Network Function Virtualization
- Cognitive computing and also machine learning
- Micro services architecture
- Adaptive security
- Augmented and virtual reality
- Cloud networking
- Big data analytics in mobile networking
- Smart personal assistants
- Wearable’s in sensor networks
- Blockchain as a service (BaaS)
- Containerization (traditional virtualization)
- Resource allocation SDN
- Ultra dense wireless networks planning
- SDN + Virtualized radio Access Networks also with Fog computing
- Spectrum efficiency enhancement by LTE-U also with Wi-Fi
- 5G wireless backhaul networks
- SDN based Elastic optical networks also in cloud.
- Green mobile cloud network: Green cloudlet
- C-RAN: Cloud Radio Access Network
- 5G networks multicasting
- Traffic engineering also in software defined networks
- D2D communication in 5G
- Over Wi-Fi secure device-to-device communication
- Cloud Robotics
- 5G networks for visible light communication
- Big data in mobile cloud networks
- Prevention and also in detection of network attacks
- SDN network automation to 802.11ac and also in IPv6
Simulation Tools, Software’s and Programming Languages Used in Networking Projects
Programming languages:.
- R-programming
- Matlab and also in scilab
Simulation Software’s:
- Psimulator2
- Network simulators (NS2 and also in NS3)
Other Tools:
- Matlab Simulink
- Matlab tool boxes
- Word net tool
- And also in MADAMIRA tool
We also provide a few collections of networking and simulation tools, software, and programming languages for developing projects in the networking and other areas. For each project, we give PPT, documents, video files, and also completed code implementation. Our additional support for our students is journal paper writing support, paper publication in high reputed journals, and thesis writing support.
A good beginning is often overt as happy endings…..
Let us come together for your immense research…… , related pages, services we offer.
Mathematical proof
Pseudo code
Conference Paper
Research Proposal
System Design
Literature Survey
Data Collection
Thesis Writing
Data Analysis
Rough Draft
Paper Collection
Code and Programs
Paper Writing
Course Work
- How It Works
- PhD thesis writing
- Master thesis writing
- Bachelor thesis writing
- Dissertation writing service
- Dissertation abstract writing
- Thesis proposal writing
- Thesis editing service
- Thesis proofreading service
- Thesis formatting service
- Coursework writing service
- Research paper writing service
- Architecture thesis writing
- Computer science thesis writing
- Engineering thesis writing
- History thesis writing
- MBA thesis writing
- Nursing dissertation writing
- Psychology dissertation writing
- Sociology thesis writing
- Statistics dissertation writing
- Buy dissertation online
- Write my dissertation
- Cheap thesis
- Cheap dissertation
- Custom dissertation
- Dissertation help
- Pay for thesis
- Pay for dissertation
- Senior thesis
- Write my thesis
100 Best Media Topics For Research Writing

We know you need the best media topics for your next papers. Otherwise, why would you be reading this blog post? The good news is that you have picked the best place to look for topics. Our experienced writers have put together a list of the best media topics for high school and college students. Furthermore, we work hard to keep the list fresh. This means that these ideas will be most likely original. They will work great in 2023 because the list of media essay topics is updated periodically.
The Importance of Great Media Topics
You are probably wondering why we are putting so much emphasis on getting you the best media topics to write about. There are several reasons for it, but we will only tell you about 3 of them:
- Your professor will greatly appreciate your willingness to dedicate the time and effort to finding excellent topics . Trust us, professors know how to make the difference between students based solely on the topics they choose for their papers.
- It is much easier to write essays if you choose good media essays topics . A topic you know something about is the best choice. Also, a good topic enables you to quickly find plenty of information on the Internet. Following this advice you’ll easily write your literature review and the following components of your paper.
- By choosing a great topic, your essay will immediately stand out from all the rest . Your professor is surely bored of reading papers written about the same things over and over again. An interesting idea will entice him to award you at least some bonus points.
Mass Media Topics
Mass media is something of great importance in modern times, so why not write your papers on some mass media topics? Here are some great examples:
- The effect of mass media on psychological health
- Mass media and emotional health
- Mass media addiction in the US
- The role of mass media in politics
- The First Amendment in mass media
- Promoting sexuality in mass media
Media Research Topics
Did your professor ask of you to write a research paper? No problem, we have some excellent media research topics in our list. Check them out below:
- Discuss children media
- Violence in mass media in the US
- Video games in the media
- Controversial topics in the media in Europe
- Discuss post-truth in the media
- Media regulations in China
Media Analysis Essay Topics for Presentation
Would you like to write a media analysis paper for a presentation? It’s not difficult to do, if you pick the right media analysis essay topics for presentation. Here are some excellent ideas:
- Is the media creating events or reacting to them?
- Media and public relations links
- Discuss 3 major types of media
- The use of media in education (one of the most interesting mass media research paper topics)
- Influence of virtual reality on the media (one of the best media analysis essay topics)
- Discuss journalism ethics
Media Research Paper Topics for High School
Are you a high school student looking for some awesome topic for his next research paper on media? Here are some excellent examples of media research paper topics for high school:
- Major innovations in 21st century media
- Compare mainstream media in India and China
- What makes an outlet a reliable source?
- Advertisements in media
- Benefits of mass media for society
- Compare traditional media with mass media
Mass Media Research Topics
If you need to write a research paper and want to talk about something in mass media, we have some very nice ideas right here. Check out our mass media research topics:
- The right of expression in mass media
- Journalism in mass media
- Compare TV, film and radio
- Mass media in democracy
- The war against terror in mass media
- Discuss the rise of mobile media
Media Research Topics for College Students
College students who are looking to research topics about media should choose something that can bring them a top grade. Here are our best media research topics for college students:
- Influences of technology on media
- Latest innovations in media
- Discuss media censorship in China (a recommended media related topic)
- What is media propaganda?
- Mass media and its preemptive effects
Complex Media Related Research Topics
Do you want to try your hand at some difficult topics? If you want to impress your professor, we advise you to select one of these complex media related research topics:
- Mass media violating civil rights
- Does media benefit the economy of the US?
- Define media addition and discuss its effects
- Perform a qualitative analysis of 3 media outlets
- Media’s scare strategies: a case study
- Media influencing a rise in violence in the UK
Controversial Media Topics
Why should you be frightened by controversial topics? You are free to write about them, of course. Here are our best and most controversial media topics:
- Exercising the First Amendment in media in the US
- Promoting gun violence in mass media
- Mass media effects on terrorism
- Digital media is destroying traditional media
- Artificial intelligence in mass media
- Media effects on the death penalty in China
Digital Media Topics
Discussing digital media is a very good way to impress your professor. Let’s face it; the digital realm is extremely popular these days. Here are some brand new digital media topics:
- Define and discuss digital media
- Climate change in digital media
- What is mobile media?
- The fate of journalism in the 21st century (one of the best digital media research topics)
- Effects of digital media on politics
Media Analysis Topics
Writing a media analysis essay can be a very difficult task, especially if you don’t have much academic writing experience. Here are some media analysis topics that should make things easier:
- How Trump lost the media war
- Biden’s coverage in mass media in the United States
- Advertising revenue in media outlets
- Analyze screen time
- What are deepfakes and how to spot one?
- The crisis of journalism in the 21st century
Easy Media Related Topics
The perfect choice for times when you simply cannot afford to spend too much time writing your essay, our list easy media related topics is right here:
- Define mass media in the United Kingdom
- Should children watch the news?
- Promoting violence in mass media
- Spreading awareness via media
- Are newspapers still relevant today?
- The very first occurrence of mass media
Research Topics in Media and Communication
Would you like to talk about media and communication? It is not an easy subject to write about, but we can make things easier. Here are the easiest research topics in media and communication:
- Discuss body image in media
- Analyze children’s advertising tactics
- Freedom of speech in the media
- Copyright law in the media
- Define symmetrical dialogue in the media
Media Debate Topics
Are you interested in a media debate? Getting the best topics for 2023 should be your primary concern in this case. We have some very interesting media debate topics right here:
- The impact of public relations on communities
- Location-based advertising in modern media
- Analyze the concept of yellow journalism
- Good news vs bad news in the media
- Discuss the concept of proportionality in media
Brand New Media Topics
Just like you, our writers are interested in writing about the latest topics. Why don’t you pick one of our brand new media topics?
- Is radio still an important part of media?
- Newspapers going bankrupt in 2023
- Sexual content on TV shows
- Politicians’ love for the media
- Is the backing of the media important for a president?
Media Ethics Topics
Discussing ethics in relation to media is a very interesting choice. It can also get you an A+ on your next paper. Here are some exceptional media ethics topics:
- Including graphic images in media
- Depicting terrorism on TV
- Regulating newspapers in Europe
- Celebrity gossip in the media
- The influence of large media corporations
Media Law Topics
Yes, there is such a thing as media law. Would you like to write an essay about it? Here are some great ideas for media law topics:
- Discuss the First Amendment and media
- The responsibilities of journalists
- Journalists in war zones
- Fake news in the media
- Showing unsuitable content to children
Research Topics in Communication and Media Studies
Writing about communication and media studies has the potential to help you get a top grade. Here are our best research topics in communication and media studies:
- Analyze media bias in the United States
- Is digital media addictive?
- Influence of media on religion
Interesting Media Topics
We know, you want the most interesting media topics to write about. Pick one of these and write a paper that will impress your professor:
- State-controlled media in China
- Effects of media coverage on criminal trials
- The power of mass media in 2023
Trending Media Topics
You may not know which topics are trending when it comes to media, but our writers do. Here are the latest trending media topics:
- The war in Afghanistan
- Joe Biden’s rise to power
- The fall of Donald Trump
- Climate change problems
- Global warming in the media
But what if you need more topics or professional help with thesis ? What if you didn’t find the media research topic you were looking for in the list above? While this is highly unlikely, we are prepared to help you. Would you like to talk about media literacy? In case you do, our ENL writers can create a list of the most interesting (and new) media literacy topics you can find. For anything you need, just get in touch with us.
Leave a Reply Cancel reply
Your email address will not be published. Required fields are marked *
Comment * Error message
Name * Error message
Email * Error message
Save my name, email, and website in this browser for the next time I comment.
As Putin continues killing civilians, bombing kindergartens, and threatening WWIII, Ukraine fights for the world's peaceful future.
Ukraine Live Updates

Choose Your Test
Sat / act prep online guides and tips, 113 great research paper topics.
General Education
One of the hardest parts of writing a research paper can be just finding a good topic to write about. Fortunately we've done the hard work for you and have compiled a list of 113 interesting research paper topics. They've been organized into ten categories and cover a wide range of subjects so you can easily find the best topic for you.
In addition to the list of good research topics, we've included advice on what makes a good research paper topic and how you can use your topic to start writing a great paper.
What Makes a Good Research Paper Topic?
Not all research paper topics are created equal, and you want to make sure you choose a great topic before you start writing. Below are the three most important factors to consider to make sure you choose the best research paper topics.
#1: It's Something You're Interested In
A paper is always easier to write if you're interested in the topic, and you'll be more motivated to do in-depth research and write a paper that really covers the entire subject. Even if a certain research paper topic is getting a lot of buzz right now or other people seem interested in writing about it, don't feel tempted to make it your topic unless you genuinely have some sort of interest in it as well.
#2: There's Enough Information to Write a Paper
Even if you come up with the absolute best research paper topic and you're so excited to write about it, you won't be able to produce a good paper if there isn't enough research about the topic. This can happen for very specific or specialized topics, as well as topics that are too new to have enough research done on them at the moment. Easy research paper topics will always be topics with enough information to write a full-length paper.
Trying to write a research paper on a topic that doesn't have much research on it is incredibly hard, so before you decide on a topic, do a bit of preliminary searching and make sure you'll have all the information you need to write your paper.
#3: It Fits Your Teacher's Guidelines
Don't get so carried away looking at lists of research paper topics that you forget any requirements or restrictions your teacher may have put on research topic ideas. If you're writing a research paper on a health-related topic, deciding to write about the impact of rap on the music scene probably won't be allowed, but there may be some sort of leeway. For example, if you're really interested in current events but your teacher wants you to write a research paper on a history topic, you may be able to choose a topic that fits both categories, like exploring the relationship between the US and North Korea. No matter what, always get your research paper topic approved by your teacher first before you begin writing.
113 Good Research Paper Topics
Below are 113 good research topics to help you get you started on your paper. We've organized them into ten categories to make it easier to find the type of research paper topics you're looking for.
Arts/Culture
- Discuss the main differences in art from the Italian Renaissance and the Northern Renaissance .
- Analyze the impact a famous artist had on the world.
- How is sexism portrayed in different types of media (music, film, video games, etc.)? Has the amount/type of sexism changed over the years?
- How has the music of slaves brought over from Africa shaped modern American music?
- How has rap music evolved in the past decade?
- How has the portrayal of minorities in the media changed?

Current Events
- What have been the impacts of China's one child policy?
- How have the goals of feminists changed over the decades?
- How has the Trump presidency changed international relations?
- Analyze the history of the relationship between the United States and North Korea.
- What factors contributed to the current decline in the rate of unemployment?
- What have been the impacts of states which have increased their minimum wage?
- How do US immigration laws compare to immigration laws of other countries?
- How have the US's immigration laws changed in the past few years/decades?
- How has the Black Lives Matter movement affected discussions and view about racism in the US?
- What impact has the Affordable Care Act had on healthcare in the US?
- What factors contributed to the UK deciding to leave the EU (Brexit)?
- What factors contributed to China becoming an economic power?
- Discuss the history of Bitcoin or other cryptocurrencies (some of which tokenize the S&P 500 Index on the blockchain) .
- Do students in schools that eliminate grades do better in college and their careers?
- Do students from wealthier backgrounds score higher on standardized tests?
- Do students who receive free meals at school get higher grades compared to when they weren't receiving a free meal?
- Do students who attend charter schools score higher on standardized tests than students in public schools?
- Do students learn better in same-sex classrooms?
- How does giving each student access to an iPad or laptop affect their studies?
- What are the benefits and drawbacks of the Montessori Method ?
- Do children who attend preschool do better in school later on?
- What was the impact of the No Child Left Behind act?
- How does the US education system compare to education systems in other countries?
- What impact does mandatory physical education classes have on students' health?
- Which methods are most effective at reducing bullying in schools?
- Do homeschoolers who attend college do as well as students who attended traditional schools?
- Does offering tenure increase or decrease quality of teaching?
- How does college debt affect future life choices of students?
- Should graduate students be able to form unions?

- What are different ways to lower gun-related deaths in the US?
- How and why have divorce rates changed over time?
- Is affirmative action still necessary in education and/or the workplace?
- Should physician-assisted suicide be legal?
- How has stem cell research impacted the medical field?
- How can human trafficking be reduced in the United States/world?
- Should people be able to donate organs in exchange for money?
- Which types of juvenile punishment have proven most effective at preventing future crimes?
- Has the increase in US airport security made passengers safer?
- Analyze the immigration policies of certain countries and how they are similar and different from one another.
- Several states have legalized recreational marijuana. What positive and negative impacts have they experienced as a result?
- Do tariffs increase the number of domestic jobs?
- Which prison reforms have proven most effective?
- Should governments be able to censor certain information on the internet?
- Which methods/programs have been most effective at reducing teen pregnancy?
- What are the benefits and drawbacks of the Keto diet?
- How effective are different exercise regimes for losing weight and maintaining weight loss?
- How do the healthcare plans of various countries differ from each other?
- What are the most effective ways to treat depression ?
- What are the pros and cons of genetically modified foods?
- Which methods are most effective for improving memory?
- What can be done to lower healthcare costs in the US?
- What factors contributed to the current opioid crisis?
- Analyze the history and impact of the HIV/AIDS epidemic .
- Are low-carbohydrate or low-fat diets more effective for weight loss?
- How much exercise should the average adult be getting each week?
- Which methods are most effective to get parents to vaccinate their children?
- What are the pros and cons of clean needle programs?
- How does stress affect the body?
- Discuss the history of the conflict between Israel and the Palestinians.
- What were the causes and effects of the Salem Witch Trials?
- Who was responsible for the Iran-Contra situation?
- How has New Orleans and the government's response to natural disasters changed since Hurricane Katrina?
- What events led to the fall of the Roman Empire?
- What were the impacts of British rule in India ?
- Was the atomic bombing of Hiroshima and Nagasaki necessary?
- What were the successes and failures of the women's suffrage movement in the United States?
- What were the causes of the Civil War?
- How did Abraham Lincoln's assassination impact the country and reconstruction after the Civil War?
- Which factors contributed to the colonies winning the American Revolution?
- What caused Hitler's rise to power?
- Discuss how a specific invention impacted history.
- What led to Cleopatra's fall as ruler of Egypt?
- How has Japan changed and evolved over the centuries?
- What were the causes of the Rwandan genocide ?

- Why did Martin Luther decide to split with the Catholic Church?
- Analyze the history and impact of a well-known cult (Jonestown, Manson family, etc.)
- How did the sexual abuse scandal impact how people view the Catholic Church?
- How has the Catholic church's power changed over the past decades/centuries?
- What are the causes behind the rise in atheism/ agnosticism in the United States?
- What were the influences in Siddhartha's life resulted in him becoming the Buddha?
- How has media portrayal of Islam/Muslims changed since September 11th?
Science/Environment
- How has the earth's climate changed in the past few decades?
- How has the use and elimination of DDT affected bird populations in the US?
- Analyze how the number and severity of natural disasters have increased in the past few decades.
- Analyze deforestation rates in a certain area or globally over a period of time.
- How have past oil spills changed regulations and cleanup methods?
- How has the Flint water crisis changed water regulation safety?
- What are the pros and cons of fracking?
- What impact has the Paris Climate Agreement had so far?
- What have NASA's biggest successes and failures been?
- How can we improve access to clean water around the world?
- Does ecotourism actually have a positive impact on the environment?
- Should the US rely on nuclear energy more?
- What can be done to save amphibian species currently at risk of extinction?
- What impact has climate change had on coral reefs?
- How are black holes created?
- Are teens who spend more time on social media more likely to suffer anxiety and/or depression?
- How will the loss of net neutrality affect internet users?
- Analyze the history and progress of self-driving vehicles.
- How has the use of drones changed surveillance and warfare methods?
- Has social media made people more or less connected?
- What progress has currently been made with artificial intelligence ?
- Do smartphones increase or decrease workplace productivity?
- What are the most effective ways to use technology in the classroom?
- How is Google search affecting our intelligence?
- When is the best age for a child to begin owning a smartphone?
- Has frequent texting reduced teen literacy rates?

How to Write a Great Research Paper
Even great research paper topics won't give you a great research paper if you don't hone your topic before and during the writing process. Follow these three tips to turn good research paper topics into great papers.
#1: Figure Out Your Thesis Early
Before you start writing a single word of your paper, you first need to know what your thesis will be. Your thesis is a statement that explains what you intend to prove/show in your paper. Every sentence in your research paper will relate back to your thesis, so you don't want to start writing without it!
As some examples, if you're writing a research paper on if students learn better in same-sex classrooms, your thesis might be "Research has shown that elementary-age students in same-sex classrooms score higher on standardized tests and report feeling more comfortable in the classroom."
If you're writing a paper on the causes of the Civil War, your thesis might be "While the dispute between the North and South over slavery is the most well-known cause of the Civil War, other key causes include differences in the economies of the North and South, states' rights, and territorial expansion."
#2: Back Every Statement Up With Research
Remember, this is a research paper you're writing, so you'll need to use lots of research to make your points. Every statement you give must be backed up with research, properly cited the way your teacher requested. You're allowed to include opinions of your own, but they must also be supported by the research you give.
#3: Do Your Research Before You Begin Writing
You don't want to start writing your research paper and then learn that there isn't enough research to back up the points you're making, or, even worse, that the research contradicts the points you're trying to make!
Get most of your research on your good research topics done before you begin writing. Then use the research you've collected to create a rough outline of what your paper will cover and the key points you're going to make. This will help keep your paper clear and organized, and it'll ensure you have enough research to produce a strong paper.
What's Next?
Are you also learning about dynamic equilibrium in your science class? We break this sometimes tricky concept down so it's easy to understand in our complete guide to dynamic equilibrium .
Thinking about becoming a nurse practitioner? Nurse practitioners have one of the fastest growing careers in the country, and we have all the information you need to know about what to expect from nurse practitioner school .
Want to know the fastest and easiest ways to convert between Fahrenheit and Celsius? We've got you covered! Check out our guide to the best ways to convert Celsius to Fahrenheit (or vice versa).
These recommendations are based solely on our knowledge and experience. If you purchase an item through one of our links, PrepScholar may receive a commission.

Christine graduated from Michigan State University with degrees in Environmental Biology and Geography and received her Master's from Duke University. In high school she scored in the 99th percentile on the SAT and was named a National Merit Finalist. She has taught English and biology in several countries.
Ask a Question Below
Have any questions about this article or other topics? Ask below and we'll reply!
Improve With Our Famous Guides
- For All Students
The 5 Strategies You Must Be Using to Improve 160+ SAT Points
How to Get a Perfect 1600, by a Perfect Scorer
Series: How to Get 800 on Each SAT Section:
Score 800 on SAT Math
Score 800 on SAT Reading
Score 800 on SAT Writing
Series: How to Get to 600 on Each SAT Section:
Score 600 on SAT Math
Score 600 on SAT Reading
Score 600 on SAT Writing
Free Complete Official SAT Practice Tests
What SAT Target Score Should You Be Aiming For?
15 Strategies to Improve Your SAT Essay
The 5 Strategies You Must Be Using to Improve 4+ ACT Points
How to Get a Perfect 36 ACT, by a Perfect Scorer
Series: How to Get 36 on Each ACT Section:
36 on ACT English
36 on ACT Math
36 on ACT Reading
36 on ACT Science
Series: How to Get to 24 on Each ACT Section:
24 on ACT English
24 on ACT Math
24 on ACT Reading
24 on ACT Science
What ACT target score should you be aiming for?
ACT Vocabulary You Must Know
ACT Writing: 15 Tips to Raise Your Essay Score
How to Get Into Harvard and the Ivy League
How to Get a Perfect 4.0 GPA
How to Write an Amazing College Essay
What Exactly Are Colleges Looking For?
Is the ACT easier than the SAT? A Comprehensive Guide
Should you retake your SAT or ACT?
When should you take the SAT or ACT?
Stay Informed
Get the latest articles and test prep tips!
Looking for Graduate School Test Prep?
Check out our top-rated graduate blogs here:
GRE Online Prep Blog
GMAT Online Prep Blog
TOEFL Online Prep Blog
Holly R. "I am absolutely overjoyed and cannot thank you enough for helping me!”
148 Social Networking Essay Topics
🏆 best essay topics on social networking, 🔎 easy social networking research paper topics, 👍 good social networking research topics & essay examples, 🎓 most interesting social networking research titles, 💡 simple social networking essay ideas, ❓ social networking research questions.
- Schools Should Block Social Networking Sites
- Social Networking Advantages and Disadvantages
- The Uses and Abuses of Social Networking Sites
- Excessive Use of Social Networks
- Social Networks’ Advantages and Disadvantages
- People’s Attitude toward Social Networking Services
- The Role of Social Networks in the Political and Social Activism of Citizens
- Technical Communication: Social Networking Social networking can be defined as a virtual environment in which individuals form groups for a common goal of socializing.
- Is Social Networking Bad for Society? A modern person starts their day checking social networks for news and messages, during the day this person logs in and out multiple times to review various pages.
- Social Networks as a New Way of Socialization Social networks have simplified socialization and given more room to find the people and information one needs without stopping at one city or country.
- Aspects of Social Networking Social networking is a multifaceted phenomenon that differs from person to person. It has changed the way of communicating between individuals.
- Google and Social Networks This study discusses about the relationship between Google and other Social networks gives a brief introduction to Google, and how it differs from online social networking.
- Social Networking Site Facebook Facebook is a good social networking site for it allows its users to connect with friends, learn new cultures and share and/or solve some health-related issues.
- TikTok: Getting Acquainted with Social Network It is worth highlighting some of the stigmatization of TikTok. More specifically, this social network has been firmly associated with “dancing,” “lip-syncing”, etc.
- The Link Between Self-Esteem and Social Network Usage In social networks users’ social comparisons constitute a significant aspect that influences people’s perceptions of themselves as inferior to their peers.
- Social Networks Security: Ethical Issues and Practicies Social networks have been having privacy issues. This paper discusses steps that Facebook should Facebook do with the data transferred to the site by Beacon.
- Social Networking at Work: Benefits and Drawbacks Social networks are often criticized by organizations since those can be one of the major distractions for employees during the working hours.
- Social Network in Hiring Process Although some people are against checking social networks, they will still be helpful when hiring, as managers will be able to learn many candidate characteristics from them.
- Social Networks’ Impact on Relationships This paper aims at analyzing the effects of a social network as a key element of an organization, its benefits, downfalls, and effects on relationships.
- Leader–Member Exchange and Social Network Theory This paper discusses leader-member exchange theory and social network theory, their differences and similarities, and their application in the field of public health.
- Google and Social Networks: Integration Paper This integration paper is an overview of the entire week’s projects.And a discussion on the relationship between Google and Social networks.
- Social Networking: Positive and Negative Outcomes Social networking creates digital ties, but real world communication channels cease to exist, which can have numerous negative outcomes in future as people can lose ability to create new ties.
- Online Privacy on Social Networking Sites Most people do not think twice about providing this information because they assume that the site will take measures to protect their privacy.
- Social Networks: Blocking at Schools It is important for schools to block sites such as Facebook, YouTube, and Instagram to protect the students from imminent danger, even for just a few hours.
- Freedom of Speech: Restrictions in Social Networks Actions by the US government to influence free speech on Facebook, Twitter, and other such networks are acceptable, but only if they are related to national security.
- Restrictions on Freedom of Speech on Social Networks Social networks control modern restrictions on freedom of speech in many ways, affecting all aspects of people’s lives to reduce the existing imbalance and avoid open hatred.
- Security of Information Sharing on Social Networking Sites The article “Exploring the security of information sharing on social networking sites” focuses on how the social networking site causes a threat to privacy and ethical conduct.
- Employee Access to Social Networks at Work In the day and age of the rise of information technology, social media serves as a powerful tool for communication for people in all areas of life.
- Social Networks’ Destructive Impact on Society As the internet becomes the primary mode of human existence, it becomes necessary to analyze the goals and methods of the few companies that control it.
- Social Networks’ Impact on Society Social networks, while creating many development opportunities, also hinder motivation to use them due to the large flows of information and, thus, distractions.
- Political Censorship in Social Networks The aim of this work is to try to form an objective unbiased idea of what modern political censorship in social networks is.
- The Role of Social Networks in People’s Everyday Lives and Social Movements Social media has changed dramatically and is stuck in our minds in the 21st century; it has become a surrogate for live communication between people.
- An Analysis of the Discourse of Social Networks The paper presents an analysis of the discourse of social networks. It analyzes how users use dehumanizing language and normalize dangerous levels of hatred.
- Self-Esteem & Social Network Usage Link The paper states that social media and its principle of evaluation and approval in the form of likes harm the body’s self-esteem and self-image.
- Aspects of Technology and Social Network Technology and social networks occupy an important place in people’s lives and some individuals, bloggers, even combine work and persona life, as it brings them income.
- Harm From Social Networks and Internet Usage Social networks bring more harm than benefits and cause damage, not benefit to relationships, communication skills, and life quality.
- Social Networks’ Impact on Companies’ Operations Social networking has become an essential medium for marketers to connect with clients and customers and positively impact business operations.
- Epatient, Social Networking, Personal Health Record Personal Health Record (PHR) is a promising technology because it combines EHR data and information obtained directly from patients even without their participation.
- Data Mining for Predictive Social Network Analysis The paper aims to reveal the mechanism of data mining with the help of Twitter and demonstrate the overall impact of Twitter and similar platforms on present-day companies.
- How IBM Integrated Social Networks Into Their Business Information Systems Business information systems can be made more efficient by improving communication between employees as well as consumers.
- Social Networks and Support for Human Health The percentage of deaths among the people that are more involved in social networks is much lower than the rate of those who mostly prefer loneliness.
- Leader-Exchange and Social Network Theory in the Healthcare Setting Leadership in the healthcare setting is vital as it contributes to the development of efficient strategies and methods to provide high-quality services.
- Models of Small-World Social Networks In study uses the Barabási-Albert scale-free network and the Watts-Strogatz small-world network, to assess the implications of different network structures and properties of disease spread.
- Impact of Social Networks on Communication Social networks have become integral parts of everyday life, thus facilitating the exchange of information, including personal and professional.
- Social Media and Social Networking in Modern Life Social media and social networking are relatively new phenomena that already have a significant effect on society.
- Social Networking Sites as a Tool for Shy and Lonely People The use of the internet has been a factor in averting loneliness because the shy and lonely have been less inhibited in online relationships.
- McCain Online Campaign in Form of Social Networking The essay reveals facts about John McCain online campaign in form of Social Networking, discusses its process and gives advantages and disadvantages of this method.
- Privacy Issues in Social Networks Privacy issues and protective measures addressing the challenges of big data in online social networks are current problems in the field of information technology.
- E-Learning and Social Networking: Articles Comparison The paper compares two studies: “The Impact of E-Learning on End-Users Satisfaction” by Singh and “Using Online Social Networking” by Argan.
- Executives’ Compensation Levels: Social Network Analysis This paper discusses how do social network analysis measures affect the compensation levels of executive directors during different economic periods.
- Pinterest: Social Network as a Communication Channel This essay describes how social networks have been used as communication channels for marketing various brands. Pinterest use to promote companies.
- Mental Disorders and Social Networks Correlation Social media is currently a vital component of enhancing communication amongst friends and families through the sharing of personal content.
- Women’s Stress Caused by Social Networks Consumption of social networks ideas creates the desire to be perfect in women leading to low self-esteem, depression, eating disorders, and at times, to suicide.
- Social Networking Sites: Companies Fan Pages Popularity Companies use several points of appeal to attract people and retain them in their fan pages. They often use display advertising where a niche market is targeted based on the profile information.
- Social Networking Benefits in Social Life In article uses the three types of appeal to demonstrate how the Facebook social networking application can actually harm relationships.
- Social Networking Media and the Revolution This paper discusses the roles, which Facebook, Twitter and YouTube have played in speeding up activists’ activities on the world stage in the past years.
- Social Networking: Privacy and Surveillance Social networking sites make an effort to protect the personal information of its users. However, few people recognize the need to enable privacy settings.
- Company’s Social Networking Policies
- Social Networking’s Good and Bad Impacts on Kids
- Internet and Social Networking Privacy
- Children and Social Networking
- The Difference Between Social Networking Relationships and Real-Life Relationships
- Social Networking and Its Applications to Todays Culture
- The Pros and Cons of Social Networking for Teenagers: A Parent’s Guide
- Cyberbullying: Abuse and Social Networking
- Social Networking and Health
- Dangers and Privacy Violations of Social Networking
- Social Networking and Mental Health
- American Students and Social Networking
- Social Networking and Its’ Effects on Everyday Life and How People Communicate
- College Student Social Networking and Its Relationship to Perceived Social Support
- Social Networking Sites Are Taking Control Over Human Behavior and Causing Loneliness
- The Dangers and Consequences of Seeking Popularity on Social Networking Sites
- Social Networking and the Untimely Death of Intelligence
- Online Social Networking and Office Environmental Factors That Affect Worker Productivity
- Social Networking and Effects on Society
- The Evolution and Challenges of Communication and Social Networking Technology
- Social Networking Sites Are Not Responsible for Bullying Acts on the Internet
- Project Management and Social Networking Media
- Social Networking and Its Effects on Children
- Social Networking and Its Impact on the 21st Century
- The Social Networking Sites on the Study Habits of the Students
- Internet and Social Networking and Its Impact on Business
- The Link Between Social Networking and Digital Technology
- Positive and Negative Effects of Social Networking Addiction
- Social Networking Sites Negatively Affecting Our Society
- Good Social Networking and Enterprise Reports
- Database Trigger and Social Networking Option
- Social Networking Websites Who Is Reading Your Personal Information
- Using Social Networking Sites for Teaching and Learning
- Social Networking, Social and Political Awareness
- The Social Networking Industry in the Service Sector
- Social Networking Sites and Key Task of Adolescent Psychosocial Development
- Employee Selection and Recruiting Through Social Networking
- Social Networking Can Impair Communication and Identity
- Advertising Through Social Networking Websites
- Social Networking and Its Effects on Interpersonal
- Using Social Networking Sites to Meet New People
- Factors Affecting Malaysian University Students’ Purchase Intention in Social Networking Sites
- The Advantages and Disadvantages to Using Social Networking Sites to Find Dates
- Social Networking Websites Affecting Mode of Non-Verbal Communication
- The Digital Human Activity on Social Networking Sites
- Social Networking and Transformational Leadership in Learning Organizations
- Giblin Social Networking and Revenue Sharing
- Social Networking Sites: The Privacy Enemy
- Marketing Using Social Networking
- Social Networking and Freedom of Speech
- The Link Between Social Networking Sites and Narcissism
- Social Networking Furthers Participation and Communication in Politics
- Cybercrimes Committed Through Social Networking
- Social Networking and Its Impact on the Future Development of the World
- Positive and Negative Effects of Social Networking
- Social Networking Affects Our Youth
- Ethics and Social Networking: An Interdisciplinary Approach To Evaluating Online Information Disclosure
- Social Networking Has Caused More Harm Than Good to People
- Using Social Networking Websites to Improve Academic Performance
- Social Networking: Advantages and Disadvantages
- Why Isn’t Social Networking Really Social?
- How Does Social Networking Affect Our Generation?
- Does Family Composition Affect Social Networking?
- How Does Social Networking Affect Kids’ Relationships?
- Should Parents Enforce the Usage of Social Networking From Youth?
- Are Social Networking Sites Beneficial for Our Society?
- Does Online Social Networking Hinder the Development of Teenagers?
- How Does Social Networking Affect People’s Lives?
- Are Social Networking Sites Damaging the Quality of America’s Communication?
- Does Privacy Really Exist in Social Networking?
- How Does Social Networking Affect Our Community?
- Why Do Teenagers Like to Use Online Social Networking Sites?
- Are Social Networking Sites Good for Students?
- How Does Social Networking Affect Your Privacy?
- Are Social Networking Sites Necessary?
- How Far Have Chat Rooms and Social Networking Sites Changed the Way of Young People?
- Are Social Networking Sites Really Insecure?
- Why Are Social Networking Sites So Popular?
- How Has Social Networking Affected Society Media?
- Are Social Networking Sites Worth the Consequences?
- Does Social Networking Affect Our Society Negatively?
- How Have Social Networking Websites Affected Consumers’ Decision-Making Process?
- Should Congress Require Schools and Public Libraries to Block Social Networking Web Sites?
- How Does Social Networking Affect Students’ Lifestyles?
- What Are the Effects of Social Networking on Today’s Society?
- How Has Social Networking Changed Social Interactions?
- Why Do Mobile Users Trust Smartphone Social Networking Services?
- How Does Social Networking Create a Collaboration Culture?
- Are Social Networking Sites a Source of Online Harassment for Teens?
- How Has the Social Networking Changed Communication?
Cite this post
- Chicago (N-B)
- Chicago (A-D)
StudyCorgi. (2022, March 1). 148 Social Networking Essay Topics. https://studycorgi.com/ideas/social-networking-essay-topics/
"148 Social Networking Essay Topics." StudyCorgi , 1 Mar. 2022, studycorgi.com/ideas/social-networking-essay-topics/.
StudyCorgi . (2022) '148 Social Networking Essay Topics'. 1 March.
1. StudyCorgi . "148 Social Networking Essay Topics." March 1, 2022. https://studycorgi.com/ideas/social-networking-essay-topics/.
Bibliography
StudyCorgi . "148 Social Networking Essay Topics." March 1, 2022. https://studycorgi.com/ideas/social-networking-essay-topics/.
StudyCorgi . 2022. "148 Social Networking Essay Topics." March 1, 2022. https://studycorgi.com/ideas/social-networking-essay-topics/.
These essay examples and topics on Social Networking were carefully selected by the StudyCorgi editorial team. They meet our highest standards in terms of grammar, punctuation, style, and fact accuracy. Please ensure you properly reference the materials if you’re using them to write your assignment.
This essay topic collection was updated on January 9, 2024 .
Purdue Online Writing Lab Purdue OWL® College of Liberal Arts
Welcome to the Purdue Online Writing Lab
Welcome to the Purdue OWL
This page is brought to you by the OWL at Purdue University. When printing this page, you must include the entire legal notice.
Copyright ©1995-2018 by The Writing Lab & The OWL at Purdue and Purdue University. All rights reserved. This material may not be published, reproduced, broadcast, rewritten, or redistributed without permission. Use of this site constitutes acceptance of our terms and conditions of fair use.
The Online Writing Lab at Purdue University houses writing resources and instructional material, and we provide these as a free service of the Writing Lab at Purdue. Students, members of the community, and users worldwide will find information to assist with many writing projects. Teachers and trainers may use this material for in-class and out-of-class instruction.
The Purdue On-Campus Writing Lab and Purdue Online Writing Lab assist clients in their development as writers—no matter what their skill level—with on-campus consultations, online participation, and community engagement. The Purdue Writing Lab serves the Purdue, West Lafayette, campus and coordinates with local literacy initiatives. The Purdue OWL offers global support through online reference materials and services.
A Message From the Assistant Director of Content Development
The Purdue OWL® is committed to supporting students, instructors, and writers by offering a wide range of resources that are developed and revised with them in mind. To do this, the OWL team is always exploring possibilties for a better design, allowing accessibility and user experience to guide our process. As the OWL undergoes some changes, we welcome your feedback and suggestions by email at any time.
Please don't hesitate to contact us via our contact page if you have any questions or comments.
All the best,
Social Media
Facebook twitter.
Featured Topics
Featured series.
A series of random questions answered by Harvard experts.
Explore the Gazette
Read the latest.

What is ‘original scholarship’ in the age of AI?

Complex questions, innovative approaches
Early warning sign of extinction?
Epic science inside a cubic millimeter of brain.
Six layers of excitatory neurons color-coded by depth.
Credit: Google Research and Lichtman Lab
Anne J. Manning
Harvard Staff Writer
Researchers publish largest-ever dataset of neural connections
A cubic millimeter of brain tissue may not sound like much. But considering that that tiny square contains 57,000 cells, 230 millimeters of blood vessels, and 150 million synapses, all amounting to 1,400 terabytes of data, Harvard and Google researchers have just accomplished something stupendous.
Led by Jeff Lichtman, the Jeremy R. Knowles Professor of Molecular and Cellular Biology and newly appointed dean of science , the Harvard team helped create the largest 3D brain reconstruction to date, showing in vivid detail each cell and its web of connections in a piece of temporal cortex about half the size of a rice grain.
Published in Science, the study is the latest development in a nearly 10-year collaboration with scientists at Google Research, combining Lichtman’s electron microscopy imaging with AI algorithms to color-code and reconstruct the extremely complex wiring of mammal brains. The paper’s three first co-authors are former Harvard postdoc Alexander Shapson-Coe, Michał Januszewski of Google Research, and Harvard postdoc Daniel Berger.
The ultimate goal, supported by the National Institutes of Health BRAIN Initiative , is to create a comprehensive, high-resolution map of a mouse’s neural wiring, which would entail about 1,000 times the amount of data the group just produced from the 1-cubic-millimeter fragment of human cortex.
“The word ‘fragment’ is ironic,” Lichtman said. “A terabyte is, for most people, gigantic, yet a fragment of a human brain — just a minuscule, teeny-weeny little bit of human brain — is still thousands of terabytes.”
Jeff Lichtman.
Kris Snibbe/Harvard Staff Photographer
The latest map contains never-before-seen details of brain structure, including a rare but powerful set of axons connected by up to 50 synapses. The team also noted oddities in the tissue, such as a small number of axons that formed extensive whorls. Because the sample was taken from a patient with epilepsy, the researchers don’t know whether such formations are pathological or simply rare.
Lichtman’s field is connectomics, which seeks to create comprehensive catalogs of brain structure, down to individual cells. Such completed maps would unlock insights into brain function and disease, about which scientists still know very little.
Google’s state-of-the-art AI algorithms allow for reconstruction and mapping of brain tissue in three dimensions. The team has also developed a suite of publicly available tools researchers can use to examine and annotate the connectome.
“Given the enormous investment put into this project, it was important to present the results in a way that anybody else can now go and benefit from them,” said Google collaborator Viren Jain.
Next the team will tackle the mouse hippocampal formation, which is important to neuroscience for its role in memory and neurological disease.
Share this article
You might like.
Symposium considers how technology is changing academia
Seven projects awarded Star-Friedman Challenge grants
Fossil record stretching millions of years shows tiny ocean creatures on the move before Earth heats up
Excited about new diet drug? This procedure seems better choice.
Study finds minimally invasive treatment more cost-effective over time, brings greater weight loss
How far has COVID set back students?
An economist, a policy expert, and a teacher explain why learning losses are worse than many parents realize
Understanding Demand for Police Alternatives
While police brutality has sparked demands to scale back policing, public constituencies still have limited knowledge about policing alternatives. In survey experiments, we provide information about dontcallthepolice.com—a database of police alternatives—and police violence statistics and evaluate their impact on respondents’ stated likelihood of calling the police. We find information about police alternatives increases the likelihood of relying on police in violent scenarios but significantly reduces it in scenarios for which police alternatives exist. These findings hold across political affiliations, suggesting broad support for limiting police involvement to violent crises and investing in police alternatives for nonviolent situations. In a follow-up survey six months later, individuals informed about police alternatives were 12 percentage points more likely to recall that the newly available 988 government hotline is available for suicidal crises, a result highlighting the enduring effectiveness of targeted educational interventions. Our study shows that providing information on existing 911 alternatives results in increased demand for these police substitutes in non-violent situations both in the short and long run.
Special thanks to Mallory Sepler-King for allowing us to use her website for research purposes and providing general expertise on police alternatives. We are grateful to Abi Adams-Prassl, Amna Akbar, Randy Akee, Marcella Alsan, Isaiah Andrews, Manuela Angelucci, Peter Arcidiacono, David Autor, Pat Bayer, Peter Blair, Marika Cabral, Sylvain Chassang, Tony Cheng, Zoe Cullen, Janet Currie, Jeff DeSimone, Jennifer Doleac, Joe Doyle, Samantha Eyler-Driscoll, Rob Garlick, Jonah Gelbach, Arkadev Ghosh, Felipe Goncalves, Jonathan Gruber, Nathan Hendren, Anjelica Hendricks, Mitch Hoffman, Justin Holz, Kalila Jackson-Spieker, Larry Katz, Desire Kedagni, Dean Knox, Jonathan Kolstad, Phil McHarris, Jonathan Moreno-Medina, Ismael Mourifie, Aurelie Ouss, Laura Pilossoph, Michael Pollman, James Poterba, Roman Rivera, Chris Roth, Viviana Rodriguez, Felwine Sarr, Todd Sarver, Duncan Thomas, Cody Tuttle, Nastasia Watkins, Huseyin Yildirim, and seminar participants at JPAL Design Within Reach, MIT, UCSB, and the HBS Inequality in the Digital Age Conference. Omar Farrag, Mary Ann Fahmy, Lily Levine, Della Maggio, Pushkar Nimkar, Judicaël Waounwa, Alex Whitefield, and the Woodman Scholars from the Duke Economic Analytics Lab—Sanjit Beriwal, Jack Duhon, Alicia Gong, Justice Hatcher, Julia Ma, Melissa Sandoval, and Audrey Wang—provided outstanding research assistance. The study is approved by the IRB at Duke (IRB 2023-0369) and the IRB at Penn (IRB 853115) and registered at the AEA RCT Registry (AEARCTR-0011938). We gratefully acknowledge financial support from JPAL North America’s Social Policy Research Initiative and Duke Economics Department. Any errors are our own. The views expressed herein are those of the authors and do not necessarily reflect the views of the National Bureau of Economic Research.
MARC RIS BibTeΧ
Download Citation Data
Working Groups
More from nber.
In addition to working papers , the NBER disseminates affiliates’ latest findings through a range of free periodicals — the NBER Reporter , the NBER Digest , the Bulletin on Retirement and Disability , the Bulletin on Health , and the Bulletin on Entrepreneurship — as well as online conference reports , video lectures , and interviews .

Numbers, Facts and Trends Shaping Your World
Read our research on:
Full Topic List
Regions & Countries
- Publications
- Our Methods
- Short Reads
- Tools & Resources
Read Our Research On:
- Americans’ Changing Relationship With Local News
3. Sources of local news
Table of contents.
- 1. Attention to local news
- 2. Local news topics
- Americans’ changing local news providers
- How people feel about their local news media’s performance
- Most Americans think local journalists are in touch with their communities
- Interactions with local journalists
- 5. Americans’ views on the financial health of local news
- Acknowledgments
- The American Trends Panel survey methodology
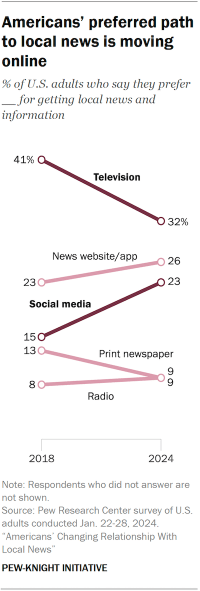
The way Americans get local news is changing, both in terms of which devices they’re using and who is delivering the news.
Television is still the most common way people prefer to get their local news, but it is no longer dominant as digital pathways to news continue to rise.
About a third of U.S. adults (32%) say they prefer to get their local news via television, a decline from 41% in 2018. Meanwhile, the share who prefer to get local news from social media has increased, from 15% in 2018 to 23% today. And roughly a quarter of adults (26%) say they prefer to use news websites. Combined, about half of U.S. adults prefer to get news through one of these digital platforms – even if the content they’re getting may be coming from traditional media outlets with an online presence.
Fewer Americans prefer print newspapers and radio for local news (9% each). The share who say they prefer print newspapers has dropped by 4 percentage points in the last six years.
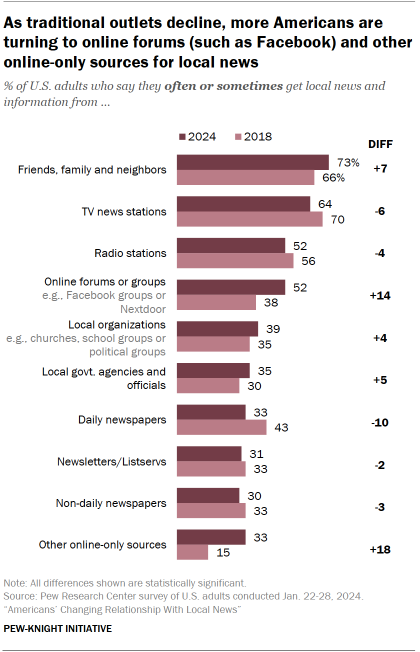
In addition to the technologies being used to access local news, the organizations and specific sources where people are getting local news also are evolving.
The share of Americans who say they often or sometimes get local news and information from daily newspapers has dropped from 43% in 2018 to 33% today – putting newspapers on par with government agencies as a source of local news. About twice as many people say they at least sometimes get news from local TV stations (64%), but this also represents a drop from 70% six years ago.
The two types of sources that have seen the most substantial growth are primarily digital by nature.
The share of U.S. adults who at least sometimes get news from online forums like Facebook groups increased from 38% in 2018 to 52% in 2024. More people also are getting news from online-only sources that aren’t included in any of the other categories (up from 15% in 2018 to 33% this year).
If respondents said they got news from one of these sources, we asked them to name (in their own words) a specific source they were thinking of as “online-only.” Respondents cited a variety of different types of sources, reflecting the complexity of the ever-changing online information environment.
Some people mentioned local websites and blogs, local news aggregator apps (such as NewsBreak), and specific Facebook groups and Instagram accounts. Others had more general responses such as social media sites more broadly (simply “Facebook”), search engines and online portals (such as Google or MSN), and outlets that cover more national news (e.g., CNN or Breitbart).
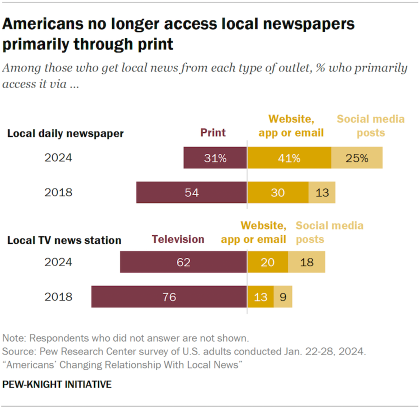
Growth in digital access extends to traditional news sources
The impact of digital technology is visible through how people access two more traditional sources of local news: daily newspapers and TV stations.
Many of these outlets now offer news not only in their original format (print and broadcast TV), but through websites and social media feeds as well. For example, among Americans who say they get news from local TV stations, a majority (62%) still say they primarily access it on a television, but 37% say they mainly access that information online – whether from a TV station’s website, app, email newsletter or social media posts.
Among those who get news from local daily newspapers, just 31% access it primarily via their print version. About two-thirds of those who get news from local daily papers (66%) primarily access them online, including 41% who say they use websites or apps and 25% who say they use social media.
How Americans access each of these types of outlets is becoming more digital. In 2018, people were more likely to access both local TV and newspapers via their original analog form: 76% of local TV consumers said they primarily accessed that news on TV, and 54% of daily newspaper users said they mostly used the print format.
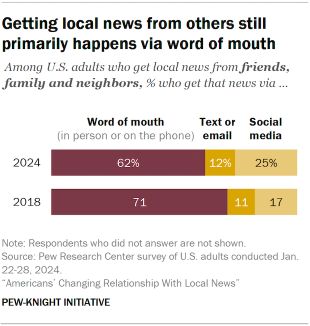
Even the way that people get information from friends and family shows signs of change.
A majority of Americans say they often (18%) or sometimes (55%) get local news from other people in their community, such as friends, family or neighbors. In 2018, a slightly smaller share said they got local news this way often (17%) or sometimes (49%).
News from friends, family and neighbors is still most often shared by word of mouth (i.e., in person or on the phone), but it is increasingly likely to be shared on social media. Among those who get local news from people in their community, 25% now say that primarily happens on social media, up from 17% in 2018.
Americans’ awareness of the outlets covering their local area
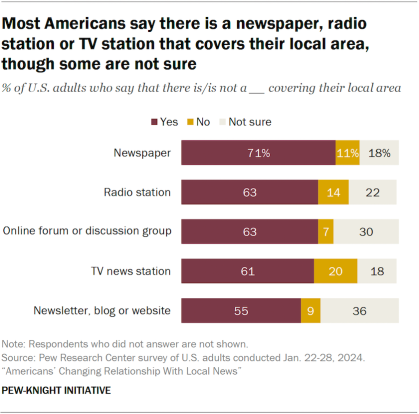
How Americans access their local news first depends on whether they have local outlets available to them – and not everyone does. Others aren’t aware if there are specific types of sources that cover their local area.
We asked Americans whether or not there are newspapers, radio stations, online forums, TV news stations, or newsletters or blogs that cover their local area. For all five types of sources, more than half of Americans say there is at least one of these covering their area, although more say this about newspapers (71%) than other types of sources.
In each case, some respondents say their area doesn’t have a certain type of news outlet. For instance, 20% of respondents say their area doesn’t have a TV station, 14% say there is no radio station and 11% say their area doesn’t have a local newspaper.
In addition, substantial shares say they are not sure whether their area has each type of source, including 30% who aren’t sure if there is an online news forum in their area and 36% who aren’t sure if there is a local newsletter, blog or website.
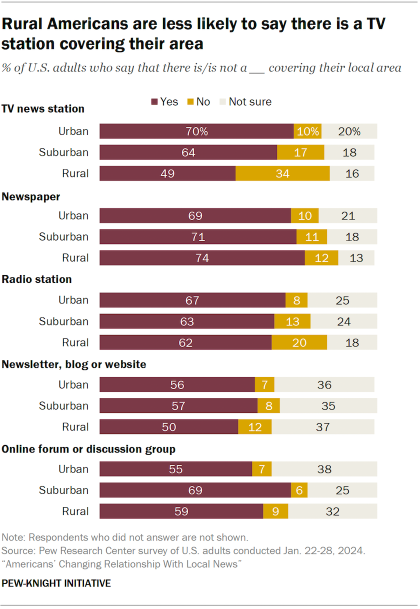
Some of this availability is connected to where respondents live – especially for local television stations. Americans who live in rural areas are much less likely to say there is a TV station covering their local area – 49% say there is, vs. 64% of those living in suburban areas and 70% of those in urban areas.
About a third of rural Americans (34%) say they do not have a TV station that covers their area, and 16% say they are not sure. By contrast, 17% of those in the suburbs and 10% of those in urban areas say there is no local TV station.
Americans in the suburbs, on the other hand, stand out for being more likely to say there are online forums or discussion groups (such as on Facebook or Nextdoor) in their local area. About seven-in-ten suburban Americans (69%) say there is at least one of these types of groups, compared with 55% of urban and 59% of rural Americans who say the same.
Sign up for our weekly newsletter
Fresh data delivery Saturday mornings
Sign up for The Briefing
Weekly updates on the world of news & information
- Digital News Landscape
- Journalists
- Trust in Media
Introducing the Pew-Knight Initiative
8 facts about black americans and the news, audiences are declining for traditional news media in the u.s. – with some exceptions, how black americans engage with local news, local tv news fact sheet, most popular, report materials.
1615 L St. NW, Suite 800 Washington, DC 20036 USA (+1) 202-419-4300 | Main (+1) 202-857-8562 | Fax (+1) 202-419-4372 | Media Inquiries
Research Topics
- Age & Generations
- Coronavirus (COVID-19)
- Economy & Work
- Family & Relationships
- Gender & LGBTQ
- Immigration & Migration
- International Affairs
- Internet & Technology
- Methodological Research
- News Habits & Media
- Non-U.S. Governments
- Other Topics
- Politics & Policy
- Race & Ethnicity
- Email Newsletters
ABOUT PEW RESEARCH CENTER Pew Research Center is a nonpartisan fact tank that informs the public about the issues, attitudes and trends shaping the world. It conducts public opinion polling, demographic research, media content analysis and other empirical social science research. Pew Research Center does not take policy positions. It is a subsidiary of The Pew Charitable Trusts .
Copyright 2024 Pew Research Center
Terms & Conditions
Privacy Policy
Cookie Settings
Reprints, Permissions & Use Policy

IMAGES
VIDEO
COMMENTS
This particular research topic can be based on setting up a live streaming server on the AWS or Azure cloud platform to make sure high network bandwidth is provided with decreased latency. The research gap analysis would be conducted to analyze the performance of live streaming servers on local and cloud environments in terms of network ...
Topic 1: An evaluation of the network security during machine to machine communication in IoT. Research Aim: The research aims to evaluate the network security issues associated with M2M communication in IoT. Objectives: To evaluate the factors affecting the network security of IoT devices. To determine the methods for increasing data integrity ...
Computer networks are a. system of i nterconnected computers for the purpose of. sharing digital information. The computer network. enables to analyze, organize and disseminate the. information ...
Explore the latest full-text research PDFs, articles, conference papers, preprints and more on COMPUTER NETWORKING. Find methods information, sources, references or conduct a literature review on ...
The International Journal of Computer and Telecommunications Networking. Computer Networks is an international, archival journal providing a publication vehicle for complete coverage of all topics of interest to those involved in the computer communications networking area. The audience includes researchers, managers and operators of networks ...
The report proposes new research directions to advance research. This paper discusses network security for secure data communication. Discover the world's research. 25+ million members;
6. Eytan Modiano, "Random Algorithms for Scheduling Multicast Traffic in WDM Broadcast-and-Select Networks," IEEE Transactions on Networking, July, 1999. 5. Eytan Modiano and Richard Barry, "Architectural Considerations in the Design of WDM-based Optical Access Networks," Computer Networks, February 1999.
All types of network architectures are getting enhanced daily, and the traditional network management process becomes more complex, especially rendering the performance during technology and entity modifications. ... This research article proposes a detailed review of SDN in the form of history, overview, architecture, benefits, services ...
We describe research that touch on both topics. First, we consider a model of data-optical inter-networking, where routes connecting end-points in data domains are concatenation of segments in the data and optical domains. The optical domain in effect acts as a carrier's carrier for multiple data domains.
Our research combines building and deploying novel networking systems at unprecedented scale, with recent work focusing on fundamental questions around data center architecture, cloud virtual networking, and wide-area network interconnects. We helped pioneer the use of Software Defined Networking, the application of ML to networking, and the ...
Ghost-USB-Honeypot project. This effort, focused on nixing malware like Flame that spreads from computer to computer via USB storage drives, got its start based on research from Sebastian Poeplau ...
A Better Approach to Networking. by. Christie Hunter Arscott. November 04, 2022. PM Images/Getty Images. Summary. Meeting strangers — especially in the context of work — is uncomfortable for ...
Nonetheless, networking is a crucial research skill for students and early career researchers, who likely find it the most intimidating. There are several benefits to research networking. It is a great way to start new collaborations, share research, learn about funding opportunities, and connect with journal editors and reviewers 2. Networking ...
A computer network is a network of diverse computing hardware linked through different communication technologies to share various resources.The communication links of the network can be either wired (cables) or wireless (radio waves / IR signals).. This page shows you useful information on Computer Network Research Topics, Projects with Source Code, Research Areas, Project Topics, and Tools!!!
Social Media Research Topics are as follows: The effects of social media on mental health. The role of social media in political polarization. The impact of social media on relationships. The use of social media by businesses for marketing. The effects of social media on body image and self-esteem.
Software defined networking. Network security and also cryptography. Network Function Virtualization. Cognitive computing and also machine learning. Micro services architecture. Adaptive security. Augmented and virtual reality. Cloud networking. Big data analytics in mobile networking.
Here are our best and most controversial media topics: Exercising the First Amendment in media in the US. Promoting gun violence in mass media. Mass media effects on terrorism. Digital media is destroying traditional media. Artificial intelligence in mass media. Media effects on the death penalty in China.
1. Introduction. Most recently, in three decades, rapid growth was marked in the field of wireless communication concerning the transition of 1G to 4G [1,2].The main motto behind this research was the requirements of high bandwidth and very low latency. 5G provides a high data rate, improved quality of service (QoS), low-latency, high coverage, high reliability, and economically affordable ...
113 Great Research Paper Topics. Posted by Christine Sarikas. General Education. One of the hardest parts of writing a research paper can be just finding a good topic to write about. Fortunately we've done the hard work for you and have compiled a list of 113 interesting research paper topics. They've been organized into ten categories and ...
Social networking is a multifaceted phenomenon that differs from person to person. It has changed the way of communicating between individuals. This study discusses about the relationship between Google and other Social networks gives a brief introduction to Google, and how it differs from online social networking.
For example, an interpretive research paper on a communication topic might evaluate why different social groups make different conclusions after perceiving the same information. Related: 12 Effective Communication Strategies To Use at Work ... Social media research topics. Social media and its influence on social movements;
The Guide for Authors and link to submit your manuscript is available on the Journal's homepage at: Guide for authors - European Journal of Operational Research - ISSN 0377-2217 | ScienceDirect.com by Elsevier. Inquiries, including questions about appropriate topics, may be sent electronically to GE (Sergio Vergalli) at Email: sergio.vergalli ...
Mission. The Purdue On-Campus Writing Lab and Purdue Online Writing Lab assist clients in their development as writers—no matter what their skill level—with on-campus consultations, online participation, and community engagement. The Purdue Writing Lab serves the Purdue, West Lafayette, campus and coordinates with local literacy initiatives.
Explore the latest full-text research PDFs, articles, conference papers, preprints and more on NETWORK TOPOLOGY. Find methods information, sources, references or conduct a literature review on ...
Measuring What is Top of Mind. Ingar K. Haaland, Christopher Roth, Stefanie Stantcheva & Johannes Wohlfart. Working Paper 32421. DOI 10.3386/w32421. Issue Date May 2024. We survey the recent literature in economics measuring what is on top of people's minds using open-ended questions. We first provide an overview of studies in political economy ...
Immigrants contribute disproportionately to entrepreneurship in many countries, accounting for a quarter of new employer businesses in the US. We review recent research on the measurement of immigrant entrepreneurship, the traits of immigrant founders, their economic impact, and policy levers. We ...
The ultimate goal, supported by the National Institutes of Health BRAIN Initiative, is to create a comprehensive, high-resolution map of a mouse's neural wiring, which would entail about 1,000 times the amount of data the group just produced from the 1-cubic-millimeter fragment of human cortex. "The word 'fragment' is ironic ...
Fewer people now say they prefer to get local news through a television set (32%, down from 41% who said the same in 2018). Americans are now more likely to say they prefer to get local news online, either through news websites (26%) or social media (23%). Both of these numbers have increased in recent years. Smaller shares prefer getting their ...
Understanding Demand for Police Alternatives. Bocar A. Ba, Meghna Baskar & Rei Mariman. Working Paper 32418. DOI 10.3386/w32418. Issue Date May 2024. While police brutality has sparked demands to scale back policing, public constituencies still have limited knowledge about policing alternatives. In survey experiments, we provide information ...
About a third of U.S. adults (32%) say they prefer to get their local news via television, a decline from 41% in 2018. Meanwhile, the share who prefer to get local news from social media has increased, from 15% in 2018 to 23% today. And roughly a quarter of adults (26%) say they prefer to use news websites.