Unsupported browser
This site was designed for modern browsers and tested with Internet Explorer version 10 and later.
It may not look or work correctly on your browser.
- PHP Scripts

11 Best PHP Learning Management System (LMS) Scripts
Whether you run an in-person school or an online learning platform, you need a learning management system (LMS) that will help you run your enterprise efficiently.
PHP learning management systems are a great option. Classes, courses, and training are now commonly delivered and administered through learning management systems. Lessons are created and uploaded on these systems and can be accessed anytime, anyplace. Learning can happen on desktops or mobile devices, with websites and apps.
In addition, PHP learning management system scripts automate every aspect of school management, from administration tasks to online classes and exams, payments, managing students, teachers and staff, and so on.
On CodeCanyon you will find learning management system scripts that will help your business excel.
Have a look at these trending PHP learning management systems .

The Best-Selling PHP Learning Management Systems on CodeCanyon for 2022
Grab one of these PHP learning management scripts and transform the way you deliver classes and run your school—whether online or in person.

At CodeCanyon, you'll find PHP learning management systems that will help you offer top-notch online learning services.
Let's have a look at the best of the best.
1. Best-Selling: Academy Learning Management Systems

One of the most comprehensive LMS scripts out there is Academy. It makes it easy for you to create and sell courses online. Students can sign up and get access to a slick, easy-to-use learning interface.
Academy also has a number of add-ons to make it even more powerful. Note: These add-ons only work with Academy LMS. You have to purchase and install Academy LMS on your web server before purchasing them.
Elegant: Academy LMS Theme

Every LMS needs a great-looking interface. Using the Elegant theme, you can give your Academy LMS site a professional look and feel.
Academy LMS Live Streaming

This addon gives Academy LMS instructors the ability to teach online courses to students using the Zoom live streaming service. If the course has no more than 100 students, you can start with Zoom’s free package.
This live streaming add-on for academy LMS is extremely secure. Zoom meeting IDs and passwords can’t be accessed by an outsider. Only valid and enrolled students are able to join in the live class with the course instructors.
Academy LMS Certificate Add-On

When students finish your course, they'll want a certificate, either for their own satisfaction or to use as proof of their qualifications in future. This add-on for Academy LMS makes it easy to create certificates that students can either download or access online.
Academy LMS Offline Payments Add-On

What can students do if they come from countries where common international payment gateways are not available, or if they don't have access for some other reason? With this add-on, you can allow students to sign up for a course and then make payment through an alternative method, such as cash, check, or wire transfer. You can then verify and approve the payment later. It's a great way of reaching out to more students.
2. Smart School: School Management System

Managing students, teachers, exams, and many other resources is crucial for any school. Smart School helps you to manage everything in a centralized way.
This modern and complete school automation software works for every educational institution. It covers all aspects of school management, from student admission to student leaving, from fee collection to exam results.
It includes 30+ modules with 8 built-in user types: super admin, admin, accountant, teacher, receptionist, librarian, parent, and student.
On the student management side, you can:
- Create a detailed student admission form that also asks for multiple documents to maintain a complete record in the student profile.
- Manage classes and teachers, assign subjects, and create a class timetable.
- Manage downloadable content for students like the syllabus, assignments, and study materials.
- Promote students to the next academic session based on results.
- Send messages to students, parents, and teachers through the noticeboard.
On the financial management side, you can:
- Use the advanced fee collection mechanism to adopt any type of fee structure.
- Implement due date, fine, discount, fees, and discount allotment based on more than five different criteria.
- Manage the school's other income and expenses.
- View and create various fee reports.
- Get various reports on students: fee statement, transactions, fee balance, attendance, and exam results.
When it comes to day-to-day logistics for the efficient running of the school, you have:
- A complete library management system for adding, issuing, and returning books.
- A system for managing school vehicles, as well as their routes and driver details.
- A system to manage school hostel rooms.
Smart School Mobile Android App Add-On
Want to make an Android app to go with your Smart School LMS? This add-on helps you create an easy-to-use app to help students access courses on their mobile phones. It's easy to customize the logo, color scheme, etc., and to enable or disable particular modules.
3. eClass Learning Management System

eClass is an all-in-one learning management system that is user-friendly, secure, scalable, reliable, expandable, and flexible. This highly affordable, highly customizable, and great-looking system comes packed with features to help you connect your audience with the right learning. It also uses SEO best practices so you can optimize your courses to sell more.
With eClass, you can build a global marketplace for learning and instruction where students can buy your courses whenever it might suit them.
4. Rocket LMS: Learning Management System

Rocket LMS is the ideal solution for a comprehensive online marketplace for selling online learning courses. In addition to a subscription system, it comes with a built-in referral and affiliate system including various commission structures so you can take advantage of its full business potential. You can receive payments offline, and it also supports over 15 worldwide payment gateways to make payments easily for all your local and international subscribers.
This multi-language script supports RTL languages so instructors can create unlimited courses in whatever language and can be accessed from all types of devices. They can create courses in video or text, quizzes, projects, files, and more. It also includes in-app live learning, multiple live class system support, and webinars. Login is by SMS or social media accounts.
Additional features of this awesome script include:
- multiple content types: video courses, live classes, text courses
- integration with YouTube or Vimeo
- Google calendar integration
5. NeonLMS: Learning Management System

Set up your online school and earn by enrolling students using NeonLMS . You can offer courses with articles, videos, and quizzes.
The bundle includes a responsive front-end website managed by a full-fledged dashboard for admin, teachers, and students. It also has a blog to publish articles and a forum to help users to communicate among themselves and learn as a group.
Admins can manage every aspect of the system. Teachers create multiple courses with lessons and tests. Users can browse through this list and enroll as students by paying for the course—they can learn anytime and from anywhere.
The LMS is built with Laravel 5.7 and comes with detailed documentation.
6. Infix Learning Management System

With the InfixLMS script, you can sell your courses directly and keep all your money. You can also go a step further and set up your own marketplace where others can sell their courses and you get a commission. As the admin, you can manage instructors, students, and courses, including payments and commissions.
Instructors can add their courses, generate coupons, view comments, and reply to students. In addition, they can view their sales history, check their earnings, request payments, and get paid. Instructors can offer classes and easily create chapters and lessons using the drag-and-drop creator. Zoom integration allows instructors to offer live classes.
Students can register on the marketplace, purchase and enroll for courses, set their own default language and currency, and download course certificates after completion. Students can leave testimonials and rate the course. They can also download class notes via PDF.
The script is SEO-ready and translation-ready—it even supports RTL languages. It integrates with different payment gateways like PayPal, Stripe, Paystack, Paytm, Razorpay, and more. This script also supports YouTube, Vimeo, and MP4.
7. Tutors Menorah: Online Video Classes Tutoring Script

Tutors Menorah is a powerful, user-friendly LMS. Anyone with a basic knowledge of computers can use this system.
Tutors Menorah automates student management, credits system, timetable management, salary management, and records.
Users can log in with their Facebook or Google accounts. They can also pay using different payment gateways like PayPal, Razorpay, Stripe, and 2Checkout.
It is also translation-ready!
8. Ramom: Multibranch School Management System

If your school, polytechnic, or university has many branches and different locations, then Ramom School Management is your ideal choice. It is an invaluable tool for planning resources for your enterprise.
A super admin can manage all branches and their staff. Each branch in turn is controlled by an admin, and information is kept separate and secure between locations.
This system also comes with language translation systems. Users can select the language they want to use for the interface and school resources.
9. InstiKit: School Management System

InstiKit is a real-time management solution for your school, college, institute, or academy. Administrative tasks take less time when you use InstiKit, so you can focus on students and improving their performance.
Here are some things you can do with InstiKit:
- Match the application to your own branding with pre-built themes and color options.
- Manage students, teachers, and staff with detailed profiles.
- Control access for students, parents, and staff with powerful roles and a permission control system.
- Create multiple academic sessions and manage courses, classes, and subjects.
- Manage fees, including billing, concession, and cancellation.
- Use a powerful library management system to manage books. Filter and search books by author, publisher, subject, and topic.
- Keep records of the books issued and returned, and track late fees and penalties.
10. iTest: Complete Online Exams System

iTest is a dynamic system dedicated to managing exams that students can take online. Through this system, you can manage and track information on students, parents, and teachers.
The admin and teachers can:
- create and manage question banks
- manage the question levels: basic, intermediate, advanced
- manage online exam instructions
- send private and group messaging for all users
This LMS is available in 15 different languages!
Free PHP Learning Management Systems

This fully responsive Online Learning Management System is built using PHP and MySQL and can be used for modular distance learning. The system has three types of users: admin, teachers, and students. The admin is in charge of maintaining important data such as the list of subjects, classes, departments, etc. Teachers can upload courses and create quizzes and assignments. Students can answer quizzes within the time allotted by the teacher.
Online E-Learning System Using PHP and MySQLi
This E-Learning System is an online framework that is made with PHP, JavaScript, Bootstrap layouts, jQuery, and a MySQL database. It is perfect for online exercises and tests.
Advanced School Management System With Complete Features

Using this script, you can manage all aspects of running a school. Admins manage the records for teachers, students, and parents, including viewing and editing personal information, all accounting, and school transportation. Teachers can create exams, send notices, manage students, and add events to class calendars. Parents can monitor their children's progress.
Things to Consider When Choosing a Learning Management System
An LMS is made up of many components that enable different users to achieve their objectives. To make sure you're getting the best bang for your buck, your choice should be guided both by your budget and by the features of the LMS.
Automated Administrative and Communication Tools
Communication is key to any successful venture. Automating communication takes a load off administrators’ shoulders. Communication with teachers and students can include notifications about accounts and payments, email reminders, weekly course summaries, real-time onscreen progress indicators, and so on. Administrative tools include tools for registering teachers and calculating teachers' commissions.
Diverse Course Options
An LMS should combine different learning methods. For example, learning content can be delivered via audio, video, PowerPoint, multimedia, text, games, social learning, and more.
Course Content Creation Tools
An LMS comes with built-in authoring tools that allow for easy creation of course content.
Student Engagement and Collaboration
Online community tools—like chats and forums—integrated into the LMS offer opportunities for students to engage with their peers and collaborate on assignments.
Assessment and Testing Tools
A good LMS will let you test to see how students are learning and retaining material in the courses through quizzes and exams.
Instant Feedback
Teachers should be able to give learners feedback to show them where they need to improve.
Grading and Scoring
Your LMS should allow you to track student progress and performance over the duration of the course.
Certification
If you want to issue certificates, check that the LMS comes with the ability to create certificates for students who complete a course.
As a school administrator, you'll need access to data like the number of students taking a particular course, individual reports for each student, and how much time students spend on each lesson and quiz.
The only way to improve is through user feedback. That's why you might look for features for gathering feedback and suggestions from students to learn what they think about the quality of the courses and the system itself.
Many learning management systems offer students tools to review and rate their experience with courses. This will be helpful for others who want to take the course.
How to Create Engaging Online Courses
Maybe you want to share your expertise with the world through an online course, but you're wondering how you will create a course that draws in your students and keep them engaged to the end.
Here are a few tips to help you in this very exciting journey:
1. Use Different Media and Learning Strategies
Each lesson should use a mix of methods to deliver content:
- written explanations
Keep them short and sweet so students can easily understand the lesson. Don't bore them to death with facts and statistics.
2. Use Storytelling to Keep Learners Interested
Storytelling is still the most powerful way to teach and learn. Find bite-sized stories that can be the hook that draws your students in for each lesson, and figure out how to connect those stories to the course materials.
3. Encourage Collaboration
Create an environment where students engage with each other. Weekly discussion topics where every student chimes in and responds to other students can help promote sharing of knowledge and create bonds between students.
4. Get Feedback!
Ask students for honest feedback about your lessons so you can keep improving how you create and deliver them.
Benefits of Receiving Feedback
Feedback helps you gauge how effective your online courses are, if they are going in the right direction and if learners are deriving benefits from them. It gives you valuable data that you can use to redesign and improve your courses and make learning more engaging for those who take them.
Asking for feedback shows you are invested in your courses and care about them enough to ask learners for their honest opinion.
The best time to ask for feedback is not at the end of the course. It pays to seek feedback continuously during the duration of the course when it is fresh on the minds of your students. This opens up honest communication that will allow you to see what is working and what is not.
Effective Ways of Getting Meaningful Feedback
Do your learners need more resources, guidance, or clarification? The right kind of feedback contains specific information that will help you improve your courses.
How do you ask for, and get, the right kind of feedback?
1. Identify Specific Areas Where You Need to Improve
When you create a course, some topics and themes will be easy to create material for. Others will be difficult, and you will struggle with whether the learners will have a hard time understanding them. Breaking down different aspects of your courses allows you to see areas that need improvement.
2. Avoid Generic Questions, Ask Super Specific Questions
Asking specific questions allows you to make targeted improvements. Questions like "How did you like the course?" waste your time and the learner's time. Seek feedback on what was clearly expressed and what they found lacking. For example, was a particular section too heavy on text, were interactive materials enough, or were they distracting? What did they learn from the course, and will it help them?
3. Use the Right Tools for Gathering Feedback
Surveys ask very specific questions which allow you to get very specific feedback. You can add them anywhere on your course. You can do surveys at particular stages of the course. It could be at the beginning, middle, or end of the course.
Email lets you stay in touch with learners through regular course emails. It makes sense that you should ask them to send you feedback by email, which allows them to elaborate their opinions on what is working or what can be improved in ways that a survey does not capture.
The Best PHP Scripts on CodeCanyon
The free libraries are wonderful for basic functionality, but for more specialized features or for complete applications that you can use and customize, take a look at the professional PHP scripts on CodeCanyon.
Explore thousands of the best and most useful PHP scripts ever created on CodeCanyon .

Here are a few of the best-selling and up-and-coming PHP scripts available on CodeCanyon for 2022.


Online Examination System in PHP MySQL Free Source Code

Table of Contents
Revolutionizing Education: Online Examination System in PHP MySQL Free Source Code Download
In the digital age, traditional methods of conducting examinations are rapidly evolving to keep pace with technological advancements. One such groundbreaking innovation is the Online Examination System, a paradigm shift in the assessment landscape. This system transcends geographical barriers, enabling participants to undertake assessments remotely, at their convenience, and utilizing their preferred devices. With just a web browser and an internet connection, the Online Examination System empowers learners to demonstrate their knowledge and skills effortlessly.
About this Online Examination System in PHP MySQL Project
Online Examination System is directing a test online to quantify the information on the members on a given theme. In the times past, everyone needed to accumulate in a study hall simultaneously to take a test. With online assessment understudies can do the test on the web, time permitting, with their own gadget, paying little heed to where they live. You just need a program and a web association. This additionally makes c checking the appropriate response simple and blunder evidence as PCs are more exact than man and give quick outcomes as well. PHP is an electronic language so we can make an online assessment framework in PHP .
Embracing Convenience and Accessibility
Gone are the days when candidates had to assemble in a physical classroom to undertake exams. The Online Examination System liberates learners from the constraints of time and location, offering unparalleled flexibility. Whether a student resides in a bustling metropolis or a remote village, they can seamlessly access the examination platform from the comfort of their surroundings. This democratization of education ensures inclusivity and equal opportunity for all.
Unveiling the Features
Client-side functions, registration.
The system facilitates seamless registration for participants, streamlining the onboarding process and ensuring a hassle-free experience.
Participants can embark on their examination journey with ease, navigating through the intuitive interface to access their assessments promptly.
View History
A comprehensive record of past examinations allows learners to track their progress and identify areas for improvement, fostering a culture of continuous growth.
View Ranking
Transparency reigns supreme as participants can gauge their performance relative to their peers, motivating them to strive for excellence.
Submit Feedback
Feedback is the cornerstone of improvement. Participants can articulate their suggestions and insights, contributing to the refinement of the examination process.
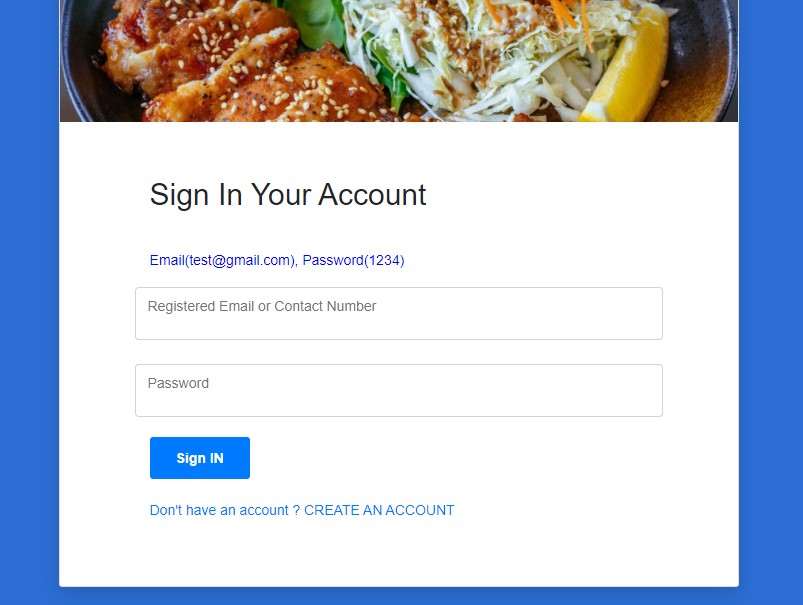
Sign-in/Sign-out
Seamless authentication mechanisms facilitate secure access to the platform, safeguarding the integrity of the examination ecosystem.
Admin-Side Functions
User management.
Administrators wield robust tools to manage user accounts efficiently, ensuring optimal utilization of resources.
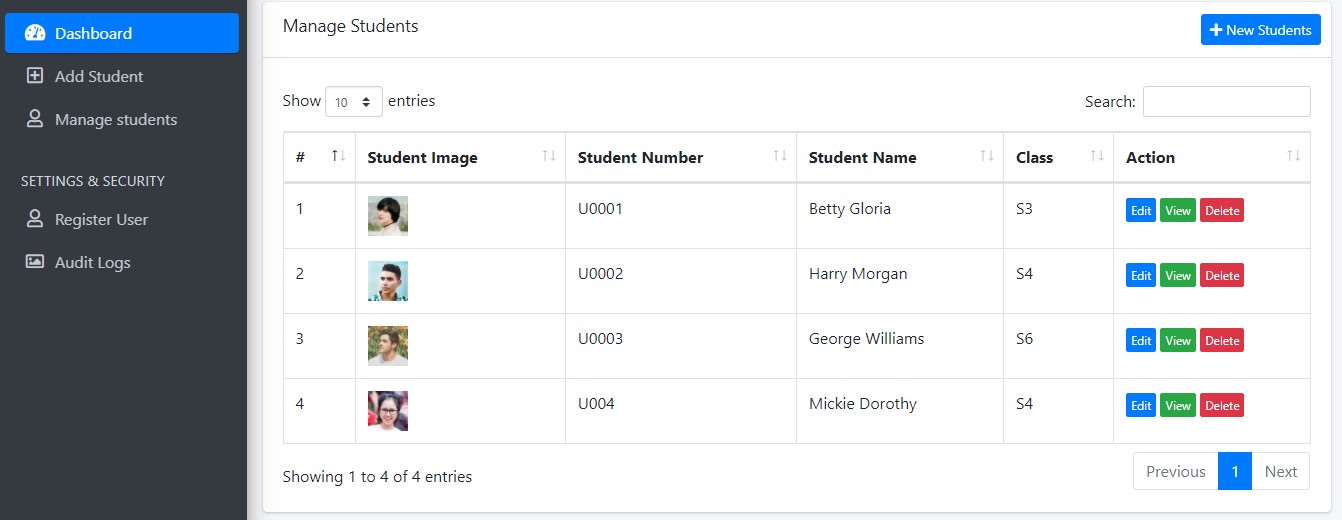
CRUD – Students
The system empowers administrators to perform Create, Read, Update, and Delete operations seamlessly, enhancing administrative efficacy.
Create and Remove Examination
Flexibility is paramount. Administrators can effortlessly create and remove examinations, adapting to evolving educational requirements.
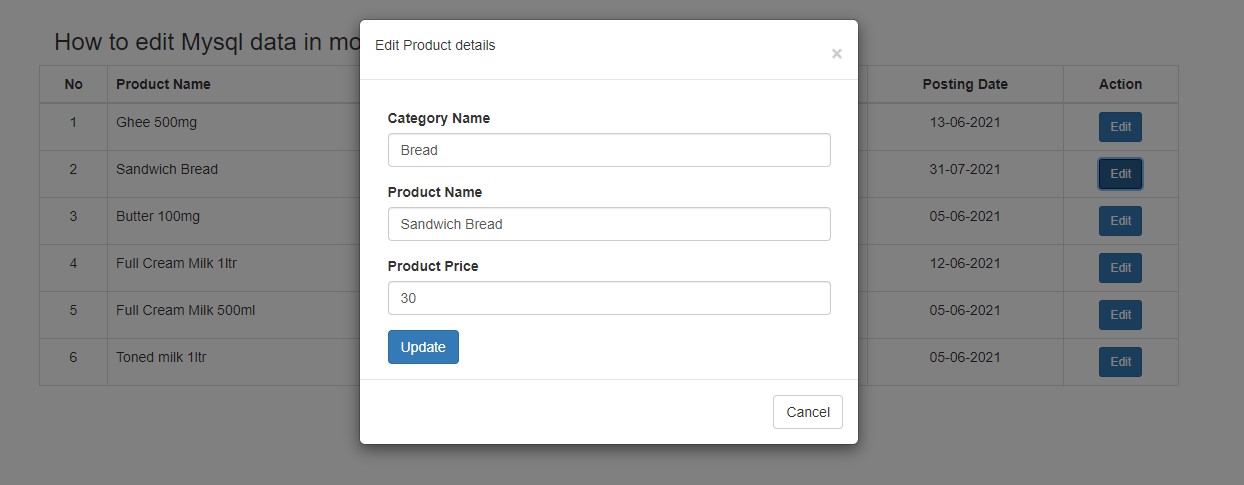
View and Change Examination
Real-time visibility into ongoing examinations enables administrators to monitor proceedings closely and intervene if necessary, ensuring smooth operations.
View History and Rankings
Administrators gain insights into historical data and rankings, enabling informed decision-making and strategic planning.
View Feedback
The voice of the participants matters. Administrators have access to valuable feedback, facilitating iterative improvements and optimization.

online examination system in php mysql ER Diagram
Elevating the Learning Experience: A Video Demo
To provide a visual walkthrough of the Online Examination System’s functionality and user interface, we have prepared a comprehensive video demo. Please refer to the following link to embark on an immersive journey:
Please refer to the video demo below on how to run this project.
The Online Examination System heralds a new era of educational assessment, characterized by convenience, accessibility, and efficiency. By harnessing the power of technology, this system empowers learners and administrators alike, fostering a culture of excellence and continuous improvement. Embrace the future of education with the Online Examination System, where boundaries dissolve, and knowledge knows no limits.
Related Projects: Complete Online Examination System in PHP and MySQL , Advanced Online Examination System Project in PHP MySQL , Online Examination System in PHP/MySQLi , Complete Laravel Admin Dashboard Panel CMS with Frontend and Restful API , Agricultural Reviewer System using PHP/MySQL , Online Reviewer System Using PHP/MySQL , Advanced School Management System with Complete Features , Simple Online Quiz System Project using PHP MySQL
Free Download Online Examination System in PHP MySQL Project Source Code
- Related Articles

Web Based Student Portal in PHP MySQL Free Download

Online Student Grading System in PHP MySQL

Gatepass Management System in PHP MySQL Free Download

Complete Blood Bank Management System in PHP MySQL Free Download
hi checked for lot of codes password is not working if you changed pls let us know what is the password or how to change it , thanks
Please send me the admin ID for me to unlock the system
Please what is the admin password,i can not lock on to the system
what algorithm is used in this project?
Hi Adnin, where the hell the source code you promised can be found? There is no link to download. Or do you cheat us on purpose? That is the reason, why no one left a comment here.
Kindly click the Pink Color Button with a Label “Download Here”. This is working in my end.
I download but there is no code inside
Sir please make a complete system for student online registration system php.
Sir can you send please school management system php
Okay, that will be my next php project to be posted soon
bro what is the admin password and user id??
Leave a Reply Cancel reply
Your email address will not be published. Required fields are marked *
Save my name, email, and website in this browser for the next time I comment.

Don't be Afraid of Source Code
PHP Projects Free Downloads
Core php projects list, free projects list.
| # | PHP Project Name |
|---|---|
| 1 | |
| 2 | |
| 3 | |
| 4 | |
| 5 | |
| 6 | |
| 7 | |
| 8 | |
| 9 | |
| 10 | |
| 11 | |
| 12 | |
| 13 | |
| 14 | |
| 15 | |
| 16 | |
| 17 | |
| 18 | |
| 19 | |
| 20 | |
| 21 | |
| 22 | |
| 23 | |
| 24 | |
| 25 | |
| 26 | |
| 27 | |
| 28 | |
| 29 | |
| 30 | |
| 31 | |
| 32 | |
| 33 | |
| 34 | |
| 35 | |
| 36 | |
| 37 | |
| 38 | 39 |
| 40 | |
| 41 | |
| 42 | |
| 43 | |
| 44 | |
| 45 | |
| 46 | |
| 47 | |
| 48 | |
| 49 | |
| 50 | |
| 51 | |
| 52 | |
| 53 | |
| 54 | |
| 55 | |
| 56 | |
| 57 | |
| 58 | |
| 59 | |
| 60 | |
| 61 | |
| 62 |

CodeIgniter Projects List
| # | Project Name |
|---|---|
| 1. | |
| 2. | |
| 3 | |
| 4 | |
| 5. | |
| 6. |
Python Projects
| # | Project Name |
|---|---|
| 1. | |
| 2. | |
| 3. | |
| 4. | |
| 5. | |
| 6. | |
| 7. | |
| 8. | |
| 9. | |
| 10. | |
| 11. | |
| 12. | |
| 13. | |
| 14. |
Premium / Paid Projects List
| # | PHP Project Name | Cost |
|---|---|---|
| 1 | Rs.699 / $9.90 | |
| 2 | Rs.499 / $7 | |
| 3 | Rs.499 / $7 | |
| 4 | Rs.549 / $7.77 | |
| 5 | Rs.599 / $7.20 | |
| 6 | Rs.799 / $9.61 | |
| 7 | Rs.999 / $12.19 | |
| 8 | Rs.399 / $5.65 | |
| 9 | Rs.699 / $9.90 | |
| 10 | Rs.699 / $8.5 | |
| 11 | Rs.449 / $6.36 | |
| 12 | Rs.649 / $9.40 | |
| 13 | Rs.599 / $7.21 | |
| 14 | Rs.549 / $7.77 | |
| 15 | Rs.799 / $11.31 | |
| 16 | Rs.699 / $9.90 | |
| 17 | Rs.649 / $9.19 | |
| 18 | Rs.299 / $4.23 | |
| 19 | Rs.549 / $7.77 | |
| 20 | Rs.699 / $9.90 | |
| 21 | Rs.349 / $4.94 | |
| 22 | Rs.499 / $6.54 | |
| 23 | Rs.499 / $6.54 | |
| 24 | Rs.599/ $7.87 | |
| 25 | Rs.449/ $5.91 | |
| 26 | Rs.399/ $5.28 | |
| 27 | Rs.799/ $10.58 | |
| 28 | Rs.599/ $7.87 | |
| 29 | Rs.499/ $6.61 | |
| 30 | Rs.499/ $6.61 | |
| 31 | Rs.429/ $5.69 | |
| 32 | Rs.299/ $3.76 | |
| 33 | Rs.549/ $7.49 | |
| 34 | Rs.649/ $8.82 | |
| 35 | Rs.499/ $6.80 | |
| 36 | Rs.499/ $6.80 | |
| 37 | Rs.349/ $4.70 | |
| 38 | Rs.449/ $6.02 | |
| 39 | Rs.499/ $6.69 | |
| 40 | Rs.499/ $6.69 | |
| 41 | Rs.499/ $6.69 | |
| 42 | Rs.299/ $4.05 | |
| 43 | Rs.499/ $6.7 | |
| 44 | Rs.449/ $6.0 | |
| 45 | Rs.449/ $6.0 | |
| 46 | Rs.499/ $6.65 | |
| 47 | Rs.349/ $4.625 | |
| 48 | Rs.499/ $6.68 | |
| 49 | Rs.599/ $8 | |
| 50 | Rs.599/ $8 | |
| 51 | Rs.399/ $5.31 | |
| 52 | Rs.499/ $6.69 | |
| 53 | Rs.599/ $7.73 | |
| 54 | Rs.799/ $9.61 | |
| 55 | Rs.519/ $6.81 | |
| 56 | Rs.449/ $5.92 | |
| 57 | Rs.549/ $7.23 | |
| 58 | Rs.399/ $5.11 | |
| 59 | Rs.599/ $7.56 | |
| 60 | Rs.549/ $6.93 | |
| 61 | Rs.549/ $6.88 | |
| 62 | Rs.649/ $8.15 | |
| 63 | Rs.599/ $7.27 | |
| 64 | Rs.599/ $7.27 | |
| 65 | Rs.499/ $6.11 | |
| 65 | Rs.349/ $4.22 | |
| 66 | Rs.499/ $6.11 | |
| 67 | Rs.599/ $7.36 | |
| 68 | Rs.549/ $6.63 | |
| 69 | Rs.799/ $9.22 | |
| 70 | Rs.799/ $9.22 | |
| 71 | Rs.449/ $5.5 | |
| 72 | Rs.899/ $10.80 | |
| 73 | Rs.799/ $9.61 | |
| 74 | Rs.799/ $9.61 | |
| 75 | Rs.649/ $7.81 | |
| 76 | Rs.599/ $7.22 | |
| 77 | Rs.499/ $6 | |
| 78 | Rs.549/ $6.5 | |
| 79 | Rs.549/ $6.5 | |
| 80 | Rs.499/ $6.0 | |
| 81 | Rs.699/ $8.42 | |
| 82 | Rs.649/ $7.82 | |
| 83 | Rs.799/ $9.6 | |
| 84 | Rs.499/ $6.0 |
PHP (Pre-Processor Hypertext) is a server-side scripting language, which is considered best for developing the dynamic web pages. At PHPGurukul students can easily download the FREE PHP projects on varied topics according to their requirements. This list of projects in PHP with source code aims to enhance the user’s skills with the dynamic and attractive web application. These PHP projects are well designed for users to understand the PHP concept during the execution of any web development. And it could also be helpful for students or beginners to gain the primary ideas before starting any project. PHP programming is a crucial part of the Web development mechanism, so make it simpler and easier with PHP free projects download at PHPGurukul.
With time we would introduce PHP Projects Ideas & new PHP projects List related to PHP that you can easily download them.
PHP projects are one of the major asks these days either in college, high school, or training institutes and even offices. PHP is a preferable option for a web development project due to its flexible and dynamic nature. And if you get built PHP Projects Free , it is easy to customize and modify according to your requirements.
Our website offers you built PHP Projects with source code to help you learn as a student and an employee. Even as an employer, if you are running short out of time and not getting any PHP developer, you can use our website for PHP Free Projects Download and save your time and money.
Below are the major benefits of our PHP Projects Free Downloads :
- Cost-effective way of web development.
- Easy learning with actual source code.
- Practical knowledge is always better than theoretical tutorials.
- Quick customizations are available.
- Free PHP Projects with source code contains functions and procedures that are reusable.
Our website offers PHP Projects for students with basic as well as advanced projects. As an additional benefit, the project report is also included when you download a PHP project. These project reports can be purchased at a minimal price. When you submit your assessment for PHP, it would be really helpful and save a lot of your time and efforts. You can always customize these PHP projects as per your need.
PHP Projects Free Downloads include around 36 Free PHP projects, 3 Projects built using CodeIgniter, and 76 Paid PHP projects. These projects are very obliging to enhance your skills with attractive web applications, and each Project is well designed for effective and interactive usage.
The PHP projects are categorized into versatile topics that attract attention and also include simple and common PHP projects for your references. For beginners, projects like Online Library management and hospital management are included. For advanced web developers and professionals’ projects like Inventory management, Online Catering Curfew e-Pass Management, Teachers Record management are included.
Welcome to PHPGurukul .
How can I help you?
🟢 Online | Privacy policy
Free PHP Projects with Source Code
Free PHP Projects with Source Code. Download latest editors' pick PHP projects with source code for free here. We select the best source code uploaded here and hand pick it for you.
Best house rental management system project in php

- Read more about Best house rental management system project in php
- Add new comment
Prison Management System Using PHP
- Read more about Prison Management System Using PHP
Advocate office management system free download

- Read more about Advocate office management system free download
Computer Laboratory Management System using PHP and MySQL

- Read more about Computer Laboratory Management System using PHP and MySQL
php task management system free download

- Read more about php task management system free download
- 11653 views
Insurance Management System PHP and MySQL

- Read more about Insurance Management System PHP and MySQL
- 11 comments
- 11081 views
Employee Management System using PHP and MySQL

- Read more about Employee Management System using PHP and MySQL
- 21842 views
Simple Image Stack Website using PHP and API

- Read more about Simple Image Stack Website using PHP and API
Simple Student Attendance System using PHP and MySQL
- Read more about Simple Student Attendance System using PHP and MySQL
- 14011 views
Best courier management system project in php

- Read more about Best courier management system project in php
- 17568 views
Navigation Menu
Search code, repositories, users, issues, pull requests..., provide feedback.
We read every piece of feedback, and take your input very seriously.
Saved searches
Use saved searches to filter your results more quickly.
To see all available qualifiers, see our documentation .

Empowering the next generation of developers
GitHub Education bridges the gap between coding education and a tech career, and is accessible to everyone globally at no cost.
More than a platform. GitHub Education is a commitment to bringing tech and open source collaboration to students and educators across the globe.
5 million students.
Connect with millions of peers who've expanded their skills through GitHub Education.
200K verified educators
Collaborate with educators around the world who enhance their lesson plans and workstreams with GitHub tools.
+2K educational institutions
Join thousands of schools globally that incorporate GitHub into their tech curriculum.
Join a community where learning meets doing, with free access to the same tools professional developers use, including GitHub Copilot and Codespaces.

Connect with a community of peers, expand your teaching methods, and leverage GitHub Classroom to track and manage assignments, automate grading, and empower students to dream big.
Enhance your technical and academic departments with real-world software solutions, thanks to free access to GitHub Enterprise.

Expand your brand's footprint in the tech landscape and ensure the tech leaders of tomorrow know your tools by name by partnering with GitHub Education.
We've partnered with GitHub Education to ensure students receive a robust education in computer science and practical skills, equipping them for success in any field.

GitHub Education is a fantastic opportunity for students to build solid communities. The program offers awesome tools like the GitHub Student Developer Pack and helps shape great leaders with the Campus Experts Program. If you make the most of these resources, you’re in for some amazing opportunities!

Begin your GitHub Education journey
Join us today and take the first step towards transforming your tech education experience.
About GitHub Classroom
Teachers and school administrators can use GitHub Classroom to create virtual classrooms, make and edit assignments, automatically grade assignment submissions, and more.
Community Discussions
Have questions or need help? Join in on the conversation and meet fellow students and teachers all learning together with GitHub.
GitHub Skills
Learn how to use GitHub with interactive courses designed for beginners and experts.
Frequently Asked Questions
What is github education.
GitHub Education is a community dedicated to empowering the next generation of developers through the power of open-source education. Whether you're a student eager to make your mark, an educator aiming to inspire, or an early career developer looking to sharpen your skills, GitHub Education is here to help you succeed.
Why Join GitHub Education?
Free access to tools : Jump-start your development journey with the GitHub Student Developer Pack, offering dozens of premium tools and services at no cost. From GitHub Copilot’s AI-powered coding assistance to GitHub Codespaces, which provide a fully configured cloud development environment, these tools are used daily by professional developers globally. They’d normally cost a fortune, but are available for free to verified students.
Real-world experience : Engage in open source projects and collaborative development to gain practical experience and build a portfolio of contributions. This hands-on approach prepares you for a successful career in tech, offering real-world application and visibility.
Exclusive learning content : Explore our Learning Paths to find structured educational content designed to guide your learning. These paths provide a clear progression through different tech topics, helping you enhance your knowledge and skills at your own pace.
Global network : Connect campus advisors and experts, and attend special events and live streams. Each connection will expand your horizon and open doors to new growth opportunities.
Sign up for free and take the first step toward becoming a leader in technology and innovation.
How do I join the GitHub Education?
As a student : If you're currently enrolled at an accredited educational institution, you can apply to become part of GitHub Education. You'll need to provide a school-issued email address or other documents proving your enrollment. Apply through the GitHub Education website, select 'Student', and follow the instructions to submit your information.
As a teacher : Educators can join by verifying their teacher status with a school-issued email and documentation of school affiliation. Head over to the GitHub Education site, choose 'Teacher' under the benefits section, and submit your application.
As a school : To get your school on board with the free GitHub Education program for schools, you need to be an educational institution offering degrees or certificates. The application should be completed by someone in charge of IT or a department head. Apply through the GitHub Education website, select 'Schools', and follow the instructions to submit your information.
As a partner : To begin a collaboration with GitHub Education, visit our partners page to learn more about the details and types of partnership we aim for, then, complete our partnerships form for our team to reach out and discuss the next steps.

Download 30 Best Free PHP Projects with Source Code
By john smith . last updated on april 1st, 2022..

What this means is that if you try to run the PHP code in a web browser, it results in the web browser printing the entire code. You need a server to execute PHP projects or scripts. We’ll come to this part later in the article.
In the event that you are hoping to dominate PHP prior to making your first venture, udemy course PHP for Beginners (with CMS Project) will be truly useful.
PHP is a prearranging language that powers the vast majority of the sites today. PHP projects, in this manner, allude to sites, web applications, applications, anything, and all that is created by utilizing PHP. Along these lines, how about we start the conversation with things that go into a PHP project.
What Makes Up a PHP Project?
1. php development environment/language release.
Nonetheless, there are a few certain viewpoints, as PHP 7 does not offer help for MySQL augmentation, that one ought to note down while making the pick between the two PHP discharges.
2. Development Tools; Editors, IDEs, and Frameworks
PHP projects require PHP scripts. You can easily create a PHP script using Notepad sublime text.
- Simply create a new file using the popular text editor,
- Write down the PHP code, and
- Save using a .php extension.
It is the most favored way while simply branching out to learn PHP, without rehashing an already solved problem. The equivalent, in any case, is a wasteful way while chipping away at an undeniable venture or in any event, while learning progressed ideas that require writing down Brobdingnagian extents of code.
- Komodo Edit
- Sublime Text 3
- Visual Studio Code
- Rapid PHP editor
- Zend Studio
Dissimilar to IDEs and code editors, systems are an assemblage of libraries and modules that offer a conventional construction of program (for a site or a web application) advancement. Here is an article that plunges further into probably the best PHP systems for web advancement.
3. Web Server
Where to get php projects code, download 10 best free php projects with source code, 1. church management system in php.
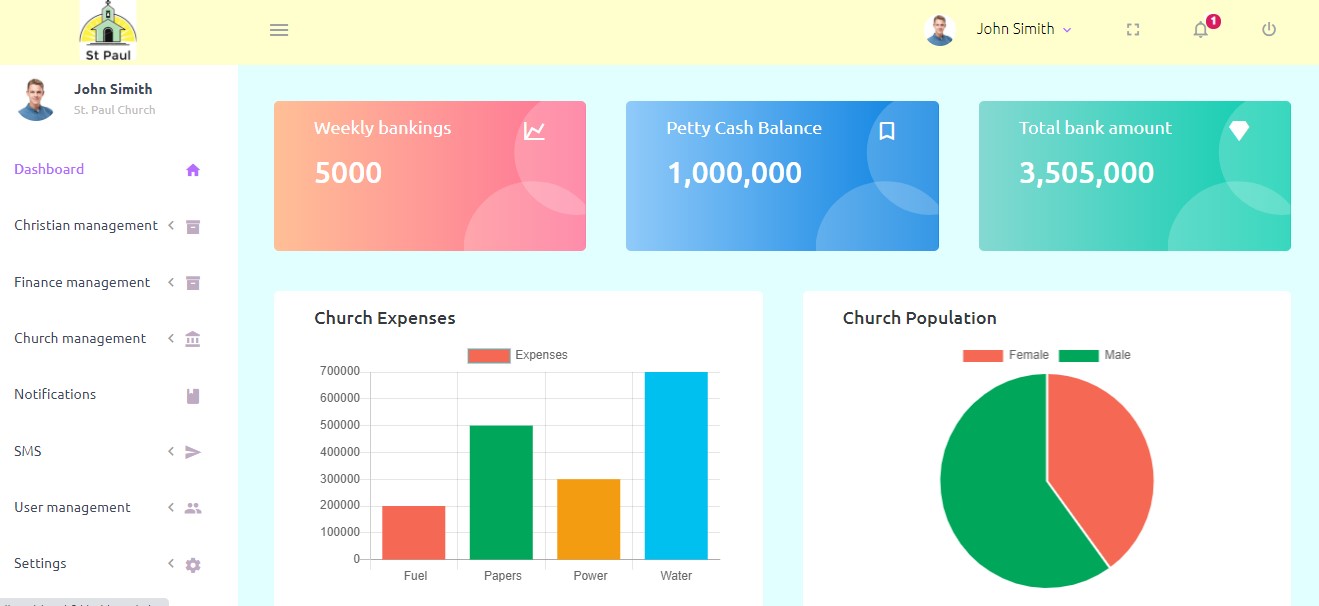
Church is commonly defined as abuilding used for public worship.however, many people refere to church as an organisation. Examples are the Catholic Church, the Church of England, and the Southern Baptism Church amongst many others.
Church management system is online system which controls all operations and activities that take place in church, it has many features like chritian management, christian attendance with thier templature records, store management, finance and many others. The system analyse data and display it in graph format and cards to the admins on dashboard page.
2. Online Grocery shop in php and mysql with source code
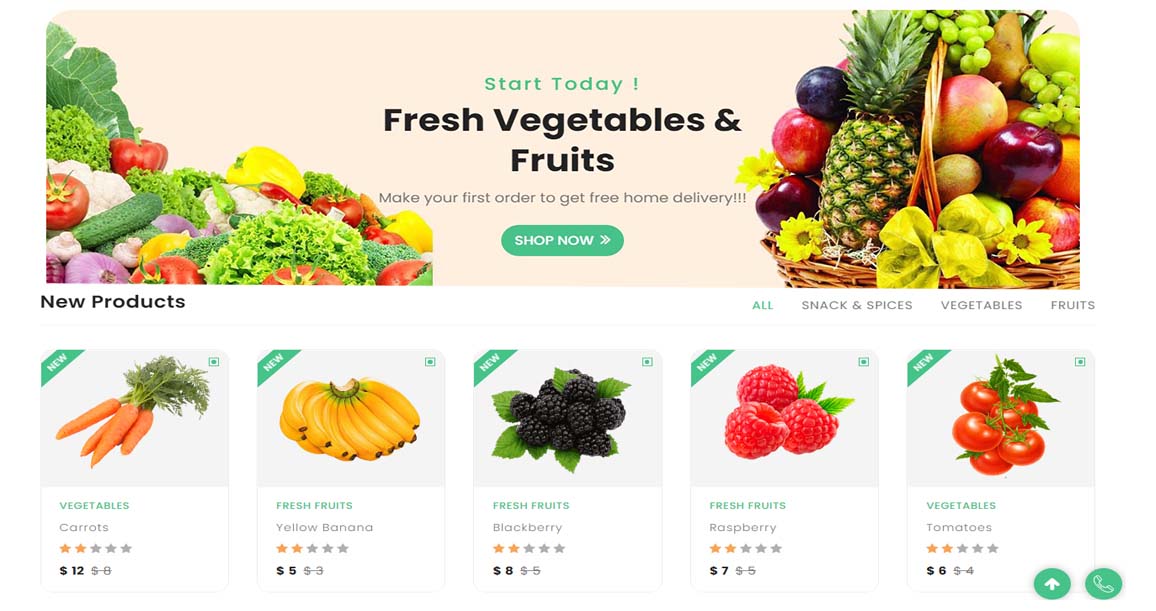
The grocery management system is a PHP and SQL-based online application. It allows you to manage your grocery store, customer information, and assist in the online sale of your groceries. This project will help grocery store to keep truck of their business, To know products sold, amount generated and automatic invoice generation.
The grocery management system is developed in PHP and Mysql to help traders to sell their products online. products like fresh vegetables, organic, fresh fruits, fruit juice, fresh food and many others can be bought online without accessing the physical shop.
3. Online Furniture shop in php and mysql with source code
Online Furniture Shop Management System using PHP and MySQL is web based application which help people to buy and sell furniture online without visiting physical shop. The main aim of this project of Online Furniture Shop Project in PHP is to manage truck the sales, automatic invoice generation to customer after purchase, to know furniture sold, Order etc.
4. Online Electronics shop in php and mysql with source code
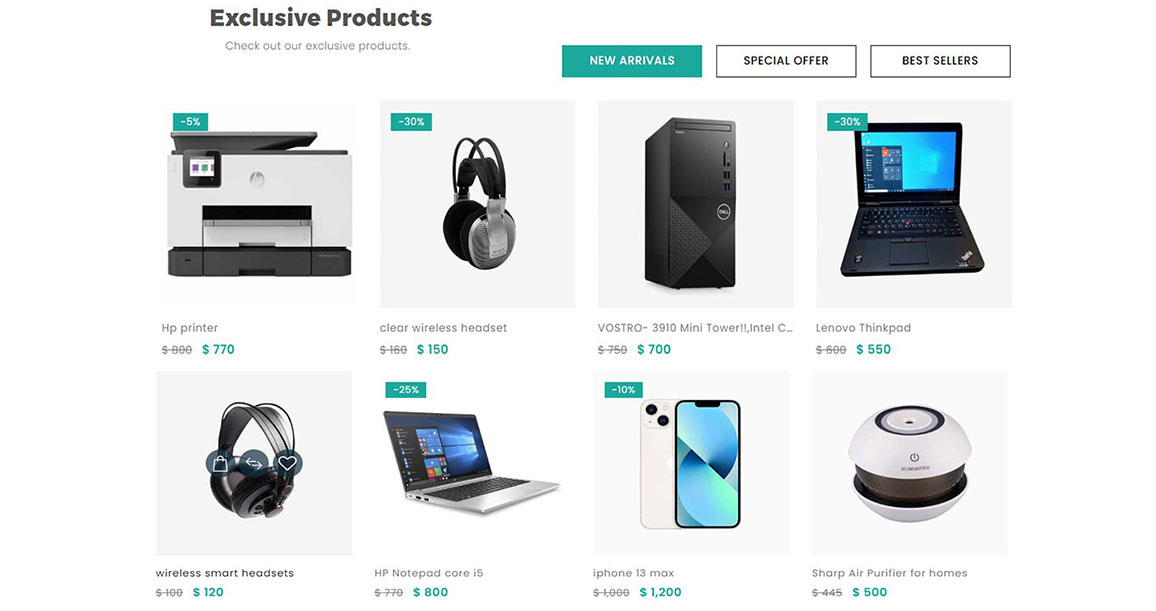
Electronic Shop Management System using PHP and MySQL is web based application which help people to buy and sell electronics online without visiting physical shop. The main aim of this project of Online Electronic Shop Project in PHP is to manage truck the sales, automatic invoice generation to customer after purchase, to know electronics purchased, amount collected etc.
5. Beauty Salon management system
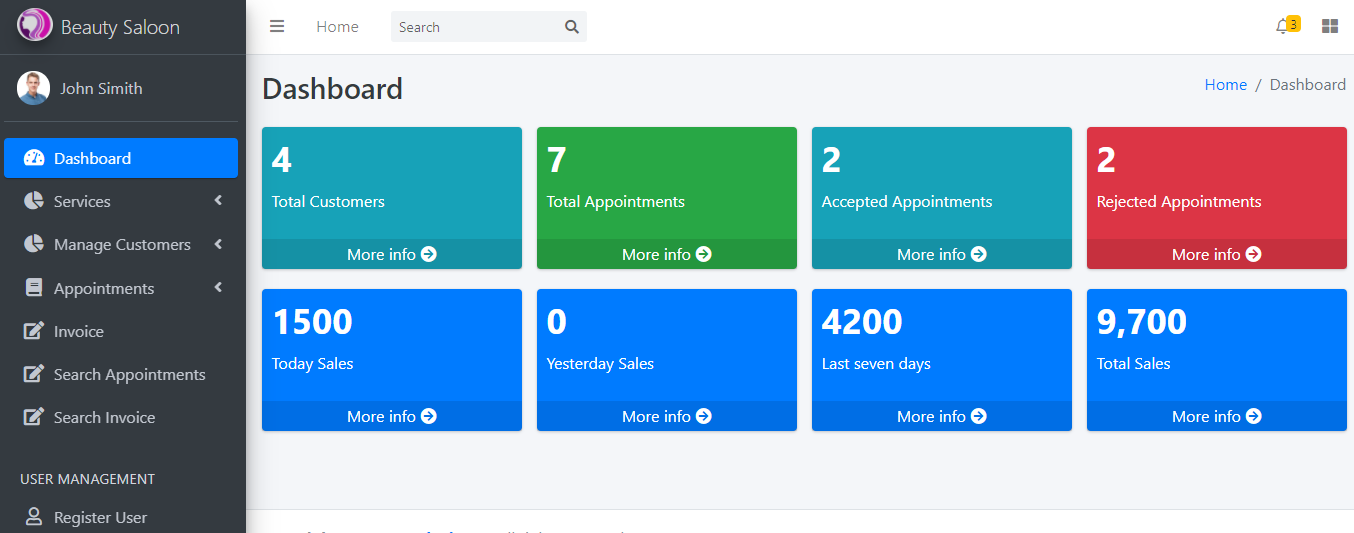
A beauty salon is an establishment dealing with cosmetic treatments for men and women.
A place where your hair, face, and body can be given special treatments to improve their appearance.
This is online system which help customers to submit their appointments(date and time), it help to overcome problem of time wastage for customers waiting to be worked on. Admin get notification of new appontment and take action immediately, other useful features like customer and service management, invoices, report generation are also included in system.
6. Zoo management system in php
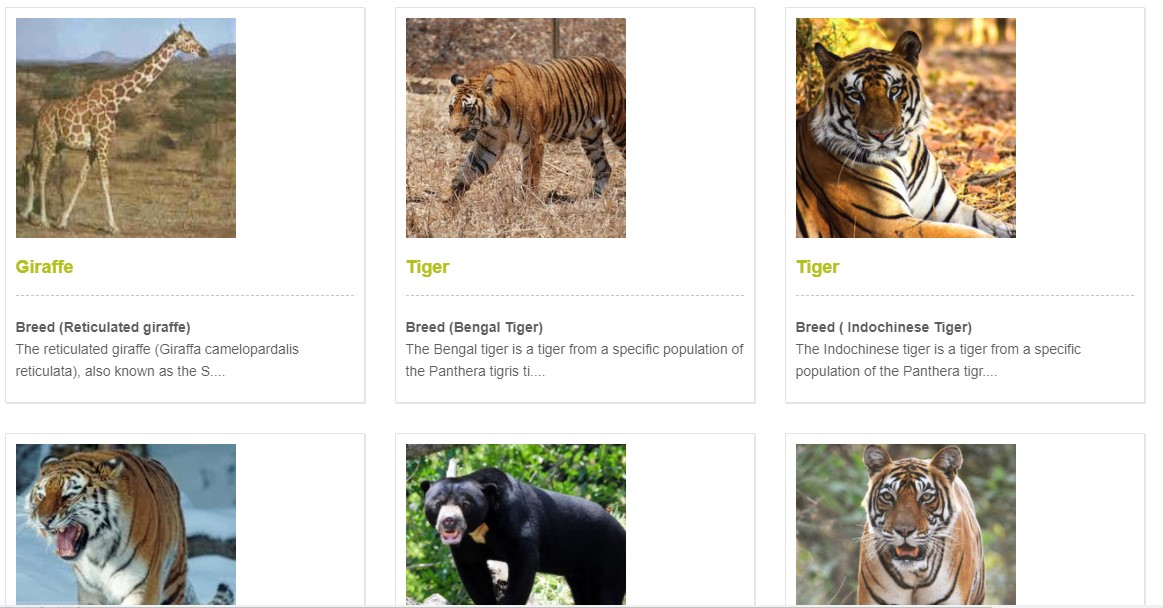
A park or an institution in which living animals are kept and usually exhibited to the public. Also called zoological garden.
Zoo management system is a computerised system which help tourist to see animal kept in that specific zoo before visiting, Also it help admin to prepare tourist tickets both young and old, citizens and foreigners. It has strong features which help to do the operations faster.
7. Poultry farm management system
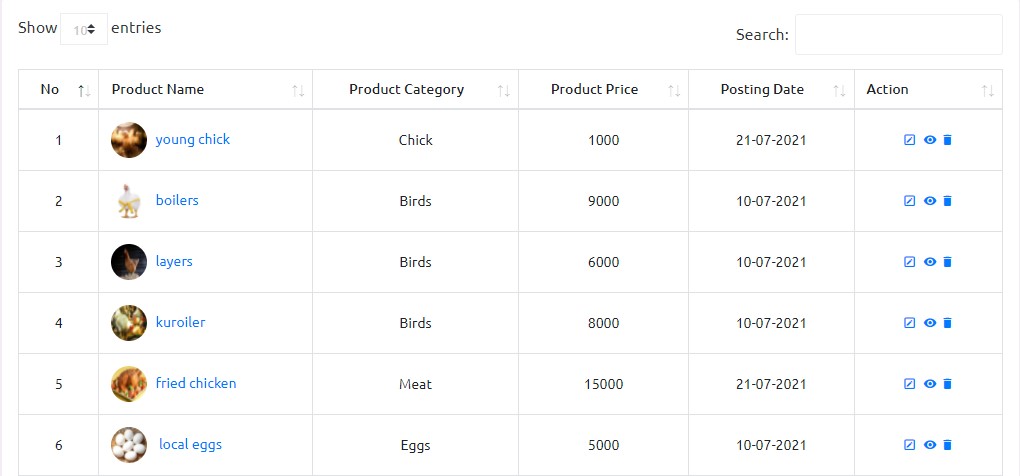
Poultry - mostly chickens - are farmed in great numbers. Farmers raise more than 50 billion chickens annually as a source of food, both for their meat and for their eggs. Chickens raised for eggs are usually called layers while chickens raised for meat are often called broilers.
Poultry farm management system is online system which help farmers to manage all activities carried out which include chicken population, store management,sells, invoices and many others. Farm managers and owners can truck and see what is taking place without visiting farm.
8. Car rental management system in php
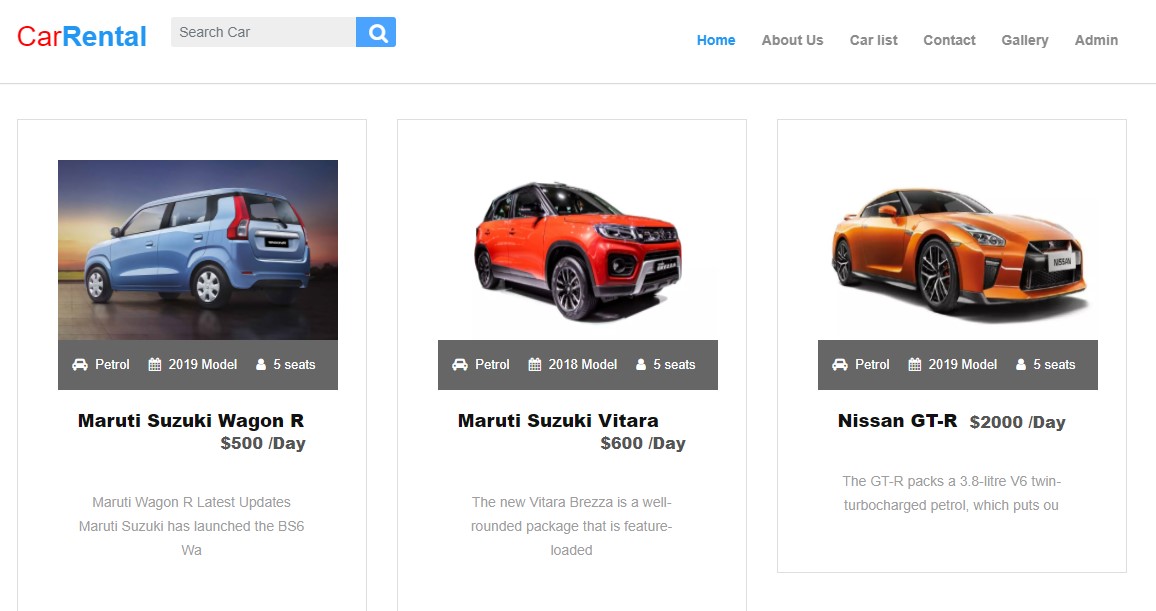
A car rental, hire car or car hire agency is a company that rents automobiles for short periods of time for a fee. It is often organized with numerous local branches, and primarily located near airports or busy city areas and often complemented by a website allowing online reservations. Car rental agencies primarily serve people who have a car that is temporarily out of reach or out of service, for example travelers who are out of town or owners of damaged or destroyed vehicles who are awaiting repair or insurance compensation. Because of the variety of sizes of their vehicles, car rental agencies may also serve the self-moving industry needs, by renting vans or trucks, and in certain markets other types of vehicles such as motorcycles or scooters may also be offered. Alongside the basic rental of a vehicle, car rental agencies typically also offer extra products such as insurance, global positioning system navigation systems, entertainment systems, and even such things as mobile phones.
Car rental system is online booking system which help customers to book a vehicle without visiting bond and it has feature for customers to truck their bookings, profile updates, changing password and many others. Managers and administrators have thier panel where they control and truck what ever is taking plae in car bond.
9. Student details management system
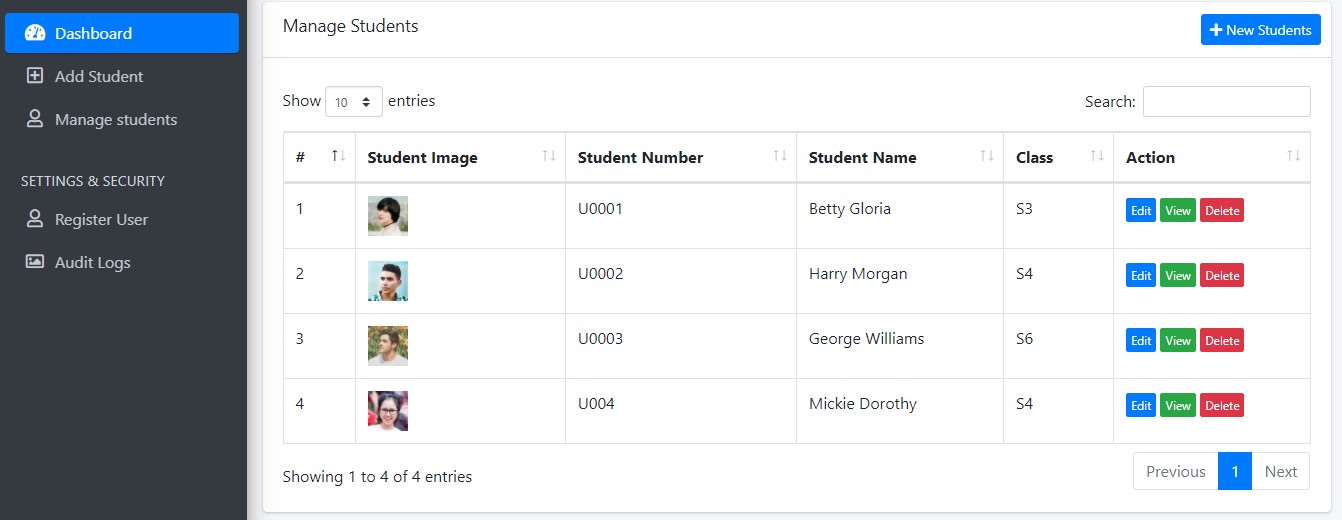
Student Details Management allows you manage all the academic, personal, family, previous school details along with his/her passport size photo. You can also register and update student from the student details management section.
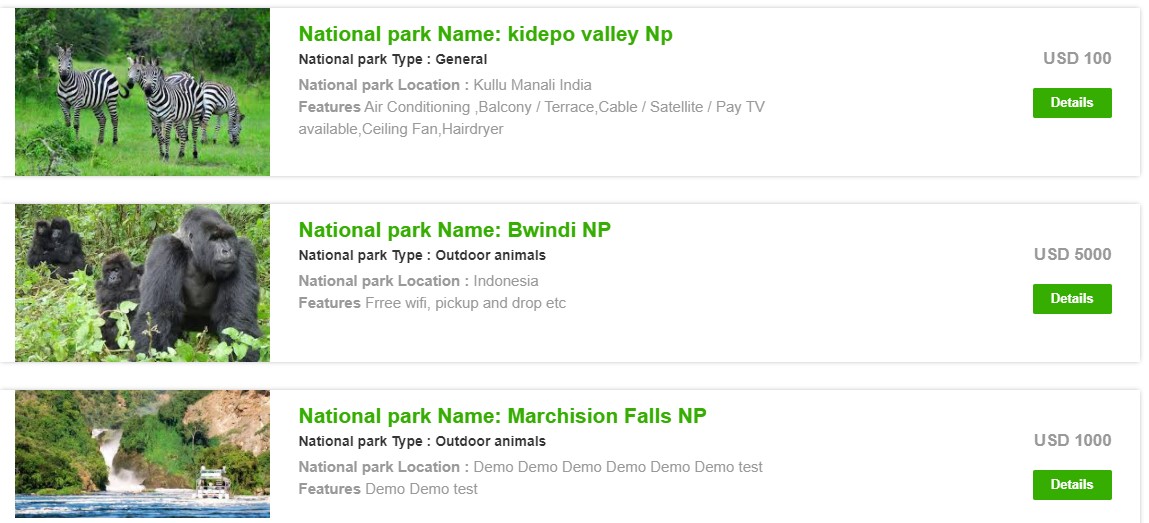
10. Tourism management system
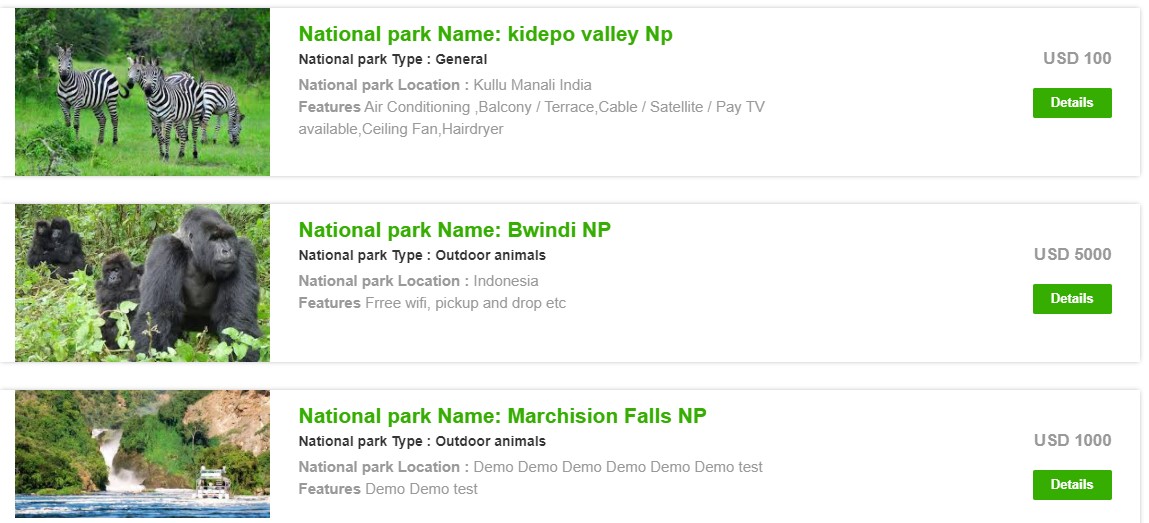
Tourism, the act and process of spending time away from home in pursuit of recreation, relaxation, and pleasure, while making use of the commercial provision of services. As such, tourism is a product of modern social arrangements, beginning in western Europe in the 17th century, although it has antecedents in Classical antiquity.
Tourism management system is online system which help tourists to access available tour packages and book without accessing offices and they have features of tracking and controlling their bookings, accessing tour history, password and profile update. Admin has thier panel where they control the system and see people who are ready to go, also they have many feature like package management and many others.
11. Decoration management system
Something used to decorate, especially when put up temporarily to celebrate or call attention to a special occasion.
Decoration management system is online system which helps customer to book online without accessing offices, Admin has their panel with beautiful features which help them to control and manage bookings.
12. Hostel booking management system in php
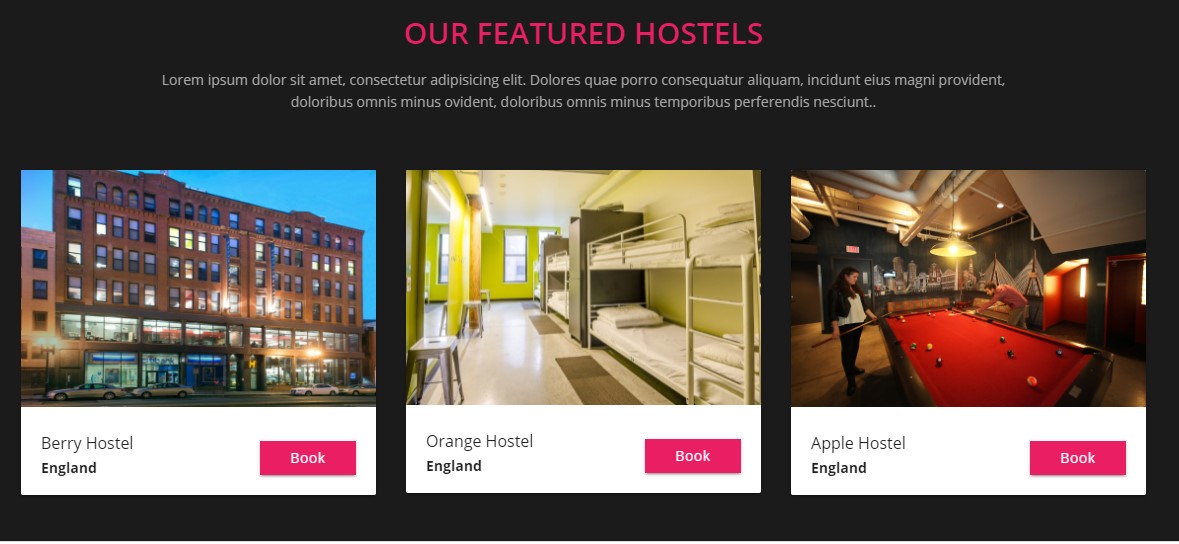
Hostels are defined as a second home for the ones who reside in the same. Hostels are the place where the students live, spend time with their friends, study and do all their chores after school hours.
A hostel is a form of low-cost, short-term shared sociable lodging where guests can rent a bed, usually a bunk bed in a dormitory, with shared use of a lounge and sometimes a kitchen. Rooms can be mixed or single-sex and have private or shared bathrooms. Private rooms may also be available, but the property must offer dormitories to be considered a hostel.
This system helps student to book hostel online without visisting the school. The school administrators get to know new booking and information about those students like name, address, booked months, course, with or without food and many others.
13. Company Visitors management system
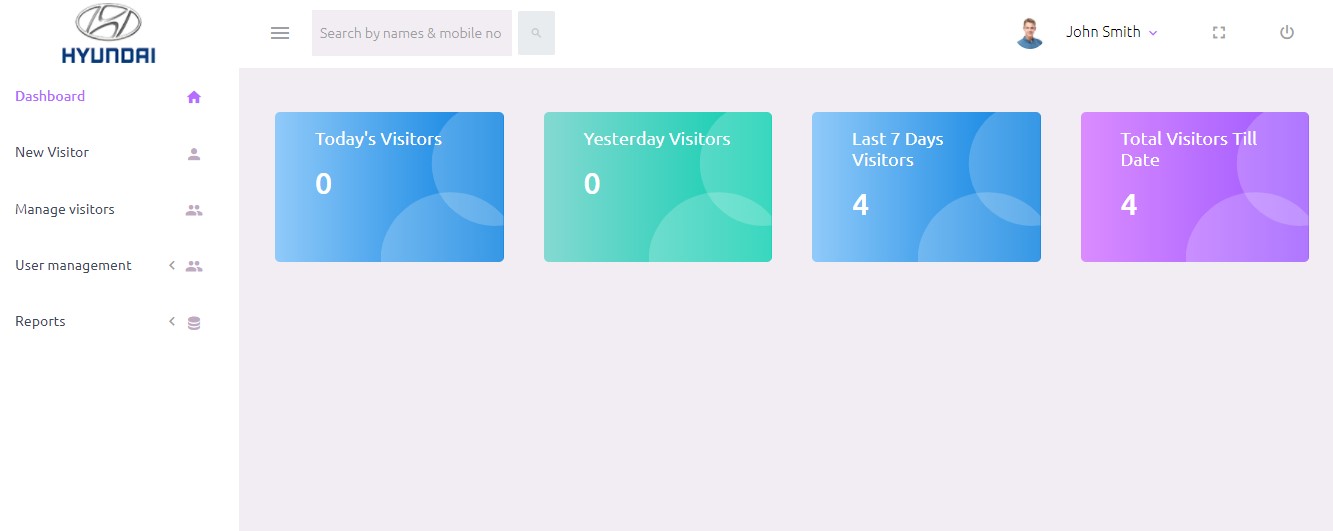
Visitor management means the tracking of how much a building is used, the visitor details and their activities when they are in your building. Examples of buildings include airports, hotels, schools, universities, shopping centres, office buildings, and more.
Visitor management is also the processes that someone undertakes in order to process visitors, including pre-registration, checking-in, badge printing and security, wayfinding, meeting room booking and more.
Company visitors management system is online which help to register visitors details like Name, address, email, Natonal ID numbers, reason, entering time and contacts before they enter. And also their information is updated at time of leaving(Leaving time). This system enables company truck to thier visitors in case of any crime.
Recent Tutorials
- How to create piechart with Mysql dynamic data.
- How to register and login in php.
- How to check password strength in php.
- Dependant dropdown in Php and Mysql.
PHP Projects
- Ecommerce website in php and mysql with source code
- Electronics management system using php and mysql with source code
- Grocery management system using php and mysql with source code
- Furniture shop management system using php and mysql with source code
- Student details management system
- Poultry farm management system
- Church management system
- Car rental management system
- Tourism management system
- Company visitors management system
- Hostel booking management system
- Beauty salon management system
- Decoration booking management system
- Zoo management system
All Tutorials
- Inline editing in Php and Mysql
- Dependant dropdown in Php and Mysql
- How to upload image using php and Mysql
- How to update image using php and Mysql
- How to restrict image format upload using php and Mysql
- How to limit image size upload using php and Mysql
- How to create bar graph with Mysql dynamic data
- How to create piechart with Mysql dynamic data
- How to create area chart with Mysql dynamic data
- How to create doughnut chart with mysql dynamic data
- How to delete Table Row using Sweetalert2
- How to dispaly Mysql data in modal using php
- How to edit Mysql data in modal using php
- How to insert Mysql data with modal
- How to insert and edit Mysql data with modal using php
- How to delete Multiple Record in PHP
- How to generate Mysql data in excel
- How to generate Mysql data in pdf
- How to login with remember me function in php
- How to generate barcode in php
- How to register and login in php
- Login attempts in php
- How to check password strength in php
- How to insert data into MySql using PHP
- How to fetch data from MySql using PHP
- User Login And Login Tracking Using PHP
- How to insert data in the Database using PHP Prepared Statement
- How to create,read,update and delete data in the Database using Php data objects
- How to delete data from Mysql database using Php
- How to upload pdf/docs/zipped files using Php
You Might Also Like
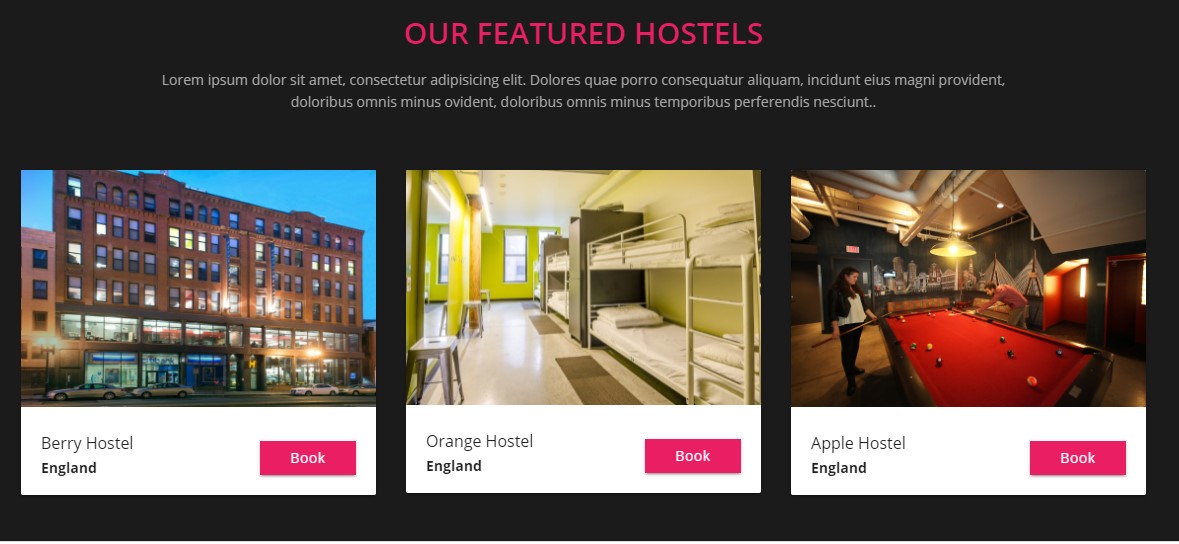
Hostel booking management system Learn More .
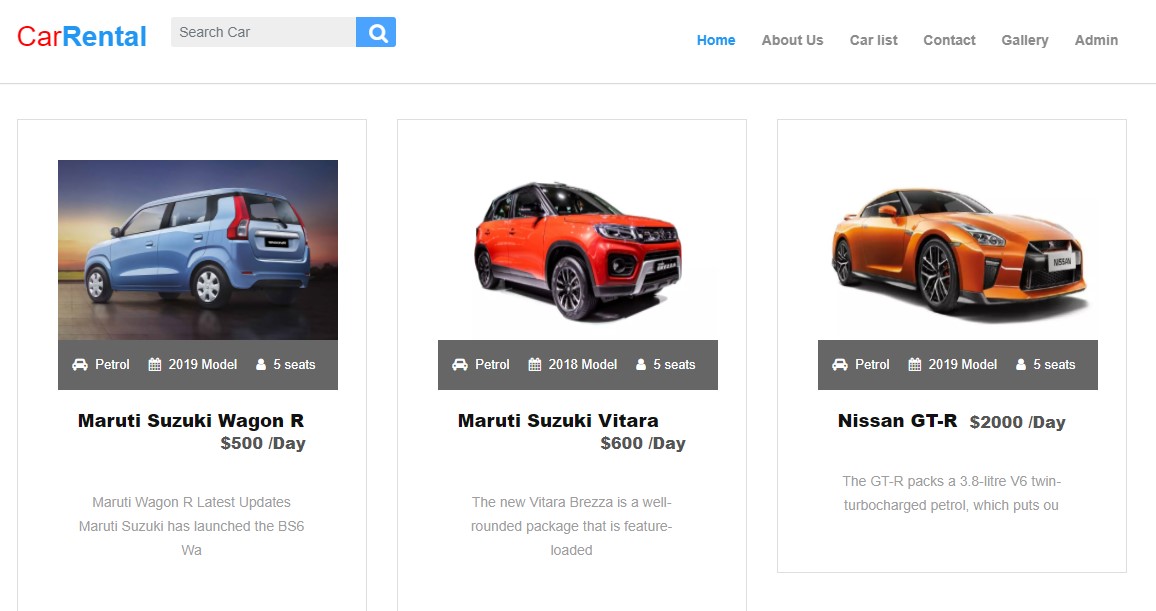
Car rental management system in Php Learn More .
Student details management system Learn More .
Tourism management system in Php and Mysql Learn More
Latest Tutorial
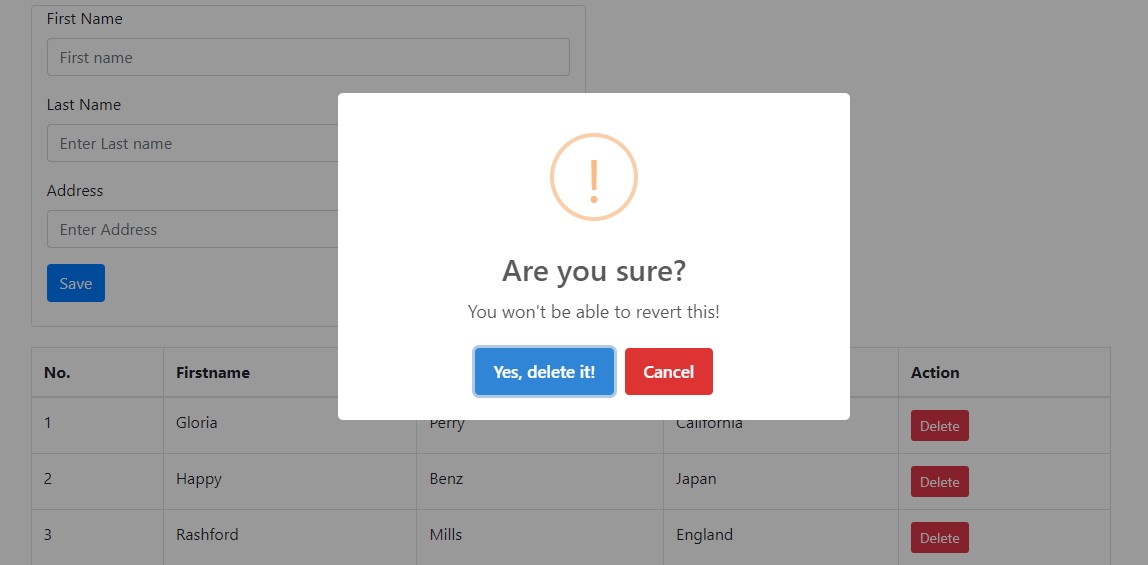
How to delete table row using sweet alert2 Learn More
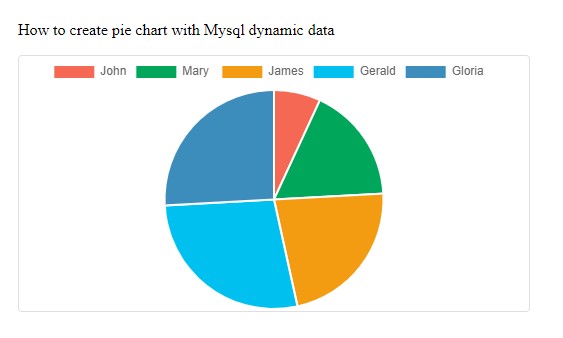
How to create piechart with Mysql data Learn More
How to register and login in php Learn More
How to edit Mysql data in modal using php Learn More
School Management System In PHP Open Source
[complete] school management system in php open source.
Are you looking for a COMPLETE School Management System In PHP with Source Code ? Well I’m glad to say that you are on the right website because today, I will give you an idea about the major functionalities and a complete source code of School Management System using PHP.
Open Source School Management System In PHP : About the project
The School Management System In PHP was developed using PHP CodeIgniter and MySQL Database as the system’s Back-End. This School Management System Project In PHP has a unique Interface design and a user friendly project. and also this project has many features that answer’s the needs of school.
School Management System Using PHP : Project Details and Technology
| Project Title: | School Management System In PHP |
|---|---|
| was developed using PHP CodeIgniter and MySQL Database as the system’s Back-End. | |
| Website | |
| PHP version 5.6 | |
| MySQL Database |
School Management System Project In PHP : Features
Student List of Featu res
Project Output
Admin Dashboard
Parent Information System
To start executing this School Management System In PHP , makes sure that you have sublime or any platform of PHP and MySQL installed in your computer.
School Management System In PHP Open Source : Steps on how to run the project
Download source code below, related articles, 104 thoughts on “school management system in php open source”.
There is a password on the zip file Please can you give me the password
Password: itsourcecode
thank you . 🥰🥰🥰
Great sms, but isn’t updated.. mysql has been removed!
Do you have dcmont analysis files?
emails and the passwords for the management system
When I log in to localhost/sms, it does not start, it shows a white page devoid of any interfaces
same problem occured for me also.. did you resolved it yet… 8019140701
hey dude it show a internal error of code 500 , please help me resolve it
It says page is not working Error: 500
same with me. Hope someone helps us.
Make sure you download XAMPP with PHP 5.6, it’ll work
Hi my php is 7.4 but after installing there is only white page showing
What is the error?
This page isn’t working right now localhost can’t currently handle this request. HTTP ERROR 500
If the php is higher should be working right, or it need PHP 5.6 only?
It need xampp version 5.6 only
Hi : h how to run the project in godaddy domain by cpanel thanks
need password for admin profile
the admin password is in the sql database
Project shows Unauthorised
If it is unauthorized it means your username and password is not in database
how do u mean
$db[‘default’][‘hostname’] = ‘localhost’; $db[‘default’][‘username’] = ‘u991834391_theschool’; $db[‘default’][‘password’] = ‘fsfgmmit843.’; $db[‘default’][‘database’] = ‘u991834391_school’; $db[‘default’][‘dbdriver’] = ‘mysql’;
user – [email protected] Password is – admin
Unable to process what can I do for that
What is unable to process?
This page isn’t working localhost is unable to handle this request HTTP error 500
What xampp version did you used?
localhost/sms……. but not run http://500 error……………………………….
Maybe it can solve your problem
Meu email: [email protected] Instagram: https://www.instagram.com/edvanbveloso/
May I see the error?
can’t login
You already export the database in phpmyadmin?
Variable name was expected. (near “?” at position 1) Unexpected character. (near “[” at position 2229) Unexpected character. (near “]” at position 2238) Variable name was expected. (near “?” at position 2241) Unexpected character. (near “[” at position 2251) Unexpected character. (near “]” at position 2260) Variable name was expected. (near ” ” at position 2263) Unexpected beginning of statement. (near “?” at position 1) Unexpected beginning of statement. (near “php” at position 2) Unexpected beginning of statement. (near “CodeIgniter” at position 13) Unexpected beginning of statement. (near “An” at position 31) Unrecognized statement type. (near “open” at position 34)
What version of php you are using?
Hello how much can I pay to buy this system
You dont need to buy this system. Its already free. you can download it for free.
please can you give me the pass word of zip file
itsourcecode or itsourcecode.com
attendance system is not working can you please tell me why?
Its working..what is the error?
Why is not work?
using updated PHP
[email protected] par
can you add it’s UML diagrams such as use case , class …..ect
Can we used XAMPP with PHP 8.1?
Yes, try to used the xampp 8.1
Installed on c panel of web page, after configurating only white page is showing
It shows a blank page after running the ( localhost/sms
You need to install xampp 5.6 version and it will run it
Can we upload our logo? The system says it is successful but not changing the logo while uploading it.
Yes you can upload it.. Maybe there is an error?
What a click bate crook. All developers like you should should just resign
Why did you say that. I think there is an error?
how to put it online in 2023
What do you mean put it online in 2023?
Should I downgrade my php to the spesific requirement or something cause the error is 505. Says the page isn’t working right now. Or is there any directories i should change inside any of the files. But that’s not the case right? It supposed to be just import the sql to the db and then can directly open the index. But that error pop up.
Moderator notice me.
Yes you can downgrade it tp xampp version 5.5 or 5.6
Kind sir. Please reply me. I have that death error 500.
you need to install xampp 5.5 or 5.6 version
your package does not have source code and show the error 500 on the localhost is currently unable to handle this request how to fix
You need to install xampp 5.5 or 5.6 version
Hello, I cannot extract the zip file.. Getting unexpected error
Zip file Password: itsourcecode
Hellew sir I can’t login
What do you mean you can’t login?
[email protected] does not work
You already import the sql in phpmyadmin?
how can we change Logo, looks its not works
You may change it inside the code
what changes we require ?
hey it shows 404 page not found and if i want to access index page it keeps me directing in same page http://localhost/sms/index.php?librarian/dashboard
please do you have the extraction code ?
Extraction Password: itsourcecode
please for the extraction code the one you gave ‘ itsourcecode’ is not working
i used PHP version: 8.0.25 blank page how to solve this
To run the system You need PHP version 5.6.
Can I get the documentation File of the Project Please!
Yes You can search it in the website
Unauthorized, this is what i am getting on startup i have changed the Database setting to my server, what could be the issue?
what database server did you use to open the sql database?
Sorry when I’m logging in by using teacher login account it display 404 page not found. Can you help me to solve this?
Unauthorized! error showing but database also correctly placed so please guide me
php version using 5.6 and above this version showing only white blank page
You can install php version 5.4 or 5.5
password- admin
What version of PHP did you use?
If you use 5.6 it will function
how to get zip extract password
thanks for such complete system but how can use with all features because just a few options are working others are just screenshots. I need this system for my school with all mention features and how much it will cost
Which school will used this system?
Leave a Comment Cancel reply
At the heart of GitHub is an open-source version control system (VCS) called Git. Git is responsible for everything GitHub-related that happens locally on your computer.
In this article
To use Git on the command line, you will need to download, install, and configure Git on your computer. You can also install GitHub CLI to use GitHub from the command line. For more information, see " About GitHub CLI ."
If you want to work with Git locally, but do not want to use the command line, you can download and install the GitHub Desktop client. For more information, see " About GitHub Desktop ."
If you do not need to work with files locally, GitHub lets you complete many Git-related actions directly in the browser, including:
- Quickstart for repositories
- Fork a repository
- Managing files
Setting up Git
Download and install the latest version of Git .
Note : Most Chrome OS devices from 2020 onwards now have a built-in Linux environment, which includes Git. To enable it, go to the Launcher, search for Linux, and click Turn on .
If you are using an older Chrome OS device, another method is required:
- Install a terminal emulator such as Termux from the Google Play Store on your Chrome OS device.
- From the terminal emulator that you installed, install Git. For example, in Termux, enter apt install git and then type y when prompted.
Set your username in Git .
Set your commit email address in Git .
Authenticating with GitHub from Git
When you connect to a GitHub repository from Git, you will need to authenticate with GitHub using either HTTPS or SSH.
Note: You can authenticate to GitHub using GitHub CLI, for either HTTP or SSH. For more information, see gh auth login .
Connecting over HTTPS (recommended)
If you clone with HTTPS, you can cache your GitHub credentials in Git using a credential helper. For more information, see " About remote repositories " and " Caching your GitHub credentials in Git ."
Connecting over SSH
If you clone with SSH, you must generate SSH keys on each computer you use to push or pull from GitHub. For more information, see " About remote repositories " and " Generating a new SSH key and adding it to the ssh-agent ."
You now have Git and GitHub all set up. You may now choose to create a repository where you can put your projects. Saving your code in a repository allows you to back up your code and share it around the world.
Creating a repository for your project allows you to store code in GitHub. This provides a backup of your work that you can choose to share with other developers. For more information, see " Quickstart for repositories ."
Forking a repository will allow you to make changes to another repository without affecting the original. For more information, see " Fork a repository ."
Each repository on GitHub is owned by a person or an organization. You can interact with the people, repositories, and organizations by connecting and following them on GitHub. For more information, see " Finding inspiration on GitHub ."
GitHub has a great support community where you can ask for help and talk to people from around the world. Join the conversation on GitHub Community .

An official website of the United States government
Here’s how you know
Official websites use .gov A .gov website belongs to an official government organization in the United States.
Secure .gov websites use HTTPS A lock ( Lock A locked padlock ) or https:// means you’ve safely connected to the .gov website. Share sensitive information only on official, secure websites.
Free Cyber Services #protect2024 Secure Our World Shields Up Report A Cyber Issue
Vulnerability Summary for the Week of June 3, 2024
The CISA Vulnerability Bulletin provides a summary of new vulnerabilities that have been recorded by the National Institute of Standards and Technology (NIST) National Vulnerability Database (NVD) in the past week. NVD is sponsored by CISA. In some cases, the vulnerabilities in the bulletin may not yet have assigned CVSS scores. Please visit NVD for updated vulnerability entries, which include CVSS scores once they are available.
Vulnerabilities are based on the Common Vulnerabilities and Exposures (CVE) vulnerability naming standard and are organized according to severity, determined by the Common Vulnerability Scoring System (CVSS) standard. The division of high, medium, and low severities correspond to the following scores:
- High : vulnerabilities with a CVSS base score of 7.0–10.0
- Medium : vulnerabilities with a CVSS base score of 4.0–6.9
- Low : vulnerabilities with a CVSS base score of 0.0–3.9
Entries may include additional information provided by organizations and efforts sponsored by CISA. This information may include identifying information, values, definitions, and related links. Patch information is provided when available. Please note that some of the information in the bulletin is compiled from external, open-source reports and is not a direct result of CISA analysis.
High Vulnerabilities
| Primary Vendor -- Product | Description | Published | CVSS Score | Source & Patch Info |
|---|---|---|---|---|
| 8theme--XStore Core | Improper Limitation of a Pathname to a Restricted Directory ('Path Traversal') vulnerability in 8theme XStore Core allows PHP Local File Inclusion.This issue affects XStore Core: from n/a through 5.3.8. | 2024-06-04 | | |
| 8theme--XStore | Improper Limitation of a Pathname to a Restricted Directory ('Path Traversal') vulnerability in 8theme XStore allows PHP Local File Inclusion.This issue affects XStore: from n/a through 9.3.8. | 2024-06-04 | | |
| ABB, Busch-Jaeger--2.4! Display 55, SD/U12.55.11-825 | FDSK Leak in ABB, Busch-Jaeger, FTS Display (version 1.00) and BCU (version 1.3.0.33) allows attacker to take control via access to local KNX Bus-System | 2024-06-05 | | |
| ABB, Busch-Jaeger--2.4! Display 55, SD/U12.55.11-825 | Replay Attack in ABB, Busch-Jaeger, FTS Display (version 1.00) and BCU (version 1.3.0.33) allows attacker to capture/replay KNX telegram to local KNX Bus-System | 2024-06-05 | | |
| BdThemes--Element Pack Pro | Improper Limitation of a Pathname to a Restricted Directory ('Path Traversal'), Deserialization of Untrusted Data vulnerability in BdThemes Element Pack Pro allows Path Traversal, Object Injection.This issue affects Element Pack Pro: from n/a through 7.7.4. | 2024-06-04 | | |
| BestWebSoft--Contact Form to DB by BestWebSoft | Improper Neutralization of Special Elements used in an SQL Command ('SQL Injection') vulnerability in BestWebSoft Contact Form to DB by BestWebSoft.This issue affects Contact Form to DB by BestWebSoft: from n/a through 1.7.2. | 2024-06-08 | | |
| Bitdefender--GravityZone Console On-Premise | A host whitelist parser issue in the proxy service implemented in the GravityZone Update Server allows an attacker to cause a server-side request forgery. This issue only affects GravityZone Console versions before 6.38.1-2 that are running only on premise. | 2024-06-06 | | |
| bobbysmith007--WP-DB-Table-Editor | The WP-DB-Table-Editor plugin for WordPress is vulnerable to unauthorized access of data, modification of data, and loss of data due to lack of a default capability requirement on the 'dbte_render' function in all versions up to, and including, 1.8.4. This makes it possible for authenticated attackers, with contributor access and above, to modify database tables that the theme has been configured to use the plugin to edit. | 2024-06-04 | | |
| chainguard-dev--apko | apko is an apk-based OCI image builder. apko exposures HTTP basic auth credentials from repository and keyring URLs in log output. This vulnerability is fixed in v0.14.5. | 2024-06-03 | | |
| Chanjet--Smooth T+system | A vulnerability, which was classified as critical, has been found in Chanjet Smooth T+system 3.5. This issue affects some unknown processing of the file /tplus/UFAQD/keyEdit.aspx. The manipulation of the argument KeyID leads to sql injection. The attack may be initiated remotely. The exploit has been disclosed to the public and may be used. The identifier VDB-267185 was assigned to this vulnerability. NOTE: The vendor was contacted early about this disclosure but did not respond in any way. | 2024-06-05 | | |
| chrisbadgett--LifterLMS WordPress LMS for eLearning | The LifterLMS - WordPress LMS Plugin for eLearning plugin for WordPress is vulnerable to SQL Injection via the orderBy attribute of the lifterlms_favorites shortcode in all versions up to, and including, 7.6.2 due to insufficient escaping on the user supplied parameter and lack of sufficient preparation on the existing SQL query. This makes it possible for authenticated attackers, with Contributor-level access and above, to append additional SQL queries into already existing queries that can be used to extract sensitive information from the database. | 2024-06-05 | | |
| Cisco--Cisco Unified Contact Center Enterprise | A vulnerability in the web-based management interface of Cisco Finesse could allow an unauthenticated, remote attacker to conduct an SSRF attack on an affected system. This vulnerability is due to insufficient validation of user-supplied input for specific HTTP requests that are sent to an affected system. An attacker could exploit this vulnerability by sending a crafted HTTP request to the affected device. A successful exploit could allow the attacker to obtain limited sensitive information for services that are associated to the affected device. | 2024-06-05 | | |
| Code for Recovery--12 Step Meeting List | Improper Neutralization of Input During Web Page Generation (XSS or 'Cross-site Scripting') vulnerability in Code for Recovery 12 Step Meeting List allows Reflected XSS.This issue affects 12 Step Meeting List: from n/a through 3.14.33. | 2024-06-08 | | |
| Code Parrots--Easy Forms for Mailchimp | Insertion of Sensitive Information into Log File vulnerability in Code Parrots Easy Forms for Mailchimp.This issue affects Easy Forms for Mailchimp: from n/a through 6.9.0. | 2024-06-04 | | |
| Codeer Limited--Bricks Builder | Improper Control of Generation of Code ('Code Injection') vulnerability in Codeer Limited Bricks Builder allows Code Injection.This issue affects Bricks Builder: from n/a through 1.9.6. | 2024-06-04 | | |
| codelessthemes--Cowidgets Elementor Addons | The Cowidgets - Elementor Addons plugin for WordPress is vulnerable to Local File Inclusion in all versions up to, and including, 1.1.1 via the 'item_style' and 'style' parameters. This makes it possible for authenticated attackers, with Contributor-level access and above, to include and execute arbitrary files on the server, allowing the execution of any PHP code in those files. This can be used to bypass access controls, obtain sensitive data, or achieve code execution in cases where images and other "safe" file types can be uploaded and included. | 2024-06-06 | | |
| CodePeople--WP Time Slots Booking Form | Improper Neutralization of Input During Web Page Generation (XSS or 'Cross-site Scripting') vulnerability in CodePeople WP Time Slots Booking Form allows Stored XSS.This issue affects WP Time Slots Booking Form: from n/a through 1.2.10. | 2024-06-08 | | |
| CODESYS--CODESYS Control for BeagleBone SL | An unauthenticated remote attacker can use a malicious OPC UA client to send a crafted request to affected CODESYS products which can cause a DoS due to incorrect calculation of buffer size. | 2024-06-04 | | |
| CODESYS--CODESYS Control Win (SL) | A local attacker with low privileges can read and modify any users files and cause a DoS in the working directory of the affected products due to exposure of resource to wrong sphere. | 2024-06-04 | | |
| Dell--CPG BIOS | Dell BIOS contains a missing support for integrity check vulnerability. An attacker with physical access to the system could potentially bypass security mechanisms to run arbitrary code on the system. | 2024-06-07 | | |
| Dell--PowerScale OneFS | Dell PowerScale OneFS versions 8.2.x through 9.8.0.x contain a use of hard coded credentials vulnerability. An adjacent network unauthenticated attacker could potentially exploit this vulnerability, leading to information disclosure of network traffic and denial of service. | 2024-06-04 | | |
| denoland--deno | An issue in `.npmrc` support in Deno 1.44.0 was discovered where Deno would send `.npmrc` credentials for the scope to the tarball URL when the registry provided URLs for a tarball on a different domain. All users relying on .npmrc are potentially affected by this vulnerability if their private registry references tarball URLs at a different domain. This includes usage of deno install subcommand, auto-install for npm: specifiers and LSP usage. It is recommended to upgrade to Deno 1.44.1 and if your private registry ever serves tarballs at a different domain to rotate your registry credentials. | 2024-06-06 | | |
| dexta--Dextaz Ping | Improper Neutralization of Special Elements used in a Command ('Command Injection') vulnerability in dexta Dextaz Ping allows Command Injection.This issue affects Dextaz Ping: from n/a through 0.65. | 2024-06-04 | | |
| DigiWin--EasyFlow .NET | DigiWin EasyFlow .NET lacks validation for certain input parameters. An unauthenticated remote attacker can inject arbitrary SQL commands to read, modify, and delete database records. | 2024-06-03 | | |
| directus--directus | Directus is a real-time API and App dashboard for managing SQL database content. Prior to 10.11.2, providing a non-numeric length value to the random string generation utility will create a memory issue breaking the capability to generate random strings platform wide. This creates a denial of service situation where logged in sessions can no longer be refreshed as sessions depend on the capability to generate a random session ID. This vulnerability is fixed in 10.11.2. | 2024-06-03 | | |
| envoyproxy--envoy | Envoy is a cloud-native, open source edge and service proxy. Envoyproxy with a Brotli filter can get into an endless loop during decompression of Brotli data with extra input. | 2024-06-04 | | |
| envoyproxy--envoy | Envoy is a cloud-native, open source edge and service proxy. Due to how Envoy invoked the nlohmann JSON library, the library could throw an uncaught exception from downstream data if incomplete UTF-8 strings were serialized. The uncaught exception would cause Envoy to crash. | 2024-06-04 | | |
| evmos--evmos | Evmos is the Ethereum Virtual Machine (EVM) Hub on the Cosmos Network. There is an issue with how to liquid stake using Safe which itself is a contract. The bug only appears when there is a local state change together with an ICS20 transfer in the same function and uses the contract's balance, that is using the contract address as the sender parameter in an ICS20 transfer using the ICS20 precompile. This is in essence the "infinite money glitch" allowing contracts to double the supply of Evmos after each transaction.The issue has been patched in versions >=V18.1.0. | 2024-06-06 | | |
| expresstech--Quiz and Survey Master (QSM) Easy Quiz and Survey Maker | The Quiz And Survey Master - Best Quiz, Exam and Survey Plugin for WordPress plugin for WordPress is vulnerable to SQL Injection via the 'question_id' parameter in all versions up to, and including, 9.0.1 due to insufficient escaping on the user supplied parameter and lack of sufficient preparation on the existing SQL query. This makes it possible for authenticated attackers, with contributor-level access and above, to append additional SQL queries into already existing queries that can be used to extract sensitive information from the database. | 2024-06-07 | | |
| Fahad Mahmood--WP Docs | Improper Neutralization of Input During Web Page Generation (XSS or 'Cross-site Scripting') vulnerability in Fahad Mahmood WP Docs allows Reflected XSS.This issue affects WP Docs: from n/a through 2.1.3. | 2024-06-08 | | |
| Foliovision--FV Flowplayer Video Player | Improper Neutralization of Input During Web Page Generation (XSS or 'Cross-site Scripting') vulnerability in Foliovision FV Flowplayer Video Player allows Reflected XSS.This issue affects FV Flowplayer Video Player: from n/a through 7.5.45.7212. | 2024-06-03 | | |
| Fortinet--FortiWebManager | An improper authorization in Fortinet FortiWebManager version 7.2.0 and 7.0.0 through 7.0.4 and 6.3.0 and 6.2.3 through 6.2.4 and 6.0.2 allows attacker to execute unauthorized code or commands via HTTP requests or CLI. | 2024-06-03 | | |
| Fortinet--FortiWebManager | An improper authorization in Fortinet FortiWebManager version 7.2.0 and 7.0.0 through 7.0.4 and 6.3.0 and 6.2.3 through 6.2.4 and 6.0.2 allows attacker to execute unauthorized code or commands via HTTP requests or CLI. | 2024-06-03 | | |
| Fortinet--FortiWebManager | An improper authorization in Fortinet FortiWebManager version 7.2.0 and 7.0.0 through 7.0.4 and 6.3.0 and 6.2.3 through 6.2.4 and 6.0.2 allows attacker to execute unauthorized code or commands via HTTP requests or CLI. | 2024-06-03 | | |
| gelform--Social Link Pages: link-in-bio landing pages for your social media profiles | The Social Link Pages: link-in-bio landing pages for your social media profiles plugin for WordPress is vulnerable to unauthorized access due to a missing capability check on the import_link_pages() function in all versions up to, and including, 1.6.9. This makes it possible for unauthenticated attackers to inject arbitrary pages and malicious web scripts. | 2024-06-04 | | |
| GiveWP--GiveWP | Improper Neutralization of Input During Web Page Generation (XSS or 'Cross-site Scripting') vulnerability in GiveWP allows Reflected XSS.This issue affects GiveWP: from n/a through 3.12.0. | 2024-06-08 | | |
| Grafana--OnCall | Grafana OnCall is an easy-to-use on-call management tool that will help reduce toil in on-call management through simpler workflows and interfaces that are tailored specifically for engineers. Grafana OnCall, from version 1.1.37 before 1.5.2 are vulnerable to a Server Side Request Forgery (SSRF) vulnerability in the webhook functionallity. This issue was fixed in version 1.5.2 | 2024-06-05 | | |
| HCL Software--Domino Server | The Domino Catalog template is susceptible to a Stored Cross-Site Scripting (XSS) vulnerability. An attacker with the ability to edit documents in the catalog application/database created from this template can embed a cross site scripting attack. The attack would be activated by an end user clicking it. | 2024-06-06 | | |
| IBM--Engineering Requirements Management DOORS Next | IBM Engineering Requirements Management DOORS Next 7.0.2 and 7.0.3 is vulnerable to an XML External Entity Injection (XXE) attack when processing XML data. A remote attacker could exploit this vulnerability to expose sensitive information or consume memory resources. IBM X-Force ID: 268758. | 2024-06-06 | | |
| icegram--Email Subscribers by Icegram Express Email Marketing, Newsletters, Automation for WordPress & WooCommerce | The Email Subscribers by Icegram Express plugin for WordPress is vulnerable to SQL Injection via the 'hash' parameter in all versions up to, and including, 5.7.20 due to insufficient escaping on the user supplied parameter and lack of sufficient preparation on the existing SQL query. This makes it possible for unauthenticated attackers to append additional SQL queries into already existing queries that can be used to extract sensitive information from the database. | 2024-06-05 | | |
| idccms -- idccms | idccms V1.35 was discovered to contain a Cross-Site Request Forgery (CSRF) via the component admin/vpsClass_deal.php?mudi=add | 2024-06-04 | | |
| idccms -- idccms | idccms V1.35 was discovered to contain a Cross-Site Request Forgery (CSRF) via admin/vpsCompany_deal.php?mudi=del | 2024-06-04 | | |
| idccms -- idccms | idccms v1.35 was discovered to contain a Cross-Site Request Forgery (CSRF) via /admin/vpsCompany_deal.php?mudi=rev&nohrefStr=close | 2024-06-04 | | |
| idccms -- idccms | idccms V1.35 was discovered to contain a Cross-Site Request Forgery (CSRF) via /admin/vpsCompany_deal.php?mudi=add&nohrefStr=close | 2024-06-04 | | |
| ifm--moneo appliance QVA200 | An unauthenticated remote attacker can change the admin password in a moneo appliance due to weak password recovery mechanism. | 2024-06-03 | | |
| itsourcecode--Bakery Online Ordering System | A vulnerability was found in itsourcecode Bakery Online Ordering System 1.0. It has been classified as critical. Affected is an unknown function of the file /admin/modules/product/controller.php?action=add. The manipulation of the argument image leads to unrestricted upload. It is possible to launch the attack remotely. The exploit has been disclosed to the public and may be used. VDB-267414 is the identifier assigned to this vulnerability. | 2024-06-07 | | |
| itsourcecode--Online Discussion Forum | A vulnerability was found in itsourcecode Online Discussion Forum 1.0. It has been rated as critical. This issue affects some unknown processing of the file register_me.php. The manipulation of the argument eaddress leads to sql injection. The attack may be initiated remotely. The exploit has been disclosed to the public and may be used. The associated identifier of this vulnerability is VDB-267407. | 2024-06-07 | | |
| jupyter-server--jupyter_server | The Jupyter Server provides the backend for Jupyter web applications. Jupyter Server on Windows has a vulnerability that lets unauthenticated attackers leak the NTLMv2 password hash of the Windows user running the Jupyter server. An attacker can crack this password to gain access to the Windows machine hosting the Jupyter server, or access other network-accessible machines or 3rd party services using that credential. Or an attacker perform an NTLM relay attack without cracking the credential to gain access to other network-accessible machines. This vulnerability is fixed in 2.14.1. | 2024-06-06 | | |
| kanboard--kanboard | Kanboard is project management software that focuses on the Kanban methodology. The vuln is in app/Controller/ProjectPermissionController.php function addUser(). The users permission to add users to a project only get checked on the URL parameter project_id. If the user is authorized to add users to this project the request gets processed. The users permission for the POST BODY parameter project_id does not get checked again while processing. An attacker with the 'Project Manager' on a single project may take over any other project. The vulnerability is fixed in 1.2.37. | 2024-06-06 | | |
| litonice13--Master Addons Free Widgets, Hover Effects, Toggle, Conditions, Animations for Elementor | The Master Addons - Free Widgets, Hover Effects, Toggle, Conditions, Animations for Elementor plugin for WordPress is vulnerable to Stored Cross-Site Scripting via the Navigation Menu widget of the plugin's Mega Menu extension in all versions up to, and including, 2.0.6.1 due to insufficient input sanitization and output escaping on user supplied attributes. This makes it possible for unauthenticated attackers to inject arbitrary web scripts in pages that will execute whenever a user accesses an injected page. | 2024-06-07 | | |
| LJ Apps--WP TripAdvisor Review Slider | Improper Neutralization of Special Elements used in an SQL Command ('SQL Injection') vulnerability in LJ Apps WP TripAdvisor Review Slider allows Blind SQL Injection.This issue affects WP TripAdvisor Review Slider: from n/a through 12.6. | 2024-06-03 | | |
| Loopus--WP Visitors Tracker | Improper Neutralization of Input During Web Page Generation (XSS or 'Cross-site Scripting') vulnerability in Loopus WP Visitors Tracker allows Reflected XSS.This issue affects WP Visitors Tracker: from n/a through 2.3. | 2024-06-08 | | |
| lvaudore--The Moneytizer | The The Moneytizer plugin for WordPress is vulnerable to unauthorized access of data, modification of data, and loss of data due to a missing capability check on multiple AJAX functions in the /core/core_ajax.php file in all versions up to, and including, 9.5.20. This makes it possible for authenticated attackers, with subscriber access and above, to update and retrieve billing and bank details, update and reset the plugin's settings, and update languages as well as other lower-severity actions. | 2024-06-06 | | |
| lvaudore--The Moneytizer | The The Moneytizer plugin for WordPress is vulnerable to Cross-Site Request Forgery in all versions up to, and including, 9.5.20. This is due to missing or incorrect nonce validation on multiple AJAX functions. This makes it possible for unauthenticated attackers to to update and retrieve billing and bank details, update and reset the plugin's settings, and update languages as well as other lower-severity actions via a forged request granted they can trick a site administrator into performing an action such as clicking on a link. | 2024-06-06 | | |
| misskey-dev--misskey | Misskey is an open source, decentralized microblogging platform. Misskey doesn't perform proper normalization on the JSON structures of incoming signed ActivityPub activity objects before processing them, allowing threat actors to spoof the contents of signed activities and impersonate the authors of the original activities. This vulnerability is fixed in 2024.5.0. | 2024-06-03 | | |
| MLflow--MLflow | Deserialization of untrusted data can occur in versions of the MLflow platform running version 1.1.0 or newer, enabling a maliciously uploaded scikit-learn model to run arbitrary code on an end user's system when interacted with. | 2024-06-04 | | |
| MLflow--MLflow | Deserialization of untrusted data can occur in versions of the MLflow platform running version 1.1.0 or newer, enabling a maliciously uploaded scikit-learn model to run arbitrary code on an end user's system when interacted with. | 2024-06-04 | | |
| MLflow--MLflow | Deserialization of untrusted data can occur in versions of the MLflow platform running version 0.9.0 or newer, enabling a maliciously uploaded PyFunc model to run arbitrary code on an end user's system when interacted with. | 2024-06-04 | | |
| MLflow--MLflow | Deserialization of untrusted data can occur in versions of the MLflow platform running version 1.24.0 or newer, enabling a maliciously uploaded pmdarima model to run arbitrary code on an end user's system when interacted with. | 2024-06-04 | | |
| MLflow--MLflow | Deserialization of untrusted data can occur in versions of the MLflow platform running version 1.23.0 or newer, enabling a maliciously uploaded LightGBM scikit-learn model to run arbitrary code on an end user's system when interacted with. | 2024-06-04 | | |
| MLflow--MLflow | Deserialization of untrusted data can occur in versions of the MLflow platform running version 2.0.0rc0 or newer, enabling a maliciously uploaded Tensorflow model to run arbitrary code on an end user's system when interacted with. | 2024-06-04 | | |
| MLflow--MLflow | Deserialization of untrusted data can occur in versions of the MLflow platform running version 2.5.0 or newer, enabling a maliciously uploaded Langchain AgentExecutor model to run arbitrary code on an end user's system when interacted with. | 2024-06-04 | | |
| MLflow--MLflow | Deserialization of untrusted data can occur in versions of the MLflow platform running version 0.5.0 or newer, enabling a maliciously uploaded PyTorch model to run arbitrary code on an end user's system when interacted with. | 2024-06-04 | | |
| MLflow--MLflow | Deserialization of untrusted data can occur in versions of the MLflow platform running version 1.27.0 or newer, enabling a maliciously crafted Recipe to execute arbitrary code on an end user's system when run. | 2024-06-04 | | |
| MLflow--MLflow | Remote Code Execution can occur in versions of the MLflow platform running version 1.11.0 or newer, enabling a maliciously crafted MLproject to execute arbitrary code on an end user's system when run. | 2024-06-04 | | |
| n/a--Clash | A vulnerability was found in Clash up to 0.20.1 on Windows. It has been declared as critical. This vulnerability affects unknown code of the component Proxy Port. The manipulation leads to improper authentication. The attack can be initiated remotely. The exploit has been disclosed to the public and may be used. It is recommended to change the configuration settings. VDB-267406 is the identifier assigned to this vulnerability. | 2024-06-07 | | |
| n/a--n/a | An issue was discovered in Samsung Mobile Processor Exynos 2200, Exynos 1480, Exynos 2400. It lacks a check for the validation of native handles, which can result in code execution. | 2024-06-07 | | |
| n/a--n/a | An issue was discovered in Samsung Mobile Processor and Wearable Processor Exynos 850, Exynos 1080, Exynos 2100, Exynos 1280, Exynos 1380, Exynos 1330, Exynos W920, Exynos W930. The mobile processor lacks proper reference count checking, which can result in a UAF (Use-After-Free) vulnerability. | 2024-06-07 | | |
| n/a--n/a | An issue was discovered in Samsung Mobile Processor and Wearable Processor Exynos 850, Exynos 1080, Exynos 2100, Exynos 1280, Exynos 1380, Exynos 1330, Exynos W920, Exynos W930. The mobile processor lacks proper memory deallocation checking, which can result in a UAF (Use-After-Free) vulnerability. | 2024-06-07 | | |
| Netgsm--Netgsm | Missing Authorization vulnerability in Netgsm.This issue affects Netgsm: from n/a through 2.9.16. | 2024-06-04 | | |
| open-telemetry--opentelemetry-collector | The OpenTelemetry Collector offers a vendor-agnostic implementation on how to receive, process and export telemetry data. An unsafe decompression vulnerability allows unauthenticated attackers to crash the collector via excessive memory consumption. OTel Collector version 0.102.1 fixes this issue. It is also fixed in the confighttp module version 0.102.0 and configgrpc module version 0.102.1. | 2024-06-05 | | |
| phoeniixx--Social Login Lite For WooCommerce | The Social Login Lite For WooCommerce plugin for WordPress is vulnerable to authentication bypass in versions up to, and including, 1.6.0. This is due to insufficient verification on the user being supplied during the social login through the plugin. This makes it possible for unauthenticated attackers to log in as any existing user on the site, such as an administrator, if they have access to the email. | 2024-06-04 | | |
| pimcore--pimcore | Pimcore is an Open Source Data & Experience Management Platform. The Pimcore thumbnail generation can be used to flood the server with large files. By changing the file extension or scaling factor of the requested thumbnail, attackers can create files that are much larger in file size than the original. This vulnerability is fixed in 11.2.4. | 2024-06-04 | | |
| pokornydavid--Frontend Registration Contact Form 7 | The Frontend Registration - Contact Form 7 plugin for WordPress is vulnerable to privilege escalation in versions up to, and including, 5.1 due to insufficient restriction on the '_cf7frr_' post meta. This makes it possible for authenticated attackers, with editor-level access and above, to modify the default user role in the registration form settings. | 2024-06-04 | | |
| PORTY Smart Tech Technology Joint Stock Company--PowerBank Application | Exposure of Sensitive Information to an Unauthorized Actor vulnerability in PORTY Smart Tech Technology Joint Stock Company PowerBank Application allows Retrieve Embedded Sensitive Data.This issue affects PowerBank Application: before 2.02. | 2024-06-05 | | |
| PowerPack--PowerPack Pro for Elementor | The PowerPack Pro for Elementor plugin for WordPress is vulnerable to privilege escalation in all versions up to, and including, 2.10.17. This is due to the plugin not restricting low privileged users from setting a default role for a registration form. This makes it possible for authenticated attackers, with contributor-level access and above, to create a registration form with administrator set as the default role and then register as an administrator. | 2024-06-08 | | |
| qodeinteractive--Qi Addons For Elementor | The Qi Addons For Elementor plugin for WordPress is vulnerable to Remote File Inclusion in all versions up to, and including, 1.7.2 via the 'behavior' attributes found in the qi_addons_for_elementor_blog_list shortcode. This makes it possible for authenticated attackers, with Contributor-level access and above, to include remote files on the server, resulting in code execution. Please note that this requires an attacker to create a non-existent directory or target an instance where file_exists won't return false with a non-existent directory in the path, in order to successfully exploit. | 2024-06-07 | | |
| Qualcomm, Inc.--Snapdragon | Memory corruption in TZ Secure OS while Tunnel Invoke Manager initialization. | 2024-06-03 | | |
| Qualcomm, Inc.--Snapdragon | Cryptographic issue while performing attach with a LTE network, a rogue base station can skip the authentication phase and immediately send the Security Mode Command. | 2024-06-03 | | |
| Qualcomm, Inc.--Snapdragon | Memory corruption in Hypervisor when platform information mentioned is not aligned. | 2024-06-03 | | |
| Qualcomm, Inc.--Snapdragon | Information disclosure in Video while parsing mp2 clip with invalid section length. | 2024-06-03 | | |
| Qualcomm, Inc.--Snapdragon | Memory corruption while creating a LPAC client as LPAC engine was allowed to access GPU registers. | 2024-06-03 | | |
| Qualcomm, Inc.--Snapdragon | Memory corruption while copying a keyblob`s material when the key material`s size is not accurately checked. | 2024-06-03 | | |
| Qualcomm, Inc.--Snapdragon | Transient DOS while processing an improperly formatted Fine Time Measurement (FTM) management frame. | 2024-06-03 | | |
| realmag777--Active Products Tables for WooCommerce | Improper Neutralization of Input During Web Page Generation (XSS or 'Cross-site Scripting') vulnerability in realmag777 Active Products Tables for WooCommerce allows Reflected XSS.This issue affects Active Products Tables for WooCommerce: from n/a through 1.0.6.3. | 2024-06-08 | | |
| Red Hat--Logging Subsystem for Red Hat OpenShift | A flaw was found in OpenShift's Telemeter. If certain conditions are in place, an attacker can use a forged token to bypass the issue ("iss") check during JSON web token (JWT) authentication. | 2024-06-05 | | |
| Red Hat--Red Hat Build of Keycloak | A flaw was found in Keycloak in OAuth 2.0 Pushed Authorization Requests (PAR). Client-provided parameters were found to be included in plain text in the KC_RESTART cookie returned by the authorization server's HTTP response to a `request_uri` authorization request, possibly leading to an information disclosure vulnerability. | 2024-06-03 | | |
| Red Hat--Red Hat Enterprise Linux 8 | A flaw was found in Booth, a cluster ticket manager. If a specially-crafted hash is passed to gcry_md_get_algo_dlen(), it may allow an invalid HMAC to be accepted by the Booth server. | 2024-06-06 | | |
| Repute Infosystems--ARMember | Improper Privilege Management vulnerability in Repute Infosystems ARMember allows Privilege Escalation.This issue affects ARMember: from n/a through 4.0.10. | 2024-06-04 | | |
| RLDD--Auto Coupons for WooCommerce | Improper Neutralization of Input During Web Page Generation (XSS or 'Cross-site Scripting') vulnerability in RLDD Auto Coupons for WooCommerce allows Reflected XSS.This issue affects Auto Coupons for WooCommerce: from n/a through 3.0.14. | 2024-06-08 | | |
| Samsung Mobile--Samsung Mobile Devices | Improper access control vulnerability in SmartManagerCN prior to SMR Jun-2024 Release 1 allows local attackers to launch privileged activities. | 2024-06-04 | | |
| Samsung Mobile--Samsung Mobile Devices | Heap out-of-bound write vulnerability in parsing grid image header in libsavscmn.so prior to SMR Jun-2024 Release 1 allows local attackers to execute arbitrary code. | 2024-06-04 | | |
| Samsung Mobile--Samsung Mobile Devices | Heap out-of-bound write vulnerability in parsing grid image in libsavscmn.so prior to SMR June-2024 Release 1 allows local attackers to execute arbitrary code. | 2024-06-04 | | |
| Select-Themes--Stockholm Core | Improper Limitation of a Pathname to a Restricted Directory ('Path Traversal') vulnerability in Select-Themes Stockholm Core allows PHP Local File Inclusion.This issue affects Stockholm Core: from n/a through 2.4.1. | 2024-06-04 | | |
| Select-Themes--Stockholm | Improper Limitation of a Pathname to a Restricted Directory ('Path Traversal') vulnerability in Select-Themes Stockholm allows PHP Local File Inclusion.This issue affects Stockholm: from n/a through 9.6. | 2024-06-04 | | |
| Select-Themes--Stockholm | Improper Limitation of a Pathname to a Restricted Directory ('Path Traversal') vulnerability in Select-Themes Stockholm allows PHP Local File Inclusion.This issue affects Stockholm: from n/a through 9.6. | 2024-06-04 | | |
| Skops-dev--Skops | Deserialization of untrusted data can occur in versions 0.6 or newer of the skops python library, enabling a maliciously crafted model to run arbitrary code on an end user's system when loaded. | 2024-06-04 | | |
| softaculous--FileOrganizer Manage WordPress and Website Files | The FileOrganizer - Manage WordPress and Website Files plugin for WordPress is vulnerable to Sensitive Information Exposure in all versions up to, and including, 1.0.7 via the 'fileorganizer_ajax_handler' function. This makes it possible for unauthenticated attackers to extract sensitive data including backups or other sensitive information if the files have been moved to the built-in Trash folder. | 2024-06-07 | | |
| solarwinds -- solarwinds_platform | The SolarWinds Platform was determined to be affected by a SWQL Injection Vulnerability. Attack complexity is high for this vulnerability. | 2024-06-04 | | |
| solarwinds -- solarwinds_platform | The SolarWinds Platform was determined to be affected by a Race Condition Vulnerability affecting the web console. | 2024-06-04 | | |
| SolarWinds --SolarWinds Serv-U | SolarWinds Serv-U was susceptible to a directory transversal vulnerability that would allow access to read sensitive files on the host machine. | 2024-06-06 | | |
| sonalsinha21--SKT Addons for Elementor | The SKT Addons for Elementor plugin for WordPress is vulnerable to Stored Cross-Site Scripting via the plugin's Age Gate and Creative Slider widgets in all versions up to, and including, 2.0 due to insufficient input sanitization and output escaping on user supplied attributes. This makes it possible for authenticated attackers, with contributor-level access and above, to inject arbitrary web scripts in pages that will execute whenever a user accesses an injected page. | 2024-06-08 | | |
| Summar Software--Mentor Employee Portal | Untrusted data deserialization vulnerability has been found in Mentor - Employee Portal, affecting version 3.83.35. This vulnerability could allow an attacker to execute arbitrary code, by injecting a malicious payload into the "ViewState" field. | 2024-06-06 | | |
| Sysaid--SysAid | SysAid - CWE-89: Improper Neutralization of Special Elements used in an SQL Command ('SQL Injection') | 2024-06-06 | | |
| Sysaid--SysAid | SysAid - CWE-78: Improper Neutralization of Special Elements used in an OS Command ('OS Command Injection') | 2024-06-06 | | |
| Tainacan.org--Tainacan | Improper Neutralization of Input During Web Page Generation (XSS or 'Cross-site Scripting') vulnerability in Tainacan.Org Tainacan allows Reflected XSS.This issue affects Tainacan: from n/a through 0.21.3. | 2024-06-03 | | |
| Team Heateor--Heateor Social Login | Improper Neutralization of Input During Web Page Generation (XSS or 'Cross-site Scripting') vulnerability in Team Heateor Heateor Social Login allows Cross-Site Scripting (XSS).This issue affects Heateor Social Login: from n/a through 1.1.32. | 2024-06-08 | | |
| Themeisle--Visualizer | Improper Neutralization of Special Elements used in an SQL Command ('SQL Injection') vulnerability in Themeisle Visualizer.This issue affects Visualizer: from n/a through 3.11.1. | 2024-06-08 | | |
| themeum--Tutor LMS eLearning and online course solution | The Tutor LMS - eLearning and online course solution plugin for WordPress is vulnerable to time-based SQL Injection via the 'course_id' parameter in all versions up to, and including, 2.7.1 due to insufficient escaping on the user supplied parameter and lack of sufficient preparation on the existing SQL query. This makes it possible for authenticated attackers, with admin access and above, to append additional SQL queries into already existing queries that can be used to extract sensitive information from the database. | 2024-06-07 | | |
| ThimPress--Eduma | Improper Neutralization of Input During Web Page Generation (XSS or 'Cross-site Scripting') vulnerability in ThimPress Eduma allows Reflected XSS.This issue affects Eduma: from n/a through 5.4.7. | 2024-06-08 | | |
| Tribulant--Newsletters | Improper Neutralization of Input During Web Page Generation (XSS or 'Cross-site Scripting') vulnerability in Tribulant Newsletters allows Reflected XSS.This issue affects Newsletters: from n/a through 4.9.5. | 2024-06-08 | | |
| unitecms--Unlimited Elements For Elementor (Free Widgets, Addons, Templates) | The Unlimited Elements For Elementor (Free Widgets, Addons, Templates) plugin for WordPress is vulnerable to blind SQL Injection via the 'data[addonID]' parameter in all versions up to, and including, 1.5.109 due to insufficient escaping on the user supplied parameter and lack of sufficient preparation on the existing SQL query. This makes it possible for authenticated attackers, with Contributor-level access and above, to append additional SQL queries into already existing queries that can be used to extract sensitive information from the database. | 2024-06-06 | | |
| Unlimited Elements--Unlimited Elements For Elementor (Free Widgets, Addons, Templates) | Unrestricted Upload of File with Dangerous Type vulnerability in Unlimited Elements Unlimited Elements For Elementor (Free Widgets, Addons, Templates) allows Code Injection.This issue affects Unlimited Elements For Elementor (Free Widgets, Addons, Templates): from n/a through 1.5.66. | 2024-06-04 | | |
| userproplugin -- userpro | Improper Privilege Management vulnerability in DeluxeThemes Userpro allows Privilege Escalation.This issue affects Userpro: from n/a through 5.1.8. | 2024-06-04 | | |
| vanyukov--Market Exporter | The Market Exporter plugin for WordPress is vulnerable to unauthorized loss of data due to a missing capability check on the 'remove_files' function in all versions up to, and including, 2.0.19. This makes it possible for authenticated attackers, with Subscriber-level access and above, to use path traversal to delete arbitrary files on the server. | 2024-06-07 | | |
| viz-rs--nano-id | nano-id is a unique string ID generator for Rust. Affected versions of the nano-id crate incorrectly generated IDs using a reduced character set in the `nano_id::base62` and `nano_id::base58` functions. Specifically, the `base62` function used a character set of 32 symbols instead of the intended 62 symbols, and the `base58` function used a character set of 16 symbols instead of the intended 58 symbols. Additionally, the `nano_id::gen` macro is also affected when a custom character set that is not a power of 2 in size is specified. It should be noted that `nano_id::base64` is not affected by this vulnerability. This can result in a significant reduction in entropy, making the generated IDs predictable and vulnerable to brute-force attacks when the IDs are used in security-sensitive contexts such as session tokens or unique identifiers. The vulnerability is fixed in 0.4.0. | 2024-06-04 | | |
| Wow-Company--Easy Digital Downloads Recent Purchases | Improper Control of Filename for Include/Require Statement in PHP Program ('PHP Remote File Inclusion') vulnerability in Wow-Company Easy Digital Downloads - Recent Purchases allows PHP Remote File Inclusion.This issue affects Easy Digital Downloads - Recent Purchases: from n/a through 1.0.2. | 2024-06-04 | | |
| wpase--Admin and Site Enhancements (ASE) | Improper Authentication vulnerability in wpase Admin and Site Enhancements (ASE) allows Accessing Functionality Not Properly Constrained by ACLs.This issue affects Admin and Site Enhancements (ASE): from n/a through 5.7.1. | 2024-06-04 | | |
| wpdevart--Responsive Image Gallery, Gallery Album | Improper Neutralization of Special Elements used in an SQL Command ('SQL Injection') vulnerability in wpdevart Responsive Image Gallery, Gallery Album.This issue affects Responsive Image Gallery, Gallery Album: from n/a through 2.0.3. | 2024-06-08 | | |
| WPMobile.App--WPMobile.App | Improper Neutralization of Input During Web Page Generation (XSS or 'Cross-site Scripting') vulnerability in WPMobile.App allows Reflected XSS.This issue affects WPMobile.App: from n/a through 11.41. | 2024-06-08 | | |
| wshberlin--Startklar Elementor Addons | The Startklar Elementor Addons plugin for WordPress is vulnerable to Directory Traversal in all versions up to, and including, 1.7.15 via the 'dropzone_hash' parameter. This makes it possible for unauthenticated attackers to copy the contents of arbitrary files on the server, which can contain sensitive information, and to delete arbitrary directories, including the root WordPress directory. | 2024-06-06 | | |
| XforWooCommerce--XforWooCommerce | Improper Limitation of a Pathname to a Restricted Directory ('Path Traversal') vulnerability in XforWooCommerce allows PHP Local File Inclusion.This issue affects XforWooCommerce: from n/a through 2.0.2. | 2024-06-04 | | |
| xootix--Login/Signup Popup ( Inline Form + Woocommerce ) | The Login/Signup Popup ( Inline Form + Woocommerce ) plugin for WordPress is vulnerable to unauthorized modification of data due to a missing capability check on the 'import_settings' function in versions 2.7.1 to 2.7.2. This makes it possible for authenticated attackers, with Subscriber-level access and above, to change arbitrary options on affected sites. This can be used to enable new user registration and set the default role for new users to Administrator. | 2024-06-06 | | |
| Yannick Lefebvre--Link Library | Improper Neutralization of Input During Web Page Generation (XSS or 'Cross-site Scripting') vulnerability in Yannick Lefebvre Link Library link-library allows Reflected XSS.This issue affects Link Library: from n/a through 7.6.3. | 2024-06-08 | | |
| YdataAI--ydata-profiling | Deserialization of untrusted data can occur in versions 3.7.0 or newer of Ydata's ydata-profiling open-source library, enabling a malicously crafted report to run arbitrary code on an end user's system when loaded. | 2024-06-04 | | |
| YdataAI--ydata-profiling | A cross-site scripting (XSS) vulnerability in versions 3.7.0 or newer of Ydata's ydata-profiling open-source library allows for payloads to be run when a maliocusly crafted report is viewed in the browser. | 2024-06-04 | | |
| YdataAI--ydata-profiling | Deseriliazation of untrusted data can occur in versions 3.7.0 or newer of Ydata's ydata-profiling open-source library, enabling a maliciously crafted dataset to run arbitrary code on an end user's system when loaded. | 2024-06-04 | |
Back to top
Medium Vulnerabilities
| Primary Vendor -- Product | Description | Published | CVSS Score | Source & Patch Info |
|---|---|---|---|---|
| 10up--ElasticPress | Cross-Site Request Forgery (CSRF) vulnerability in 10up ElasticPress.This issue affects ElasticPress: from n/a through 5.1.0. | 2024-06-08 | | |
| 10up--Restricted Site Access | Authentication Bypass by Spoofing vulnerability in 10up Restricted Site Access allows Accessing Functionality Not Properly Constrained by ACLs.This issue affects Restricted Site Access: from n/a through 7.4.1. | 2024-06-04 | | |
| 10Web Form Builder Team--Form Maker by 10Web | Improper Restriction of Excessive Authentication Attempts vulnerability in 10Web Form Builder Team Form Maker by 10Web allows Functionality Bypass.This issue affects Form Maker by 10Web: from n/a through 1.15.20. | 2024-06-04 | | |
| 10web--Photo Gallery by 10Web Mobile-Friendly Image Gallery | The Photo Gallery by 10Web - Mobile-Friendly Image Gallery plugin for WordPress is vulnerable to Stored Cross-Site Scripting via the 'svg' parameter in all versions up to, and including, 1.8.23 due to insufficient input sanitization and output escaping. This makes it possible for authenticated attackers to inject arbitrary web scripts in pages that will execute whenever a user accesses an injected page. By default, this can only be exploited by administrators, but the ability to use and configure Photo Gallery can be extended to contributors on pro versions of the plugin. | 2024-06-07 | | |
| 10web--Photo Gallery by 10Web Mobile-Friendly Image Gallery | The Photo Gallery by 10Web - Mobile-Friendly Image Gallery plugin for WordPress is vulnerable to Path Traversal in all versions up to, and including, 1.8.23 via the esc_dir function. This makes it possible for authenticated attackers to cut and paste (copy) the contents of arbitrary files on the server, which can contain sensitive information, and to cut (delete) arbitrary directories, including the root WordPress directory. By default this can be exploited by administrators only. In the premium version of the plugin, administrators can give gallery edit permissions to lower level users, which might make this exploitable by users as low as contributors. | 2024-06-07 | | |
| A WP Life--Contact Form Widget | Exposure of Sensitive Information to an Unauthorized Actor vulnerability in A WP Life Contact Form Widget.This issue affects Contact Form Widget: from n/a through 1.3.9. | 2024-06-03 | | |
| AccessAlly--PopupAlly | Improper Neutralization of Input During Web Page Generation (XSS or 'Cross-site Scripting') vulnerability in AccessAlly PopupAlly allows Stored XSS.This issue affects PopupAlly: from n/a through 2.1.1. | 2024-06-03 | | |
| adamskaat--Countdown, Coming Soon, Maintenance Countdown & Clock | The Countdown, Coming Soon, Maintenance - Countdown & Clock plugin for WordPress is vulnerable to unauthorized access due to a missing capability check on the conditionsRow and switchCountdown functions in all versions up to, and including, 2.7.8. This makes it possible for authenticated attackers, with subscriber-level access and above, to inject PHP Objects and modify the status of countdowns. | 2024-06-06 | | |
| Analytify--Analytify | Cross-Site Request Forgery (CSRF) vulnerability in Analytify.This issue affects Analytify: from n/a through 5.2.3. | 2024-06-08 | | |
| apollo13themes--Rife Free | Improper Neutralization of Input During Web Page Generation (XSS or 'Cross-site Scripting') vulnerability in apollo13themes Rife Free allows Stored XSS.This issue affects Rife Free: from n/a through 2.4.19. | 2024-06-08 | | |
| argoproj--argo-cd | Argo CD is a declarative, GitOps continuous delivery tool for Kubernetes. The vulnerability allows unauthorized access to the sensitive settings exposed by /api/v1/settings endpoint without authentication. All sensitive settings are hidden except passwordPattern. This vulnerability is fixed in 2.11.3, 2.10.12, and 2.9.17. | 2024-06-06 | | |
| argoproj--argo-cd | Argo CD is a declarative, GitOps continuous delivery tool for Kubernetes. It's possible for authenticated users to enumerate clusters by name by inspecting error messages. It's also possible to enumerate the names of projects with project-scoped clusters if you know the names of the clusters. This vulnerability is fixed in 2.11.3, 2.10.12, and 2.9.17. | 2024-06-06 | | |
| ARI Soft--ARI Stream Quiz | Improper Neutralization of Script-Related HTML Tags in a Web Page (Basic XSS) vulnerability in ARI Soft ARI Stream Quiz allows Code Injection.This issue affects ARI Stream Quiz: from n/a through 1.3.2. | 2024-06-04 | | |
| artbees--SellKit Funnel builder and checkout optimizer for WooCommerce to sell more, faster | The SellKit - Funnel builder and checkout optimizer for WooCommerce to sell more, faster plugin for WordPress is vulnerable to Stored Cross-Site Scripting via the 'id' parameter in all versions up to, and including, 1.9.8 due to insufficient input sanitization and output escaping. This makes it possible for authenticated attackers, with contributor-level access and above, to inject arbitrary web scripts in pages that will execute whenever a user accesses an injected page. | 2024-06-06 | | |
| Automattic--ChaosTheory | Improper Neutralization of Input During Web Page Generation (XSS or 'Cross-site Scripting') vulnerability in Automattic ChaosTheory allows Stored XSS.This issue affects ChaosTheory: from n/a through 1.3. | 2024-06-03 | | |
| awordpresslife--Formula | The Formula theme for WordPress is vulnerable to Reflected Cross-Site Scripting via the 'id' parameter in the 'quality_customizer_notify_dismiss_action' AJAX action in all versions up to, and including, 0.5.1 due to insufficient input sanitization and output escaping. This makes it possible for unauthenticated attackers to inject arbitrary web scripts in pages that execute if they can successfully trick a user into performing an action such as clicking on a link. | 2024-06-08 | | |
| awordpresslife--Formula | The Formula theme for WordPress is vulnerable to Reflected Cross-Site Scripting via the 'id' parameter in the 'ti_customizer_notify_dismiss_recommended_plugins' AJAX action in all versions up to, and including, 0.5.1 due to insufficient input sanitization and output escaping. This makes it possible for unauthenticated attackers to inject arbitrary web scripts in pages that execute if they can successfully trick a user into performing an action such as clicking on a link. | 2024-06-08 | | |
| bdthemes--Prime Slider Addons For Elementor (Revolution of a slider, Hero Slider, Ecommerce Slider) | The Prime Slider - Addons For Elementor (Revolution of a slider, Hero Slider, Ecommerce Slider) plugin for WordPress is vulnerable to Stored Cross-Site Scripting via the 'id' attribute within the Pacific widget in all versions up to, and including, 3.14.7 due to insufficient input sanitization and output escaping. This makes it possible for authenticated attackers, with Contributor-level access and above, to inject arbitrary web scripts in pages that will execute whenever a user accesses an injected page. | 2024-06-07 | | |
| Benoit Mercusot--Simple Popup Manager | Improper Neutralization of Input During Web Page Generation (XSS or 'Cross-site Scripting') vulnerability in Benoit Mercusot Simple Popup Manager allows Stored XSS.This issue affects Simple Popup Manager: from n/a through 1.3.5. | 2024-06-03 | | |
| BetterAddons--Better Elementor Addons | Improper Limitation of a Pathname to a Restricted Directory ('Path Traversal') vulnerability in BetterAddons Better Elementor Addons allows PHP Local File Inclusion.This issue affects Better Elementor Addons: from n/a through 1.4.1. | 2024-06-04 | | |
| BeyondTrust--BeyondInsight | Prior to 23.2, it is possible to perform arbitrary Server-Side requests via HTTP-based connectors within BeyondInsight, resulting in a server-side request forgery vulnerability. | 2024-06-04 | | |
| BeyondTrust--BeyondInsight | Prior to 23.1, an information disclosure vulnerability exists within BeyondInsight which can allow an attacker to enumerate usernames. | 2024-06-04 | | |
| biplob018--Image Hover Effects for Elementor with Lightbox and Flipbox | The Image Hover Effects for Elementor with Lightbox and Flipbox plugin for WordPress is vulnerable to Stored Cross-Site Scripting via the '_id', 'oxi_addons_f_title_tag', and 'content_description_tag' parameters in all versions up to, and including, 3.0.2 due to insufficient input sanitization and output escaping. This makes it possible for authenticated attackers, with Contributor-level access and above, to inject arbitrary web scripts in pages that will execute whenever a user accesses an injected page. | 2024-06-06 | | |
| Born05--CraftCMS Plugin - Two-Factor Authentication | The CraftCMS plugin Two-Factor Authentication through 3.3.3 allows reuse of TOTP tokens multiple times within the validity period. | 2024-06-06 | | |
| Brainstorm Force--Spectra | Improper Restriction of Excessive Authentication Attempts vulnerability in Brainstorm Force Spectra allows Functionality Bypass.This issue affects Spectra: from n/a through 2.3.0. | 2024-06-03 | | |
| Brainstorm Force--Spectra | Improper Neutralization of Script-Related HTML Tags in a Web Page (Basic XSS) vulnerability in Brainstorm Force Spectra allows Code Injection.This issue affects Spectra: from n/a through 2.3.0. | 2024-06-03 | | |
| Brainstorm Force--Spectra | Improper Neutralization of Special Elements in Output Used by a Downstream Component ('Injection') vulnerability in Brainstorm Force Spectra allows Content Spoofing, Phishing.This issue affects Spectra: from n/a through 2.3.0. | 2024-06-03 | | |
| brainstormforce--Cards for Beaver Builder | The Cards for Beaver Builder plugin for WordPress is vulnerable to Stored Cross-Site Scripting via the plugin's Cards widget in all versions up to, and including, 1.1.3 due to insufficient input sanitization and output escaping on user supplied attributes. This makes it possible for authenticated attackers, with contributor-level access and above, to inject arbitrary web scripts in pages that will execute whenever a user accesses an injected page. | 2024-06-08 | | |
| brainstormforce--SureTriggers Connect All Your Plugins, Apps, Tools & Automate Everything! | The SureTriggers - Connect All Your Plugins, Apps, Tools & Automate Everything! plugin for WordPress is vulnerable to Stored Cross-Site Scripting via the plugin's Trigger Link shortcode in all versions up to, and including, 1.0.47 due to insufficient input sanitization and output escaping on user supplied attributes. This makes it possible for authenticated attackers, with contributor-level access and above, to inject arbitrary web scripts in pages that will execute whenever a user accesses an injected page. | 2024-06-04 | | |
| brizy -- brizy-page_builder | The Brizy - Page Builder plugin for WordPress is vulnerable to Stored Cross-Site Scripting via the form name values in all versions up to, and including, 2.4.43 due to insufficient input sanitization and output escaping. This makes it possible for unauthenticated attackers to inject arbitrary web scripts in pages that will execute whenever a user accesses an injected page. | 2024-06-05 | | |
| brizy -- brizy-page_builder | The Brizy - Page Builder plugin for WordPress is vulnerable to Stored Cross-Site Scripting via the plugin's Custom Attributes for blocks in all versions up to, and including, 2.4.43 due to insufficient input sanitization and output escaping. This makes it possible for authenticated attackers with contributor-level and above permissions to inject arbitrary web scripts in pages that will execute whenever a user accesses an injected page. | 2024-06-05 | | |
| brizy -- brizy-page_builder | The Brizy - Page Builder plugin for WordPress is vulnerable to Stored Cross-Site Scripting via post content in all versions up to, and including, 2.4.41 due to insufficient input sanitization performed only on the client side and insufficient output escaping. This makes it possible for authenticated attackers, with contributor access and above, to inject arbitrary web scripts in pages that will execute whenever a user accesses an injected page. | 2024-06-05 | | |
| brizy -- brizy-page_builder | The Brizy - Page Builder plugin for WordPress is vulnerable to Stored Cross-Site Scripting via the 'Link To' field of multiple widgets in all versions up to, and including, 2.4.43 due to insufficient input sanitization and output escaping on user supplied attributes. This makes it possible for authenticated attackers, with contributor-level access and above, to inject arbitrary web scripts in pages that will execute whenever a user accesses an injected page. | 2024-06-05 | | |
| Bryan Hadaway--Site Favicon | Improper Neutralization of Input During Web Page Generation (XSS or 'Cross-site Scripting') vulnerability in Bryan Hadaway Site Favicon allows Stored XSS.This issue affects Site Favicon: from n/a through 0.2. | 2024-06-03 | | |
| Canonical Ltd.--Netplan | netplan leaks the private key of wireguard to local users. A security fix will be released soon. | 2024-06-07 | | |
| cartpauj--Cartpauj Register Captcha | : Improper Control of Interaction Frequency vulnerability in cartpauj Cartpauj Register Captcha allows Functionality Misuse.This issue affects Cartpauj Register Captcha: from n/a through 1.0.02. | 2024-06-04 | | |
| CeiKay--Tooltip CK | Improper Neutralization of Input During Web Page Generation (XSS or 'Cross-site Scripting') vulnerability in CeiKay Tooltip CK tooltip-ck allows Stored XSS.This issue affects Tooltip CK: from n/a through 2.2.15. | 2024-06-08 | | |
| Ciprian Popescu--Block for Font Awesome | Improper Neutralization of Input During Web Page Generation (XSS or 'Cross-site Scripting') vulnerability in Ciprian Popescu Block for Font Awesome allows Stored XSS.This issue affects Block for Font Awesome: from n/a through 1.4.4. | 2024-06-08 | | |
| Cisco--Cisco Unified Contact Center Enterprise | A vulnerability in the web-based management interface of Cisco Finesse could allow an unauthenticated, remote attacker to conduct a stored XSS attack by exploiting an RFI vulnerability. This vulnerability is due to insufficient validation of user-supplied input for specific HTTP requests that are sent to an affected device. An attacker could exploit this vulnerability by persuading a user to click a crafted link. A successful exploit could allow the attacker to execute arbitrary script code in the context of the affected interface or access sensitive information on the affected device. | 2024-06-05 | | |
| claudiosanches--Claudio Sanches Checkout Cielo for WooCommerce | The Claudio Sanches - Checkout Cielo for WooCommerce plugin for WordPress is vulnerable to unauthorized modification of data due to insufficient payment validation in the update_order_status() function in all versions up to, and including, 1.1.0. This makes it possible for unauthenticated attackers to update the status of orders to paid bypassing payment. | 2024-06-04 | | |
| Codection--Import and export users and customers | Missing Authorization vulnerability in Codection Import and export users and customers.This issue affects Import and export users and customers: from n/a through 1.24.6. | 2024-06-08 | | |
| codeless -- cowidgets_-_elementor | Improper Neutralization of Input During Web Page Generation (XSS or 'Cross-site Scripting') vulnerability in Codeless Cowidgets - Elementor Addons allows Stored XSS.This issue affects Cowidgets - Elementor Addons: from n/a through 1.1.1. | 2024-06-04 | | |
| codelessthemes--Cowidgets Elementor Addons | The Cowidgets - Elementor Addons plugin for WordPress is vulnerable to Stored Cross-Site Scripting via the 'heading_tag' parameter in all versions up to, and including, 1.1.1 due to insufficient input sanitization and output escaping. This makes it possible for authenticated attackers, with contributor-level access and above, to inject arbitrary web scripts in pages that will execute whenever a user accesses an injected page. | 2024-06-04 | | |
| codename065--Download Manager | The Download Manager plugin for WordPress is vulnerable to Stored Cross-Site Scripting via the plugin's 'wpdm_modal_login_form' shortcode in all versions up to, and including, 3.2.93 due to insufficient input sanitization and output escaping on user supplied attributes. This makes it possible for authenticated attackers, with contributor-level access and above, to inject arbitrary web scripts in pages that will execute whenever a user accesses an injected page. | 2024-06-05 | | |
| CodePeople, paypaldev--CP Contact Form with Paypal | Missing Authorization vulnerability in CodePeople, paypaldev CP Contact Form with Paypal allows Functionality Misuse.This issue affects CP Contact Form with Paypal: from n/a through 1.3.34. | 2024-06-03 | | |
| CodePeople--Calculated Fields Form | Missing Authorization vulnerability in CodePeople Calculated Fields Form allows Functionality Misuse.This issue affects Calculated Fields Form: from n/a through 1.1.120. | 2024-06-03 | | |
| CodePeople--Contact Form Email | Improper Restriction of Excessive Authentication Attempts vulnerability in CodePeople Contact Form Email allows Functionality Bypass.This issue affects Contact Form Email: from n/a through 1.3.41. | 2024-06-04 | | |
| CodePeople--Contact Form Email | Missing Authorization vulnerability in CodePeople Contact Form Email allows Functionality Misuse.This issue affects Contact Form Email: from n/a through 1.3.31. | 2024-06-04 | | |
| CodePeople--CP Multi View Event Calendar | Missing Authorization vulnerability in CodePeople CP Multi View Event Calendar allows Functionality Misuse.This issue affects CP Multi View Event Calendar: from n/a through 1.4.10. | 2024-06-03 | | |
| CodePeople--Search in Place | Missing Authorization vulnerability in CodePeople Search in Place allows Functionality Misuse.This issue affects Search in Place: from n/a through 1.0.104. | 2024-06-03 | | |
| Creative Motion, Will Bontrager Software, LLC--Woody ad snippets | Improper Neutralization of Input During Web Page Generation (XSS or 'Cross-site Scripting') vulnerability in Creative Motion, Will Bontrager Software, LLC Woody ad snippets allows Stored XSS.This issue affects Woody ad snippets: from n/a through 2.4.10. | 2024-06-08 | | |
| CreativeThemes--Blocksy Companion | Server-Side Request Forgery (SSRF) vulnerability in CreativeThemes Blocksy Companion.This issue affects Blocksy Companion: from n/a through 2.0.42. | 2024-06-03 | | |
| creativethemeshq--Blocksy | The Blocksy theme for WordPress is vulnerable to Reflected Cross-Site Scripting via the custom_url parameter in all versions up to, and including, 2.0.50 due to insufficient input sanitization and output escaping. This makes it possible for unauthenticated attackers to inject arbitrary web scripts in pages that execute if they can successfully trick a user into performing an action such as clicking on a link. | 2024-06-05 | | |
| CRM Perks.--Integration for Contact Form 7 and Constant Contact | Cross-Site Request Forgery (CSRF) vulnerability in CRM Perks. Integration for Contact Form 7 and Constant Contact.This issue affects Integration for Contact Form 7 and Constant Contact: from n/a through 1.1.5. | 2024-06-03 | | |
| cyberchimps--Responsive Addons Starter Templates, Advanced Features and Customizer Settings for Responsive Theme. | The Responsive Addons - Starter Templates, Advanced Features and Customizer Settings for Responsive Theme. plugin for WordPress is vulnerable to Stored Cross-Site Scripting via the plugin's file uploader in all versions up to, and including, 3.0.5 due to insufficient input sanitization and output escaping. This makes it possible for authenticated attackers, with Author-level access and above, to inject arbitrary web scripts in pages that will execute whenever a user accesses an injected page. | 2024-06-05 | | |
| CyberChimps--Responsive | Improper Neutralization of Input During Web Page Generation (XSS or 'Cross-site Scripting') vulnerability in CyberChimps Responsive allows Stored XSS.This issue affects Responsive: from n/a through 5.0.3. | 2024-06-04 | | |
| cyclonetheme--Elegant Blocks | Improper Neutralization of Input During Web Page Generation (XSS or 'Cross-site Scripting') vulnerability in cyclonetheme Elegant Blocks allows Stored XSS.This issue affects Elegant Blocks: from n/a through 1.7. | 2024-06-03 | | |
| dain--snappy | iq80 Snappy is a compression/decompression library. When uncompressing certain data, Snappy tries to read outside the bounds of the given byte arrays. Because Snappy uses the JDK class `sun.misc.Unsafe` to speed up memory access, no additional bounds checks are performed and this has similar security consequences as out-of-bounds access in C or C++, namely it can lead to non-deterministic behavior or crash the JVM. iq80 Snappy is not actively maintained anymore. As quick fix users can upgrade to version 0.5. | 2024-06-03 | | |
| Devnath verma--WP Captcha | Improper Restriction of Excessive Authentication Attempts vulnerability in Devnath verma WP Captcha allows Functionality Bypass.This issue affects WP Captcha: from n/a through 2.0.0. | 2024-06-04 | | |
| dextorlobo--Custom Dash | The Custom Dash plugin for WordPress is vulnerable to Stored Cross-Site Scripting via admin settings in all versions up to, and including, 1.0.2 due to insufficient input sanitization and output escaping. This makes it possible for authenticated attackers, with administrator-level permissions and above, to inject arbitrary web scripts in pages that will execute whenever a user accesses an injected page. This only affects multi-site installations and installations where unfiltered_html has been disabled. | 2024-06-06 | | |
| dfactory--Download Attachments | The Download Attachments plugin for WordPress is vulnerable to Stored Cross-Site Scripting via the plugin's 'download-attachments' shortcode in all versions up to, and including, 1.3 due to insufficient input sanitization and output escaping on user supplied attributes. This makes it possible for authenticated attackers, with contributor-level access and above, to inject arbitrary web scripts in pages that will execute whenever a user accesses an injected page. | 2024-06-04 | | |
| Dulldusk--PHP File Manager | Vulnerability in Dulldusk's PHP File Manager affecting version 1.7.8. This vulnerability consists of an XSS through the fm_current_dir parameter of index.php. An attacker could send a specially crafted JavaScript payload to an authenticated user and partially hijack their browser session. | 2024-06-06 | | |
| duongancol--Boostify Header Footer Builder for Elementor | The Boostify Header Footer Builder for Elementor plugin for WordPress is vulnerable to Stored Cross-Site Scripting via the 'size' parameter in all versions up to, and including, 1.3.2 due to insufficient input sanitization and output escaping. This makes it possible for authenticated attackers, with Contributor-level access and above, to inject arbitrary web scripts in pages that will execute whenever a user accesses an injected page. | 2024-06-05 | | |
| duongancol--Boostify Header Footer Builder for Elementor | The Boostify Header Footer Builder for Elementor plugin for WordPress is vulnerable to unauthorized modification of data due to a missing capability check on the create_bhf_post function in all versions up to, and including, 1.3.3. This makes it possible for authenticated attackers, with subscriber-level access and above, to create pages or posts with arbitrary content. | 2024-06-06 | | |
| El tiempo--Weather Widget Pro | Improper Neutralization of Input During Web Page Generation (XSS or 'Cross-site Scripting') vulnerability in El tiempo Weather Widget Pro allows Stored XSS.This issue affects Weather Widget Pro: from n/a through 1.1.40. | 2024-06-08 | | |
| elearningfreak -- insert_or_embed_articulate_content | The Insert or Embed Articulate Content into WordPress plugin through 4.3000000023 lacks validation of URLs when adding iframes, allowing attackers to inject an iFrame in the page and thus load arbitrary content from any page. | 2024-06-04 | | |
| EmailGPT--EmailGPT | The EmailGPT service contains a prompt injection vulnerability. The service uses an API service that allows a malicious user to inject a direct prompt and take over the service logic. Attackers can exploit the issue by forcing the AI service to leak the standard hard-coded system prompts and/or execute unwanted prompts. When engaging with EmailGPT by submitting a malicious prompt that requests harmful information, the system will respond by providing the requested data. This vulnerability can be exploited by any individual with access to the service. | 2024-06-05 | | |
| Enea Overclokk--Stellissimo Text Box | Improper Neutralization of Input During Web Page Generation (XSS or 'Cross-site Scripting') vulnerability in Enea Overclokk Stellissimo Text Box allows Stored XSS.This issue affects Stellissimo Text Box: from n/a through 1.1.4. | 2024-06-08 | | |
| envothemes--Envo Extra | The Envo Extra plugin for WordPress is vulnerable to Stored Cross-Site Scripting via the 'button_css_id' parameter within the Button widget in all versions up to, and including, 1.8.23 due to insufficient input sanitization and output escaping. This makes it possible for authenticated attackers, with Contributor-level access and above, to inject arbitrary web scripts in pages that will execute whenever a user accesses an injected page. | 2024-06-07 | | |
| envoyproxy--envoy | Envoy is a cloud-native, open source edge and service proxy. A theoretical request smuggling vulnerability exists through Envoy if a server can be tricked into adding an upgrade header into a response. Per RFC https://www.rfc-editor.org/rfc/rfc7230#section-6.7 a server sends 101 when switching protocols. Envoy incorrectly accepts a 200 response from a server when requesting a protocol upgrade, but 200 does not indicate protocol switch. This opens up the possibility of request smuggling through Envoy if the server can be tricked into adding the upgrade header to the response. | 2024-06-04 | | |
| envoyproxy--envoy | Envoy is a cloud-native, open source edge and service proxy. A crash was observed in `EnvoyQuicServerStream::OnInitialHeadersComplete()` with following call stack. It is a use-after-free caused by QUICHE continuing push request headers after `StopReading()` being called on the stream. As after `StopReading()`, the HCM's `ActiveStream` might have already be destroyed and any up calls from QUICHE could potentially cause use after free. | 2024-06-04 | | |
| envoyproxy--envoy | Envoy is a cloud-native, open source edge and service proxy. There is a crash at `QuicheDataReader::PeekVarInt62Length()`. It is caused by integer underflow in the `QuicStreamSequencerBuffer::PeekRegion()` implementation. | 2024-06-04 | | |
| envoyproxy--envoy | Envoy is a cloud-native, open source edge and service proxy. There is a use-after-free in `HttpConnectionManager` (HCM) with `EnvoyQuicServerStream` that can crash Envoy. An attacker can exploit this vulnerability by sending a request without `FIN`, then a `RESET_STREAM` frame, and then after receiving the response, closing the connection. | 2024-06-04 | | |
| envoyproxy--envoy | Envoy is a cloud-native, open source edge and service proxy. Envoy exposed an out-of-memory (OOM) vector from the mirror response, since async HTTP client will buffer the response with an unbounded buffer. | 2024-06-04 | | |
| Essential Addons--Essential Addons for Elementor Pro | The Essential Addons for Elementor Pro plugin for WordPress is vulnerable to Stored Cross-Site Scripting via the 'eael_lightbox_open_btn_icon' parameter within the Lightbox & Modal widget in all versions up to, and including, 5.8.15 due to insufficient input sanitization and output escaping. This makes it possible for authenticated attackers, with Contributor-level access and above, to inject arbitrary web scripts in pages that will execute whenever a user accesses an injected page. | 2024-06-07 | | |
| evmos--evmos | Evmos is the Ethereum Virtual Machine (EVM) Hub on the Cosmos Network. Users are able to delegate tokens that have not yet been vested. This affects employees and grantees who have funds managed via `ClawbackVestingAccount`. This affects 18.1.0 and earlier. | 2024-06-06 | | |
| extendthemes--Colibri Page Builder | The Colibri Page Builder plugin for WordPress is vulnerable to Stored Cross-Site Scripting via the plugin's colibri_video_player shortcode in all versions up to, and including, 1.0.276 due to insufficient input sanitization and output escaping on user supplied attributes. This makes it possible for authenticated attackers, with contributor-level access and above, to inject arbitrary web scripts in pages that will execute whenever a user accesses an injected page. | 2024-06-07 | | |
| extendthemes--Colibri Page Builder | The Colibri Page Builder plugin for WordPress is vulnerable to Stored Cross-Site Scripting via the plugin's shortcode(s) in all versions up to, and including, 1.0.276 due to insufficient input sanitization and output escaping on user supplied attributes. This makes it possible for authenticated attackers, with contributor-level access and above, to inject arbitrary web scripts in pages that will execute whenever a user accesses an injected page. | 2024-06-06 | | |
| Fahad Mahmood--WP Docs | Improper Neutralization of Input During Web Page Generation (XSS or 'Cross-site Scripting') vulnerability in Fahad Mahmood WP Docs allows Stored XSS.This issue affects WP Docs: from n/a through 2.1.3. | 2024-06-08 | | |
| Fastly--Fastly | Missing Authorization vulnerability in Fastly.This issue affects Fastly: from n/a through 1.2.25. | 2024-06-03 | | |
| FeedbackWP--Rate my Post WP Rating System | Authentication Bypass by Spoofing vulnerability in FeedbackWP Rate my Post - WP Rating System allows Accessing Functionality Not Properly Constrained by ACLs.This issue affects Rate my Post - WP Rating System: from n/a through 3.4.2. | 2024-06-04 | | |
| flowdee--EasyAzon Amazon Associates Affiliate Plugin | The EasyAzon - Amazon Associates Affiliate Plugin plugin for WordPress is vulnerable to Reflected Cross-Site Scripting via the 'easyazon-cloaking-locale' parameter in all versions up to, and including, 5.1.0 due to insufficient input sanitization and output escaping. This makes it possible for unauthenticated attackers to inject arbitrary web scripts in pages that execute if they can successfully trick a user into performing an action such as clicking on a link. | 2024-06-06 | | |
| Forge12 Interactive GmbH--Captcha/Honeypot for Contact Form 7 | Improper Restriction of Excessive Authentication Attempts vulnerability in Forge12 Interactive GmbH Captcha/Honeypot for Contact Form 7 allows Functionality Bypass.This issue affects Captcha/Honeypot for Contact Form 7: from n/a through 1.11.3. | 2024-06-04 | | |
| Fortinet--FortiAuthenticator | A URL redirection to untrusted site ('open redirect') in Fortinet FortiAuthenticator version 6.6.0, version 6.5.3 and below, version 6.4.9 and below may allow an attacker to to redirect users to an arbitrary website via a crafted URL. | 2024-06-03 | | |
| Fortinet--FortiPortal | A client-side enforcement of server-side security in Fortinet FortiPortal version 6.0.0 through 6.0.14 allows attacker to improper access control via crafted HTTP requests. | 2024-06-03 | | |
| Fortinet--FortiSOAR | An improper removal of sensitive information before storage or transfer vulnerability [CWE-212] in FortiSOAR version 7.3.0, version 7.2.2 and below, version 7.0.3 and below may allow an authenticated low privileged user to read Connector passwords in plain-text via HTTP responses. | 2024-06-03 | | |
| Fortinet--FortiWebManager | An improper authorization in Fortinet FortiWebManager version 7.2.0 and 7.0.0 through 7.0.4 and 6.3.0 and 6.2.3 through 6.2.4 and 6.0.2 allows attacker to execute unauthorized code or commands via HTTP requests or CLI. | 2024-06-05 | | |
| Fortinet--FortiWeb | An exposure of sensitive information to an unauthorized actor vulnerability [CWE-200] in FortiWeb version 7.4.0, version 7.2.4 and below, version 7.0.8 and below, 6.3 all versions may allow an authenticated attacker to read password hashes of other administrators via CLI commands. | 2024-06-03 | | |
| Fortinet--FortiWeb | Multiple improper authorization vulnerabilities [CWE-285] in FortiWeb version 7.4.2 and below, version 7.2.7 and below, version 7.0.10 and below, version 6.4.3 and below, version 6.3.23 and below may allow an authenticated attacker to perform unauthorized ADOM operations via crafted requests. | 2024-06-03 | | |
| freephp-1--Nafeza Prayer Time | The Nafeza Prayer Time plugin for WordPress is vulnerable to Stored Cross-Site Scripting via admin settings in all versions up to, and including, 1.2.9 due to insufficient input sanitization and output escaping. This makes it possible for authenticated attackers, with administrator-level permissions and above, to inject arbitrary web scripts in pages that will execute whenever a user accesses an injected page. This only affects multi-site installations and installations where unfiltered_html has been disabled. | 2024-06-04 | | |
| g5theme--Essential Real Estate | The Essential Real Estate plugin for WordPress is vulnerable to Stored Cross-Site Scripting via the plugin's 'ere_property_map' shortcode in all versions up to, and including, 4.4.2 due to insufficient input sanitization and output escaping on user supplied attributes. This makes it possible for authenticated attackers, with contributor-level access and above, to inject arbitrary web scripts in pages that will execute whenever a user accesses an injected page. | 2024-06-04 | | |
| g5theme--Essential Real Estate | The Essential Real Estate plugin for WordPress is vulnerable to unauthorized loss of data due to insufficient validation on the remove_property_attachment_ajax() function in all versions up to, and including, 4.4.2. This makes it possible for authenticated attackers, with subscriber-level access and above, to delete arbitrary attachments. | 2024-06-04 | | |
| GeneratePress--GP Premium | The GP Premium plugin for WordPress is vulnerable to Reflected Cross-Site Scripting via the message parameter in all versions up to, and including, 2.4.0 due to insufficient input sanitization and output escaping. This makes it possible for unauthenticated attackers to inject arbitrary web scripts in pages that execute if they can successfully trick a user into performing an action such as clicking on a link. | 2024-06-05 | | |
| getbrave -- brave | Improper Neutralization of Input During Web Page Generation (XSS or 'Cross-site Scripting') vulnerability in Brave Brave Popup Builder allows Stored XSS.This issue affects Brave Popup Builder: from n/a through 0.6.8. | 2024-06-04 | | |
| getformwork--formwork | Formwork is a flat file-based Content Management System (CMS). An attackers (requires administrator privilege) to execute arbitrary web scripts by modifying site options via /panel/options/site. This type of attack is suitable for persistence, affecting visitors across all pages (except the dashboard). This vulnerability is fixed in 1.13.1. | 2024-06-07 | | |
| gn_themes--WP Shortcodes Plugin Shortcodes Ultimate | The WP Shortcodes Plugin - Shortcodes Ultimate plugin for WordPress is vulnerable to Stored Cross-Site Scripting via the plugin's su_lightbox shortcode in all versions up to, and including, 7.1.6 due to insufficient input sanitization and output escaping on user supplied attributes. This makes it possible for authenticated attackers, with contributor-level access and above, to inject arbitrary web scripts in pages that will execute whenever a user accesses an injected page. | 2024-06-05 | | |
| GregRoss--Just Writing Statistics | Improper Neutralization of Input During Web Page Generation (XSS or 'Cross-site Scripting') vulnerability in GregRoss Just Writing Statistics allows Stored XSS.This issue affects Just Writing Statistics: from n/a through 4.5. | 2024-06-03 | | |
| gVectors Team--wpDiscuz | Improper Neutralization of Input During Web Page Generation (XSS or 'Cross-site Scripting') vulnerability in gVectors Team wpDiscuz allows Stored XSS.This issue affects wpDiscuz: from n/a through 7.6.18. | 2024-06-08 | | |
| gVectors Team--wpDiscuz | Improper Neutralization of Script-Related HTML Tags in a Web Page (Basic XSS) vulnerability in gVectors Team wpDiscuz allows Code Injection.This issue affects wpDiscuz: from n/a through 7.6.10. | 2024-06-04 | | |
| Hans van Eijsden,niwreg--ImageMagick Sharpen Resized Images | Improper Neutralization of Input During Web Page Generation (XSS or 'Cross-site Scripting') vulnerability in Hans van Eijsden,niwreg ImageMagick Sharpen Resized Images allows Stored XSS.This issue affects ImageMagick Sharpen Resized Images: from n/a through 1.1.7. | 2024-06-03 | | |
| HasThemes--HT Feed | Improper Neutralization of Input During Web Page Generation (XSS or 'Cross-site Scripting') vulnerability in HasThemes HT Feed allows Stored XSS.This issue affects HT Feed: from n/a through 1.2.8. | 2024-06-08 | | |
| HasThemes--ShopLentor | Improper Neutralization of Input During Web Page Generation (XSS or 'Cross-site Scripting') vulnerability in HasThemes ShopLentor allows Stored XSS.This issue affects ShopLentor: from n/a through 2.8.7. | 2024-06-03 | | |
| HCL Software--Connections Docs | HCL Connections Docs is vulnerable to a cross-site scripting attack where an attacker may leverage this issue to execute arbitrary code. This may lead to credentials disclosure and possibly launch additional attacks. | 2024-06-08 | | |
| horearadu--Materialis Companion | The Materialis Companion plugin for WordPress is vulnerable to Stored Cross-Site Scripting via the plugin's materialis_contact_form shortcode in all versions up to, and including, 1.3.41 due to insufficient input sanitization and output escaping on user supplied attributes. This makes it possible for authenticated attackers, with contributor-level access and above, to inject arbitrary web scripts in pages that will execute whenever a user accesses an injected page. | 2024-06-06 | | |
| horearadu--One Page Express Companion | The One Page Express Companion plugin for WordPress is vulnerable to Stored Cross-Site Scripting via the plugin's one_page_express_contact_form shortcode in all versions up to, and including, 1.6.37 due to insufficient input sanitization and output escaping on user supplied attributes. This makes it possible for authenticated attackers, with contributor-level access and above, to inject arbitrary web scripts in pages that will execute whenever a user accesses an injected page. | 2024-06-07 | | |
| ibabar--WordPress prettyPhoto | The WordPress prettyPhoto plugin for WordPress is vulnerable to Stored Cross-Site Scripting via the 'url' parameter in all versions up to, and including, 1.2.3 due to insufficient input sanitization and output escaping. This makes it possible for authenticated attackers, with Contributor-level access and above, to inject arbitrary web scripts in pages that will execute whenever a user accesses an injected page. | 2024-06-06 | | |
| IBM--i | IBM i 7.2, 7.3, 7.4, and 7.5 Service Tools Server (SST) is vulnerable to SST user enumeration by a remote attacker. This vulnerability can be used by a malicious actor to gather information about SST users that can be targeted in further attacks. IBM X-Force ID: 287538. | 2024-06-07 | | |
| IBM--System Storage DS8900F | IBM System Storage DS8900F 89.22.19.0, 89.30.68.0, 89.32.40.0, 89.33.48.0, 89.40.83.0, and 89.40.93.0 could allow a remote user to create an LDAP connection with a valid username and empty password to establish an anonymous connection. IBM X-Force ID: 279518. | 2024-06-06 | | |
| Icegram--Icegram | Missing Authorization vulnerability in Icegram.This issue affects Icegram: from n/a through 3.1.21. | 2024-06-08 | | |
| IdoPesok--zsa | zsa is a library for building typesafe server actions in Next.js. All users are impacted. The zsa application transfers the parse error stack from the server to the client in production build mode. This can potentially reveal sensitive information about the server environment, such as the machine username and directory paths. An attacker could exploit this vulnerability to gain unauthorized access to sensitive server information. This information could be used to plan further attacks or gain a deeper understanding of the server infrastructure. This has been patched on `0.3.3`. | 2024-06-07 | | |
| ILLID--Advanced Woo Labels | Improper Neutralization of Input During Web Page Generation (XSS or 'Cross-site Scripting') vulnerability in ILLID Advanced Woo Labels allows Cross-Site Scripting (XSS).This issue affects Advanced Woo Labels: from n/a through 1.93. | 2024-06-08 | | |
| IP2Location--Download IP2Location Country Blocker | Authentication Bypass by Spoofing vulnerability in IP2Location Download IP2Location Country Blocker allows Accessing Functionality Not Properly Constrained by ACLs.This issue affects Download IP2Location Country Blocker: from n/a through 2.29.1. | 2024-06-04 | | |
| ishanverma--Authorize.net Payment Gateway For WooCommerce | The Authorize.net Payment Gateway For WooCommerce plugin for WordPress is vulnerable to payment bypass in all versions up to, and including, 8.0. This is due to the plugin not properly verifying the authenticity of the request that updates a orders payment status. This makes it possible for unauthenticated attackers to update order payment statuses to paid bypassing any payment. | 2024-06-04 | | |
| itsourcecode--Bakery Online Ordering System | A vulnerability was found in itsourcecode Bakery Online Ordering System 1.0. It has been declared as critical. Affected by this vulnerability is an unknown functionality of the file index.php. The manipulation of the argument txtsearch leads to sql injection. The attack can be launched remotely. The exploit has been disclosed to the public and may be used. The associated identifier of this vulnerability is VDB-267091. | 2024-06-04 | | |
| itsourcecode--Bakery Online Ordering System | A vulnerability was found in itsourcecode Bakery Online Ordering System 1.0. It has been rated as critical. Affected by this issue is some unknown functionality of the file report/index.php. The manipulation of the argument procduct leads to sql injection. The attack may be launched remotely. The exploit has been disclosed to the public and may be used. The identifier of this vulnerability is VDB-267092. | 2024-06-05 | | |
| itsourcecode--Online Discussion Forum | A vulnerability classified as critical has been found in itsourcecode Online Discussion Forum 1.0. Affected is an unknown function of the file /members/poster.php. The manipulation of the argument image leads to unrestricted upload. It is possible to launch the attack remotely. The exploit has been disclosed to the public and may be used. The identifier of this vulnerability is VDB-267408. | 2024-06-07 | | |
| J.N. Breetvelt a.k.a. OpaJaap--WP Photo Album Plus | Exposure of Sensitive Information to an Unauthorized Actor vulnerability in J.N. Breetvelt a.K.A. OpaJaap WP Photo Album Plus allows Accessing Functionality Not Properly Constrained by ACLs.This issue affects WP Photo Album Plus: from n/a through 8.5.02.005. | 2024-06-04 | | |
| j0hnsmith--Testimonials Widget | The Testimonials Widget plugin for WordPress is vulnerable to Stored Cross-Site Scripting via the plugin's testimonials shortcode in all versions up to, and including, 4.0.4 due to insufficient input sanitization and output escaping on user supplied attributes. This makes it possible for authenticated attackers, with contributor-level access and above, to inject arbitrary web scripts in pages that will execute whenever a user accesses an injected page. | 2024-06-06 | | |
| Jewel Theme--Master Addons for Elementor | Improper Neutralization of Input During Web Page Generation (XSS or 'Cross-site Scripting') vulnerability in Jewel Theme Master Addons for Elementor allows Stored XSS.This issue affects Master Addons for Elementor: from n/a through 2.0.5.9. | 2024-06-08 | | |
| Jewel Theme--Master Addons for Elementor | Improper Neutralization of Input During Web Page Generation (XSS or 'Cross-site Scripting') vulnerability in Jewel Theme Master Addons for Elementor allows Stored XSS.This issue affects Master Addons for Elementor: from n/a through 2.0.6.0. | 2024-06-08 | | |
| johnnash1975--Easy Social Like Box Popup Sidebar Widget | The Easy Social Like Box - Popup - Sidebar Widget plugin for WordPress is vulnerable to Stored Cross-Site Scripting via the plugin's 'cardoza_facebook_like_box' shortcode in all versions up to, and including, 4.0 due to insufficient input sanitization and output escaping on user supplied attributes. This makes it possible for authenticated attackers, with contributor-level access and above, to inject arbitrary web scripts in pages that will execute whenever a user accesses an injected page. | 2024-06-06 | | |
| JumpDEMAND Inc.--ActiveDEMAND | Cross-Site Request Forgery (CSRF) vulnerability in JumpDEMAND Inc. ActiveDEMAND.This issue affects ActiveDEMAND: from n/a through 0.2.43. | 2024-06-03 | | |
| Kharim Tomlinson--WP Next Post Navi | Improper Neutralization of Input During Web Page Generation (XSS or 'Cross-site Scripting') vulnerability in Kharim Tomlinson WP Next Post Navi allows Stored XSS.This issue affects WP Next Post Navi: from n/a through 1.8.3. | 2024-06-03 | | |
| Kognetiks--Kognetiks Chatbot for WordPress | Improper Neutralization of Input During Web Page Generation (XSS or 'Cross-site Scripting') vulnerability in Kognetiks Kognetiks Chatbot for WordPress allows Stored XSS.This issue affects Kognetiks Chatbot for WordPress: from n/a through 1.9.8. | 2024-06-08 | | |
| LabVantage--LIMS | A vulnerability classified as critical was found in LabVantage LIMS 2017. This vulnerability affects unknown code of the file /labvantage/rc?command=page&page=SampleList&_iframename=list of the component POST Request Handler. The manipulation of the argument param1 leads to sql injection. The attack can be initiated remotely. The exploit has been disclosed to the public and may be used. VDB-267454 is the identifier assigned to this vulnerability. NOTE: The vendor was contacted early about this disclosure but did not respond in any way. | 2024-06-08 | | |
| Lester GaMerZ Chan--WP-PostRatings | Improper Control of Interaction Frequency vulnerability in Lester 'GaMerZ' Chan WP-PostRatings allows Functionality Misuse.This issue affects WP-PostRatings: from n/a through 1.91. | 2024-06-04 | | |
| litonice13--Master Addons Free Widgets, Hover Effects, Toggle, Conditions, Animations for Elementor | The Master Addons - Free Widgets, Hover Effects, Toggle, Conditions, Animations for Elementor plugin for WordPress is vulnerable to unauthorized modification of data due to a missing capability check on the 'ma-template' REST API route in all versions up to, and including, 2.0.6.1. This makes it possible for unauthenticated attackers to create or modify existing Master Addons templates or make settings modifications related to these templates. | 2024-06-07 | | |
| Lukman Nakib--Debug Log Manger Tool | Insertion of Sensitive Information into Log File vulnerability in Lukman Nakib Debug Log - Manger Tool.This issue affects Debug Log - Manger Tool: from n/a through 1.4.5. | 2024-06-03 | | |
| MagniGenie--RestroPress | Improper Neutralization of Input During Web Page Generation (XSS or 'Cross-site Scripting') vulnerability in MagniGenie RestroPress allows Stored XSS.This issue affects RestroPress: from n/a through 3.1.2.1. | 2024-06-08 | | |
| Marketing Fire, LLC--Widget Options - Extended | Exposure of Sensitive Information to an Unauthorized Actor vulnerability in Marketing Fire, LLC Widget Options - Extended.This issue affects Widget Options - Extended: from n/a through 5.1.0. | 2024-06-08 | | |
| melapress--Admin Notices Manager | The Admin Notices Manager plugin for WordPress is vulnerable to unauthorized access of data due to a missing capability check on the handle_ajax_call() function in all versions up to, and including, 1.4.0. This makes it possible for authenticated attackers, with subscriber-level access and above, to retrieve a list of registered user emails. | 2024-06-04 | | |
| Menno Luitjes--Foyer | Improper Neutralization of Script-Related HTML Tags in a Web Page (Basic XSS) vulnerability in Menno Luitjes Foyer allows Code Injection.This issue affects Foyer: from n/a through 1.7.5. | 2024-06-04 | | |
| Mervin Praison--Praison SEO WordPress | Improper Neutralization of Input During Web Page Generation (XSS or 'Cross-site Scripting') vulnerability in Mervin Praison Praison SEO WordPress allows Stored XSS.This issue affects Praison SEO WordPress: from n/a through 4.0.15. | 2024-06-03 | | |
| metagauss--ProfileGrid User Profiles, Groups and Communities | The ProfileGrid - User Profiles, Groups and Communities plugin for WordPress is vulnerable to unauthorized modification of data due to a missing capability check on the pm_dismissible_notice and pm_wizard_update_group_icon functions in all versions up to, and including, 5.8.6. This makes it possible for authenticated attackers, with Subscriber-level access and above, to change arbitrary options to the value '1' or change group icons. | 2024-06-05 | | |
| Metagauss--RegistrationMagic | Authentication Bypass by Spoofing vulnerability in Metagauss RegistrationMagic allows Accessing Functionality Not Properly Constrained by ACLs.This issue affects RegistrationMagic: from n/a through 5.2.5.0. | 2024-06-04 | | |
| Metagauss--RegistrationMagic | Improper Control of Interaction Frequency vulnerability in Metagauss RegistrationMagic allows Functionality Misuse.This issue affects RegistrationMagic: from n/a through 5.2.5.0. | 2024-06-04 | | |
| miniorange--Malware Scanner | Authentication Bypass by Spoofing vulnerability in miniorange Malware Scanner allows Accessing Functionality Not Properly Constrained by ACLs.This issue affects Malware Scanner: from n/a through 4.7.1. | 2024-06-04 | | |
| MongoDB Inc--PyMongo | An out-of-bounds read in the 'bson' module of PyMongo 4.6.2 or earlier allows deserialization of malformed BSON provided by a Server to raise an exception which may contain arbitrary application memory. | 2024-06-05 | | |
| moveaddons--Move Addons for Elementor | Missing Authorization vulnerability in moveaddons Move Addons for Elementor.This issue affects Move Addons for Elementor: from n/a through 1.2.9. | 2024-06-04 | | |
| mpntod--Rotating Tweets (Twitter widget and shortcode) | The Rotating Tweets (Twitter widget and shortcode) plugin for WordPress is vulnerable to Stored Cross-Site Scripting via the plugin's' 'rotatingtweets' in all versions up to, and including, 1.9.10 due to insufficient input sanitization and output escaping on user supplied attributes. This makes it possible for authenticated attackers, with contributor-level access and above, to inject arbitrary web scripts in pages that will execute whenever a user accesses an injected page. | 2024-06-06 | | |
| N/A--Church Admin | Server-Side Request Forgery (SSRF) vulnerability in Church Admin.This issue affects Church Admin: from n/a through 4.3.6. | 2024-06-03 | | |
| N/A--KiviCare | Authorization Bypass Through User-Controlled Key vulnerability in KiviCare.This issue affects KiviCare: from n/a through 3.6.2. | 2024-06-08 | | |
| n/a--n/a | An issue was discovered in Samsung Mobile Processor Exynos 980, Exynos 850, Exynos 1280, Exynos 1380, and Exynos 1330. In the function slsi_nan_config_get_nl_params(), there is no input validation check on hal_req->num_config_discovery_attr coming from userspace, which can lead to a heap overwrite. | 2024-06-05 | | |
| n/a--n/a | An issue was discovered in Samsung Mobile Processor Exynos 980, Exynos 850, Exynos 1280, Exynos 1380, and Exynos 1330. In the function slsi_nan_followup_get_nl_params(), there is no input validation check on hal_req->service_specific_info_len coming from userspace, which can lead to a heap overwrite. | 2024-06-05 | | |
| n/a--n/a | An issue was discovered in Samsung Mobile Processor Exynos 980, Exynos 850, Exynos 1280, Exynos 1380, and Exynos 1330. In the function slsi_nan_config_get_nl_params(), there is no input validation check on disc_attr->infrastructure_ssid_len coming from userspace, which can lead to a heap overwrite. | 2024-06-05 | | |
| n/a--n/a | An issue was discovered in Samsung Mobile Processor Exynos 980, Exynos 850, Exynos 1280, Exynos 1380, and Exynos 1330. In the function slsi_nan_config_get_nl_params(), there is no input validation check on disc_attr->mesh_id_len coming from userspace, which can lead to a heap overwrite. | 2024-06-05 | | |
| n/a--n/a | An issue was discovered in Samsung Mobile Processor Exynos 980, Exynos 850, Exynos 1280, Exynos 1380, and Exynos 1330. In the function slsi_nan_publish_get_nl_params(), there is no input validation check on hal_req->service_specific_info_len coming from userspace, which can lead to a heap overwrite. | 2024-06-05 | | |
| n/a--n/a | An issue was discovered in Samsung Mobile Processor Exynos 980, Exynos 850, Exynos 1280, Exynos 1380, and Exynos 1330. In the function slsi_nan_followup_get_nl_params(), there is no input validation check on hal_req->sdea_service_specific_info_len coming from userspace, which can lead to a heap overwrite. | 2024-06-05 | | |
| n/a--n/a | An issue was discovered in Samsung Mobile Processor Exynos 980, Exynos 850, Exynos 1280, Exynos 1380, and Exynos 1330. In the function slsi_nan_subscribe_get_nl_params(), there is no input validation check on hal_req->rx_match_filter_len coming from userspace, which can lead to a heap overwrite. | 2024-06-05 | | |
| n/a--n/a | An issue was discovered in Samsung Mobile Processor Exynos 980, Exynos 850, Exynos 1280, Exynos 1380, and Exynos 1330. In the function slsi_nan_get_security_info_nl(), there is no input validation check on sec_info->key_info.body.pmk_info.pmk_len coming from userspace, which can lead to a heap overwrite. | 2024-06-05 | | |
| n/a--n/a | An issue was discovered in Samsung Mobile Processor Exynos 980, Exynos 850, Exynos 1280, Exynos 1380, and Exynos 1330. In the function slsi_send_action_frame_cert(), there is no input validation check on len coming from userspace, which can lead to a heap over-read. | 2024-06-05 | | |
| n/a--n/a | An issue was discovered in Samsung Mobile Processor Exynos 980, Exynos 850, Exynos 1280, Exynos 1380, and Exynos 1330. In the function slsi_nan_subscribe_get_nl_params(), there is no input validation check on hal_req->num_intf_addr_present coming from userspace, which can lead to a heap overwrite. | 2024-06-05 | | |
| n/a--n/a | An issue was discovered in Samsung Mobile Processor Exynos 980, Exynos 850, Exynos 1280, Exynos 1380, and Exynos 1330. In the function slsi_set_delayed_wakeup_type(), there is no input validation check on a length of ioctl_args->args[i] coming from userspace, which can lead to a heap over-read. | 2024-06-05 | | |
| n/a--n/a | An issue was discovered in Samsung Mobile Processor Exynos 980, Exynos 850, Exynos 1280, Exynos 1380, and Exynos 1330. In the function slsi_send_action_frame_ut(), there is no input validation check on len coming from userspace, which can lead to a heap over-read. | 2024-06-05 | | |
| n/a--n/a | An issue was discovered in Samsung Mobile Processor Exynos 980, Exynos 850, Exynos 1280, Exynos 1380, and Exynos 1330. In the function slsi_send_action_frame(), there is no input validation check on len coming from userspace, which can lead to a heap over-read. | 2024-06-05 | | |
| n/a--n/a | An issue was discovered in Samsung Mobile Processor EExynos 2200, Exynos 1480, Exynos 2400. It lacks a check for the validation of native handles, which can result in an Out-of-Bounds Write. | 2024-06-07 | | |
| n/a--n/a | Ariane Allegro Scenario Player through 2024-03-05, when Ariane Duo kiosk mode is used, allows physically proximate attackers to obtain sensitive information (such as hotel invoice content with PII), and potentially create unauthorized room keys, by entering a guest-search quote character and then accessing the underlying Windows OS. | 2024-06-06 | | |
| n/a--n/a | An issue was discovered in Samsung Mobile Processor, Automotive Processor, Wearable Processor, and Modem Exynos 980, 990, 850, 1080, 2100, 2200, 1280, 1380, 1330, 9110, W920, Exynos Modem 5123, Exynos Modem 5300, and Exynos Auto T5123. The baseband software does not properly check format types specified by the RRC. This can lead to a lack of encryption. | 2024-06-05 | | |
| n/a--n/a | An issue was discovered in Samsung Mobile Processor, Wearable Processor, Automotive Processor, and Modem Exynos 980, 990, 850, 1080, 2100, 2200, 1280, 1380, 1330, 2400, 9110, W920, W930, Modem 5123, Modem 5300, and Auto T5123. The baseband software does not properly check states specified by the RRC (Radio Resource Control) module. This can lead to disclosure of sensitive information. | 2024-06-05 | | |
| n/a--n/a | An issue was discovered in Samsung Mobile Processor, Wearable Processor, Automotive Processor, and Modem Exynos 980, 990, 850, 1080, 2100, 2200, 1280, 1380, 1330, 2400, 9110, W920, W930, Modem 5123, Modem 5300, and Auto T5123. The baseband software does not properly check states specified by the RRC (Radio Resource Control) Reconfiguration message. This can lead to disclosure of sensitive information. | 2024-06-04 | | |
| N/A--RT Easy Builder Advanced addons for Elementor | Missing Authorization vulnerability in RT Easy Builder - Advanced addons for Elementor.This issue affects RT Easy Builder - Advanced addons for Elementor: from n/a through 2.0. | 2024-06-04 | | |
| nalam-1--Magical Addons For Elementor ( Header Footer Builder, Free Elementor Widgets, Elementor Templates Library ) | The Magical Addons For Elementor ( Header Footer Builder, Free Elementor Widgets, Elementor Templates Library ) plugin for WordPress is vulnerable to Stored Cross-Site Scripting via the '_id' parameter in all versions up to, and including, 1.1.39 due to insufficient input sanitization and output escaping. This makes it possible for authenticated attackers, with Contributor-level access and above, to inject arbitrary web scripts in pages that will execute whenever a user accesses an injected page. | 2024-06-06 | | |
| nayrathemes--Clever Fox | The Clever Fox plugin for WordPress is vulnerable to Stored Cross-Site Scripting via the plugin's info box block in all versions up to, and including, 25.2.0 due to insufficient input sanitization and output escaping on user supplied attributes. This makes it possible for authenticated attackers with contributor-level and above permissions to inject arbitrary web scripts in pages that will execute whenever a user accesses an injected page. | 2024-06-07 | | |
| nayrathemes--Clever Fox | The Clever Fox - One Click Website Importer by Nayra Themes plugin for WordPress is vulnerable to unauthorized modification of data due to a missing capability check on the 'clever-fox-activate-theme' function in all versions up to, and including, 25.2.0. This makes it possible for authenticated attackers, with subscriber access and above, to modify the active theme, including to an invalid value which can take down the site. | 2024-06-07 | | |
| ndijkstra--Mollie Forms | The Mollie Forms plugin for WordPress is vulnerable to Cross-Site Request Forgery in all versions up to, and including, 2.6.13. This is due to missing or incorrect nonce validation on the duplicateForm() function. This makes it possible for unauthenticated attackers to duplicate forms via a forged request granted they can trick a site administrator into performing an action such as clicking on a link. | 2024-06-05 | | |
| Netentsec--NS-ASG Application Security Gateway | A vulnerability was found in Netentsec NS-ASG Application Security Gateway 6.3. It has been classified as critical. This affects an unknown part of the file /admin/config_MT.php?action=delete. The manipulation of the argument Mid leads to sql injection. It is possible to initiate the attack remotely. The exploit has been disclosed to the public and may be used. The associated identifier of this vulnerability is VDB-266847. NOTE: The vendor was contacted early about this disclosure but did not respond in any way. | 2024-06-03 | | |
| Netentsec--NS-ASG Application Security Gateway | A vulnerability was found in Netentsec NS-ASG Application Security Gateway 6.3. It has been declared as critical. This vulnerability affects unknown code of the file /protocol/iscuser/uploadiscuser.php of the component JSON Content Handler. The manipulation of the argument messagecontent leads to sql injection. The attack can be initiated remotely. The exploit has been disclosed to the public and may be used. The identifier of this vulnerability is VDB-266848. NOTE: The vendor was contacted early about this disclosure but did not respond in any way. | 2024-06-03 | | |
| netty--netty-incubator-codec-ohttp | netty-incubator-codec-ohttp is the OHTTP implementation for netty. BoringSSLAEADContext keeps track of how many OHTTP responses have been sent and uses this sequence number to calculate the appropriate nonce to use with the encryption algorithm. Unfortunately, two separate errors combine which would allow an attacker to cause the sequence number to overflow and thus the nonce to repeat. | 2024-06-04 | | |
| Nitin Rathod--WP Forms Puzzle Captcha | Improper Restriction of Excessive Authentication Attempts vulnerability in Nitin Rathod WP Forms Puzzle Captcha allows Functionality Bypass.This issue affects WP Forms Puzzle Captcha: from n/a through 4.1. | 2024-06-04 | | |
| oslabs-beta--SkyScraper | SkyScrape is a GUI Dashboard for AWS Infrastructure and Managing Resources and Usage Costs. SkyScrape's API requests are currently unsecured HTTP requests, leading to potential vulnerabilities for the user's temporary credentials and data. This affects version 1.0.0. | 2024-06-07 | | |
| OTRS AG--OTRS | The file upload feature in OTRS and ((OTRS)) Community Edition has a path traversal vulnerability. This issue permits authenticated agents or customer users to upload potentially harmful files to directories accessible by the web server, potentially leading to the execution of local code like Perl scripts. This issue affects OTRS: from 7.0.X through 7.0.49, 8.0.X, 2023.X, from 2024.X through 2024.3.2; ((OTRS)) Community Edition: from 6.0.1 through 6.0.34. | 2024-06-06 | | |
| pandaboxwp--WP jQuery Lightbox | The WP jQuery Lightbox plugin for WordPress is vulnerable to Stored Cross-Site Scripting via the 'title' attribute in all versions up to, and including, 1.5.4 due to insufficient input sanitization and output escaping. This makes it possible for authenticated attackers, with Contributor-level access and above, to inject arbitrary web scripts in pages that will execute whenever a user accesses an injected page. | 2024-06-07 | | |
| pdfcrowd -- save_as_pdf_plugin | Improper Neutralization of Input During Web Page Generation (XSS or 'Cross-site Scripting') vulnerability in Pdfcrowd Save as PDF plugin by Pdfcrowd allows Stored XSS.This issue affects Save as PDF plugin by Pdfcrowd: from n/a through 3.2.3. | 2024-06-04 | | |
| Peregrine themes--Bloglo | Improper Neutralization of Input During Web Page Generation (XSS or 'Cross-site Scripting') vulnerability in Peregrine themes Bloglo allows Stored XSS.This issue affects Bloglo: from n/a through 1.1.3. | 2024-06-08 | | |
| pickplugins--Gutenberg Blocks, Page Builder ComboBlocks | The Post Grid, Form Maker, Popup Maker, WooCommerce Blocks, Post Blocks, Post Carousel - Combo Blocks plugin for WordPress is vulnerable to Stored Cross-Site Scripting via the 'tag' attribute in blocks in all versions up to, and including, 2.2.80 due to insufficient input sanitization and output escaping. This makes it possible for authenticated attackers, with contributor-level access and above, to inject arbitrary web scripts in pages that will execute whenever a user accesses an injected page. | 2024-06-07 | | |
| pickplugins--Gutenberg Blocks, Page Builder ComboBlocks | The Post Grid, Form Maker, Popup Maker, WooCommerce Blocks, Post Blocks, Post Carousel - Combo Blocks plugin for WordPress is vulnerable to Stored Cross-Site Scripting via the 'class' attribute of the menu-wrap-item block in all versions up to, and including, 2.2.80 due to insufficient input sanitization and output escaping. This makes it possible for authenticated attackers, with contributor-level access and above, to inject arbitrary web scripts in pages that will execute whenever a user accesses an injected page. | 2024-06-07 | | |
| PickPlugins--Tabs & Accordion | Improper Neutralization of Script-Related HTML Tags in a Web Page (Basic XSS) vulnerability in PickPlugins Tabs & Accordion allows Code Injection.This issue affects Tabs & Accordion: from n/a through 1.3.10. | 2024-06-04 | | |
| PINPOINT.WORLD--Pinpoint Booking System | External Control of Assumed-Immutable Web Parameter vulnerability in PINPOINT.WORLD Pinpoint Booking System allows Functionality Misuse.This issue affects Pinpoint Booking System: from n/a through 2.9.9.3.4. | 2024-06-04 | | |
| Plechev Andrey--WP-Recall | Cross-Site Request Forgery (CSRF) vulnerability in Plechev Andrey WP-Recall.This issue affects WP-Recall: from n/a through 16.26.6. | 2024-06-08 | | |
| Pluggabl LLC--Booster Elite for WooCommerce | Improper Authentication vulnerability in Pluggabl LLC Booster Elite for WooCommerce allows Accessing Functionality Not Properly Constrained by ACLs.This issue affects Booster Elite for WooCommerce: from n/a before 7.1.3. | 2024-06-04 | | |
| Pluggabl LLC--Booster for WooCommerce | Improper Authentication vulnerability in Pluggabl LLC Booster for WooCommerce allows Accessing Functionality Not Properly Constrained by ACLs.This issue affects Booster for WooCommerce: from n/a through 7.1.2. | 2024-06-04 | | |
| pluginever--WP Content Pilot Autoblogging & Affiliate Marketing Plugin | Improper Neutralization of Script-Related HTML Tags in a Web Page (Basic XSS) vulnerability in pluginever WP Content Pilot - Autoblogging & Affiliate Marketing Plugin allows Code Injection.This issue affects WP Content Pilot - Autoblogging & Affiliate Marketing Plugin: from n/a through 1.3.3. | 2024-06-04 | | |
| pluginkollektiv--Antispam Bee | Authentication Bypass by Spoofing vulnerability in pluginkollektiv Antispam Bee allows Accessing Functionality Not Properly Constrained by ACLs.This issue affects Antispam Bee: from n/a through 2.11.3. | 2024-06-04 | | |
| Podlove--Podlove Web Player | Exposure of Sensitive Information to an Unauthorized Actor vulnerability in Podlove Podlove Web Player.This issue affects Podlove Web Player: from n/a through 5.7.3. | 2024-06-08 | | |
| Popup Maker--Popup Maker WP | Improper Neutralization of Input During Web Page Generation (XSS or 'Cross-site Scripting') vulnerability in Popup Maker Popup Maker WP allows Stored XSS.This issue affects Popup Maker WP: from n/a through 1.2.8. | 2024-06-03 | | |
| POSIMYTH--The Plus Addons for Elementor Page Builder Lite | Improper Neutralization of Input During Web Page Generation (XSS or 'Cross-site Scripting') vulnerability in POSIMYTH The Plus Addons for Elementor Page Builder Lite allows Stored XSS.This issue affects The Plus Addons for Elementor Page Builder Lite: from n/a through 5.5.4. | 2024-06-08 | | |
| PropertyHive--PropertyHive | Improper Neutralization of Input During Web Page Generation (XSS or 'Cross-site Scripting') vulnerability in PropertyHive allows Stored XSS.This issue affects PropertyHive: from n/a through 2.0.13. | 2024-06-08 | | |
| ptz0n--Google CSE | The Google CSE plugin for WordPress is vulnerable to Stored Cross-Site Scripting via admin settings in all versions up to, and including, 1.0.7 due to insufficient input sanitization and output escaping. This makes it possible for authenticated attackers, with administrator-level permissions and above, to inject arbitrary web scripts in pages that will execute whenever a user accesses an injected page. This only affects multi-site installations and installations where unfiltered_html has been disabled. | 2024-06-06 | | |
| Pure Chat by Ruby--Pure Chat | Cross-Site Request Forgery (CSRF) vulnerability in Pure Chat by Ruby Pure Chat.This issue affects Pure Chat: from n/a through 2.22. | 2024-06-05 | | |
| purvabathe--Simple Image Popup Shortcode | The Simple Image Popup Shortcode plugin for WordPress is vulnerable to Stored Cross-Site Scripting via the plugin's 'sips_popup' shortcode in all versions up to, and including, 1.0 due to insufficient input sanitization and output escaping on user supplied attributes. This makes it possible for authenticated attackers, with contributor-level access and above, to inject arbitrary web scripts in pages that will execute whenever a user accesses an injected page. | 2024-06-06 | | |
| qodeinteractive--Qi Addons For Elementor | The Qi Addons For Elementor plugin for WordPress is vulnerable to Stored Cross-Site Scripting via the plugin's button widgets in all versions up to, and including, 1.7.2 due to insufficient input sanitization and output escaping on user supplied attributes. This makes it possible for authenticated attackers, with contributor-level access and above, to inject arbitrary web scripts in pages that will execute whenever a user accesses an injected page. | 2024-06-06 | | |
| qodeinteractive--Qi Blocks | The Qi Blocks plugin for WordPress is vulnerable to Stored Cross-Site Scripting via the plugin's file uploader in all versions up to, and including, 1.2.9 due to insufficient input sanitization and output escaping. This makes it possible for authenticated attackers, with Author-level access and above, to inject arbitrary web scripts in pages that will execute whenever a user accesses an injected page. | 2024-06-06 | | |
| Qualcomm, Inc.--Snapdragon | Information disclosure while handling T2LM Action Frame in WLAN Host. | 2024-06-03 | | |
| Qualcomm, Inc.--Snapdragon | Memory corruption in Audio during a playback or a recording due to race condition between allocation and deallocation of graph object. | 2024-06-03 | | |
| Qualcomm, Inc.--Snapdragon | Memory corruption when IPC callback handle is used after it has been released during register callback by another thread. | 2024-06-03 | | |
| Qualcomm, Inc.--Snapdragon | Memory corruption when more scan frequency list or channels are sent from the user space. | 2024-06-03 | | |
| Qualcomm, Inc.--Snapdragon | transient DOS when setting up a fence callback to free a KGSL memory entry object during DMA. | 2024-06-03 | | |
| quomodosoft--ElementsReady Addons for Elementor | The ElementsReady Addons for Elementor plugin for WordPress is vulnerable to Stored Cross-Site Scripting via the '_id' parameter in all versions up to, and including, 6.1.0 due to insufficient input sanitization and output escaping. This makes it possible for authenticated attackers, with Contributor-level access and above, to inject arbitrary web scripts in pages that will execute whenever a user accesses an injected page. | 2024-06-06 | | |
| RadiusTheme--The Post Grid | Improper Neutralization of Input During Web Page Generation (XSS or 'Cross-site Scripting') vulnerability in RadiusTheme The Post Grid allows Stored XSS.This issue affects The Post Grid: from n/a through 7.7.1. | 2024-06-08 | | |
| rails--rails | Action Text brings rich text content and editing to Rails. Instances of ActionText::Attachable::ContentAttachment included within a rich_text_area tag could potentially contain unsanitized HTML. This vulnerability is fixed in 7.1.3.4 and 7.2.0.beta2. | 2024-06-04 | | |
| rails--rails | Action Pack is a framework for handling and responding to web requests. Since 6.1.0, the application configurable Permissions-Policy is only served on responses with an HTML related Content-Type. This vulnerability is fixed in 6.1.7.8, 7.0.8.2, and 7.1.3.3. | 2024-06-04 | | |
| Red Hat--Red Hat Satellite 6 | A flaw was found in foreman-installer when puppet-candlepin is invoked cpdb with the --password parameter. This issue leaks the password in the process list and allows an attacker to take advantage and obtain the password. | 2024-06-05 | | |
| Red Hat--Red Hat Satellite 6 | A flaw was found in the Katello plugin for Foreman, where it is possible to store malicious JavaScript code in the "Description" field of a user. This code can be executed when opening certain pages, for example, Host Collections. | 2024-06-05 | | |
| restrict--Restrict for Elementor | The Restrict for Elementor plugin for WordPress is vulnerable to Sensitive Information Exposure in all versions up to, and including, 1.0.6 due to improper restrictions on hidden data that make it accessible through the REST API. This makes it possible for unauthenticated attackers to extract potentially sensitive data from post content. | 2024-06-06 | | |
| Revolution Slider--Slider Revolution | The Slider Revolution plugin for WordPress is vulnerable to Stored Cross-Site Scripting via the plugin's Add Layer widget in all versions up to, and including, 6.7.11 due to insufficient input sanitization and output escaping on the user supplied 'class', 'id', and 'title' attributes. This makes it possible for authenticated attackers, with author-level access and above, to inject arbitrary web scripts in pages that will execute whenever a user accesses an injected page. NOTE: Successful exploitation of this vulnerability requires an Administrator to give Slider Creation privileges to Author-level users. | 2024-06-04 | | |
| Revolution Slider--Slider Revolution | The Slider Revolution plugin for WordPress is vulnerable to Stored Cross-Site Scripting in all versions up to, and including, 6.7.10 due to insufficient input sanitization and output escaping on the user supplied Elementor 'wrapperid' and 'zindex' display attributes. This makes it possible for authenticated attackers, with contributor-level access and above, to inject arbitrary web scripts in pages that will execute whenever a user accesses an injected page. | 2024-06-04 | | |
| rubengc--GamiPress Link | The GamiPress - Link plugin for WordPress is vulnerable to Stored Cross-Site Scripting via the plugin's gamipress_link shortcode in all versions up to, and including, 1.1.4 due to insufficient input sanitization and output escaping on user supplied attributes. This makes it possible for authenticated attackers, with contributor-level access and above, to inject arbitrary web scripts in pages that will execute whenever a user accesses an injected page. | 2024-06-05 | | |
| rustaurius--Five Star Restaurant Menu and Food Ordering | The Restaurant Menu and Food Ordering plugin for WordPress is vulnerable to unauthorized creation of data due to a missing capability check on 'add_section', 'add_menu', 'add_menu_item', and 'add_menu_page' functions in all versions up to, and including, 2.4.16. This makes it possible for authenticated attackers, with Subscriber-level access and above, to create menu sections, menus, food items, and new menu pages. | 2024-06-05 | | |
| Samsung Mobile--GalaxyBudsManager PC | Arbitrary directory creation in GalaxyBudsManager PC prior to version 2.1.240315.51 allows attacker to create arbitrary directory. | 2024-06-04 | | |
| Samsung Mobile--Samsung Live Wallpaper PC | Arbitrary directory creation in Samsung Live Wallpaper PC prior to version 3.3.8.0 allows attacker to create arbitrary directory. | 2024-06-04 | | |
| Samsung Mobile--Samsung Mobile Devices | Improper input validation in libsheifdecadapter.so prior to SMR Jun-2024 Release 1 allows local attackers to lead to memory corruption. | 2024-06-04 | | |
| Samsung Mobile--Samsung Mobile Devices | Stack-based buffer overflow vulnerability in bootloader prior to SMR Jun-2024 Release 1 allows physical attackers to overwrite memory. | 2024-06-04 | | |
| Samsung Mobile--Samsung Mobile Devices | Improper input validation vulnerability in chnactiv TA prior to SMR Jun-2024 Release 1 allows local privileged attackers lead to potential arbitrary code execution. | 2024-06-04 | | |
| Samsung Mobile--Samsung Mobile Devices | Incorrect use of privileged API vulnerability in registerBatteryStatsCallback in BatteryStatsService prior to SMR Jun-2024 Release 1 allows local attackers to use privileged API. | 2024-06-04 | | |
| Samsung Mobile--Samsung Mobile Devices | Incorrect use of privileged API vulnerability in getSemBatteryUsageStats in BatteryStatsService prior to SMR Jun-2024 Release 1 allows local attackers to use privileged API. | 2024-06-04 | | |
| Samsung Mobile--Samsung Mobile Devices | Improper component protection vulnerability in Samsung Dialer prior to SMR May-2024 Release 1 allows local attackers to make a call without proper permission. | 2024-06-04 | | |
| Samsung Mobile--Samsung Mobile Devices | Improper input validation vulnerability in caminfo driver prior to SMR Jun-2024 Release 1 allows local privileged attackers to write out-of-bounds memory. | 2024-06-04 | | |
| Samsung Mobile--Samsung Mobile Devices | Improper caller verification vulnerability in SemClipboard prior to SMR June-2024 Release 1 allows local attackers to access arbitrary files. | 2024-06-04 | | |
| Samsung Mobile--Samsung Mobile Devices | Improper input validation vulnerability in libsavscmn.so prior to SMR Jun-2024 Release 1 allows local attackers to write out-of-bounds memory. | 2024-06-04 | | |
| Samsung Mobile--Samsung Mobile Devices | Out-of-bounds read vulnerability in bootloader prior to SMR June-2024 Release 1 allows physical attackers to arbitrary data access. | 2024-06-04 | | |
| satollo--Newsletter Send awesome emails from WordPress | The Newsletter plugin for WordPress is vulnerable to Stored Cross-Site Scripting via the 'np1' parameter in all versions up to, and including, 8.3.4 due to insufficient input sanitization and output escaping. This makes it possible for unauthenticated attackers to inject arbitrary web scripts in pages that will execute whenever a user accesses an injected page. | 2024-06-05 | | |
| sendinblue -- newsletter\,_smtp\,_email_marketing_and_subscribe | Improper Neutralization of Input During Web Page Generation (XSS or 'Cross-site Scripting') vulnerability in Brevo Newsletter, SMTP, Email marketing and Subscribe forms by Sendinblue allows Reflected XSS.This issue affects Newsletter, SMTP, Email marketing and Subscribe forms by Sendinblue: from n/a through 3.1.77. | 2024-06-04 | | |
| Sensei--Sensei Pro (WC Paid Courses) | Improper Neutralization of Input During Web Page Generation (XSS or 'Cross-site Scripting') vulnerability in Sensei Sensei Pro (WC Paid Courses) allows Stored XSS.This issue affects Sensei Pro (WC Paid Courses): from n/a through 4.23.1.1.23.1. | 2024-06-08 | | |
| shafayat-alam--Gutenberg Blocks and Page Layouts Attire Blocks | The Gutenberg Blocks and Page Layouts - Attire Blocks plugin for WordPress is vulnerable to unauthorized modification of data due to a missing capability check on the disable_fe_assets function in all versions up to, and including, 1.9.2. This makes it possible for authenticated attackers, with subscriber access or above, to change the plugin's settings. Additionally, no nonce check is performed resulting in a CSRF vulnerability. | 2024-06-05 | | |
| shrinitech--Fluid Notification Bar | The Fluid Notification Bar plugin for WordPress is vulnerable to Stored Cross-Site Scripting via admin settings in all versions up to, and including, 3.2.3 due to insufficient input sanitization and output escaping. This makes it possible for authenticated attackers, with administrator-level permissions and above, to inject arbitrary web scripts in pages that will execute whenever a user accesses an injected page. This only affects multi-site installations and installations where unfiltered_html has been disabled. | 2024-06-04 | | |
| silabs.com--Gecko SDK | A bug exists in the API, mesh_node_power_off(), which fails to copy the contents of the Replay Protection List (RPL) from RAM to NVM before powering down, resulting in the ability to replay unsaved messages. Note that as of June 2024, the Gecko SDK was renamed to the Simplicity SDK, and the versioning scheme was changed from Gecko SDK vX.Y.Z to Simplicity SDK YYYY.MM.Patch#. | 2024-06-06 | | |
| SinaExtra--Sina Extension for Elementor | Improper Limitation of a Pathname to a Restricted Directory ('Path Traversal') vulnerability in SinaExtra Sina Extension for Elementor allows PHP Local File Inclusion.This issue affects Sina Extension for Elementor: from n/a through 3.5.1. | 2024-06-04 | | |
| SinaExtra--Sina Extension for Elementor | Improper Neutralization of Input During Web Page Generation (XSS or 'Cross-site Scripting') vulnerability in SinaExtra Sina Extension for Elementor allows Stored XSS.This issue affects Sina Extension for Elementor: from n/a through 3.5.3. | 2024-06-08 | | |
| SoftLab--Integrate Google Drive | Broken Authentication vulnerability in SoftLab Integrate Google Drive.This issue affects Integrate Google Drive: from n/a through 1.3.93. | 2024-06-04 | | |
| solarwinds -- solarwinds_platform | The SolarWinds Platform was determined to be affected by a stored cross-site scripting vulnerability affecting the web console. A high-privileged user and user interaction is required to exploit this vulnerability. | 2024-06-04 | | |
| Spiffy Plugins--Spiffy Calendar | Missing Authorization vulnerability in Spiffy Plugins Spiffy Calendar.This issue affects Spiffy Calendar: from n/a through 4.9.10. | 2024-06-04 | | |
| spiffyplugins -- wp_flow_plus | Improper Neutralization of Input During Web Page Generation (XSS or 'Cross-site Scripting') vulnerability in Spiffy Plugins WP Flow Plus allows Stored XSS.This issue affects WP Flow Plus: from n/a through 5.2.2. | 2024-06-04 | | |
| StarCitizenTools--mediawiki-skins-Citizen | Citizen is a MediaWiki skin that makes extensions part of the cohesive experience. The page `MediaWiki:Tagline` has its contents used unescaped, so custom HTML (including Javascript) can be injected by someone with the ability to edit the MediaWiki namespace (typically those with the `editinterface` permission, or sysops). This vulnerability is fixed in 2.16.0. | 2024-06-03 | | |
| sulu--SuluFormBundle | The SuluFormBundle adds support for creating dynamic forms in Sulu Admin. The TokenController get parameter formName is not sanitized in the returned input field which leads to XSS. This vulnerability is fixed in 2.5.3. | 2024-06-06 | | |
| Synology--Camera Firmware | A vulnerability regarding buffer copy without checking the size of input ('Classic Buffer Overflow') has been found in the login component. This allows remote attackers to conduct denial-of-service attacks via unspecified vectors. This attack only affects the login service which will automatically restart. The following models with Synology Camera Firmware versions before 1.1.1-0383 may be affected: BC500 and TC500. | 2024-06-04 | | |
| tagDiv--tagDiv Composer | The tagDiv Composer plugin for WordPress is vulnerable to Stored Cross-Site Scripting via the plugin's button shortcode in all versions up to, and including, 4.8 due to insufficient input sanitization and output escaping on user supplied attributes. This makes it possible for authenticated attackers, with contributor-level access and above, to inject arbitrary web scripts in pages that will execute whenever a user accesses an injected page. NOTE: The vulnerable code in this plugin is specifically tied to the tagDiv Newspaper theme. If another theme is installed (e.g., NewsMag), this code may not be present. | 2024-06-04 | | |
| Tainacan.org--Tainacan | Improper Neutralization of Input During Web Page Generation (XSS or 'Cross-site Scripting') vulnerability in Tainacan.Org Tainacan allows Stored XSS.This issue affects Tainacan: from n/a through 0.21.3. | 2024-06-03 | | |
| takanakui--WP Mobile Menu The Mobile-Friendly Responsive Menu | The WP Mobile Menu - The Mobile-Friendly Responsive Menu plugin for WordPress is vulnerable to Stored Cross-Site Scripting via image alt text in all versions up to, and including, 2.8.4.2 due to insufficient input sanitization and output escaping. This makes it possible for authenticated attackers, with author-level access and above, to inject arbitrary web scripts in pages that will execute whenever a user accesses an injected page. | 2024-06-07 | | |
| Team Heateor--Heateor Social Login | Improper Neutralization of Input During Web Page Generation (XSS or 'Cross-site Scripting') vulnerability in Team Heateor Heateor Social Login allows Stored XSS.This issue affects Heateor Social Login: from n/a through 1.1.32. | 2024-06-08 | | |
| TemplatesNext--TemplatesNext OnePager | Improper Neutralization of Input During Web Page Generation (XSS or 'Cross-site Scripting') vulnerability in TemplatesNext TemplatesNext OnePager allows Stored XSS.This issue affects TemplatesNext OnePager: from n/a through 1.3.3. | 2024-06-08 | | |
| Theme Freesia--Event | Improper Neutralization of Input During Web Page Generation (XSS or 'Cross-site Scripting') vulnerability in Theme Freesia Event allows Stored XSS.This issue affects Event: from n/a through 1.2.2. | 2024-06-08 | | |
| Theme Freesia--Idyllic | Improper Neutralization of Input During Web Page Generation (XSS or 'Cross-site Scripting') vulnerability in Theme Freesia Idyllic allows Stored XSS.This issue affects Idyllic: from n/a through 1.1.8. | 2024-06-08 | | |
| Theme Freesia--Pixgraphy | Improper Neutralization of Input During Web Page Generation (XSS or 'Cross-site Scripting') vulnerability in Theme Freesia Pixgraphy allows Stored XSS.This issue affects Pixgraphy: from n/a through 1.3.8. | 2024-06-08 | | |
| themefarmer--WooCommerce Tools | The WooCommerce Tools plugin for WordPress is vulnerable to unauthorized modification of data due to a missing capability check on the woocommerce_tool_toggle_module() function in all versions up to, and including, 1.2.9. This makes it possible for authenticated attackers, with subscriber-level access and above, to deactivate arbitrary plugin modules. | 2024-06-07 | | |
| themefusecom--Brizy Page Builder | The Brizy - Page Builder plugin for WordPress is vulnerable to Stored Cross-Site Scripting via the plugin's contact form widget error message and redirect URL in all versions up to, and including, 2.4.43 due to insufficient input sanitization and output escaping on user supplied error messages. This makes it possible for authenticated attackers with contributor-level and above permissions to inject arbitrary web scripts in pages that will execute whenever a user accesses an injected page. | 2024-06-05 | | |
| Themeisle--Otter Blocks PRO | Exposure of Sensitive Information to an Unauthorized Actor vulnerability in Themeisle Otter Blocks PRO.This issue affects Otter Blocks PRO: from n/a through 2.6.11. | 2024-06-08 | | |
| themekraft -- buddyforms | The BuddyForms plugin for WordPress is vulnerable to Email Verification Bypass in all versions up to, and including, 2.8.9 via the use of an insufficiently random activation code. This makes it possible for unauthenticated attackers to bypass the email verification. | 2024-06-05 | | |
| themesflat -- themesflat_addons_for_elementor | Improper Neutralization of Input During Web Page Generation (XSS or 'Cross-site Scripting') vulnerability in Themesflat Themesflat Addons For Elementor allows Stored XSS.This issue affects Themesflat Addons For Elementor: from n/a through 2.1.2. | 2024-06-04 | | |
| themesflat--Themesflat Addons For Elementor | The Themesflat Addons For Elementor plugin for WordPress is vulnerable to Stored Cross-Site Scripting via widget tags in all versions up to, and including, 2.1.1 due to insufficient input sanitization and output escaping on user supplied attributes. This makes it possible for authenticated attackers, with contributor-level access and above, to inject arbitrary web scripts in pages that will execute whenever a user accesses an injected page. | 2024-06-06 | | |
| themesflat--Themesflat Addons For Elementor | The Themesflat Addons For Elementor plugin for WordPress is vulnerable to Stored Cross-Site Scripting via the plugin's TF Group Image, TF Nav Menu, TF Posts, TF Woo Product Grid, TF Accordion, and TF Image Box widgets in all versions up to, and including, 2.1.1 due to insufficient input sanitization and output escaping on user supplied attributes. This makes it possible for authenticated attackers, with contributor-level access and above, to inject arbitrary web scripts in pages that will execute whenever a user accesses an injected page. | 2024-06-06 | | |
| themesflat--Themesflat Addons For Elementor | The Themesflat Addons For Elementor plugin for WordPress is vulnerable to Stored Cross-Site Scripting in several widgets via URL parameters in all versions up to, and including, 2.1.1 due to insufficient input sanitization and output escaping. This makes it possible for authenticated attackers, with contributor access and above, to inject arbitrary web scripts in pages that will execute whenever a user accesses an injected page. | 2024-06-06 | | |
| themesflat--Themesflat Addons For Elementor | The Themesflat Addons For Elementor plugin for WordPress is vulnerable to Stored Cross-Site Scripting via the plugin's widget's titles in all versions up to, and including, 2.1.1 due to insufficient input sanitization and output escaping on user supplied attributes. This makes it possible for authenticated attackers, with contributor-level access and above, to inject arbitrary web scripts in pages that will execute whenever a user accesses an injected page. | 2024-06-06 | | |
| themeum--Tutor LMS eLearning and online course solution | The Tutor LMS - eLearning and online course solution plugin for WordPress is vulnerable to Insecure Direct Object Reference in all versions up to, and including, 2.7.1 via the 'attempt_delete' function due to missing validation on a user controlled key. This makes it possible for authenticated attackers, with Instructor-level access and above, to delete arbitrary quiz attempts. | 2024-06-07 | | |
| thimpress--LearnPress WordPress LMS Plugin | The LearnPress - WordPress LMS Plugin plugin for WordPress is vulnerable to Sensitive Information Exposure in all versions up to, and including, 4.2.6.8 due to incorrect implementation of get_items_permissions_check function. This makes it possible for unauthenticated attackers to extract basic information about website users, including their emails | 2024-06-05 | | |
| Tips and Tricks HQ--Stripe Payments | Improper Neutralization of Script-Related HTML Tags in a Web Page (Basic XSS) vulnerability in Tips and Tricks HQ Stripe Payments allows Code Injection.This issue affects Stripe Payments: from n/a through 2.0.79. | 2024-06-04 | | |
| TNB Mobile Solutions--Cockpit Software | Inclusion of Sensitive Information in Source Code vulnerability in TNB Mobile Solutions Cockpit Software allows Retrieve Embedded Sensitive Data.This issue affects Cockpit Software: before v0.251.1. | 2024-06-05 | | |
| tobiasbg--TablePress Tables in WordPress made easy | The TablePress - Tables in WordPress made easy plugin for WordPress is vulnerable to Server-Side Request Forgery in all versions up to, and including, 2.3 via the get_files_to_import() function. This makes it possible for authenticated attackers, with author-level access and above, to make web requests to arbitrary locations originating from the web application and can be used to query and modify information from internal services. Due to the complex nature of protecting against DNS rebind attacks in WordPress software, we settled on the developer simply restricting the usage of the URL import functionality to just administrators. While this is not optimal, we feel this poses a minimal risk to most site owners and ideally WordPress core would correct this issue in wp_safe_remote_get() and other functions. | 2024-06-07 | | |
| Tomas Cordero--Safety Exit | Improper Neutralization of Input During Web Page Generation (XSS or 'Cross-site Scripting') vulnerability in Tomas Cordero Safety Exit allows Stored XSS.This issue affects Safety Exit: from n/a through 1.7.0. | 2024-06-03 | | |
| UAPP GROUP--Testimonial Carousel For Elementor | Improper Neutralization of Input During Web Page Generation (XSS or 'Cross-site Scripting') vulnerability in UAPP GROUP Testimonial Carousel For Elementor allows Stored XSS.This issue affects Testimonial Carousel For Elementor: from n/a through 10.1.1. | 2024-06-08 | | |
| Unlimited Elements--Unlimited Elements For Elementor (Free Widgets, Addons, Templates) | Missing Authorization vulnerability in Unlimited Elements Unlimited Elements For Elementor (Free Widgets, Addons, Templates).This issue affects Unlimited Elements For Elementor (Free Widgets, Addons, Templates): from n/a through 1.5.109. | 2024-06-05 | | |
| victorfreitas--WPUpper Share Buttons | The WPUpper Share Buttons plugin for WordPress is vulnerable to unauthorized access of data when preparing sharing links for posts and pages in all versions up to, and including, 3.43. This makes it possible for unauthenticated attackers to obtain the contents of password protected posts and pages. | 2024-06-04 | | |
| VideoWhisper--Picture Gallery | Improper Neutralization of Input During Web Page Generation (XSS or 'Cross-site Scripting') vulnerability in VideoWhisper Picture Gallery allows Stored XSS.This issue affects Picture Gallery: from n/a through 1.5.11. | 2024-06-04 | | |
| visualcomposer -- visual_composer_website_builder | Improper Neutralization of Input During Web Page Generation (XSS or 'Cross-site Scripting') vulnerability in visualcomposer.Com Visual Composer Website Builder allows Stored XSS.This issue affects Visual Composer Website Builder: from n/a through 45.8.0. | 2024-06-04 | | |
| Volkswagen Group Charging GmbH - Elli, EVBox--ID Charger Connect & Pro | An attacker with access to the private network (the charger is connected to) or local access to the Ethernet-Interface can exploit a faulty implementation of the JWT-library in order to bypass the password authentication to the web configuration interface and then has full access as the user would have. However, an attacker will not have developer or admin rights. If the implementation of the JWT-library is wrongly configured to accept "none"-algorithms, the server will pass insecure JWT. A local, unauthenticated attacker can exploit this vulnerability to bypass the authentication mechanism. | 2024-06-06 | | |
| vollstart -- event_tickets_with_ticket_scanner | Improper Neutralization of Input During Web Page Generation (XSS or 'Cross-site Scripting') vulnerability in Saso Nikolov Event Tickets with Ticket Scanner allows Reflected XSS.This issue affects Event Tickets with Ticket Scanner: from n/a through 2.3.1. | 2024-06-04 | | |
| Vsourz Digital--Responsive Slick Slider WordPress | Improper Neutralization of Script-Related HTML Tags in a Web Page (Basic XSS) vulnerability in Vsourz Digital Responsive Slick Slider WordPress allows Code Injection.This issue affects Responsive Slick Slider WordPress: from n/a through 1.4. | 2024-06-04 | | |
| wbcomdesigns--Wbcom Designs Custom Font Uploader | The Wbcom Designs - Custom Font Uploader plugin for WordPress is vulnerable to unauthorized loss of data due to a missing capability check on the 'cfu_delete_customfont' function in all versions up to, and including, 2.3.4. This makes it possible for authenticated attackers, with Subscriber-level access and above, to delete any custom font. | 2024-06-06 | | |
| wcmp--MultiVendorX Marketplace WooCommerce MultiVendor Marketplace Solution | The MultiVendorX Marketplace - WooCommerce MultiVendor Marketplace Solution plugin for WordPress is vulnerable to Stored Cross-Site Scripting via the 'hover_animation' parameter in all versions up to, and including, 4.1.11 due to insufficient input sanitization and output escaping. This makes it possible for authenticated attackers, with Contributor-level access and above, to inject arbitrary web scripts in pages that will execute whenever a user accesses an injected page. | 2024-06-06 | | |
| web-audimex -- audimexee | Cross Site Scripting vulnerability in audimex audimexEE v.15.1.2 and fixed in 15.1.3.9 allows a remote attacker to execute arbitrary code via the service, method, widget_type, request_id, payload parameters. | 2024-06-04 | | |
| WebFactory Ltd--Captcha Code | Improper Restriction of Excessive Authentication Attempts vulnerability in WebFactory Ltd Captcha Code allows Functionality Bypass.This issue affects Captcha Code: from n/a through 2.9. | 2024-06-04 | | |
| webfactory--Minimal Coming Soon Coming Soon Page | The Minimal Coming Soon - Coming Soon Page plugin for WordPress is vulnerable to unauthorized modification of data due to a missing capability check on the validate_ajax, deactivate_ajax, and save_ajax functions in all versions up to, and including, 2.38. This makes it possible for authenticated attackers, with Subscriber-level access and above, to edit the license key, which could disable features of the plugin. | 2024-06-08 | | |
| webfactory--WP Force SSL & HTTPS SSL Redirect | The WP Force SSL & HTTPS SSL Redirect plugin for WordPress is vulnerable to unauthorized modification of data due to a missing capability check on the 'ajax_save_setting' function in versions up to, and including, 1.66. This makes it possible for authenticated attackers, subscriber-level permissions and above, to update the plugin settings. | 2024-06-08 | | |
| webfactory--WP Reset Most Advanced WordPress Reset Tool | The WP Reset plugin for WordPress is vulnerable to unauthorized modification of data due to a missing capability check on the save_ajax function in all versions up to, and including, 2.02. This makes it possible for authenticated attackers, with subscriber-level access and above, to modify the value fo the 'License Key' field for the 'Activate Pro License' setting. | 2024-06-08 | | |
| Webliberty--Simple Spoiler | Improper Neutralization of Input During Web Page Generation (XSS or 'Cross-site Scripting') vulnerability in Webliberty Simple Spoiler allows Stored XSS.This issue affects Simple Spoiler: from n/a through 1.2. | 2024-06-03 | | |
| westerndeal--CF7 Google Sheets Connector | The CF7 Google Sheets Connector plugin for WordPress is vulnerable to unauthorized modification of data due to a missing capability check on the 'execute_post_data_cg7_free' function in all versions up to, and including, 5.0.9. This makes it possible for unauthenticated attackers to toggle site configuration settings, including WP_DEBUG, WP_DEBUG_LOG, SCRIPT_DEBUG, and SAVEQUERIES. | 2024-06-08 | | |
| westguard--WS Form LITE Drag & Drop Contact Form Builder for WordPress | The WS Form LITE plugin for WordPress is vulnerable to CSV Injection in versions up to, and including, 1.9.217. This allows unauthenticated attackers to embed untrusted input into exported CSV files, which can result in code execution when these files are downloaded and opened on a local system with a vulnerable configuration. | 2024-06-07 | | |
| willnorris--Open Graph | The Open Graph plugin for WordPress is vulnerable to Sensitive Information Exposure in all versions up to, and including, 1.11.2 via the 'opengraph_default_description' function. This makes it possible for unauthenticated attackers to extract sensitive data including partial content of password-protected blog posts. | 2024-06-06 | | |
| wordpresschef--Salon Booking System | The Salon booking system plugin for WordPress is vulnerable to unauthorized access and modification of data due to a missing capability check on several functions hooked into admin_init in all versions up to, and including, 9.9. This makes it possible for authenticated attackers with subscriber access or higher to modify plugin settings and view discount codes intended for other users. | 2024-06-08 | | |
| Wow-Company--Woocommerce Recent Purchases | Improper Limitation of a Pathname to a Restricted Directory ('Path Traversal') vulnerability in Wow-Company Woocommerce - Recent Purchases allows PHP Local File Inclusion.This issue affects Woocommerce - Recent Purchases: from n/a through 1.0.1. | 2024-06-04 | | |
| WP Darko--Responsive Tabs | Improper Neutralization of Script-Related HTML Tags in a Web Page (Basic XSS) vulnerability in WP Darko Responsive Tabs allows Code Injection.This issue affects Responsive Tabs: from n/a before 4.0.6. | 2024-06-04 | | |
| WP Discussion Board--Discussion Board | Improper Neutralization of Script-Related HTML Tags in a Web Page (Basic XSS) vulnerability in WP Discussion Board Discussion Board allows Content Spoofing, Cross-Site Scripting (XSS).This issue affects Discussion Board: from n/a through 2.4.8. | 2024-06-04 | | |
| WP Hait--Post Grid Elementor Addon | Improper Neutralization of Input During Web Page Generation (XSS or 'Cross-site Scripting') vulnerability in WP Hait Post Grid Elementor Addon allows Stored XSS.This issue affects Post Grid Elementor Addon: from n/a through 2.0.16. | 2024-06-03 | | |
| WP Moose--Kenta Gutenberg Blocks Responsive Blocks and block templates library for Gutenberg Editor | Improper Neutralization of Input During Web Page Generation (XSS or 'Cross-site Scripting') vulnerability in WP Moose Kenta Gutenberg Blocks Responsive Blocks and block templates library for Gutenberg Editor allows Stored XSS.This issue affects Kenta Gutenberg Blocks Responsive Blocks and block templates library for Gutenberg Editor: from n/a through 1.3.9. | 2024-06-08 | | |
| wpbean--WPB Elementor Addons | Improper Neutralization of Input During Web Page Generation (XSS or 'Cross-site Scripting') vulnerability in wpbean WPB Elementor Addons allows Stored XSS.This issue affects WPB Elementor Addons: from n/a through 1.0.9. | 2024-06-03 | | |
| WPBlockArt--BlockArt Blocks | Improper Neutralization of Input During Web Page Generation (XSS or 'Cross-site Scripting') vulnerability in WPBlockArt BlockArt Blocks allows Stored XSS.This issue affects BlockArt Blocks: from n/a through 2.1.5. | 2024-06-08 | | |
| wpchill--Strong Testimonials | The Strong Testimonials plugin for WordPress is vulnerable to unauthorized modification of data due to an improper capability check on the wpmtst_save_view_sticky function in all versions up to, and including, 3.1.12. This makes it possible for authenticated attackers, with contributor access and above, to modify favorite views. | 2024-06-07 | | |
| WPDeveloper--Essential Addons for Elementor | Improper Neutralization of Input During Web Page Generation (XSS or 'Cross-site Scripting') vulnerability in WPDeveloper Essential Addons for Elementor allows Stored XSS.This issue affects Essential Addons for Elementor: from n/a through 5.9.15. | 2024-06-03 | | |
| wpdevteam--EmbedPress Embed PDF, Google Docs, Vimeo, Wistia, Embed YouTube Videos, Audios, Maps & Embed Any Documents in Gutenberg & Elementor | The EmbedPress - Embed PDF, Google Docs, Vimeo, Wistia, Embed YouTube Videos, Audios, Maps & Embed Any Documents in Gutenberg & Elementor plugin for WordPress is vulnerable to Stored Cross-Site Scripting via the 'url' attribute within the plugin's EmbedPress PDF widget in all versions up to, and including, 4.0.1 due to insufficient input sanitization and output escaping on user supplied attributes. This makes it possible for authenticated attackers, with contributor-level access and above, to inject arbitrary web scripts in pages that will execute whenever a user accesses an injected page. | 2024-06-05 | | |
| wpdevteam--Essential Addons for Elementor Best Elementor Templates, Widgets, Kits & WooCommerce Builders | The Essential Addons for Elementor - Best Elementor Templates, Widgets, Kits & WooCommerce Builders plugin for WordPress is vulnerable to Stored Cross-Site Scripting via the 'get_manual_calendar_events' function in all versions up to, and including, 5.9.22 due to insufficient input sanitization and output escaping. This makes it possible for authenticated attackers, with Contributor-level access and above, to inject arbitrary web scripts in pages that will execute whenever a user accesses an injected page. | 2024-06-06 | | |
| wpecommerce--Recurring PayPal Donations | Improper Neutralization of Input During Web Page Generation (XSS or 'Cross-site Scripting') vulnerability in wpecommerce Recurring PayPal Donations allows Stored XSS.This issue affects Recurring PayPal Donations: from n/a through 1.7. | 2024-06-08 | | |
| WPManageNinja LLC--Ninja Tables | Server-Side Request Forgery (SSRF) vulnerability in WPManageNinja LLC Ninja Tables.This issue affects Ninja Tables: from n/a through 5.0.9. | 2024-06-03 | | |
| WPMU DEV--Branda | Authentication Bypass by Spoofing vulnerability in WPMU DEV Branda allows Accessing Functionality Not Properly Constrained by ACLs.This issue affects Branda: from n/a through 3.4.14. | 2024-06-04 | | |
| WPMU DEV--Defender Security | Improper Authentication vulnerability in WPMU DEV Defender Security allows Accessing Functionality Not Properly Constrained by ACLs.This issue affects Defender Security: from n/a through 4.2.0. | 2024-06-04 | | |
| wponlinesupport--Album and Image Gallery plus Lightbox | The The Album and Image Gallery plus Lightbox plugin for WordPress is vulnerable to arbitrary shortcode execution in all versions up to, and including, 2.0. This is due to the software allowing users to execute an action that does not properly validate a value before running do_shortcode. This makes it possible for unauthenticated attackers to execute arbitrary shortcodes. | 2024-06-06 | | |
| WPPlugins WordPress Security Plugins--Hide My WP Ghost | Improper Restriction of Excessive Authentication Attempts vulnerability in WPPlugins - WordPress Security Plugins Hide My WP Ghost allows Functionality Bypass.This issue affects Hide My WP Ghost: from n/a through 5.0.25. | 2024-06-04 | | |
| wppool--WP Dark Mode WordPress Dark Mode Plugin for Improved Accessibility, Dark Theme, Night Mode, and Social Sharing | The WP Dark Mode - WordPress Dark Mode Plugin for Improved Accessibility, Dark Theme, Night Mode, and Social Sharing plugin for WordPress is vulnerable to unauthorized modification of data due to a missing capability check on the wpdm_social_share_save_options function in all versions up to, and including, 5.0.4. This makes it possible for authenticated attackers, with Subscriber-level access and above, to update the plugin's settings. | 2024-06-06 | | |
| wppost--WP-Recall Registration, Profile, Commerce & More | The WP-Recall - Registration, Profile, Commerce & More plugin for WordPress is vulnerable to unauthorized loss of data due to a missing capability check on the 'delete_payment' function in all versions up to, and including, 16.26.6. This makes it possible for unauthenticated attackers to delete arbitrary payments. | 2024-06-06 | | |
| wproyal--Royal Elementor Addons and Templates | The Royal Elementor Addons and Templates for WordPress is vulnerable to Stored Cross-Site Scripting via the 'inline_list' parameter in versions up to, and including, 1.3.976 due to insufficient input sanitization and output escaping. This makes it possible for authenticated attackers, with contributor-level permissions and above, to inject arbitrary web scripts in pages that will execute whenever a user accesses an injected page. | 2024-06-07 | | |
| wproyal--Royal Elementor Addons and Templates | The Royal Elementor Addons and Templates plugin for WordPress is vulnerable to Stored Cross-Site Scripting via the 'custom_upload_mimes' function in versions up to, and including, 1.3.976 due to insufficient input sanitization and output escaping. This makes it possible for authenticated attackers, with contributor-level permissions and above, to inject arbitrary web scripts in pages that will execute whenever a user accesses an injected page. | 2024-06-07 | | |
| wpvivid -- wpvivid_backup_for_mainwp | Improper Neutralization of Input During Web Page Generation (XSS or 'Cross-site Scripting') vulnerability in WPvivid Team WPvivid Backup for MainWP allows Reflected XSS.This issue affects WPvivid Backup for MainWP: from n/a through 0.9.32. | 2024-06-04 | | |
| wpweaver--Weaver Xtreme Theme Support | The Weaver Xtreme Theme Support plugin for WordPress is vulnerable to Stored Cross-Site Scripting via the plugin's div shortcode in all versions up to, and including, 6.4 due to insufficient input sanitization and output escaping on user supplied attributes. This makes it possible for authenticated attackers, with contributor-level access and above, to inject arbitrary web scripts in pages that will execute whenever a user accesses an injected page. | 2024-06-05 | | |
| wpxpo--Post Grid Gutenberg Blocks and WordPress Blog Plugin PostX | The Post Grid Gutenberg Blocks and WordPress Blog Plugin - PostX plugin for WordPress is vulnerable to Stored Cross-Site Scripting via the filterMobileText parameter in all versions up to, and including, 4.0.4 due to insufficient input sanitization and output escaping. This makes it possible for authenticated attackers, with Contributor-level access and above, to inject arbitrary web scripts in pages that will execute whenever a user accesses an injected page. | 2024-06-08 | | |
| Xabier Miranda--WP Back Button | Cross Site Scripting (XSS) vulnerability in Xabier Miranda WP Back Button allows Stored XSS.This issue affects WP Back Button: from n/a through 1.1.3. | 2024-06-03 | | |
| xootix--Login/Signup Popup ( Inline Form + Woocommerce ) | The Login/Signup Popup ( Inline Form + Woocommerce ) plugin for WordPress is vulnerable to unauthorized access of data due to a missing capability check on the 'export_settings' function in versions 2.7.1 to 2.7.2. This makes it possible for authenticated attackers, with Subscriber-level access and above, to read arbitrary options on affected sites. | 2024-06-06 | | |
| YITH--YITH Custom Login | Improper Neutralization of Input During Web Page Generation (XSS or 'Cross-site Scripting') vulnerability in YITH YITH Custom Login allows Stored XSS.This issue affects YITH Custom Login: from n/a through 1.7.0. | 2024-06-08 | | |
| YITH--YITH WooCommerce Tab Manager | Improper Neutralization of Input During Web Page Generation (XSS or 'Cross-site Scripting') vulnerability in YITH YITH WooCommerce Tab Manager allows Stored XSS.This issue affects YITH WooCommerce Tab Manager: from n/a through 1.35.0. | 2024-06-08 | | |
| YITH--YITH WooCommerce Wishlist | Improper Neutralization of Input During Web Page Generation (XSS or 'Cross-site Scripting') vulnerability in YITH YITH WooCommerce Wishlist allows Stored XSS.This issue affects YITH WooCommerce Wishlist: from n/a through 3.32.0. | 2024-06-03 | | |
| yonifre--Maspik Spam blacklist | Authentication Bypass by Spoofing vulnerability in yonifre Maspik - Spam blacklist allows Accessing Functionality Not Properly Constrained by ACLs.This issue affects Maspik - Spam blacklist: from n/a through 0.10.3. | 2024-06-04 | | |
| zhuyi--BuddyPress Members Only | The BuddyPress Members Only plugin for WordPress is vulnerable to Sensitive Information Exposure in all versions up to, and including, 3.3.5 via the REST API. This makes it possible for unauthenticated attackers to bypass the plugin's "All Other Sections On Your Site Will be Opened to Guest" feature (when unset) and view restricted page and post content. | 2024-06-06 | | |
| zootemplate--Clever Addons for Elementor | The Clever Addons for Elementor plugin for WordPress is vulnerable to Stored Cross-Site Scripting via the CAFE Icon, CAFE Team Member, and CAFE Slider widgets in all versions up to, and including, 2.1.9 due to insufficient input sanitization and output escaping. This makes it possible for authenticated attackers, with contributor-level access and above, to inject arbitrary web scripts in pages that will execute whenever a user accesses an injected page. | 2024-06-06 | | |
ninjateam--GDPR CCPA Compliance & Cookie Consent Banner | The GDPR CCPA Compliance & Cookie Consent Banner plugin for WordPress is vulnerable to unauthorized modification of data due to a missing capability check on several functions named ajaxUpdateSettings() in all versions up to, and including, 2.7.0. This makes it possible for authenticated attackers, with Subscriber-level access and above, to modify the plugin's settings, update page content, send arbitrary emails and inject malicious web scripts. | 2024-06-07 | |
Low Vulnerabilities
| Primary Vendor -- Product | Description | Published | CVSS Score | Source & Patch Info |
|---|---|---|---|---|
| All In One WP Security & Firewall Team--All In One WP Security & Firewall | Exposure of Sensitive Information to an Unauthorized Actor vulnerability in All In One WP Security & Firewall Team All In One WP Security & Firewall allows Accessing Functionality Not Properly Constrained by ACLs.This issue affects All In One WP Security & Firewall: from n/a through 5.2.4. | 2024-06-04 | | |
| Born05--CraftCMS Plugin - Two-Factor Authentication | The CraftCMS plugin Two-Factor Authentication in versions 3.3.1, 3.3.2 and 3.3.3 discloses the password hash of the currently authenticated user after submitting a valid TOTP. | 2024-06-06 | | |
| David Vongries--Ultimate Dashboard | Exposure of Sensitive Information to an Unauthorized Actor vulnerability in David Vongries Ultimate Dashboard allows Accessing Functionality Not Properly Constrained by ACLs.This issue affects Ultimate Dashboard: from n/a through 3.7.10. | 2024-06-04 | | |
| Event Espresso--Event Espresso 4 Decaf | Missing Authorization vulnerability in Event Espresso Event Espresso 4 Decaf allows Functionality Misuse.This issue affects Event Espresso 4 Decaf: from n/a through 4.10.44.Decaf. | 2024-06-03 | | |
| evmos--evmos | Evmos is the Ethereum Virtual Machine (EVM) Hub on the Cosmos Network. The spendable balance is not updated properly when delegating vested tokens. The issue allows a clawback vesting account to anticipate the release of unvested tokens. This vulnerability is fixed in 18.0.0. | 2024-06-06 | | |
| Florent Maillefaud--WP Maintenance | Authentication Bypass by Spoofing vulnerability in WP Maintenance allows Accessing Functionality Not Properly Constrained by ACLs.This issue affects WP Maintenance: from n/a through 6.1.3. | 2024-06-04 | | |
| LWS--LWS Hide Login | Exposure of Sensitive Information to an Unauthorized Actor vulnerability in LWS LWS Hide Login allows Accessing Functionality Not Properly Constrained by ACLs.This issue affects LWS Hide Login: from n/a through 2.1.8. | 2024-06-04 | | |
| n/a--Likeshop | A vulnerability was found in Likeshop up to 2.5.7 and classified as problematic. This issue affects some unknown processing of the file /admin of the component Merchandise Handler. The manipulation leads to cross site scripting. The attack may be initiated remotely. The identifier VDB-267449 was assigned to this vulnerability. | 2024-06-08 | | |
| n/a--n/a | An issue was discovered in Samsung Mobile Processor, Automotive Processor, and Modem Exynos 9820, 9825, 980, 990, 850, 1080, 2100, 2200, 1280, 1380, 1330, Modem 5123, Modem 5300, and Auto T5123. The baseband software does not properly check replay protection specified by the NAS (Non-Access-Stratum) module. This can lead to denial of service. | 2024-06-05 | | |
| n/a--n/a | An issue was discovered in Samsung Mobile Processor, Automotive Processor, and Modem Exynos 9820, 9825, 980, 990, 850, 1080, 2100, 2200, 1280, 1380, 1330, Modem 5123, Modem 5300, and Auto T5123. The baseband software does not properly check format types specified by the NAS (Non-Access-Stratum) module. This can lead to bypass of authentication. | 2024-06-05 | | |
| Webcraftic--Hide login page | Exposure of Sensitive Information to an Unauthorized Actor vulnerability in Webcraftic Hide login page allows Accessing Functionality Not Properly Constrained by ACLs.This issue affects Hide login page: from n/a through 1.1.9. | 2024-06-04 | | |
| WpDevArt--Booking calendar, Appointment Booking System | External Control of Assumed-Immutable Web Parameter vulnerability in WpDevArt Booking calendar, Appointment Booking System allows Manipulating Hidden Fields.This issue affects Booking calendar, Appointment Booking System: from n/a through 3.2.3. | 2024-06-03 | | |
| wpdevart--Coming soon and Maintenance mode | Authentication Bypass by Spoofing vulnerability in wpdevart Coming soon and Maintenance mode allows Accessing Functionality Not Properly Constrained by ACLs.This issue affects Coming soon and Maintenance mode: from n/a through 3.7.3. | 2024-06-04 | | |
| WPServeur, NicolasKulka, wpformation--WPS Hide Login | Exposure of Sensitive Information to an Unauthorized Actor vulnerability in WPServeur, NicolasKulka, wpformation WPS Hide Login allows Accessing Functionality Not Properly Constrained by ACLs.This issue affects WPS Hide Login: from n/a through 1.9.11. | 2024-06-04 | |
Severity Not Yet Assigned
| Primary Vendor -- Product | Description | Published | CVSS Score | Source & Patch Info |
|---|---|---|---|---|
| A10--Thunder ADC | A10 Thunder ADC CsrRequestView Command Injection Remote Code Execution Vulnerability. This vulnerability allows remote attackers to execute arbitrary code on affected installations of A10 Thunder ADC. Authentication is required to exploit this vulnerability. The specific flaw exists within the CsrRequestView class. The issue results from the lack of proper validation of a user-supplied string before using it to execute a system call. An attacker can leverage this vulnerability to execute code in the context of a10user. Was ZDI-CAN-22517. | 2024-06-06 | not yet calculated | |
| A10--Thunder ADC | A10 Thunder ADC Incorrect Permission Assignment Local Privilege Escalation Vulnerability. This vulnerability allows local attackers to escalate privileges on affected installations of A10 Thunder ADC. An attacker must first obtain the ability to execute low-privileged code on the target system in order to exploit this vulnerability. The specific flaw exists within the installer. The issue results from incorrect permissions on a file. An attacker can leverage this vulnerability to escalate privileges and execute arbitrary code in the context of root. Was ZDI-CAN-22754. | 2024-06-06 | not yet calculated | |
| Apache Software Foundation--Apache OFBiz | Improper Limitation of a Pathname to a Restricted Directory ('Path Traversal') vulnerability in Apache OFBiz. This issue affects Apache OFBiz: before 18.12.14. Users are recommended to upgrade to version 18.12.14, which fixes the issue. | 2024-06-04 | not yet calculated | |
| Arm Ltd--Bifrost GPU Kernel Driver | Use After Free vulnerability in Arm Ltd Bifrost GPU Kernel Driver, Arm Ltd Valhall GPU Kernel Driver allows a local non-privileged user to make improper GPU memory processing operations to gain access to already freed memory.This issue affects Bifrost GPU Kernel Driver: from r34p0 through r40p0; Valhall GPU Kernel Driver: from r34p0 through r40p0. | 2024-06-07 | not yet calculated | |
| berriai--berriai/litellm | BerriAI's litellm, in its latest version, is vulnerable to arbitrary file deletion due to improper input validation on the `/audio/transcriptions` endpoint. An attacker can exploit this vulnerability by sending a specially crafted request that includes a file path to the server, which then deletes the specified file without proper authorization or validation. This vulnerability is present in the code where `os.remove(file.filename)` is used to delete a file, allowing any user to delete critical files on the server such as SSH keys, SQLite databases, or configuration files. | 2024-06-06 | not yet calculated | |
| berriai--berriai/litellm | A code injection vulnerability exists in the berriai/litellm application, version 1.34.6, due to the use of unvalidated input in the eval function within the secret management system. This vulnerability requires a valid Google KMS configuration file to be exploitable. Specifically, by setting the `UI_LOGO_PATH` variable to a remote server address in the `get_image` function, an attacker can write a malicious Google KMS configuration file to the `cached_logo.jpg` file. This file can then be used to execute arbitrary code by assigning malicious code to the `SAVE_CONFIG_TO_DB` environment variable, leading to full system control. The vulnerability is contingent upon the use of the Google KMS feature. | 2024-06-06 | not yet calculated | |
| berriai--berriai/litellm | A blind SQL injection vulnerability exists in the berriai/litellm application, specifically within the '/team/update' process. The vulnerability arises due to the improper handling of the 'user_id' parameter in the raw SQL query used for deleting users. An attacker can exploit this vulnerability by injecting malicious SQL commands through the 'user_id' parameter, leading to potential unauthorized access to sensitive information such as API keys, user information, and tokens stored in the database. The affected version is 1.27.14. | 2024-06-06 | not yet calculated | |
| berriai--berriai/litellm | An SQL Injection vulnerability exists in the berriai/litellm repository, specifically within the `/global/spend/logs` endpoint. The vulnerability arises due to improper neutralization of special elements used in an SQL command. The affected code constructs an SQL query by concatenating an unvalidated `api_key` parameter directly into the query, making it susceptible to SQL Injection if the `api_key` contains malicious data. This issue affects the latest version of the repository. Successful exploitation of this vulnerability could lead to unauthorized access, data manipulation, exposure of confidential information, and denial of service (DoS). | 2024-06-06 | not yet calculated | |
| Canonical Ltd.--Apport | There is a race condition in the 'replaced executable' detection that, with the correct local configuration, allow an attacker to execute arbitrary code as root. | 2024-06-03 | not yet calculated | |
| Canonical Ltd.--Apport | Apport can be tricked into connecting to arbitrary sockets as the root user | 2024-06-03 | not yet calculated | |
| Canonical Ltd.--Apport | ~/.config/apport/settings parsing is vulnerable to "billion laughs" attack | 2024-06-04 | not yet calculated | |
| Canonical Ltd.--Apport | is_closing_session() allows users to fill up apport.log | 2024-06-04 | not yet calculated | |
| Canonical Ltd.--Apport | is_closing_session() allows users to create arbitrary tcp dbus connections | 2024-06-04 | not yet calculated | |
| Canonical Ltd.--Apport | is_closing_session() allows users to consume RAM in the Apport process | 2024-06-04 | not yet calculated | |
| Canonical Ltd.--Apport | Apport does not disable python crash handler before entering chroot | 2024-06-04 | not yet calculated | |
| Canonical Ltd.--Apport | Apport argument parsing mishandles filename splitting on older kernels resulting in argument spoofing | 2024-06-04 | not yet calculated | |
| Canonical Ltd.--subiquity | Subiquity Shows Guided Storage Passphrase in Plaintext with Read-all Permissions | 2024-06-03 | not yet calculated | |
| Chromium--libvpx | There exists interger overflows in libvpx in versions prior to 1.14.1. Calling vpx_img_alloc() with a large value of the d_w, d_h, or align parameter may result in integer overflows in the calculations of buffer sizes and offsets and some fields of the returned vpx_image_t struct may be invalid. Calling vpx_img_wrap() with a large value of the d_w, d_h, or stride_align parameter may result in integer overflows in the calculations of buffer sizes and offsets and some fields of the returned vpx_image_t struct may be invalid. We recommend upgrading to version 1.14.1 or beyond | 2024-06-03 | not yet calculated | |
| CodePeople--Music Store - WordPress eCommerce | SQL injection vulnerability in Music Store - WordPress eCommerce versions prior to 1.1.14 allows a remote authenticated attacker with an administrative privilege to execute arbitrary SQL commands. Information stored in the database may be obtained or altered by the attacker. | 2024-06-07 | not yet calculated | |
| deepjavalibrary--deepjavalibrary/djl | A TarSlip vulnerability exists in the deepjavalibrary/djl, affecting version 0.26.0 and fixed in version 0.27.0. This vulnerability allows an attacker to manipulate file paths within tar archives to overwrite arbitrary files on the target system. Exploitation of this vulnerability could lead to remote code execution, privilege escalation, data theft or manipulation, and denial of service. The vulnerability is due to improper validation of file paths during the extraction of tar files, as demonstrated in multiple occurrences within the library's codebase, including but not limited to the files_util.py and extract_imagenet.py scripts. | 2024-06-06 | not yet calculated | |
| EMTA Grup--PDKS | Improper Access Control vulnerability in EMTA Grup PDKS allows Exploiting Incorrectly Configured Access Control Security Levels.This issue affects PDKS: before 20240603. NOTE: The vendor was contacted early about this disclosure but did not respond in any way. | 2024-06-03 | not yet calculated | |
| Fortra--Tripwire Enterprise | An authentication bypass vulnerability has been identified in the REST and SOAP API components of Tripwire Enterprise (TE) 9.1.0 when TE is configured to use LDAP/Active Directory SAML authentication and its optional "Auto-synchronize LDAP Users, Roles, and Groups" feature is enabled. This vulnerability allows unauthenticated attackers to bypass authentication if a valid username is known. Exploitation of this vulnerability could allow remote attackers to gain privileged access to the APIs and lead to unauthorized information disclosure or modification. | 2024-06-03 | not yet calculated | |
| gaizhenbiao--gaizhenbiao/chuanhuchatgpt | The gaizhenbiao/chuanhuchatgpt application is vulnerable to a path traversal attack due to its use of an outdated gradio component. The application is designed to restrict user access to resources within the `web_assets` folder. However, the outdated version of gradio it employs is susceptible to path traversal, as identified in CVE-2023-51449. This vulnerability allows unauthorized users to bypass the intended restrictions and access sensitive files, such as `config.json`, which contains API keys. The issue affects the latest version of chuanhuchatgpt prior to the fixed version released on 20240305. | 2024-06-06 | not yet calculated | |
| gaizhenbiao--gaizhenbiao/chuanhuchatgpt | A stored Cross-Site Scripting (XSS) vulnerability existed in version (20240121) of gaizhenbiao/chuanhuchatgpt due to inadequate sanitization and validation of model output data. Despite user-input validation efforts, the application fails to properly sanitize or validate the output from the model, allowing for the injection and execution of malicious JavaScript code within the context of a user's browser. This vulnerability can lead to the execution of arbitrary JavaScript code in the context of other users' browsers, potentially resulting in the hijacking of victims' browsers. | 2024-06-06 | not yet calculated | |
| gaizhenbiao--gaizhenbiao/chuanhuchatgpt | In gaizhenbiao/chuanhuchatgpt, specifically the version tagged as 20240121, there exists a vulnerability due to improper access control mechanisms. This flaw allows an authenticated attacker to bypass intended access restrictions and read the `history` files of other users, potentially leading to unauthorized access to sensitive information. The vulnerability is present in the application's handling of access control for the `history` path, where no adequate mechanism is in place to prevent an authenticated user from accessing another user's chat history files. This issue poses a significant risk as it could allow attackers to obtain sensitive information from the chat history of other users. | 2024-06-06 | not yet calculated | |
| gaizhenbiao--gaizhenbiao/chuanhuchatgpt | An improper access control vulnerability exists in the gaizhenbiao/chuanhuchatgpt application, specifically in version 20240410. This vulnerability allows any user on the server to access the chat history of any other user without requiring any form of interaction between the users. Exploitation of this vulnerability could lead to data breaches, including the exposure of sensitive personal details, financial data, or confidential conversations. Additionally, it could facilitate identity theft and manipulation or fraud through the unauthorized access to users' chat histories. This issue is due to insufficient access control mechanisms in the application's handling of chat history data. | 2024-06-04 | not yet calculated | |
| gaizhenbiao--gaizhenbiao/chuanhuchatgpt | A timing attack vulnerability exists in the gaizhenbiao/chuanhuchatgpt repository, specifically within the password comparison logic. The vulnerability is present in version 20240310 of the software, where passwords are compared using the '=' operator in Python. This method of comparison allows an attacker to guess passwords based on the timing of each character's comparison. The issue arises from the code segment that checks a password for a particular username, which can lead to the exposure of sensitive information to an unauthorized actor. An attacker exploiting this vulnerability could potentially guess user passwords, compromising the security of the system. | 2024-06-06 | not yet calculated | |
| gaizhenbiao--gaizhenbiao/chuanhuchatgpt | gaizhenbiao/chuanhuchatgpt is vulnerable to an unrestricted file upload vulnerability due to insufficient validation of uploaded file types in its `/upload` endpoint. Specifically, the `handle_file_upload` function does not sanitize or validate the file extension or content type of uploaded files, allowing attackers to upload files with arbitrary extensions, including HTML files containing XSS payloads and Python files. This vulnerability, present in the latest version as of 20240310, could lead to stored XSS attacks and potentially result in remote code execution (RCE) on the server hosting the application. | 2024-06-06 | not yet calculated | |
| Go standard library--archive/zip | The archive/zip package's handling of certain types of invalid zip files differs from the behavior of most zip implementations. This misalignment could be exploited to create an zip file with contents that vary depending on the implementation reading the file. The archive/zip package now rejects files containing these errors. | 2024-06-05 | not yet calculated | |
| Go standard library--net/netip | The various Is methods (IsPrivate, IsLoopback, etc) did not work as expected for IPv4-mapped IPv6 addresses, returning false for addresses which would return true in their traditional IPv4 forms. | 2024-06-05 | not yet calculated | |
| Google--Omaha | Inappropriate implementation in Google Updator prior to 1.3.36.351 in Google Chrome allowed a local attacker to perform privilege escalation via a malicious file. (Chromium security severity: High) | 2024-06-07 | not yet calculated | |
| Google--Omaha | Inappropriate implementation in Google Updator prior to 1.3.36.351 in Google Chrome allowed a local attacker to bypass discretionary access control via a malicious file. (Chromium security severity: High) | 2024-06-07 | not yet calculated | |
| gradio-app--gradio-app/gradio | A command injection vulnerability exists in the gradio-app/gradio repository, specifically within the 'test-functional.yml' workflow. The vulnerability arises due to improper neutralization of special elements used in a command, allowing for unauthorized modification of the base repository or secrets exfiltration. The issue affects versions up to and including '@gradio/[email protected]'. The flaw is present in the workflow's handling of GitHub context information, where it echoes the full name of the head repository, the head branch, and the workflow reference without adequate sanitization. This could potentially lead to the exfiltration of sensitive secrets such as 'GITHUB_TOKEN', 'COMMENT_TOKEN', and 'CHROMATIC_PROJECT_TOKEN'. | 2024-06-04 | not yet calculated | |
| gradio-app--gradio-app/gradio | The 'deploy-website.yml' workflow in the gradio-app/gradio repository, specifically in the 'main' branch, is vulnerable to secrets exfiltration due to improper authorization. The vulnerability arises from the workflow's explicit checkout and execution of code from a fork, which is unsafe as it allows the running of untrusted code in an environment with access to push to the base repository and access secrets. This flaw could lead to the exfiltration of sensitive secrets such as GITHUB_TOKEN, HF_TOKEN, VERCEL_ORG_ID, VERCEL_PROJECT_ID, COMMENT_TOKEN, AWSACCESSKEYID, AWSSECRETKEY, and VERCEL_TOKEN. The vulnerability is present in the workflow file located at https://github.com/gradio-app/gradio/blob/72f4ca88ab569aae47941b3fb0609e57f2e13a27/.github/workflows/deploy-website.yml. | 2024-06-04 | not yet calculated | |
| gradio-app--gradio-app/gradio | A Server-Side Request Forgery (SSRF) vulnerability exists in the gradio-app/gradio version 4.21.0, specifically within the `/queue/join` endpoint and the `save_url_to_cache` function. The vulnerability arises when the `path` value, obtained from the user and expected to be a URL, is used to make an HTTP request without sufficient validation checks. This flaw allows an attacker to send crafted requests that could lead to unauthorized access to the local network or the AWS metadata endpoint, thereby compromising the security of internal servers. | 2024-06-06 | not yet calculated | |
| gradio-app--gradio-app/gradio | A local file inclusion vulnerability exists in the JSON component of gradio-app/gradio version 4.25. The vulnerability arises from improper input validation in the `postprocess()` function within `gradio/components/json_component.py`, where a user-controlled string is parsed as JSON. If the parsed JSON object contains a `path` key, the specified file is moved to a temporary directory, making it possible to retrieve it later via the `/file=..` endpoint. This issue is due to the `processing_utils.move_files_to_cache()` function traversing any object passed to it, looking for a dictionary with a `path` key, and then copying the specified file to a temporary directory. The vulnerability can be exploited by an attacker to read files on the remote system, posing a significant security risk. | 2024-06-06 | not yet calculated | |
| GStreamer--GStreamer | GStreamer AV1 Video Parsing Stack-based Buffer Overflow Remote Code Execution Vulnerability. This vulnerability allows remote attackers to execute arbitrary code on affected installations of GStreamer. Interaction with this library is required to exploit this vulnerability but attack vectors may vary depending on the implementation. The specific flaw exists within the parsing of tile list data within AV1-encoded video files. The issue results from the lack of proper validation of the length of user-supplied data prior to copying it to a fixed-length stack-based buffer. An attacker can leverage this vulnerability to execute code in the context of the current process. Was ZDI-CAN-22873. | 2024-06-07 | not yet calculated | |
| h2oai--h2oai/h2o-3 | In h2oai/h2o-3 version 3.40.0.4, an exposure of sensitive information vulnerability exists due to an arbitrary system path lookup feature. This vulnerability allows any remote user to view full paths in the entire file system where h2o-3 is hosted. Specifically, the issue resides in the Typeahead API call, which when requested with a typeahead lookup of '/', exposes the root filesystem including directories such as /home, /usr, /bin, among others. This vulnerability could allow attackers to explore the entire filesystem, and when combined with a Local File Inclusion (LFI) vulnerability, could make exploitation of the server trivial. | 2024-06-06 | not yet calculated | |
| imartinez--imartinez/privategpt | A Server-Side Request Forgery (SSRF) vulnerability exists in the file upload section of imartinez/privategpt version 0.5.0. This vulnerability allows attackers to send crafted requests that could result in unauthorized access to the local network and potentially sensitive information. Specifically, by manipulating the 'path' parameter in a file upload request, an attacker can cause the application to make arbitrary requests to internal services, including the AWS metadata endpoint. This issue could lead to the exposure of internal servers and sensitive data. | 2024-06-06 | not yet calculated | |
| Japan System Techniques Co., Ltd.--UNIVERSAL PASSPORT RX | Cross-site scripting vulnerability exists in UNIVERSAL PASSPORT RX versions 1.0.0 to 1.0.7, which may allow a remote authenticated attacker to execute an arbitrary script on the web browser of the user who is using the product. | 2024-06-03 | not yet calculated | |
| Japan System Techniques Co., Ltd.--UNIVERSAL PASSPORT RX | Cross-site scripting vulnerability exists in UNIVERSAL PASSPORT RX versions 1.0.0 to 1.0.8, which may allow a remote authenticated attacker with an administrative privilege to execute an arbitrary script on the web browser of the user who is using the product. | 2024-06-03 | not yet calculated | |
| Johnson Controls--Software House CCURE 9000 | Under certain circumstances the Microsoft® Internet Information Server (IIS) used to host the C•CURE 9000 Web Server will log Microsoft Windows credential details within logs. There is no impact to non-web service interfaces C•CURE 9000 or prior versions | 2024-06-06 | not yet calculated | |
| Johnson Controls--Software House iSTAR Pro, ICU | Under certain circumstances communications between the ICU tool and an iSTAR Pro door controller is susceptible to Machine-in-the-Middle attacks which could impact door control and configuration. | 2024-06-06 | not yet calculated | |
| Kofax--Power PDF | Kofax Power PDF JPF File Parsing Out-Of-Bounds Write Remote Code Execution Vulnerability. This vulnerability allows remote attackers to execute arbitrary code on affected installations of Kofax Power PDF. User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file. The specific flaw exists within the parsing of JPF files. The issue results from the lack of proper validation of user-supplied data, which can result in a write past the end of an allocated object. An attacker can leverage this vulnerability to execute code in the context of the current process. Was ZDI-CAN-22092. | 2024-06-06 | not yet calculated | |
| Kofax--Power PDF | Kofax Power PDF PSD File Parsing Heap-based Buffer Overflow Remote Code Execution Vulnerability. This vulnerability allows remote attackers to execute arbitrary code on affected installations of Kofax Power PDF. User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file. The specific flaw exists within the parsing of PSD files. The issue results from the lack of proper validation of the length of user-supplied data prior to copying it to a fixed-length heap-based buffer. An attacker can leverage this vulnerability to execute code in the context of the current process. Was ZDI-CAN-22917. | 2024-06-06 | not yet calculated | |
| Kofax--Power PDF | Kofax Power PDF PDF File Parsing Out-Of-Bounds Write Remote Code Execution Vulnerability. This vulnerability allows remote attackers to execute arbitrary code on affected installations of Kofax Power PDF. User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file. The specific flaw exists within the parsing of PDF files. The issue results from the lack of proper validation of user-supplied data, which can result in a write past the end of an allocated buffer. An attacker can leverage this vulnerability to execute code in the context of the current process. Was ZDI-CAN-22918. | 2024-06-06 | not yet calculated | |
| Kofax--Power PDF | Kofax Power PDF PSD File Parsing Out-Of-Bounds Write Remote Code Execution Vulnerability. This vulnerability allows remote attackers to execute arbitrary code on affected installations of Kofax Power PDF. User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file. The specific flaw exists within the parsing of PSD files. The issue results from the lack of proper validation of user-supplied data, which can result in a write past the end of an allocated buffer. An attacker can leverage this vulnerability to execute code in the context of the current process. Was ZDI-CAN-22919. | 2024-06-06 | not yet calculated | |
| Kofax--Power PDF | Kofax Power PDF TGA File Parsing Out-Of-Bounds Write Remote Code Execution Vulnerability. This vulnerability allows remote attackers to execute arbitrary code on affected installations of Kofax Power PDF. User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file. The specific flaw exists within the parsing of TGA files. The issue results from the lack of proper validation of user-supplied data, which can result in a write past the end of an allocated buffer. An attacker can leverage this vulnerability to execute code in the context of the current process. Was ZDI-CAN-22920. | 2024-06-06 | not yet calculated | |
| Kofax--Power PDF | Kofax Power PDF PDF File Parsing Stack-based Buffer Overflow Remote Code Execution Vulnerability. This vulnerability allows remote attackers to execute arbitrary code on affected installations of Kofax Power PDF. User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file. The specific flaw exists within the parsing of PDF files. The issue results from the lack of proper validation of the length of user-supplied data prior to copying it to a fixed-length stack-based buffer. An attacker can leverage this vulnerability to execute code in the context of the current process. Was ZDI-CAN-22921. | 2024-06-06 | not yet calculated | |
| Kofax--Power PDF | Kofax Power PDF PDF File Parsing Memory Corruption Remote Code Execution Vulnerability. This vulnerability allows remote attackers to execute arbitrary code on affected installations of Kofax Power PDF. User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file. The specific flaw exists within the parsing of PDF files. The issue results from the lack of proper validation of user-supplied data, which can result in a memory corruption condition. An attacker can leverage this vulnerability to execute code in the context of the current process. Was ZDI-CAN-22930. | 2024-06-06 | not yet calculated | |
| Kofax--Power PDF | Kofax Power PDF AcroForm Annotation Out-Of-Bounds Read Information Disclosure Vulnerability. This vulnerability allows remote attackers to disclose sensitive information on affected installations of Kofax Power PDF. User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file. The specific flaw exists within the handling of Annotation objects in AcroForms. The issue results from the lack of proper validation of user-supplied data, which can result in a read past the end of an allocated buffer. An attacker can leverage this in conjunction with other vulnerabilities to execute arbitrary code in the context of the current process. Was ZDI-CAN-22933. | 2024-06-06 | not yet calculated | |
| kubeflow--kubeflow/kubeflow | kubeflow/kubeflow is vulnerable to a Regular Expression Denial of Service (ReDoS) attack due to inefficient regular expression complexity in its email validation mechanism. An attacker can remotely exploit this vulnerability without authentication by providing specially crafted input that causes the application to consume an excessive amount of CPU resources. This vulnerability affects the latest version of kubeflow/kubeflow, specifically within the centraldashboard-angular backend component. The impact of exploiting this vulnerability includes resource exhaustion, and service disruption. | 2024-06-06 | not yet calculated | |
| langchain-ai--langchain-ai/langchain | A Denial-of-Service (DoS) vulnerability exists in the `SitemapLoader` class of the `langchain-ai/langchain` repository, affecting all versions. The `parse_sitemap` method, responsible for parsing sitemaps and extracting URLs, lacks a mechanism to prevent infinite recursion when a sitemap URL refers to the current sitemap itself. This oversight allows for the possibility of an infinite loop, leading to a crash by exceeding the maximum recursion depth in Python. This vulnerability can be exploited to occupy server socket/port resources and crash the Python process, impacting the availability of services relying on this functionality. | 2024-06-06 | not yet calculated | |
| langchain-ai--langchain-ai/langchain | A Server-Side Request Forgery (SSRF) vulnerability exists in the Web Research Retriever component of langchain-ai/langchain version 0.1.5. The vulnerability arises because the Web Research Retriever does not restrict requests to remote internet addresses, allowing it to reach local addresses. This flaw enables attackers to execute port scans, access local services, and in some scenarios, read instance metadata from cloud environments. The vulnerability is particularly concerning as it can be exploited to abuse the Web Explorer server as a proxy for web attacks on third parties and interact with servers in the local network, including reading their response data. This could potentially lead to arbitrary code execution, depending on the nature of the local services. The vulnerability is limited to GET requests, as POST requests are not possible, but the impact on confidentiality, integrity, and availability is significant due to the potential for stolen credentials and state-changing interactions with internal APIs. | 2024-06-06 | not yet calculated | |
| libaom--libaom | Integer overflow in libaom internal function img_alloc_helper can lead to heap buffer overflow. This function can be reached via 3 callers: * Calling aom_img_alloc() with a large value of the d_w, d_h, or align parameter may result in integer overflows in the calculations of buffer sizes and offsets and some fields of the returned aom_image_t struct may be invalid. * Calling aom_img_wrap() with a large value of the d_w, d_h, or align parameter may result in integer overflows in the calculations of buffer sizes and offsets and some fields of the returned aom_image_t struct may be invalid. * Calling aom_img_alloc_with_border() with a large value of the d_w, d_h, align, size_align, or border parameter may result in integer overflows in the calculations of buffer sizes and offsets and some fields of the returned aom_image_t struct may be invalid. | 2024-06-05 | not yet calculated | |
| lightning-ai--lightning-ai/pytorch-lightning | A remote code execution (RCE) vulnerability exists in the lightning-ai/pytorch-lightning library version 2.2.1 due to improper handling of deserialized user input and mismanagement of dunder attributes by the `deepdiff` library. The library uses `deepdiff.Delta` objects to modify application state based on frontend actions. However, it is possible to bypass the intended restrictions on modifying dunder attributes, allowing an attacker to construct a serialized delta that passes the deserializer whitelist and contains dunder attributes. When processed, this can be exploited to access other modules, classes, and instances, leading to arbitrary attribute write and total RCE on any self-hosted pytorch-lightning application in its default configuration, as the delta endpoint is enabled by default. | 2024-06-06 | not yet calculated | |
| Linux--Linux | In the Linux kernel, the following vulnerability has been resolved: drm/vmwgfx: Fix invalid reads in fence signaled events Correctly set the length of the drm_event to the size of the structure that's actually used. The length of the drm_event was set to the parent structure instead of to the drm_vmw_event_fence which is supposed to be read. drm_read uses the length parameter to copy the event to the user space thus resuling in oob reads. | 2024-06-03 | not yet calculated | |
| Linux--Linux | In the Linux kernel, the following vulnerability has been resolved: thermal/debugfs: Fix two locking issues with thermal zone debug With the current thermal zone locking arrangement in the debugfs code, user space can open the "mitigations" file for a thermal zone before the zone's debugfs pointer is set which will result in a NULL pointer dereference in tze_seq_start(). Moreover, thermal_debug_tz_remove() is not called under the thermal zone lock, so it can run in parallel with the other functions accessing the thermal zone's struct thermal_debugfs object. Then, it may clear tz->debugfs after one of those functions has checked it and the struct thermal_debugfs object may be freed prematurely. To address the first problem, pass a pointer to the thermal zone's struct thermal_debugfs object to debugfs_create_file() in thermal_debug_tz_add() and make tze_seq_start(), tze_seq_next(), tze_seq_stop(), and tze_seq_show() retrieve it from s->private instead of a pointer to the thermal zone object. This will ensure that tz_debugfs will be valid across the "mitigations" file accesses until thermal_debugfs_remove_id() called by thermal_debug_tz_remove() removes that file. To address the second problem, use tz->lock in thermal_debug_tz_remove() around the tz->debugfs value check (in case the same thermal zone is removed at the same time in two different threads) and its reset to NULL. Cc :6.8+ <[email protected]> # 6.8+ | 2024-06-03 | not yet calculated | |
| Linux--Linux | In the Linux kernel, the following vulnerability has been resolved: net: ks8851: Queue RX packets in IRQ handler instead of disabling BHs Currently the driver uses local_bh_disable()/local_bh_enable() in its IRQ handler to avoid triggering net_rx_action() softirq on exit from netif_rx(). The net_rx_action() could trigger this driver .start_xmit callback, which is protected by the same lock as the IRQ handler, so calling the .start_xmit from netif_rx() from the IRQ handler critical section protected by the lock could lead to an attempt to claim the already claimed lock, and a hang. The local_bh_disable()/local_bh_enable() approach works only in case the IRQ handler is protected by a spinlock, but does not work if the IRQ handler is protected by mutex, i.e. this works for KS8851 with Parallel bus interface, but not for KS8851 with SPI bus interface. Remove the BH manipulation and instead of calling netif_rx() inside the IRQ handler code protected by the lock, queue all the received SKBs in the IRQ handler into a queue first, and once the IRQ handler exits the critical section protected by the lock, dequeue all the queued SKBs and push them all into netif_rx(). At this point, it is safe to trigger the net_rx_action() softirq, since the netif_rx() call is outside of the lock that protects the IRQ handler. | 2024-06-03 | not yet calculated | |
| Linux--Linux | In the Linux kernel, the following vulnerability has been resolved: tracefs: Reset permissions on remount if permissions are options There's an inconsistency with the way permissions are handled in tracefs. Because the permissions are generated when accessed, they default to the root inode's permission if they were never set by the user. If the user sets the permissions, then a flag is set and the permissions are saved via the inode (for tracefs files) or an internal attribute field (for eventfs). But if a remount happens that specify the permissions, all the files that were not changed by the user gets updated, but the ones that were are not. If the user were to remount the file system with a given permission, then all files and directories within that file system should be updated. This can cause security issues if a file's permission was updated but the admin forgot about it. They could incorrectly think that remounting with permissions set would update all files, but miss some. For example: # cd /sys/kernel/tracing # chgrp 1002 current_tracer # ls -l [..] -rw-r----- 1 root root 0 May 1 21:25 buffer_size_kb -rw-r----- 1 root root 0 May 1 21:25 buffer_subbuf_size_kb -r--r----- 1 root root 0 May 1 21:25 buffer_total_size_kb -rw-r----- 1 root lkp 0 May 1 21:25 current_tracer -rw-r----- 1 root root 0 May 1 21:25 dynamic_events -r--r----- 1 root root 0 May 1 21:25 dyn_ftrace_total_info -r--r----- 1 root root 0 May 1 21:25 enabled_functions Where current_tracer now has group "lkp". # mount -o remount,gid=1001 . # ls -l -rw-r----- 1 root tracing 0 May 1 21:25 buffer_size_kb -rw-r----- 1 root tracing 0 May 1 21:25 buffer_subbuf_size_kb -r--r----- 1 root tracing 0 May 1 21:25 buffer_total_size_kb -rw-r----- 1 root lkp 0 May 1 21:25 current_tracer -rw-r----- 1 root tracing 0 May 1 21:25 dynamic_events -r--r----- 1 root tracing 0 May 1 21:25 dyn_ftrace_total_info -r--r----- 1 root tracing 0 May 1 21:25 enabled_functions Everything changed but the "current_tracer". Add a new link list that keeps track of all the tracefs_inodes which has the permission flags that tell if the file/dir should use the root inode's permission or not. Then on remount, clear all the flags so that the default behavior of using the root inode's permission is done for all files and directories. | 2024-06-03 | not yet calculated | |
| Linux--Linux | In the Linux kernel, the following vulnerability has been resolved: fs/9p: only translate RWX permissions for plain 9P2000 Garbage in plain 9P2000's perm bits is allowed through, which causes it to be able to set (among others) the suid bit. This was presumably not the intent since the unix extended bits are handled explicitly and conditionally on .u. | 2024-06-03 | not yet calculated | |
| Linux--Linux | In the Linux kernel, the following vulnerability has been resolved: remoteproc: mediatek: Make sure IPI buffer fits in L2TCM The IPI buffer location is read from the firmware that we load to the System Companion Processor, and it's not granted that both the SRAM (L2TCM) size that is defined in the devicetree node is large enough for that, and while this is especially true for multi-core SCP, it's still useful to check on single-core variants as well. Failing to perform this check may make this driver perform R/W operations out of the L2TCM boundary, resulting (at best) in a kernel panic. To fix that, check that the IPI buffer fits, otherwise return a failure and refuse to boot the relevant SCP core (or the SCP at all, if this is single core). | 2024-06-08 | not yet calculated | |
| Linux--Linux | In the Linux kernel, the following vulnerability has been resolved: erofs: reliably distinguish block based and fscache mode When erofs_kill_sb() is called in block dev based mode, s_bdev may not have been initialised yet, and if CONFIG_EROFS_FS_ONDEMAND is enabled, it will be mistaken for fscache mode, and then attempt to free an anon_dev that has never been allocated, triggering the following warning: ============================================ ida_free called for id=0 which is not allocated. WARNING: CPU: 14 PID: 926 at lib/idr.c:525 ida_free+0x134/0x140 Modules linked in: CPU: 14 PID: 926 Comm: mount Not tainted 6.9.0-rc3-dirty #630 RIP: 0010:ida_free+0x134/0x140 Call Trace: <TASK> erofs_kill_sb+0x81/0x90 deactivate_locked_super+0x35/0x80 get_tree_bdev+0x136/0x1e0 vfs_get_tree+0x2c/0xf0 do_new_mount+0x190/0x2f0 [...] ============================================ Now when erofs_kill_sb() is called, erofs_sb_info must have been initialised, so use sbi->fsid to distinguish between the two modes. | 2024-06-08 | not yet calculated | |
| Linux--Linux | In the Linux kernel, the following vulnerability has been resolved: KEYS: trusted: Fix memory leak in tpm2_key_encode() 'scratch' is never freed. Fix this by calling kfree() in the success, and in the error case. | 2024-06-08 | not yet calculated | |
| Linux--Linux | In the Linux kernel, the following vulnerability has been resolved: Bluetooth: L2CAP: Fix div-by-zero in l2cap_le_flowctl_init() l2cap_le_flowctl_init() can cause both div-by-zero and an integer overflow since hdev->le_mtu may not fall in the valid range. Move MTU from hci_dev to hci_conn to validate MTU and stop the connection process earlier if MTU is invalid. Also, add a missing validation in read_buffer_size() and make it return an error value if the validation fails. Now hci_conn_add() returns ERR_PTR() as it can fail due to the both a kzalloc failure and invalid MTU value. divide error: 0000 [#1] PREEMPT SMP KASAN NOPTI CPU: 0 PID: 67 Comm: kworker/u5:0 Tainted: G W 6.9.0-rc5+ #20 Hardware name: QEMU Standard PC (i440FX + PIIX, 1996), BIOS 1.15.0-1 04/01/2014 Workqueue: hci0 hci_rx_work RIP: 0010:l2cap_le_flowctl_init+0x19e/0x3f0 net/bluetooth/l2cap_core.c:547 Code: e8 17 17 0c 00 66 41 89 9f 84 00 00 00 bf 01 00 00 00 41 b8 02 00 00 00 4c 89 fe 4c 89 e2 89 d9 e8 27 17 0c 00 44 89 f0 31 d2 <66> f7 f3 89 c3 ff c3 4d 8d b7 88 00 00 00 4c 89 f0 48 c1 e8 03 42 RSP: 0018:ffff88810bc0f858 EFLAGS: 00010246 RAX: 00000000000002a0 RBX: 0000000000000000 RCX: dffffc0000000000 RDX: 0000000000000000 RSI: ffff88810bc0f7c0 RDI: ffffc90002dcb66f RBP: ffff88810bc0f880 R08: aa69db2dda70ff01 R09: 0000ffaaaaaaaaaa R10: 0084000000ffaaaa R11: 0000000000000000 R12: ffff88810d65a084 R13: dffffc0000000000 R14: 00000000000002a0 R15: ffff88810d65a000 FS: 0000000000000000(0000) GS:ffff88811ac00000(0000) knlGS:0000000000000000 CS: 0010 DS: 0000 ES: 0000 CR0: 0000000080050033 CR2: 0000000020000100 CR3: 0000000103268003 CR4: 0000000000770ef0 PKRU: 55555554 Call Trace: <TASK> l2cap_le_connect_req net/bluetooth/l2cap_core.c:4902 [inline] l2cap_le_sig_cmd net/bluetooth/l2cap_core.c:5420 [inline] l2cap_le_sig_channel net/bluetooth/l2cap_core.c:5486 [inline] l2cap_recv_frame+0xe59d/0x11710 net/bluetooth/l2cap_core.c:6809 l2cap_recv_acldata+0x544/0x10a0 net/bluetooth/l2cap_core.c:7506 hci_acldata_packet net/bluetooth/hci_core.c:3939 [inline] hci_rx_work+0x5e5/0xb20 net/bluetooth/hci_core.c:4176 process_one_work kernel/workqueue.c:3254 [inline] process_scheduled_works+0x90f/0x1530 kernel/workqueue.c:3335 worker_thread+0x926/0xe70 kernel/workqueue.c:3416 kthread+0x2e3/0x380 kernel/kthread.c:388 ret_from_fork+0x5c/0x90 arch/x86/kernel/process.c:147 ret_from_fork_asm+0x1a/0x30 arch/x86/entry/entry_64.S:244 </TASK> Modules linked in: ---[ end trace 0000000000000000 ]--- | 2024-06-08 | not yet calculated | |
| Linux--Linux | In the Linux kernel, the following vulnerability has been resolved: drm/amd/display: Fix division by zero in setup_dsc_config When slice_height is 0, the division by slice_height in the calculation of the number of slices will cause a division by zero driver crash. This leaves the kernel in a state that requires a reboot. This patch adds a check to avoid the division by zero. The stack trace below is for the 6.8.4 Kernel. I reproduced the issue on a Z16 Gen 2 Lenovo Thinkpad with a Apple Studio Display monitor connected via Thunderbolt. The amdgpu driver crashed with this exception when I rebooted the system with the monitor connected. kernel: ? die (arch/x86/kernel/dumpstack.c:421 arch/x86/kernel/dumpstack.c:434 arch/x86/kernel/dumpstack.c:447) kernel: ? do_trap (arch/x86/kernel/traps.c:113 arch/x86/kernel/traps.c:154) kernel: ? setup_dsc_config (drivers/gpu/drm/amd/amdgpu/../display/dc/dsc/dc_dsc.c:1053) amdgpu kernel: ? do_error_trap (./arch/x86/include/asm/traps.h:58 arch/x86/kernel/traps.c:175) kernel: ? setup_dsc_config (drivers/gpu/drm/amd/amdgpu/../display/dc/dsc/dc_dsc.c:1053) amdgpu kernel: ? exc_divide_error (arch/x86/kernel/traps.c:194 (discriminator 2)) kernel: ? setup_dsc_config (drivers/gpu/drm/amd/amdgpu/../display/dc/dsc/dc_dsc.c:1053) amdgpu kernel: ? asm_exc_divide_error (./arch/x86/include/asm/idtentry.h:548) kernel: ? setup_dsc_config (drivers/gpu/drm/amd/amdgpu/../display/dc/dsc/dc_dsc.c:1053) amdgpu kernel: dc_dsc_compute_config (drivers/gpu/drm/amd/amdgpu/../display/dc/dsc/dc_dsc.c:1109) amdgpu After applying this patch, the driver no longer crashes when the monitor is connected and the system is rebooted. I believe this is the same issue reported for 3113. | 2024-06-08 | not yet calculated | |
| Linux--Linux | In the Linux kernel, the following vulnerability has been resolved: wifi: iwlwifi: Use request_module_nowait This appears to work around a deadlock regression that came in with the LED merge in 6.9. The deadlock happens on my system with 24 iwlwifi radios, so maybe it something like all worker threads are busy and some work that needs to complete cannot complete. [also remove unnecessary "load_module" var and now-wrong comment] | 2024-06-08 | not yet calculated | |
| lunary-ai--lunary-ai/lunary | An improper access control vulnerability exists in lunary-ai/lunary versions up to and including 1.2.2, where an admin can update any organization user to the organization owner. This vulnerability allows the elevated user to delete projects within the organization. The issue is resolved in version 1.2.7. | 2024-06-06 | not yet calculated | |
| lunary-ai--lunary-ai/lunary | In lunary-ai/lunary version v1.2.13, an improper authorization vulnerability exists that allows unauthorized users to access and manipulate projects within an organization they should not have access to. Specifically, the vulnerability is located in the `checkProjectAccess` method within the authorization middleware, which fails to adequately verify if a user has the correct permissions to access a specific project. Instead, it only checks if the user is part of the organization owning the project, overlooking the necessary check against the `account_project` table for explicit project access rights. This flaw enables attackers to gain complete control over all resources within a project, including the ability to create, update, read, and delete any resource, compromising the privacy and security of sensitive information. | 2024-06-08 | not yet calculated | |
| lunary-ai--lunary-ai/lunary | An improper access control vulnerability exists in the lunary-ai/lunary repository, specifically within the versions.patch functionality for updating prompts. Affected versions include 1.2.2 up to but not including 1.2.25. The vulnerability allows unauthorized users to update prompt details due to insufficient access control checks. This issue was addressed and fixed in version 1.2.25. | 2024-06-06 | not yet calculated | |
| lunary-ai--lunary-ai/lunary | In lunary-ai/lunary versions 1.2.2 through 1.2.25, an improper access control vulnerability allows users on the Free plan to invite other members and assign them any role, including those intended for Paid and Enterprise plans only. This issue arises due to insufficient backend validation of roles and permissions, enabling unauthorized users to join a project and potentially exploit roles and permissions not intended for their use. The vulnerability specifically affects the Team feature, where the backend fails to validate whether a user has paid for a plan before allowing them to send invite links with any role assigned. This could lead to unauthorized access and manipulation of project settings or data. | 2024-06-06 | not yet calculated | |
| lunary-ai--lunary-ai/lunary | An Insecure Direct Object Reference (IDOR) vulnerability was identified in lunary-ai/lunary, affecting versions up to and including 1.2.2. This vulnerability allows unauthorized users to view, update, or delete any dataset_prompt or dataset_prompt_variation within any dataset or project. The issue stems from improper access control checks in the dataset management endpoints, where direct references to object IDs are not adequately secured against unauthorized access. This vulnerability was fixed in version 1.2.25. | 2024-06-06 | not yet calculated | |
| lunary-ai--lunary-ai/lunary | A Privilege Escalation Vulnerability exists in lunary-ai/lunary version 1.2.2, where any user can delete any datasets due to missing authorization checks. The vulnerability is present in the dataset deletion functionality, where the application fails to verify if the user requesting the deletion has the appropriate permissions. This allows unauthorized users to send a DELETE request to the server and delete any dataset by specifying its ID. The issue is located in the datasets.delete function within the datasets index file. | 2024-06-06 | not yet calculated | |
| lunary-ai--lunary-ai/lunary | An Incorrect Authorization vulnerability exists in lunary-ai/lunary versions up to and including 1.2.2, which allows unauthenticated users to delete any dataset. The vulnerability is due to the lack of proper authorization checks in the dataset deletion endpoint. Specifically, the endpoint does not verify if the provided project ID belongs to the current user, thereby allowing any dataset to be deleted without proper authentication. This issue was fixed in version 1.2.8. | 2024-06-06 | not yet calculated | |
| lunary-ai--lunary-ai/lunary | An Improper Access Control vulnerability exists in the lunary-ai/lunary repository, affecting versions up to and including 1.2.2. The vulnerability allows unauthorized users to view any prompts in any projects by supplying a specific prompt ID to an endpoint that does not adequately verify the ownership of the prompt ID. This issue was fixed in version 1.2.25. | 2024-06-06 | not yet calculated | |
| lunary-ai--lunary-ai/lunary | In lunary-ai/lunary version 1.2.4, an account takeover vulnerability exists due to the exposure of password recovery tokens in API responses. Specifically, when a user initiates the password reset process, the recovery token is included in the response of the `GET /v1/users/me/org` endpoint, which lists all users in a team. This allows any authenticated user to capture the recovery token of another user and subsequently change that user's password without consent, effectively taking over the account. The issue lies in the inclusion of the `recovery_token` attribute in the users object returned by the API. | 2024-06-06 | not yet calculated | |
| lunary-ai--lunary-ai/lunary | In lunary-ai/lunary version 1.2.5, an improper access control vulnerability exists due to a missing permission check in the `GET /v1/users/me/org` endpoint. The platform's role definitions restrict the `Prompt Editor` role to prompt management and project viewing/listing capabilities, explicitly excluding access to user information. However, the endpoint fails to enforce this restriction, allowing users with the `Prompt Editor` role to access the full list of users in the organization. This vulnerability allows unauthorized access to sensitive user information, violating the intended access controls. | 2024-06-06 | not yet calculated | |
| lunary-ai--lunary-ai/lunary | In lunary-ai/lunary version 1.2.4, a vulnerability exists in the password recovery mechanism where the reset password token is not invalidated after use. This allows an attacker who compromises the recovery token to repeatedly change the password of a victim's account. The issue lies in the backend's handling of the reset password process, where the token, once used, is not discarded or invalidated, enabling its reuse. This vulnerability could lead to unauthorized account access if an attacker obtains the recovery token. | 2024-06-06 | not yet calculated | |
| lunary-ai--lunary-ai/lunary | A Server-Side Request Forgery (SSRF) vulnerability exists in the lunary-ai/lunary application, specifically within the endpoint '/auth/saml/tto/download-idp-xml'. The vulnerability arises due to the application's failure to validate user-supplied URLs before using them in server-side requests. An attacker can exploit this vulnerability by sending a specially crafted request to the affected endpoint, allowing them to make unauthorized requests to internal or external resources. This could lead to the disclosure of sensitive information, service disruption, or further attacks against the network infrastructure. The issue affects the latest version of the application as of the report. | 2024-06-06 | not yet calculated | |
| lunary-ai--lunary-ai/lunary | A Cross-site Scripting (XSS) vulnerability exists in the SAML metadata endpoint `/auth/saml/${org?.id}/metadata` of lunary-ai/lunary version 1.2.7. The vulnerability arises due to the application's failure to escape or validate the `orgId` parameter supplied by the user before incorporating it into the generated response. Specifically, the endpoint generates XML responses for SAML metadata, where the `orgId` parameter is directly embedded into the XML structure without proper sanitization or validation. This flaw allows an attacker to inject arbitrary JavaScript code into the generated SAML metadata page, leading to potential theft of user cookies or authentication tokens. | 2024-06-06 | not yet calculated | |
| Luxion--KeyShot Viewer | Luxion KeyShot Viewer KSP File Parsing Out-Of-Bounds Write Remote Code Execution Vulnerability. This vulnerability allows remote attackers to execute arbitrary code on affected installations of Luxion KeyShot Viewer. User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file. The specific flaw exists within the parsing of KSP files. The issue results from the lack of proper validation of user-supplied data, which can result in a write past the end of an allocated buffer. An attacker can leverage this vulnerability to execute code in the context of the current process. Was ZDI-CAN-22449. | 2024-06-06 | not yet calculated | |
| Luxion--KeyShot Viewer | Luxion KeyShot Viewer KSP File Parsing Use-After-Free Remote Code Execution Vulnerability. This vulnerability allows remote attackers to execute arbitrary code on affected installations of Luxion KeyShot Viewer. User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file. The specific flaw exists within the parsing of KSP files. The issue results from the lack of validating the existence of an object prior to performing operations on the object. An attacker can leverage this vulnerability to execute code in the context of the current process. Was ZDI-CAN-22515. | 2024-06-06 | not yet calculated | |
| Luxion--KeyShot Viewer | Luxion KeyShot Viewer KSP File Parsing Out-Of-Bounds Write Remote Code Execution Vulnerability. This vulnerability allows remote attackers to execute arbitrary code on affected installations of Luxion KeyShot Viewer. User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file. The specific flaw exists within the parsing of KSP files. The issue results from the lack of proper validation of user-supplied data, which can result in a write past the end of an allocated buffer. An attacker can leverage this vulnerability to execute code in the context of the current process. Was ZDI-CAN-22514. | 2024-06-06 | not yet calculated | |
| Luxion--KeyShot Viewer | Luxion KeyShot Viewer KSP File Parsing Stack-based Buffer Overflow Remote Code Execution Vulnerability. This vulnerability allows remote attackers to execute arbitrary code on affected installations of Luxion KeyShot Viewer. User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file. The specific flaw exists within the parsing of KSP files. The issue results from the lack of proper validation of the length of user-supplied data prior to copying it to a stack-based buffer. An attacker can leverage this vulnerability to execute code in the context of the current process. Was ZDI-CAN-22266. | 2024-06-06 | not yet calculated | |
| Luxion--KeyShot Viewer | Luxion KeyShot Viewer KSP File Parsing Out-Of-Bounds Write Remote Code Execution Vulnerability. This vulnerability allows remote attackers to execute arbitrary code on affected installations of Luxion KeyShot Viewer. User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file. The specific flaw exists within the parsing of KSP files. The issue results from the lack of proper validation of user-supplied data, which can result in a write past the end of an allocated buffer. An attacker can leverage this vulnerability to execute code in the context of the current process. Was ZDI-CAN-22267. | 2024-06-06 | not yet calculated | |
| Luxion--KeyShot | Luxion KeyShot BIP File Parsing Uncontrolled Search Path Element Remote Code Execution Vulnerability. This vulnerability allows remote attackers to execute arbitrary code on affected installations of Luxion KeyShot. User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file. The specific flaw exists within the parsing of BIP files. The issue results from loading a library from an unsecured location. An attacker can leverage this vulnerability to execute code in the context of the current process. Was ZDI-CAN-22738. | 2024-06-06 | not yet calculated | |
| man-group--man-group/dtale | man-group/dtale version 3.10.0 is vulnerable to an authentication bypass and remote code execution (RCE) due to improper input validation. The vulnerability arises from a hardcoded `SECRET_KEY` in the flask configuration, allowing attackers to forge a session cookie if authentication is enabled. Additionally, the application fails to properly restrict custom filter queries, enabling attackers to execute arbitrary code on the server by bypassing the restriction on the `/update-settings` endpoint, even when `enable_custom_filters` is not enabled. This vulnerability allows attackers to bypass authentication mechanisms and execute remote code on the server. | 2024-06-06 | not yet calculated | |
| MediaTek, Inc.--MT6298, MT6813, MT6815, MT6833, MT6835, MT6853, MT6855, MT6873, MT6875, MT6875T, MT6877, MT6878, MT6879, MT6883, MT6885, MT6889, MT6891, MT6893, MT6895, MT6895T, MT6896, MT6897, MT6980, MT6980D, MT6983, MT6990, MT8673, MT8675, MT8765, MT8766, MT8768, MT8771, MT8786, MT8791T, MT8792, MT8797, MT8798 | In modem, there is a possible information disclosure due to using risky cryptographic algorithm during connection establishment negotiation. This could lead to remote information disclosure, when weak encryption algorithm is used, with no additional execution privileges needed. User interaction is not needed for exploitation. Patch ID: MOLY00942482; Issue ID: MSV-1469. | 2024-06-03 | not yet calculated | |
| MediaTek, Inc.--MT6298, MT6813, MT6815, MT6835, MT6878, MT6879, MT6895, MT6895T, MT6896, MT6897, MT6899, MT6980, MT6980D, MT6983, MT6986, MT6986D, MT6990, MT6991, MT8673, MT8675, MT8771, MT8791T, MT8792, MT8797, MT8798 | In modem, there is a possible system crash due to improper input validation. This could lead to remote denial of service with no additional execution privileges needed. User interaction is no needed for exploitation. Patch ID: MOLY01270721; Issue ID: MSV-1479. | 2024-06-03 | not yet calculated | |
| MediaTek, Inc.--MT6298, MT6813, MT6815, MT6835, MT6878, MT6879, MT6895, MT6895T, MT6896, MT6897, MT6899, MT6980, MT6980D, MT6983, MT6986, MT6986D, MT6990, MT6991, MT8673, MT8792, MT8798 | In modem, there is a possible out of bounds write due to an incorrect bounds check. This could lead to remote denial of service with no additional execution privileges needed. User interaction is no needed for exploitation. Patch ID: MOLY01267281; Issue ID: MSV-1477. | 2024-06-03 | not yet calculated | |
| MediaTek, Inc.--MT6580, MT6739, MT6761, MT6765, MT6768, MT6779, MT6781, MT6785, MT6789, MT6833, MT6835, MT6853, MT6855, MT6873, MT6877, MT6879, MT6883, MT6885, MT6886, MT6889, MT6893, MT6895, MT6897, MT6983, MT6985, MT6989, MT8666, MT8667, MT8673, MT8676 | In dmc, there is a possible out of bounds write due to a missing bounds check. This could lead to local escalation of privilege with System execution privileges needed. User interaction is not needed for exploitation. Patch ID: ALPS08668110; Issue ID: MSV-1333. | 2024-06-03 | not yet calculated | |
| MediaTek, Inc.--MT6768, MT6781, MT6835, MT6853, MT6855, MT6877, MT6879, MT6885, MT6886, MT6893, MT6983, MT6985, MT6989 | In telephony, there is a possible information disclosure due to a missing permission check. This could lead to local information disclosure with no additional execution privileges needed. User interaction is not needed for exploitation. Patch ID: ALPS08698617; Issue ID: MSV-1394. | 2024-06-03 | not yet calculated | |
| MediaTek, Inc.--MT6813, MT6815, MT6835, MT6878, MT6897, MT6899, MT6986, MT6986D, MT6991, MT8792 | In modem, there is a possible out of bounds write due to improper input invalidation. This could lead to remote denial of service with no additional execution privileges needed. User interaction is not needed for exploitation. Patch ID: MOLY01267285; Issue ID: MSV-1462. | 2024-06-03 | not yet calculated | |
| MediaTek, Inc.--MT6833, MT6853, MT6855, MT6873, MT6875, MT6875T, MT6877, MT6883, MT6885, MT6889, MT6891, MT6893, MT8675, MT8771, MT8791T, MT8797 | In modem, there is a possible selection of less-secure algorithm during the VoWiFi IKE due to a missing DH downgrade check. This could lead to remote information disclosure with no additional execution privileges needed. User interaction is not needed for exploitation. Patch ID: MOLY01286330; Issue ID: MSV-1430. | 2024-06-03 | not yet calculated | |
| MediaTek, Inc.--MT6833, MT6853, MT6873, MT6877, MT6885, MT6893, MT8185, MT8675, MT8786, MT8789 | In eemgpu, there is a possible out of bounds write due to a missing bounds check. This could lead to local escalation of privilege with System execution privileges needed. User interaction is not needed for exploitation. Patch ID: ALPS08713302; Issue ID: MSV-1393. | 2024-06-03 | not yet calculated | |
| MediaTek, Inc.--MT6890, MT6990, MT7622 | In wlan driver, there is a possible out of bounds read due to improper input validation. This could lead to local information disclosure with System execution privileges needed. User interaction is not needed for exploitation. Patch ID: WCNCR00364733; Issue ID: MSV-1331. | 2024-06-03 | not yet calculated | |
| MediaTek, Inc.--MT6890, MT6990, MT7622 | In wlan driver, there is a possible out of bounds write due to improper input validation. This could lead to local escalation of privilege with System execution privileges needed. User interaction is not needed for exploitation. Patch ID: WCNCR00364732; Issue ID: MSV-1332. | 2024-06-03 | not yet calculated | |
| MediaTek, Inc.--MT6890, MT7622 | In wlan service, there is a possible out of bounds write due to improper input validation. This could lead to local escalation of privilege with System execution privileges needed. User interaction is not needed for exploitation. Patch ID: WCNCR00367704; Issue ID: MSV-1411. | 2024-06-03 | not yet calculated | |
| mintplex-labs--mintplex-labs/anything-llm | An improper authorization vulnerability exists in the mintplex-labs/anything-llm application, specifically within the '/api/v/' endpoint and its sub-routes. This flaw allows unauthenticated users to perform destructive actions on the VectorDB, including resetting the database and deleting specific namespaces, without requiring any authorization or permissions. The issue affects all versions up to and including the latest version, with a fix introduced in version 1.0.0. Exploitation of this vulnerability can lead to complete data loss of document embeddings across all workspaces, rendering workspace chats and embeddable chat widgets non-functional. Additionally, attackers can list all namespaces, potentially exposing private workspace names. | 2024-06-06 | not yet calculated | |
| mintplex-labs--mintplex-labs/anything-llm | A JSON Injection vulnerability exists in the `mintplex-labs/anything-llm` application, specifically within the username parameter during the login process at the `/api/request-token` endpoint. The vulnerability arises from improper handling of values, allowing attackers to perform brute force attacks without prior knowledge of the username. Once the password is known, attackers can conduct blind attacks to ascertain the full username, significantly compromising system security. | 2024-06-06 | not yet calculated | |
| mintplex-labs--mintplex-labs/anything-llm | A remote code execution vulnerability exists in mintplex-labs/anything-llm due to improper handling of environment variables. Attackers can exploit this vulnerability by injecting arbitrary environment variables via the `POST /api/system/update-env` endpoint, which allows for the execution of arbitrary code on the host running anything-llm. The vulnerability is present in the latest version of anything-llm, with the latest commit identified as fde905aac1812b84066ff72e5f2f90b56d4c3a59. This issue has been fixed in version 1.0.0. Successful exploitation could lead to code execution on the host, enabling attackers to read and modify data accessible to the user running the service, potentially leading to a denial of service. | 2024-06-06 | not yet calculated | |
| mintplex-labs--mintplex-labs/anything-llm | A stored Cross-Site Scripting (XSS) vulnerability exists in the mintplex-labs/anything-llm application, affecting versions up to and including the latest before 1.0.0. The vulnerability arises from the application's failure to properly sanitize and validate user-supplied URLs before embedding them into the application UI as external links with custom icons. Specifically, the application does not prevent the inclusion of 'javascript:' protocol payloads in URLs, which can be exploited by a user with manager role to execute arbitrary JavaScript code in the context of another user's session. This flaw can be leveraged to steal the admin's authorization token by crafting malicious URLs that, when clicked by the admin, send the token to an attacker-controlled server. The attacker can then use this token to perform unauthorized actions, escalate privileges to admin, or directly take over the admin account. The vulnerability is triggered when the malicious link is opened in a new tab using either the CTRL + left mouse button click or the mouse scroll wheel click, or in some non-updated versions of modern browsers, by directly clicking on the link. | 2024-06-06 | not yet calculated | |
| mintplex-labs--mintplex-labs/anything-llm | A Server-Side Request Forgery (SSRF) vulnerability exists in the upload link feature of mintplex-labs/anything-llm. This feature, intended for users with manager or admin roles, processes uploaded links through an internal Collector API using a headless browser. An attacker can exploit this by hosting a malicious website and using it to perform actions such as internal port scanning, accessing internal web applications not exposed externally, and interacting with the Collector API. This interaction can lead to unauthorized actions such as arbitrary file deletion and limited Local File Inclusion (LFI), including accessing NGINX access logs which may contain sensitive information. | 2024-06-06 | not yet calculated | |
| mintplex-labs--mintplex-labs/anything-llm | In mintplex-labs/anything-llm, a vulnerability exists in the thread update process that allows users with Default or Manager roles to escalate their privileges to Administrator. The issue arises from improper input validation when handling HTTP POST requests to the endpoint `/workspace/:slug/thread/:threadSlug/update`. Specifically, the application fails to validate or check user input before passing it to the `workspace_thread` Prisma model for execution. This oversight allows attackers to craft a Prisma relation query operation that manipulates the `users` model to change a user's role to admin. Successful exploitation grants attackers the highest level of user privileges, enabling them to see and perform all actions within the system. | 2024-06-06 | not yet calculated | |
| mintplex-labs--mintplex-labs/anything-llm | mintplex-labs/anything-llm is vulnerable to multiple security issues due to improper input validation in several endpoints. An attacker can exploit these vulnerabilities to escalate privileges from a default user role to an admin role, read and delete arbitrary files on the system, and perform Server-Side Request Forgery (SSRF) attacks. The vulnerabilities are present in the `/request-token`, `/workspace/:slug/thread/:threadSlug/update`, `/system/remove-logo`, `/system/logo`, and collector's `/process` endpoints. These issues are due to the application's failure to properly validate user input before passing it to `prisma` functions and other critical operations. Affected versions include the latest version prior to 1.0.0. | 2024-06-06 | not yet calculated | |
| mintplex-labs--mintplex-labs/anything-llm | mintplex-labs/anything-llm is affected by an uncontrolled resource consumption vulnerability in its upload file endpoint, leading to a denial of service (DOS) condition. Specifically, the server can be shut down by sending an invalid upload request. An attacker with the ability to upload documents can exploit this vulnerability to cause a DOS condition by manipulating the upload request. | 2024-06-06 | not yet calculated | |
| mintplex-labs--mintplex-labs/anything-llm | A Cross-Site Scripting (XSS) vulnerability exists in mintplex-labs/anything-llm, affecting both the desktop application version 1.2.0 and the latest version of the web application. The vulnerability arises from the application's feature to fetch and embed content from websites into workspaces, which can be exploited to execute arbitrary JavaScript code. In the desktop application, this flaw can be escalated to Remote Code Execution (RCE) due to insecure application settings, specifically the enabling of 'nodeIntegration' and the disabling of 'contextIsolation' in Electron's webPreferences. The issue has been addressed in version 1.4.2 of the desktop application. | 2024-06-06 | not yet calculated | |
| mintplex-labs--mintplex-labs/anything-llm | A Server-Side Request Forgery (SSRF) vulnerability exists in the latest version of mintplex-labs/anything-llm, allowing attackers to bypass the official fix intended to restrict access to intranet IP addresses and protocols. Despite efforts to filter out intranet IP addresses starting with 192, 172, 10, and 127 through regular expressions and limit access protocols to HTTP and HTTPS, attackers can still bypass these restrictions using alternative representations of IP addresses and accessing other ports running on localhost. This vulnerability enables attackers to access any asset on the internal network, attack web services on the internal network, scan hosts on the internal network, and potentially access AWS metadata endpoints. The vulnerability is due to insufficient validation of user-supplied URLs, which can be exploited to perform SSRF attacks. | 2024-06-05 | not yet calculated | |
| mlflow--mlflow/mlflow | A vulnerability in mlflow/mlflow version 8.2.1 allows for remote code execution due to improper neutralization of special elements used in an OS command ('Command Injection') within the `mlflow.data.http_dataset_source.py` module. Specifically, when loading a dataset from a source URL with an HTTP scheme, the filename extracted from the `Content-Disposition` header or the URL path is used to generate the final file path without proper sanitization. This flaw enables an attacker to control the file path fully by utilizing path traversal or absolute path techniques, such as '../../tmp/poc.txt' or '/tmp/poc.txt', leading to arbitrary file write. Exploiting this vulnerability could allow a malicious user to execute commands on the vulnerable machine, potentially gaining access to data and model information. The issue is fixed in version 2.9.0. | 2024-06-06 | not yet calculated | |
| mlflow--mlflow/mlflow | A Local File Inclusion (LFI) vulnerability was identified in mlflow/mlflow, specifically in version 2.9.2, which was fixed in version 2.11.3. This vulnerability arises from the application's failure to properly validate URI fragments for directory traversal sequences such as '../'. An attacker can exploit this flaw by manipulating the fragment part of the URI to read arbitrary files on the local file system, including sensitive files like '/etc/passwd'. The vulnerability is a bypass to a previous patch that only addressed similar manipulation within the URI's query string, highlighting the need for comprehensive validation of all parts of a URI to prevent LFI attacks. | 2024-06-06 | not yet calculated | |
| mlflow--mlflow/mlflow | A vulnerability in mlflow/mlflow version 2.11.1 allows attackers to create multiple models with the same name by exploiting URL encoding. This flaw can lead to Denial of Service (DoS) as an authenticated user might not be able to use the intended model, as it will open a different model each time. Additionally, an attacker can exploit this vulnerability to perform data model poisoning by creating a model with the same name, potentially causing an authenticated user to become a victim by using the poisoned model. The issue stems from inadequate validation of model names, allowing for the creation of models with URL-encoded names that are treated as distinct from their URL-decoded counterparts. | 2024-06-06 | not yet calculated | |
| n/a--n/a | Precor touchscreen console P62, P80, and P82 could allow a remote attacker (within the local network) to bypass security restrictions, and access the service menu, because there is a hard-coded service code. | 2024-06-07 | not yet calculated | |
| n/a--n/a | Precor touchscreen console P82 contains a private SSH key that corresponds to a default public key. A remote attacker could exploit this to gain root privileges. | 2024-06-07 | not yet calculated | |
| n/a--n/a | Precor touchscreen console P62, P80, and P82 could allow a remote attacker to obtain sensitive information because the root password is stored in /etc/passwd. An attacker could exploit this to extract files and obtain sensitive information. | 2024-06-07 | not yet calculated | |
| n/a--n/a | Precor touchscreen console P62, P80, and P82 contains a default SSH public key in the authorized_keys file. A remote attacker could use this key to gain root privileges. | 2024-06-07 | not yet calculated | |
| n/a--n/a | dnsmasq 2.9 is vulnerable to Integer Overflow via forward_query. | 2024-06-06 | not yet calculated | |
| n/a--n/a | An issue was discovered in Samsung Mobile Processor, Automotive Processor, Wearable Processor, and Modem Exynos 980, 990, 850, 1080, 2100, 2200, 1280, 1380, 1330, 9110, W920, Exynos Modem 5123, Exynos Modem 5300, and Exynos Auto T5123. The baseband software does not properly check states specified by the RRC. This can lead to disclosure of sensitive information. | 2024-06-05 | not yet calculated | |
| n/a--n/a | A deep link validation issue in KakaoTalk 10.4.3 allowed a remote adversary to direct users to run any attacker-controller JavaScript within a WebView. The impact was further escalated by triggering another WebView that leaked its access token in a HTTP request header. Ultimately, this access token could be used to takeover another user's account and read her/his chat messages. | 2024-06-03 | not yet calculated | |
| n/a--n/a | An issue in obgm and Libcoap v.a3ed466 allows a remote attacker to cause a denial of service via thecoap_context_t function in the src/coap_threadsafe.c:297:3 component. | 2024-06-06 | not yet calculated | |
| n/a--n/a | Mercusys MW325R EU V3 (Firmware MW325R(EU)_V3_1.11.0 Build 221019) is vulnerable to a stack-based buffer overflow, which could allow an attacker to execute arbitrary code. Exploiting the vulnerability requires authentication. | 2024-06-03 | not yet calculated | |
| n/a--n/a | Dynamsoft Service 1.8.1025 through 1.8.2013, 1.7.0330 through 1.7.2531, 1.6.0428 through 1.6.1112, 1.5.0625 through 1.5.3116, 1.4.0618 through 1.4.1230, and 1.0.516 through 1.3.0115 has Incorrect Access Control. This is fixed in 1.8.2014, 1.7.4212, 1.6.3212, 1.5.31212, 1.4.3212, and 1.3.3212. | 2024-06-06 | not yet calculated | |
| n/a--n/a | dnspod-sr 0dfbd37 is vulnerable to buffer overflow. | 2024-06-06 | not yet calculated | |
| n/a--n/a | dnspod-sr 0dfbd37 contains a SEGV. | 2024-06-06 | not yet calculated | |
| n/a--n/a | robdns commit d76d2e6 was discovered to contain a heap overflow via the component block->filename at /src/zonefile-insertion.c. | 2024-06-06 | not yet calculated | |
| n/a--n/a | robdns commit d76d2e6 was discovered to contain a NULL pointer dereference via the item->tokens component at /src/conf-parse.c. | 2024-06-06 | not yet calculated | |
| n/a--n/a | robdns commit d76d2e6 was discovered to contain a misaligned address at /src/zonefile-insertion.c. | 2024-06-06 | not yet calculated | |
| n/a--n/a | smartdns commit 54b4dc was discovered to contain a misaligned address at smartdns/src/util.c. | 2024-06-06 | not yet calculated | |
| n/a--n/a | smartdns commit 54b4dc was discovered to contain a misaligned address at smartdns/src/dns.c. | 2024-06-06 | not yet calculated | |
| n/a--n/a | Invision Community through 4.7.16 allows remote code execution via the applications/core/modules/admin/editor/toolbar.php IPS\core\modules\admin\editor\_toolbar::addPlugin() method. This method handles uploaded ZIP files that are extracted into the applications/core/interface/ckeditor/ckeditor/plugins/ directory without properly verifying their content. This can be exploited by admin users (with the toolbar_manage permission) to write arbitrary PHP files into that directory, leading to execution of arbitrary PHP code in the context of the web server user. | 2024-06-07 | not yet calculated | |
| n/a--n/a | Invision Community before 4.7.16 allow SQL injection via the applications/nexus/modules/front/store/store.php IPS\nexus\modules\front\store\_store::_categoryView() method, where user input passed through the filter request parameter is not properly sanitized before being used to execute SQL queries. This can be exploited by unauthenticated attackers to carry out Blind SQL Injection attacks. | 2024-06-07 | not yet calculated | |
| n/a--n/a | Incorrect access control in the fingerprint authentication mechanism of Phone Cleaner: Boost & Clean v2.2.0 allows attackers to bypass fingerprint authentication due to the use of a deprecated API. | 2024-06-03 | not yet calculated | |
| n/a--n/a | Incorrect access control in the fingerprint authentication mechanism of Bitdefender Mobile Security v4.11.3-gms allows attackers to bypass fingerprint authentication due to the use of a deprecated API. | 2024-06-03 | not yet calculated | |
| n/a--n/a | The DNS protocol in RFC 1035 and updates allows remote attackers to cause a denial of service (resource consumption) by arranging for DNS queries to be accumulated for seconds, such that responses are later sent in a pulsing burst (which can be considered traffic amplification in some cases), aka the "DNSBomb" issue. | 2024-06-06 | not yet calculated | |
| n/a--n/a | A Reflected Cross-site scripting (XSS) vulnerability located in htdocs/compta/paiement/card.php of Dolibarr before 19.0.2 allows remote attackers to inject arbitrary web script or HTML via a crafted payload injected into the facid parameter. | 2024-06-03 | not yet calculated | |
| n/a--n/a | Cyrus IMAP before 3.8.3 and 3.10.x before 3.10.0-rc1 allows authenticated attackers to cause unbounded memory allocation by sending many LITERALs in a single command. | 2024-06-05 | not yet calculated | |
| n/a--n/a | Directory Traversal vulnerability in CubeCart v.6.5.5 and before allows an attacker to execute arbitrary code via a crafted file uploaded to the _g and node parameters. | 2024-06-06 | not yet calculated | |
| n/a--n/a | A SQL Injection vulnerability exists in the `ofrs/admin/index.php` script of PHPGurukul Online Fire Reporting System 1.2. The vulnerability allows attackers to bypass authentication and gain unauthorized access by injecting SQL commands into the username input field during the login process. | 2024-06-03 | not yet calculated | |
| n/a--n/a | Silverpeas before 6.3.5 allows authentication bypass by omitting the Password field to AuthenticationServlet, often providing an unauthenticated user with superadmin access. | 2024-06-03 | not yet calculated | |
| n/a--n/a | Sourcecodester Gas Agency Management System v1.0 is vulnerable to SQL Injection via /gasmark/editbrand.php?id=. | 2024-06-03 | not yet calculated | |
| n/a--n/a | Sourcecodester Gas Agency Management System v1.0 is vulnerable to arbitrary code execution via editClientImage.php. | 2024-06-03 | not yet calculated | |
| n/a--n/a | Tenda O3V2 v1.0.0.12(3880) was discovered to contain a Blind Command Injection via stpEn parameter in the SetStp function. This vulnerability allows attackers to execute arbitrary commands with root privileges. | 2024-06-04 | not yet calculated | |
| n/a--n/a | idccms v1.35 was discovered to contain a Cross-Site Request Forgery (CSRF) via the component /admin/idcProType_deal.php?mudi=add&nohrefStr=close | 2024-06-05 | not yet calculated | |
| n/a--n/a | idccms v1.35 was discovered to contain a Cross-Site Request Forgery (CSRF) via the component admin/type_deal.php?mudi=del | 2024-06-05 | not yet calculated | |
| n/a--n/a | idccms v1.35 was discovered to contain a Cross-Site Request Forgery (CSRF) via the component admin/type_deal.php?mudi=add. | 2024-06-05 | not yet calculated | |
| n/a--n/a | idccms v1.35 was discovered to contain a Cross-Site Request Forgery (CSRF) via the component admin/vpsClass_deal.php?mudi=del | 2024-06-05 | not yet calculated | |
| n/a--n/a | Sourcecodester Pharmacy/Medical Store Point of Sale System 1.0 is vulnerable SQL Injection via login.php. This vulnerability stems from inadequate validation of user inputs for the email and password parameters, allowing attackers to inject malicious SQL queries. | 2024-06-07 | not yet calculated | |
| n/a--n/a | LyLme_spage v1.9.5 is vulnerable to Cross Site Scripting (XSS) via admin/link.php. | 2024-06-03 | not yet calculated | |
| n/a--n/a | LyLme_spage v1.9.5 is vulnerable to Server-Side Request Forgery (SSRF) via the get_head function. | 2024-06-04 | not yet calculated | |
| n/a--n/a | TRENDnet TEW-827DRU devices through 2.06B04 contain a stack-based buffer overflow in the ssi binary. The overflow allows an authenticated user to execute arbitrary code by POSTing to apply.cgi via the action vlan_setting with a sufficiently long dns1 or dns 2 key. | 2024-06-03 | not yet calculated | |
| n/a--n/a | TRENDnet TEW-827DRU devices through 2.06B04 contain a stack-based buffer overflow in the ssi binary. The overflow allows an authenticated user to execute arbitrary code by POSTing to apply.cgi via the action wizard_ipv6 with a sufficiently long reboot_type key. | 2024-06-03 | not yet calculated | |
| n/a--n/a | Improper input validation in OneFlow-Inc. Oneflow v0.9.1 allows attackers to cause a Denial of Service (DoS) via inputting negative values into the oneflow.zeros/ones parameter. | 2024-06-06 | not yet calculated | |
| n/a--n/a | An issue in OneFlow-Inc. Oneflow v0.9.1 allows attackers to cause a Denial of Service (DoS) when an empty array is processed with oneflow.tensordot. | 2024-06-06 | not yet calculated | |
| n/a--n/a | Improper input validation in OneFlow-Inc. Oneflow v0.9.1 allows attackers to cause a Denial of Service (DoS) via inputting a negative value into the dim parameter. | 2024-06-06 | not yet calculated | |
| n/a--n/a | OneFlow-Inc. Oneflow v0.9.1 does not display an error or warning when the oneflow.eye parameter is floating. | 2024-06-06 | not yet calculated | |
| n/a--n/a | An issue in the oneflow.permute component of OneFlow-Inc. Oneflow v0.9.1 causes an incorrect calculation when the same dimension operation is performed. | 2024-06-06 | not yet calculated | |
| n/a--n/a | Improper input validation in OneFlow-Inc. Oneflow v0.9.1 allows attackers to cause a Denial of Service (DoS) via inputting a negative value into the oneflow.full parameter. | 2024-06-06 | not yet calculated | |
| n/a--n/a | An issue in OneFlow-Inc. Oneflow v0.9.1 allows attackers to cause a Denial of Service (DoS) when index as a negative number exceeds the range of size. | 2024-06-06 | not yet calculated | |
| n/a--n/a | An issue in the oneflow.scatter_nd parameter OneFlow-Inc. Oneflow v0.9.1 allows attackers to cause a Denial of Service (DoS) when index parameter exceeds the range of shape. | 2024-06-06 | not yet calculated | |
| n/a--n/a | An issue in OneFlow-Inc. Oneflow v0.9.1 allows attackers to cause a Denial of Service (DoS) when an empty array is processed with oneflow.dot. | 2024-06-06 | not yet calculated | |
| n/a--n/a | An issue in OneFlow-Inc. Oneflow v0.9.1 allows attackers to cause a Denial of Service (DoS) via inputting a negative value into the oneflow.index_select parameter. | 2024-06-06 | not yet calculated | |
| n/a--n/a | A cross-site scripting (XSS) vulnerability in Monstra CMS v3.0.4 allows attackers to execute arbitrary web scripts or HTML via a crafted payload injected into the Themes parameter at index.php. | 2024-06-07 | not yet calculated | |
| n/a--n/a | An arbitrary file upload vulnerability in Monstra CMS v3.0.4 allows attackers to execute arbitrary code via uploading a crafted PHP file. | 2024-06-06 | not yet calculated | |
| n/a--n/a | A cross-site scripting (XSS) vulnerability in Monstra CMS v3.0.4 allows attackers to execute arbitrary web scripts or HTML via a crafted payload injected into the About Me parameter in the Edit Profile page. | 2024-06-06 | not yet calculated | |
| n/a--n/a | Sourcecodester Stock Management System v1.0 is vulnerable to SQL Injection via editCategories.php. | 2024-06-06 | not yet calculated | |
| n/a--n/a | TOTOLINK CP300 V2.0.4-B20201102 was discovered to contain a hardcoded password vulnerability in /etc/shadow.sample, which allows attackers to log in as root. | 2024-06-03 | not yet calculated | |
| n/a--n/a | TOTOLINK LR350 V9.3.5u.6369_B20220309 was discovered to contain a command injection via the host_time parameter in the NTPSyncWithHost function. | 2024-06-03 | not yet calculated | |
| n/a--n/a | An issue in Netgear WNR614 JNR1010V2 N300-V1.1.0.54_1.0.1 allows attackers to bypass authentication and access the administrative interface via unspecified vectors. | 2024-06-07 | not yet calculated | |
| n/a--n/a | Netgear WNR614 JNR1010V2 N300-V1.1.0.54_1.0.1 does not properly set the HTTPOnly flag for cookies. This allows attackers to possibly intercept and access sensitive communications between the router and connected devices. | 2024-06-07 | not yet calculated | |
| n/a--n/a | An issue in Netgear WNR614 JNR1010V2/N300-V1.1.0.54_1.0.1 allows attackers to create passwords that do not conform to defined security standards. | 2024-06-07 | not yet calculated | |
| n/a--n/a | Netgear WNR614 JNR1010V2/N300-V1.1.0.54_1.0.1 was discovered to store credentials in plaintext. | 2024-06-07 | not yet calculated | |
| n/a--n/a | An issue in the implementation of the WPS in Netgear WNR614 JNR1010V2/N300-V1.1.0.54_1.0.1 allows attackers to gain access to the router's pin. | 2024-06-07 | not yet calculated | |
| n/a--n/a | Insecure permissions in Netgear WNR614 JNR1010V2/N300-V1.1.0.54_1.0.1 allows attackers to access URLs and directories embedded within the firmware via unspecified vectors. | 2024-06-06 | not yet calculated | |
| n/a--n/a | A SQL injection vulnerability in SEMCMS v.4.8, allows a remote attacker to obtain sensitive information via the ID parameter in Download.php. | 2024-06-04 | not yet calculated | |
| n/a--n/a | A SQL injection vulnerability in SEMCMS v.4.8, allows a remote attacker to obtain sensitive information via the lgid parameter in Download.php. | 2024-06-04 | not yet calculated | |
| n/a--n/a | An arbitrary file upload vulnerability in the image upload function of aimeos-core v2024.04 allows attackers to execute arbitrary code via uploading a crafted PHP file. | 2024-06-07 | not yet calculated | |
| n/a--n/a | The encrypt() function of Ninja Core v7.0.0 was discovered to use a weak cryptographic algorithm, leading to a possible leakage of sensitive information. | 2024-06-06 | not yet calculated | |
| n/a--n/a | An XML External Entity (XXE) vulnerability in the ebookmeta.get_metadata function of ebookmeta before v1.2.8 allows attackers to access sensitive information or cause a Denial of Service (DoS) via crafted XML input. | 2024-06-07 | not yet calculated | |
| n/a--n/a | SQL Injection vulnerability in CRMEB v.5.2.2 allows a remote attacker to obtain sensitive information via the getProductList function in the ProductController.php file. | 2024-06-05 | not yet calculated | |
| n/a--n/a | Jan v0.4.12 was discovered to contain an arbitrary file read vulnerability via the /v1/app/readFileSync interface. | 2024-06-04 | not yet calculated | |
| n/a--n/a | An arbitrary file upload vulnerability in the /v1/app/writeFileSync interface of Jan v0.4.12 allows attackers to execute arbitrary code via uploading a crafted file. | 2024-06-04 | not yet calculated | |
| n/a--n/a | Northern.tech Mender Enterprise before 3.6.4 and 3.7.x before 3.7.4 has Weak Authentication. | 2024-06-03 | not yet calculated | |
| n/a--n/a | The Active Admin (aka activeadmin) framework before 3.2.2 for Ruby on Rails allows stored XSS in certain situations where users can create entities (to be later edited in forms) with arbitrary names, aka a "dynamic form legends" issue. 4.0.0.beta7 is also a fixed version. | 2024-06-03 | not yet calculated | |
| n/a--n/a | An arbitrary file upload vulnerability in the /v1/app/appendFileSync interface of Jan v0.4.12 allows attackers to execute arbitrary code via uploading a crafted file. | 2024-06-04 | not yet calculated | |
| n/a--n/a | Roundcube Webmail before 1.5.7 and 1.6.x before 1.6.7 allows XSS via SVG animate attributes. | 2024-06-07 | not yet calculated | |
| n/a--n/a | Roundcube Webmail before 1.5.7 and 1.6.x before 1.6.7 allows XSS via list columns from user preferences. | 2024-06-07 | not yet calculated | |
| n/a--n/a | Roundcube Webmail before 1.5.7 and 1.6.x before 1.6.7 on Windows allows command injection via im_convert_path and im_identify_path. NOTE: this issue exists because of an incomplete fix for CVE-2020-12641. | 2024-06-07 | not yet calculated | |
| n/a--n/a | An XML External Entity (XXE) vulnerability in the ebookmeta.get_metadata function of lxml before v4.9.1 allows attackers to access sensitive information or cause a Denial of Service (DoS) via crafted XML input. | 2024-06-07 | not yet calculated | |
| n/a--n/a | Libarchive before 3.7.4 allows name out-of-bounds access when a ZIP archive has an empty-name file and mac-ext is enabled. This occurs in slurp_central_directory in archive_read_support_format_zip.c. | 2024-06-08 | not yet calculated | |
| n/a--n/a | fprintd through 1.94.3 lacks a security attention mechanism, and thus unexpected actions might be authorized by "auth sufficient pam_fprintd.so" for Sudo. | 2024-06-08 | not yet calculated | |
| NETGEAR--ProSAFE Network Management System | NETGEAR ProSAFE Network Management System UpLoadServlet Directory Traversal Remote Code Execution Vulnerability. This vulnerability allows remote attackers to execute arbitrary code on affected installations of NETGEAR ProSAFE Network Management System. Authentication is required to exploit this vulnerability. The specific flaw exists within the UpLoadServlet class. The issue results from the lack of proper validation of a user-supplied path prior to using it in file operations. An attacker can leverage this vulnerability to execute code in the context of SYSTEM. Was ZDI-CAN-22724. | 2024-06-06 | not yet calculated | |
| onnx--onnx/onnx | A vulnerability in the `download_model_with_test_data` function of the onnx/onnx framework, version 1.16.0, allows for arbitrary file overwrite due to inadequate prevention of path traversal attacks in malicious tar files. This vulnerability enables attackers to overwrite any file on the system, potentially leading to remote code execution, deletion of system, personal, or application files, thus impacting the integrity and availability of the system. The issue arises from the function's handling of tar file extraction without performing security checks on the paths within the tar file, as demonstrated by the ability to overwrite the `/home/kali/.ssh/authorized_keys` file by specifying an absolute path in the malicious tar file. | 2024-06-06 | not yet calculated | |
| parisneo--parisneo/lollms-webui | parisneo/lollms-webui is vulnerable to path traversal and denial of service attacks due to an exposed `/select_database` endpoint in version a9d16b0. The endpoint improperly handles file paths, allowing attackers to specify absolute paths when interacting with the `DiscussionsDB` instance. This flaw enables attackers to create directories anywhere on the system where the application has permissions, potentially leading to denial of service by creating directories with names of critical files, such as HTTPS certificate files, causing server startup failures. Additionally, attackers can manipulate the database path, resulting in the loss of client data by constantly changing the file location to an attacker-controlled location, scattering the data across the filesystem and making recovery difficult. | 2024-06-06 | not yet calculated | |
| parisneo--parisneo/lollms-webui | A Cross-Site Request Forgery (CSRF) vulnerability exists in the profile picture upload functionality of the Lollms application, specifically in the parisneo/lollms-webui repository, affecting versions up to 7.3.0. This vulnerability allows attackers to change a victim's profile picture without their consent, potentially leading to a denial of service by overloading the filesystem with files. Additionally, this flaw can be exploited to perform a stored cross-site scripting (XSS) attack, enabling attackers to execute arbitrary JavaScript in the context of the victim's browser session. The issue is resolved in version 9.3. | 2024-06-06 | not yet calculated | |
| parisneo--parisneo/lollms-webui | A vulnerability in the parisneo/lollms-webui version 9.3 allows attackers to bypass intended access restrictions and execute arbitrary code. The issue arises from the application's handling of the `/execute_code` endpoint, which is intended to be blocked from external access by default. However, attackers can exploit the `/update_setting` endpoint, which lacks proper access control, to modify the `host` configuration at runtime. By changing the `host` setting to an attacker-controlled value, the restriction on the `/execute_code` endpoint can be bypassed, leading to remote code execution. This vulnerability is due to improper neutralization of special elements used in an OS command (`Improper Neutralization of Special Elements used in an OS Command`). | 2024-06-06 | not yet calculated | |
| parisneo--parisneo/lollms-webui | parisneo/lollms-webui is vulnerable to path traversal attacks that can lead to remote code execution due to insufficient sanitization of user-supplied input in the 'Database path' and 'PDF LaTeX path' settings. An attacker can exploit this vulnerability by manipulating these settings to execute arbitrary code on the targeted server. The issue affects the latest version of the software. The vulnerability stems from the application's handling of the 'discussion_db_name' and 'pdf_latex_path' parameters, which do not properly validate file paths, allowing for directory traversal. This vulnerability can also lead to further file exposure and other attack vectors by manipulating the 'discussion_db_name' parameter. | 2024-06-06 | not yet calculated | |
| parisneo--parisneo/lollms-webui | A path traversal vulnerability exists in the parisneo/lollms-webui version 9.3 on the Windows platform. Due to improper validation of file paths between Windows and Linux environments, an attacker can exploit this vulnerability to delete any file on the system. The issue arises from the lack of adequate sanitization of user-supplied input in the 'del_preset' endpoint, where the application fails to prevent the use of absolute paths or directory traversal sequences ('..'). As a result, an attacker can send a specially crafted request to the 'del_preset' endpoint to delete files outside of the intended directory. | 2024-06-06 | not yet calculated | |
| parisneo--parisneo/lollms-webui | A path traversal vulnerability exists in the parisneo/lollms-webui application, specifically within the `lollms_core/lollms/server/endpoints/lollms_binding_files_server.py` and `lollms_core/lollms/security.py` files. Due to inadequate validation of file paths between Windows and Linux environments using `Path(path).is_absolute()`, attackers can exploit this flaw to read any file on the system. This issue affects the latest version of LoLLMs running on the Windows platform. The vulnerability is triggered when an attacker sends a specially crafted request to the `/user_infos/{path:path}` endpoint, allowing the reading of arbitrary files, as demonstrated with the `win.ini` file. The issue has been addressed in version 9.5 of the software. | 2024-06-06 | not yet calculated | |
| parisneo--parisneo/lollms-webui | A path traversal and arbitrary file upload vulnerability exists in the parisneo/lollms-webui application, specifically within the `@router.get("/switch_personal_path")` endpoint in `./lollms-webui/lollms_core/lollms/server/endpoints/lollms_user.py`. The vulnerability arises due to insufficient sanitization of user-supplied input for the `path` parameter, allowing an attacker to specify arbitrary file system paths. This flaw enables direct arbitrary file uploads, leakage of `personal_data`, and overwriting of configurations in `lollms-webui`->`configs` by exploiting the same named directory in `personal_data`. The issue affects the latest version of the application and is fixed in version 9.4. Successful exploitation could lead to sensitive information disclosure, unauthorized file uploads, and potentially remote code execution by overwriting critical configuration files. | 2024-06-06 | not yet calculated | |
| parisneo--parisneo/lollms-webui | A path traversal vulnerability exists in the 'cyber_security/codeguard' native personality of the parisneo/lollms-webui, affecting versions up to 9.5. The vulnerability arises from the improper limitation of a pathname to a restricted directory in the 'process_folder' function within 'lollms-webui/zoos/personalities_zoo/cyber_security/codeguard/scripts/processor.py'. Specifically, the function fails to properly sanitize user-supplied input for the 'code_folder_path', allowing an attacker to specify arbitrary paths using '../' or absolute paths. This flaw leads to arbitrary file read and overwrite capabilities in specified directories without limitations, posing a significant risk of sensitive information disclosure and unauthorized file manipulation. | 2024-06-06 | not yet calculated | |
| parisneo--parisneo/lollms-webui | A remote code execution (RCE) vulnerability exists in the '/install_extension' endpoint of the parisneo/lollms-webui application, specifically within the `@router.post("/install_extension")` route handler. The vulnerability arises due to improper handling of the `name` parameter in the `ExtensionBuilder().build_extension()` method, which allows for local file inclusion (LFI) leading to arbitrary code execution. An attacker can exploit this vulnerability by crafting a malicious `name` parameter that causes the server to load and execute a `__init__.py` file from an arbitrary location, such as the upload directory for discussions. This vulnerability affects the latest version of parisneo/lollms-webui and can lead to remote code execution without requiring user interaction, especially when the application is exposed to an external endpoint or operated in headless mode. | 2024-06-06 | not yet calculated | |
| parisneo--parisneo/lollms-webui | A Server-Side Request Forgery (SSRF) vulnerability exists in the 'add_webpage' endpoint of the parisneo/lollms-webui application, affecting the latest version. The vulnerability arises because the application does not adequately validate URLs entered by users, allowing them to input arbitrary URLs, including those that target internal resources such as 'localhost' or '127.0.0.1'. This flaw enables attackers to make unauthorized requests to internal or external systems, potentially leading to access to sensitive data, service disruption, network integrity compromise, business logic manipulation, and abuse of third-party resources. The issue is critical and requires immediate attention to maintain the application's security and integrity. | 2024-06-06 | not yet calculated | |
| parisneo--parisneo/lollms | A path traversal vulnerability exists in the parisneo/lollms application, specifically within the `sanitize_path_from_endpoint` and `sanitize_path` functions in `lollms_core\lollms\security.py`. This vulnerability allows for arbitrary file reading when the application is running on Windows. The issue arises due to insufficient sanitization of user-supplied input, enabling attackers to bypass the path traversal protection mechanisms by crafting malicious input. Successful exploitation could lead to unauthorized access to sensitive files, information disclosure, and potentially a denial of service (DoS) condition by including numerous large or resource-intensive files. This vulnerability affects the latest version prior to 9.6. | 2024-06-06 | not yet calculated | |
| parisneo--parisneo/lollms | A path traversal vulnerability exists in the parisneo/lollms application, affecting version 9.4.0 and potentially earlier versions, but fixed in version 5.9.0. The vulnerability arises due to improper validation of file paths between Windows and Linux environments, allowing attackers to traverse beyond the intended directory and read any file on the Windows system. Specifically, the application fails to adequately sanitize file paths containing backslashes (`\`), which can be exploited to access the root directory and read, or even delete, sensitive files. This issue was discovered in the context of the `/user_infos` endpoint, where a crafted request using backslashes to reference a file (e.g., `\windows\win.ini`) could result in unauthorized file access. The impact of this vulnerability includes the potential for attackers to access sensitive information such as environment variables, database files, and configuration files, which could lead to further compromise of the system. | 2024-06-06 | not yet calculated | |
| ProjectDiscovery--Interactsh | Files or Directories Accessible to External Parties vulnerability in smb server in ProjectDiscovery Interactsh allows remote attackers to read/write any files in the directory and subdirectories of where the victim runs interactsh-server via anonymous login. | 2024-06-05 | not yet calculated | |
| pytorch--pytorch/pytorch | A vulnerability in the PyTorch's torch.distributed.rpc framework, specifically in versions prior to 2.2.2, allows for remote code execution (RCE). The framework, which is used in distributed training scenarios, does not properly verify the functions being called during RPC (Remote Procedure Call) operations. This oversight permits attackers to execute arbitrary commands by leveraging built-in Python functions such as eval during multi-cpu RPC communication. The vulnerability arises from the lack of restriction on function calls when a worker node serializes and sends a PythonUDF (User Defined Function) to the master node, which then deserializes and executes the function without validation. This flaw can be exploited to compromise master nodes initiating distributed training, potentially leading to the theft of sensitive AI-related data. | 2024-06-06 | not yet calculated | |
| qdrant--qdrant/qdrant | qdrant/qdrant version 1.9.0-dev is vulnerable to arbitrary file read and write during the snapshot recovery process. Attackers can exploit this vulnerability by manipulating snapshot files to include symlinks, leading to arbitrary file read by adding a symlink that points to a desired file on the filesystem and arbitrary file write by including a symlink and a payload file in the snapshot's directory structure. This vulnerability allows for the reading and writing of arbitrary files on the server, which could potentially lead to a full takeover of the system. The issue is fixed in version v1.9.0. | 2024-06-03 | not yet calculated | |
| scikit-learn--scikit-learn/scikit-learn | A sensitive data leakage vulnerability was identified in scikit-learn's TfidfVectorizer, specifically in versions up to and including 1.4.1.post1, which was fixed in version 1.5.0. The vulnerability arises from the unexpected storage of all tokens present in the training data within the `stop_words_` attribute, rather than only storing the subset of tokens required for the TF-IDF technique to function. This behavior leads to the potential leakage of sensitive information, as the `stop_words_` attribute could contain tokens that were meant to be discarded and not stored, such as passwords or keys. The impact of this vulnerability varies based on the nature of the data being processed by the vectorizer. | 2024-06-06 | not yet calculated | |
| SEH Computertechnik--utnserver Pro | Missing input validation in the SEH Computertechnik utnserver Pro, SEH Computertechnik utnserver ProMAX, SEH Computertechnik INU-100 web-interface allows stored Cross-Site Scripting (XSS)..This issue affects utnserver Pro, utnserver ProMAX, INU-100 version 20.1.22 and below. | 2024-06-04 | not yet calculated | |
| SEH Computertechnik--utnserver Pro | Missing input validation and OS command integration of the input in the utnserver Pro, utnserver ProMAX, INU-100 web-interface allows authenticated command injection.This issue affects utnserver Pro, utnserver ProMAX, INU-100 version 20.1.22 and below. | 2024-06-04 | not yet calculated | |
| SEH Computertechnik--utnserver Pro | An uncontrolled resource consumption of file descriptors in SEH Computertechnik utnserver Pro, SEH Computertechnik utnserver ProMAX, SEH Computertechnik INU-100 allows DoS via HTTP.This issue affects utnserver Pro, utnserver ProMAX, INU-100 version 20.1.22 and below. | 2024-06-04 | not yet calculated | |
| significant-gravitas--significant-gravitas/autogpt | A Cross-Site Request Forgery (CSRF) vulnerability in significant-gravitas/autogpt version v0.5.0 allows attackers to execute arbitrary commands on the AutoGPT server. The vulnerability stems from the lack of protections on the API endpoint receiving instructions, enabling an attacker to direct a user running AutoGPT in their local network to a malicious website. This site can then send crafted requests to the AutoGPT server, leading to command execution. The issue is exacerbated by CORS being enabled for arbitrary origins by default, allowing the attacker to read the response of all cross-site queries. This vulnerability was addressed in version 5.1. | 2024-06-06 | not yet calculated | |
| significant-gravitas--significant-gravitas/autogpt | An OS command injection vulnerability exists in the MacOS Text-To-Speech class MacOSTTS of the significant-gravitas/autogpt project, affecting versions up to v0.5.0. The vulnerability arises from the improper neutralization of special elements used in an OS command within the `_speech` method of the MacOSTTS class. Specifically, the use of `os.system` to execute the `say` command with user-supplied text allows for arbitrary code execution if an attacker can inject shell commands. This issue is triggered when the AutoGPT instance is run with the `--speak` option enabled and configured with `TEXT_TO_SPEECH_PROVIDER=macos`, reflecting back a shell injection snippet. The impact of this vulnerability is the potential execution of arbitrary code on the instance running AutoGPT. The issue was addressed in version 5.1.0. | 2024-06-06 | not yet calculated | |
| significant-gravitas--significant-gravitas/autogpt | AutoGPT, a component of significant-gravitas/autogpt, is vulnerable to an improper neutralization of special elements used in an OS command ('OS Command Injection') due to a flaw in its shell command validation function. Specifically, the vulnerability exists in versions v0.5.0 up to but not including 5.1.0. The issue arises from the application's method of validating shell commands against an allowlist or denylist, where it only checks the first word of the command. This allows an attacker to bypass the intended restrictions by crafting commands that are executed despite not being on the allowlist or by including malicious commands not present in the denylist. Successful exploitation of this vulnerability could allow an attacker to execute arbitrary shell commands. | 2024-06-06 | not yet calculated | |
| Sonos--Era 100 | Sonos Era 100 SMB2 Message Handling Integer Underflow Information Disclosure Vulnerability. This vulnerability allows network-adjacent attackers to disclose sensitive information on affected installations of Sonos Era 100 smart speakers. Authentication is not required to exploit this vulnerability. The specific flaw exists within the handling of SMB2 messages. The issue results from the lack of proper validation of user-supplied data, which can result in an integer underflow before reading from memory. An attacker can leverage this in conjunction with other vulnerabilities to execute arbitrary code in the context of root. Was ZDI-CAN-22336. | 2024-06-06 | not yet calculated | |
| Sonos--Era 100 | Sonos Era 100 SMB2 Message Handling Out-Of-Bounds Write Remote Code Execution Vulnerability. This vulnerability allows network-adjacent attackers to execute arbitrary code on affected installations of Sonos Era 100 smart speakers. Authentication is not required to exploit this vulnerability. The specific flaw exists within the handling of SMB2 messages. The issue results from the lack of proper validation of user-supplied data, which can result in a write past the end of an allocated buffer. An attacker can leverage this vulnerability to execute code in the context of root. Was ZDI-CAN-22384. | 2024-06-06 | not yet calculated | |
| Sonos--Era 100 | Sonos Era 100 SMB2 Message Handling Out-Of-Bounds Read Information Disclosure Vulnerability. This vulnerability allows network-adjacent attackers to disclose sensitive information on affected installations of Sonos Era 100 smart speakers. Authentication is not required to exploit this vulnerability. The specific flaw exists within the handling of SMB2 messages. The issue results from the lack of proper validation of user-supplied data, which can result in a read past the end of an allocated buffer. An attacker can leverage this in conjunction with other vulnerabilities to execute arbitrary code in the context of root. Was ZDI-CAN-22428. | 2024-06-06 | not yet calculated | |
| Sonos--Era 100 | Sonos Era 100 SMB2 Message Handling Use-After-Free Remote Code Execution Vulnerability. This vulnerability allows network-adjacent attackers to execute arbitrary code on affected installations of Sonos Era 100 smart speakers. Authentication is not required to exploit this vulnerability. The specific flaw exists within the handling of SMB2 messages. The issue results from the lack of validating the existence of an object prior to performing operations on the object. An attacker can leverage this vulnerability to execute code in the context of root. Was ZDI-CAN-22459. | 2024-06-06 | not yet calculated | |
| stangirard--stangirard/quivr | A Server-Side Request Forgery (SSRF) vulnerability exists in the stangirard/quivr application, version 0.0.204, which allows attackers to access internal networks. The vulnerability is present in the crawl endpoint where the 'url' parameter can be manipulated to send HTTP requests to arbitrary URLs, thereby facilitating SSRF attacks. The affected code is located in the backend/routes/crawl_routes.py file, specifically within the crawl_endpoint function. This issue could allow attackers to interact with internal services that are accessible from the server hosting the application. | 2024-06-06 | not yet calculated | |
| Unknown--ARForms - Premium WordPress Form Builder Plugin | The ARForms - Premium WordPress Form Builder Plugin WordPress plugin before 6.6 allows unauthenticated users to modify uploaded files in such a way that PHP code can be uploaded when an upload file input is included on a form | 2024-06-07 | not yet calculated | |
| Unknown--ARForms - Premium WordPress Form Builder Plugin | The ARForms - Premium WordPress Form Builder Plugin WordPress plugin before 6.6 does not sanitise and escape some of its settings, which could allow high privilege users such as admin to perform Stored Cross-Site Scripting attacks even when the unfiltered_html capability is disallowed (for example in multisite setup) | 2024-06-07 | not yet calculated | |
| Unknown--buddyboss-platform | The buddyboss-platform WordPress plugin before 2.6.0 contains an IDOR vulnerability that allows a user to like a private post by manipulating the ID included in the request | 2024-06-04 | not yet calculated | |
| Unknown--buddyboss-platform | The contains an IDOR vulnerability that allows a user to comment on a private post by manipulating the ID included in the request | 2024-06-05 | not yet calculated | |
| Unknown--FS Product Inquiry | The FS Product Inquiry WordPress plugin through 1.1.1 does not sanitise and escape a parameter before outputting it back in the page, leading to a Reflected Cross-Site Scripting which could be used against high privilege users such as admin or unauthenticated users | 2024-06-04 | not yet calculated | |
| Unknown--FS Product Inquiry | The FS Product Inquiry WordPress plugin through 1.1.1 does not sanitise and escape some form submissions, which could allow unauthenticated users to perform Stored Cross-Site Scripting attacks | 2024-06-04 | not yet calculated | |
| Unknown--Gutenberg Blocks with AI by Kadence WP | The Gutenberg Blocks with AI by Kadence WP WordPress plugin before 3.2.37 does not validate and escape some of its block attributes before outputting them back in a page/post where the block is embed, which could allow users with the contributor role and above to perform Stored Cross-Site Scripting attacks | 2024-06-04 | not yet calculated | |
| Unknown--Insert or Embed Articulate Content into WordPress | The Insert or Embed Articulate Content into WordPress plugin through 4.3000000023 is not properly filtering which file extensions are allowed to be imported on the server, allowing the uploading of malicious code within zip files | 2024-06-04 | not yet calculated | |
| Unknown--Logo Slider | The Logo Slider WordPress plugin before 4.0.0 does not validate and escape some of its Slider Settings before outputting them back in attributes, which could allow users with the contributor role and above to perform Stored Cross-Site Scripting attacks | 2024-06-07 | not yet calculated | |
| Unknown--Simple Ajax Chat | The Simple Ajax Chat WordPress plugin before 20240412 does not sanitise and escape some of its settings, which could allow high privilege users such as admin to perform Stored Cross-Site Scripting attacks even when the unfiltered_html capability is disallowed (for example in multisite setup) | 2024-06-04 | not yet calculated | |
| Unknown--The Events Calendar | The Events Calendar WordPress plugin before 6.4.0.1 does not properly sanitize user-submitted content when rendering some views via AJAX. | 2024-06-04 | not yet calculated | |
| Unknown--WP Backpack | The WP Backpack WordPress plugin through 2.1 does not sanitise and escape some of its settings, which could allow high privilege users such as admin to perform Stored Cross-Site Scripting attacks even when the unfiltered_html capability is disallowed (for example in multisite setup) | 2024-06-07 | not yet calculated | |
| Unknown--WP Stacker | The WP Stacker WordPress plugin through 1.8.5 does not have CSRF check in some places, and is missing sanitisation as well as escaping, which could allow attackers to make logged in admin add Stored XSS payloads via a CSRF attack | 2024-06-07 | not yet calculated | |
| Unknown--wp-eMember | The wp-eMember WordPress plugin before 10.3.9 does not sanitize and escape the "fieldId" parameter before outputting it back in the page, leading to a Reflected Cross-Site Scripting. | 2024-06-04 | not yet calculated | |
| zenml-io--zenml-io/zenml | A race condition vulnerability exists in zenml-io/zenml versions up to and including 0.55.3, which allows for the creation of multiple users with the same username when requests are sent in parallel. This issue was fixed in version 0.55.5. The vulnerability arises due to insufficient handling of concurrent user creation requests, leading to data inconsistencies and potential authentication problems. Specifically, concurrent processes may overwrite or corrupt user data, complicating user identification and posing security risks. This issue is particularly concerning for APIs that rely on usernames as input parameters, such as PUT /api/v1/users/test_race, where it could lead to further complications. | 2024-06-06 | not yet calculated | |
| zenml-io--zenml-io/zenml | An improper authorization vulnerability exists in the zenml-io/zenml repository, specifically within the API PUT /api/v1/users/id endpoint. This vulnerability allows any authenticated user to modify the information of other users, including changing the `active` status of user accounts to false, effectively deactivating them. This issue affects version 0.55.3 and was fixed in version 0.56.2. The impact of this vulnerability is significant as it allows for the deactivation of admin accounts, potentially disrupting the functionality and security of the application. | 2024-06-06 | not yet calculated | |
| zenml-io--zenml-io/zenml | A stored Cross-Site Scripting (XSS) vulnerability was identified in the zenml-io/zenml repository, specifically within the 'logo_url' field. By injecting malicious payloads into this field, an attacker could send harmful messages to other users, potentially compromising their accounts. The vulnerability affects version 0.55.3 and was fixed in version 0.56.2. The impact of exploiting this vulnerability could lead to user account compromise. | 2024-06-06 | not yet calculated | |
| zenml-io--zenml-io/zenml | An issue was discovered in zenml-io/zenml versions up to and including 0.55.4. Due to improper authentication mechanisms, an attacker with access to an active user session can change the account password without needing to know the current password. This vulnerability allows for unauthorized account takeover by bypassing the standard password change verification process. The issue was fixed in version 0.56.3. | 2024-06-06 | not yet calculated | |
| zenml-io--zenml-io/zenml | A clickjacking vulnerability exists in zenml-io/zenml versions up to and including 0.55.5 due to the application's failure to set appropriate X-Frame-Options or Content-Security-Policy HTTP headers. This vulnerability allows an attacker to embed the application UI within an iframe on a malicious page, potentially leading to unauthorized actions by tricking users into interacting with the interface under the attacker's control. The issue was addressed in version 0.56.3. | 2024-06-06 | not yet calculated | |
| zenml-io--zenml-io/zenml | A vulnerability in zenml-io/zenml version 0.56.3 allows attackers to reuse old session credentials or session IDs due to insufficient session expiration. Specifically, the session does not expire after a password change, enabling an attacker to maintain access to a compromised account without the victim's ability to revoke this access. This issue was observed in a self-hosted ZenML deployment via Docker, where after changing the password from one browser, the session remained active and usable in another browser without requiring re-authentication. | 2024-06-08 | not yet calculated | |
Please share your thoughts
We recently updated our anonymous product survey ; we’d welcome your feedback.

IMAGES
VIDEO
COMMENTS
GitHub is where people build software. More than 100 million people use GitHub to discover, fork, and contribute to over 420 million projects. ... university e-learning educational-project Updated Aug 12, 2022; PHP; abdallah-abuzead / E-Learning Star 19. Code ... LibreEOL is an innovative online assessment system based on HTML5, CSS2/3, PHP5 ...
EducationHub is a comprehensive educational repository on GitHub that aims to provide a wide range of learning resources, projects, and tutorials for students, teachers, and self-learners. Whether you are a beginner or an experienced learner, EducationHub has something for everyone. @kambohdiv #LahoreScience-Academy.
Add this topic to your repo. To associate your repository with the educational-project topic, visit your repo's landing page and select "manage topics." Learn more. GitHub is where people build software. More than 100 million people use GitHub to discover, fork, and contribute to over 420 million projects.
To associate your repository with the learning-management-system topic, visit your repo's landing page and select "manage topics." GitHub is where people build software. More than 100 million people use GitHub to discover, fork, and contribute to over 420 million projects.
This E-Learning System is an online based system that is made of PHP, JavaScript, Bootstrap templates, JQuery and MYSQL database. This system is very helpful most especially if you are going to make online lessons, activities and also make quizzes.
To associate your repository with the school-management-system topic, visit your repo's landing page and select "manage topics." GitHub is where people build software. More than 100 million people use GitHub to discover, fork, and contribute to over 420 million projects.
E-Learning System is a web-based system that aims to make the role of teachers easier in making their lessons, activities, and quizzes.The function of this is, the teacher can upload his lesson whether it's a video or a pdf file.He can also set questions of quizzes or activities based on the lesson that he uploaded.The students need to create an account first so they can log-in and they can ...
Complete Online Learning Management System in PHP and MySQL with source code is free to download, Use for educational purposes only! Follow the following steps after Starting Apache and MySQL in XAMPP: 1st Step: Firstly, Extract the file. 2nd Step: After that, Copy the main project folder.
To associate your repository with the php-project topic, visit your repo's landing page and select "manage topics." GitHub is where people build software. More than 100 million people use GitHub to discover, fork, and contribute to over 420 million projects.
Download or set up any local web server that runs PHP script. Open the web-server database and create a new database name it "capstone". Import the SQL file located in the "db" folder of the source code. Copy and paste the source code to the location where your local web server accessing your local projects. Example for XAMPP ('C:\xampp\htdocs')
The Online E-Learning System stands as a testament to technological advancement, providing an intuitive platform for both educators and learners. Built upon a robust foundation of PHP, JavaScript, Bootstrap layouts, JQuery, and MYSQL database, this system epitomizes efficiency and versatility. Its seamless integration of various components ...
Online E-Learning System Using PHP and MySQLi. This E-Learning System is an online framework that is made with PHP, JavaScript, Bootstrap layouts, jQuery, and a MySQL database. It is perfect for online exercises and tests. Advanced School Management System With Complete Features. Using this script, you can manage all aspects of running a school.
Download or set up any local web server that runs PHP script. Open the web-server database and create a new database name it "elearning". Import the SQL file located in the "db" folder of the source code. Copy and paste the source code to the location where your local web server accessing your local projects. Example for XAMPP ('C:\xampp\htdocs')
To run this project you must have installed a virtual server i.e XAMPP on your PC. Online Student Management System in PHP with source code is free to download, Use for educational purposes only! After Starting Apache and MySQL in XAMPP, follow the following steps. 1st Step: Extract file 2nd Step: Copy the main project folder 3rd Step: Paste in ...
This E-Learning System is an online based system that is made of PHP, JavaScript, Bootstrap templates, JQuery and MYSQL database.This system is very helpful most especially if you are going to make online lessons, activities and also make quizzes.. E-learning to open more courses for trainning every one in the world. Courses will made by we, by you.
Revolutionizing Education: Online Examination System in PHP MySQL Free Source Code Download. In the digital age, traditional methods of conducting examinations are rapidly evolving to keep pace with technological advancements. One such groundbreaking innovation is the Online Examination System, a paradigm shift in the assessment landscape.
PHP Projects with Source Code free Downloads, PHP Project Download , Free PHP projects for students & beginners, free Php mini projects available with live demo, MySQL projects with source code free download on PHPGurukul. ... Real Estate Management System Project using PHP & MySQL: Rs.799 / $11.31: 16: Campus Recruitment Management System ...
Free PHP Projects with Source Code. Download latest editors' pick PHP projects with source code for free here. We select the best source code uploaded here and hand pick it for you. ... This web-based application is designed for teachers, professors, or instructors in educational institutions. The system facilitates easy recording, retrieval ...
{"payload":{"contentfulRawJsonResponse":{"sys":{"type":"Array"},"total":1,"skip":0,"limit":100,"items":[{"metadata":{"tags":[]},"sys":{"space":{"sys":{"type":"Link ...
These are the steps on how to run [ADVANCED] School Management System In PHP With Source Code. Step 1: Download Source Code. First, find the downloadable source code below and click to start downloading the source code file. Step 2: Extract File. Next, after finished to download the file, go to file location and right click the file and click ...
Download 10 Best Free PHP Projects with Source Code. There are hundreds to thousands of free PHP projects available online that you can toy to learn how to develop and program using PHP. Here is a rundown of 10 of our preferred best free PHP projects for beginners: 1. Church management system in php. Church is commonly defined as abuilding used ...
Online Learning Management System Using PHP_MySQLi With Source Code _ Free Source Code, Projects & Tutorials - Free download as PDF File (.pdf), Text File (.txt) or read online for free. This document provides source code for an online learning management system built with PHP and MySQLi. It describes the key features and functions for administrators, teachers, and students.
These are the steps on how to run School Management System In PHP Open Source. Step 1: Download Source Code. First, find the downloadable source code below and click to start downloading the source code file. Step 2: Extract File. Next, after finished to download the file, go to file location and right click the file and click extract.
The interface for osTicket is now completely translatable. Language packs are available on the download page. If you do not see your language there, join the Crowdin project and request to have your language added. Languages which reach 100% translated are are significantly reviewed will be made available on the osTicket download page.
At the heart of GitHub is an open-source version control system (VCS) called Git. ... but do not want to use the command line, you can download and install the GitHub Desktop client. For more information, see "About GitHub Desktop." ... Creating a repository for your project allows you to store code in GitHub. This provides a backup of your ...
Enjoy full access to our latest web application scanning offering designed for modern applications as part of the Tenable One Exposure Management platform. Safely scan your entire online portfolio for vulnerabilities with a high degree of accuracy without heavy manual effort or disruption to critical web applications. Sign up now.
An attacker with the 'Project Manager' on a single project may take over any other project. The vulnerability is fixed in 1.2.37. 2024-06-06: 8.2: CVE-2024-36399 [email protected] [email protected]: litonice13--Master Addons Free Widgets, Hover Effects, Toggle, Conditions, Animations for Elementor